
Linux passwords mainly exist in two files: 1. The "/etc/shadow" file is used to store user password information; only the root user has read permissions for this file, and other users do not have any permissions, so The security of user passwords is guaranteed. 2. The "/etc/gshadow" file is used to store the password information of group users. The file contains group name, encrypted password, group administrator and group additional user list information.
#The operating environment of this tutorial: linux7.3 system, Dell G3 computer.
Linux passwords mainly exist in two files
/etc/shadow File: used to store password information of users in Linux systems, also known as "shadow files".
/etc/gshadow File: used to store password information for group users in Linux systems.
1. Shadow file
/etc/shadow file is used to store the password information of users in the Linux system. , also known as "shadow files".
There is a passwd file in etc., which stores the basic information of all users in the system. However, because this file is allowed to be read by all users, it can easily lead to the leakage of user passwords. Therefore, the Linux system stores the user’s password information. Separated from the /etc/passwd file and placed in this file alone.
/etc/shadow file only the root user has read permissions, and other users do not have any permissions, thus ensuring the security of user passwords.
Note that if the permissions of this file are changed, you need to pay attention to whether it is a malicious attack.
Each line in the /etc/shadow file represents a user, and ":" is also used as the delimiter. The difference is that each line of user information is divided into 9 fields. The meaning of each field is as follows:
用户名:加密密码:最后一次修改时间:最小修改时间间隔:密码有效期:密码需要变更前的警告天数:密码过期后的宽限时间:账号失效时间:保留字段
Next, I will introduce these 9 fields to you.
1) The user name
has the same meaning as the user name in the /etc/passwd file.
2) Encrypted password
What is saved here is the truly encrypted password. Currently, Linux passwords use the SHA512 hash encryption algorithm, which originally used the MD5 or DES encryption algorithm. The SHA512 hash encryption algorithm provides a higher level of encryption and is more secure.
Note that the garbled characters generated by this string of passwords cannot be modified manually. If modified manually, the system will not be able to recognize the password, causing the password to become invalid. Many software use this function to add "!", "*" or "x" before the password string to temporarily invalidate the password.
The passwords of all pseudo users are "!!" or "*", which means you cannot log in without a password. Of course, if a newly created user does not set a password, its password item will also be "!!", which means that the user does not have a password and cannot log in.
3) Last modification time
This field indicates the time when the password was last modified. However, why does the root user display 15775?
This is because Linux calculates the date by taking January 1, 1970 as 1 and accumulating the time. By January 1, 1971, it will be 366 days. 15775 days are displayed here, that is to say, the root user password was changed by this root account on the 15775th day after January 1, 1970.
So, which day does 15775 represent? You can use the following command to convert:
[root@localhost ~]# date -d "1970-01-01 15775 days" 2013年03月11日 星期一 00:00:00 CST
You can see that through the above command, it can be converted to the system date we are used to.
4) Minimum modification time interval
Minimum modification interval time, that is to say, this field specifies the start from the 3rd field (the date of the last password modification) , how long the password cannot be changed. If it is 0, the password can be changed at any time; if it is 10, it means that the password cannot be changed again within 10 days after the password is changed.
This field is designed to prevent some people from frequently changing their account passwords.
5) Password validity period
It is a good habit to change passwords frequently. In order to force users to change passwords, this field can specify the distance from the 3rd field (the last password change) How long does it take to change the password again, otherwise the account password will expire.
The default value of this field is 99999, which is 273 years, which can be considered as permanent. If changed to 90, it means that the password must be changed again after 90 days, otherwise the user will expire. When managing the server, use this field to force users to change their passwords regularly.
6) The number of warning days before the password needs to be changed
Compared with the 5th field, when the account password validity period is about to expire, the system will issue a warning message to the account , reminding users "Your password will expire in n days, please reset your password as soon as possible!".
该字段的默认值是 7,也就是说,距离密码有效期的第 7 天开始,每次登录系统都会向该账户发出 "修改密码" 的警告信息。
7)密码过期后的宽限天数
也称为“口令失效日”,简单理解就是,在密码过期后,用户如果还是没有修改密码,则在此字段规定的宽限天数内,用户还是可以登录系统的;如果过了宽限天数,系统将不再让此账户登陆,也不会提示账户过期,是完全禁用。
比如说,此字段规定的宽限天数是 10,则代表密码过期 10 天后失效;如果是 0,则代表密码过期后立即失效;如果是 -1,则代表密码永远不会失效。
8)账号失效时间
同第 3 个字段一样,使用自 1970 年 1 月 1 日以来的总天数作为账户的失效时间。该字段表示,账号在此字段规定的时间之外,不论你的密码是否过期,都将无法使用!
该字段通常被使用在具有收费服务的系统中。
9)保留
这个字段目前没有使用,等待新功能的加入。
忘记密码怎么办
经常有读者会忘记自己的账户密码,该怎么处理呢?
对于普通账户的密码遗失,可以通过 root 账户解决,它会重新给你配置好指定账户的密码,而不需知道你原有的密码(利用 root 的身份使用 passwd 命令即可)。
如果 root 账号的密码遗失,则需要重新启动进入单用户模式,系统会提供 root 权限的 bash 接口,此时可以用 passwd 命令修改账户密码;也可以通过挂载根目录,修改 /etc/shadow,将账户的 root 密码清空的方法,此方式可使用 root 无法密码即可登陆,建议登陆后使用 passwd 命令配置 root 密码。
2、gshadow文件
组用户信息存储在 /etc/group 文件中,而将组用户的密码信息存储在 /etc/gshadow 文件中。
gshadow文件中,每行代表一个组用户的密码信息,各行信息用 ":" 作为分隔符分为 4 个字段,每个字段的含义如下:
组名:加密密码:组管理员:组附加用户列表
1)组名
同 /etc/group 文件中的组名相对应。
2)组密码
对于大多数用户来说,通常不设置组密码,因此该字段常为空,但有时为 "!",指的是该群组没有组密码,也不设有群组管理员。
3)组管理员
从系统管理员的角度来说,该文件最大的功能就是创建群组管理员。那么,什么是群组管理员呢?
考虑到 Linux 系统中账号太多,而超级管理员 root 可能比较忙碌,因此当有用户想要加入某群组时,root 或许不能及时作出回应。这种情况下,如果有群组管理员,那么他就能将用户加入自己管理的群组中,也就免去麻烦 root 了。
不过,由于目前有 sudo 之类的工具,因此群组管理员的这个功能已经很少使用了。
4)组中的附加用户
该字段显示这个用户组中有哪些附加用户,和 /etc/group 文件中附加组显示内容相同。
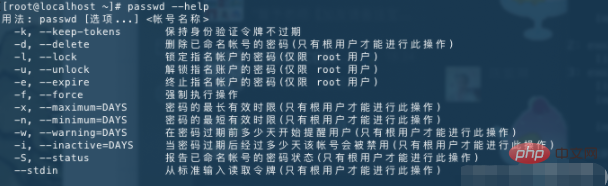
passwd命令用于更新/etc/shadow文件中用户的身份验证令牌。
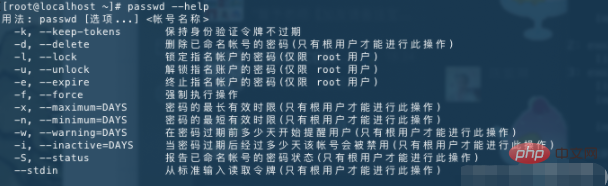
# 当前用户修改密码,直接使用passwd passwd # 为其他用户修改密码 passwd 用户名
禁用用户passwd命令用于更新/etc/shadow文件中用户的身份验证令牌。
# 锁定用户的密码 passwd -l daygeek ## 回显 Locking password for user daygeek. passwd: Success # 查看用户的密码锁定状态 passwd -S daygeek # 解锁用户的密码 passwd -u daygeek
# 查看账号的密码状态 passwd -S root
帐户密码状态的简短信息。

单引号' ',双引号" "的区别:
' '剥夺了所有字符的特殊含义,单引号' '内就变成了单纯的字符。" "则对于双引号" "内的参数替换($)和命令替换(``)是个例外。# 用echo写入新密码到passwd中 ## passwd --stdin:从标准输入(比如管道)写入密码 # echo双引号不要使用特殊字符,比如!,会被转义 ## echo使用单引号,引号内的字符不会被转义 echo '新密码'|passwd --stdin 用户名 # Ubuntu不支持 --stdin参数,可以使用替代命令 echo user:pass | chpasswd

## -d 删除已有密码 passwd -d 用户名

[root@localhost ~]# chage --help 用法:chage [选项] 登录 选项: -d, --lastday 最近日期 将最近一次密码设置时间设为“最近日期” -E, --expiredate 过期日期 将帐户过期时间设为“过期日期” -h, --help 显示此帮助信息并推出 -I, --inactive INACITVE 过期 INACTIVE 天数后,设定密码为失效状态 -l, --list 显示帐户年龄信息 -m, --mindays 最小天数 将两次改变密码之间相距的最小天数设为“最小天数” -M, --maxdays 最大天数 将两次改变密码之间相距的最大天数设为“最大天数” -R, --root CHROOT_DIR chroot 到的目录 -W, --warndays 警告天数 将过期警告天数设为“警告天数”
# 查看上次密码的修改时间 # 查看密码过期配置 chage -l root
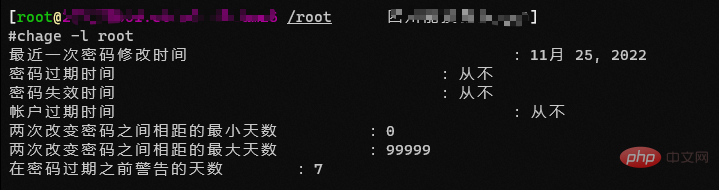
# 修改testt用户密码信息,设置最大有效期为120天,最小有效期为7天 ## -M, --maxdays 最大天数 将两次改变密码之间相距的最大天数设为“最大天数” ## -m, --mindays 最小天数 将两次改变密码之间相距的最小天数设为“最小天数” chage -M 120 -m 7 test
# test这个账号的有效期是2014-09-30 ## -E, --expiredate 过期日期 将帐户过期时间设为“过期日期” chage -E '2014-09-30' test
# 修改用户的密码有效期为永久(5个9) ## -M, --maxdays 最大天数 将两次改变密码之间相距的最大天数设为“最大天数” chage -M 99999 用户名
# 使密码立即失效 # 强制要求用户登陆时修改密码 ## -d, --lastday 最近日期 将最近一次密码设置时间设为“最近日期” chage -d 0 用户名 # 查看密码过期时间 [root@localhost ~]# chage -l use1 最近一次密码修改时间 :密码必须修改 密码过期时间 :密码必须修改 密码失效时间 :密码必须修改 帐户过期时间 :从不 两次改变密码之间相距的最小天数 :0 两次改变密码之间相距的最大天数 :99999 在密码过期之前警告的天数 :7
[student@workstation data-secret]$ openssl passwd --help Usage: passwd [options] Valid options are: -help Display this summary -in infile Read passwords from file -noverify Never verify when reading password from terminal -quiet No warnings -table Format output as table -reverse Switch table columns -salt val Use provided salt -stdin Read passwords from stdin -6 SHA512-based password algorithm -5 SHA256-based password algorithm -apr1 MD5-based password algorithm, Apache variant -1 MD5-based password algorithm -aixmd5 AIX MD5-based password algorithm -crypt Standard Unix password algorithm (default) -rand val Load the file(s) into the random number generator -writerand outfile Write random data to the specified file
[student@workstation data-secret]$ openssl passwd -6 Password: # 提示输入密码 Verifying - Password: # 确认密码 # 生成的加密后的密码 $6$hkf.tpoz/woyZn1c$ArDSHie9USt44nnqymqL6OZWKsI3e0WWl4NedhfmQOlSEN6er18SYSfyGnvxQmEgC81DLKuERhqDm5Ei3iIDw0
使用-salt 字符串 给密码加盐
不同的盐,密码相同,算法相同,密文不同
相同的盐,密码相同,算法相同,密文相同
# 加盐rhel生成密码密文 [student@workstation data-secret]$ openssl passwd -6 -salt rhel Password: # 输入密码 ## 生成的密文 $6$rhel$2JncQy/NAQr4GHoVgz49YGRni8lXx3jakLxYxEBcTYLN8hh7Nu9fJc4zSbRhiJmv0vBlB6W3YyQp.nLZo8MCy0 # 再次实验加盐rhel生成密文 [student@workstation data-secret]$ openssl passwd -6 -salt rhel Password: # 输入密码 ## 生成的密文与上次密文完全一致 $6$rhel$2JncQy/NAQr4GHoVgz49YGRni8lXx3jakLxYxEBcTYLN8hh7Nu9fJc4zSbRhiJmv0vBlB6W3YyQp.nLZo8MCy0
$6$rhel$2JncQy/NAQr4GHoVgz49YGRni8lXx3jakLxYxEBcTYLN8hh7Nu9fJc4zSbRhiJmv0vBlB6W3YyQp.nLZo8MCy0 ## $6 表示加密算法sha512 ## $rhel 表示盐时rhel ## 第三个$之后才是 算法+盐+原密码 生成的密文
相关推荐:《Linux视频教程》
The above is the detailed content of In which files do linux passwords exist?. For more information, please follow other related articles on the PHP Chinese website!