ChatGPT and large language models: what are the risks?
Large-scale language models (LLMs) and AI chatbots are attracting worldwide interest due to the release of ChatGPT in late 2022 and the query convenience it provides. It's now one of the fastest-growing consumer applications of all time, and its popularity is prompting many competitors to develop their own services and models, or to quickly deploy those they've been developing in-house.
As with any emerging technology, there are always concerns about what this means for security. This blog has recently considered some of the cybersecurity aspects of ChatGPT and LLM more generally.
What is ChatGPT and what are LLMs?
ChatGPT is an artificial intelligence chatbot developed by American technology startup OpenAI. It's based on GPT-3, a language model released in 2020 that uses deep learning to generate human-like text, but the underlying LLM technology has been around for a long time.
The LLM is where algorithms are trained on large amounts of text-based data, often scraped from the open internet, thus covering web pages and – depending on the LLM – other sources , such as scientific research, books, or social media posts. This covers such a large amount of data that it is impossible to filter out all objectionable or inaccurate content upon ingestion, so "controversial" content is likely to be included in its in the model.
These algorithms analyze the relationships between different words and convert them into probabilistic models. The algorithm can then be given a "hint" (for example, by asking it a question) and it will provide an answer based on the relationships of the words in its model.
Typically, the data in its model is static after training, although it can be improved through "fine-tuning" (training on additional data) and "hint augmentation" (providing contextual information about the problem). An example of prompt enhancement might be:
Taking into account the below information, how would you describe...
Then copying potentially a large amount of text (or the entire document) into the prompt/question .
ChatGPT effectively allows users to ask LLM questions, just like you would in a conversation with a chatbot. Other recent examples of LLM include announcements from Google's Bard and Meta's LLaMa (for scientific papers).
LL.M.s are certainly impressive because of their ability to generate a wealth of compelling content in a variety of human and computer languages. However, they are not magic, nor are they artificial general intelligence, and contain some serious flaws, including:
- They can get things wrong and "hallucinate" incorrect facts
- They can be biased and often gullible (e.g. when answering the main question)
- They require huge computing resources and massive amounts of data to train from scratch
- They can be coaxed into creating toxic content and is vulnerable to "injection attacks"
Will LLM leak my information?
A common concern is that LLM may "learn" from your prompts and provide that information to others who query related content. There are some reasons for concern here, but not for the reasons many people consider. Currently, an LLM is trained and then the resulting model is queried. LLM does not (at the time of writing) automatically add information from a query to its model for others to query. That is, including information in a query will not cause that data to be incorporated into the LLM.
However, the query will be visible to the organization providing the LLM (for ChatGPT, also for OpenAI). These queries are stored and will almost certainly be used at some point to develop an LLM service or model. This may mean that the LLM provider (or its partners/contractors) is able to read the queries and possibly incorporate them into future releases in some way. Therefore, you need to thoroughly understand the Terms of Use and Privacy Policy before asking sensitive questions.
A question may be sensitive because of the data contained in the query, or because of who (and when) asked the question. Examples of the latter might be if it is discovered that the CEO has asked "How best to fire an employee?", or if someone has asked revealing health or relationship questions. Also remember to use the same login to aggregate information across multiple queries.
Another risk that increases as more organizations produce LLMs is that queries stored online could be hacked, leaked, or more likely accidentally made publicly accessible. This may include potentially user-identifying information. Another risk is that the operator of the LLM is later acquired by an organization that adopts a different approach to privacy than when the user entered their data.
Therefore, NCSC recommends:
- Don’t include sensitive information in queries to public LLMs
- Do not submit queries to public LLMs that will cause problems
How do I securely submit queries to LLMs Sensitive information?
With the rise of LLM, many organizations may be wondering whether they can use LLM to automate certain business tasks, which may involve providing sensitive information through fine-tuning or just-in-time augmentation. While this approach is not recommended for public LLMs, a "private LLM" may be provided by a cloud provider (for example), or may be completely self-hosted:
- For cloud-provided LLMs, the Terms of Use and Privacy policies are again key (as they are for public LLMs), but are more likely to be consistent with the cloud service's existing terms. Organizations need to understand how to manage data used for fine-tuning or prompt augmentation. Can the vendor's researchers or partners use it? If so, in what form? Is data shared individually or in aggregate with other organizations? Under what circumstances can the provider's employees view the query?
- Self-hosted LLM can be very expensive. However, following a security assessment, they may be suitable for processing organizational data. In particular, organizations should refer to our guidance on protecting infrastructure and data supply chains.
Do LLMs make cybercriminals’ lives easier?
There have been some incredible demonstrations of how LLM can help write malware. The concern is that LLM could help malicious (but unskilled) individuals create tools they would not otherwise be able to deploy. In their current state, LLMs look convincing (whether they are or not) and are suited to simple tasks rather than complex ones. This means that LLM can be used to “help experts save time” because experts can verify the output of the LLM.
For more complex tasks, it is currently easier for experts to create malware from scratch rather than having to spend time correcting what LLM generates. However, experts capable of creating powerful malware may well be able to trick LLM into writing powerful malware. The trade-off between "using LLM to create malware from scratch" and "validating LLM-created malware" will change as LLM improves.
You can also ask the LLM for advice on technical issues. Criminals may use LLM to help conduct cyber attacks beyond their current capabilities, especially after the attacker gains access to the network. For example, if an attacker is working to escalate privileges or find data, they might ask LLM and receive a different answer than the search engine results but with more context. Current LLMs provide answers that sound convincing but may only be partially correct, especially as the topic becomes more niche. The answers may help criminals carry out attacks they could not otherwise perform, or they may suggest actions to expedite detection of criminals. Either way, the attacker's queries may be stored and retained by the LLM operator.
Because LLM excels at replicating writing styles on demand, there is a risk that criminals could use LLM to write convincing phishing emails, including emails in multiple languages. This can help attackers with high technical abilities but lack language skills, helping them create convincing phishing emails (or conduct social engineering) in the target's native language.
In summary, in the short term we may see:
- More convincing phishing emails due to LLM
- Attackers try things they wouldn’t before Familiar Technology
The risk of a less skilled attacker writing powerful malware is also low.
Summary
This is an exciting time for LLM, especially with ChatGPT capturing the imagination of the world. As with all technological developments, there will be people who are keen to use it and study what it has to offer, and people who may never use it.
As we have outlined above, there are undoubtedly risks associated with the unrestricted use of a public LLM. Individuals and organizations should be extremely careful about the data they choose to submit in prompts. You should ensure that those who want to try LLM can, but do so without putting organizational data at risk.
NCSC is aware of other emerging threats (and opportunities) related to cybersecurity and LLM adoption, and we will of course make you aware of these in future blog posts.
——Compiled from UK NCSC
The above is the detailed content of ChatGPT and large language models: what are the risks?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 ChatGPT now allows free users to generate images by using DALL-E 3 with a daily limit
Aug 09, 2024 pm 09:37 PM
ChatGPT now allows free users to generate images by using DALL-E 3 with a daily limit
Aug 09, 2024 pm 09:37 PM
DALL-E 3 was officially introduced in September of 2023 as a vastly improved model than its predecessor. It is considered one of the best AI image generators to date, capable of creating images with intricate detail. However, at launch, it was exclus
 The world's most powerful open source MoE model is here, with Chinese capabilities comparable to GPT-4, and the price is only nearly one percent of GPT-4-Turbo
May 07, 2024 pm 04:13 PM
The world's most powerful open source MoE model is here, with Chinese capabilities comparable to GPT-4, and the price is only nearly one percent of GPT-4-Turbo
May 07, 2024 pm 04:13 PM
Imagine an artificial intelligence model that not only has the ability to surpass traditional computing, but also achieves more efficient performance at a lower cost. This is not science fiction, DeepSeek-V2[1], the world’s most powerful open source MoE model is here. DeepSeek-V2 is a powerful mixture of experts (MoE) language model with the characteristics of economical training and efficient inference. It consists of 236B parameters, 21B of which are used to activate each marker. Compared with DeepSeek67B, DeepSeek-V2 has stronger performance, while saving 42.5% of training costs, reducing KV cache by 93.3%, and increasing the maximum generation throughput to 5.76 times. DeepSeek is a company exploring general artificial intelligence
 Hello, electric Atlas! Boston Dynamics robot comes back to life, 180-degree weird moves scare Musk
Apr 18, 2024 pm 07:58 PM
Hello, electric Atlas! Boston Dynamics robot comes back to life, 180-degree weird moves scare Musk
Apr 18, 2024 pm 07:58 PM
Boston Dynamics Atlas officially enters the era of electric robots! Yesterday, the hydraulic Atlas just "tearfully" withdrew from the stage of history. Today, Boston Dynamics announced that the electric Atlas is on the job. It seems that in the field of commercial humanoid robots, Boston Dynamics is determined to compete with Tesla. After the new video was released, it had already been viewed by more than one million people in just ten hours. The old people leave and new roles appear. This is a historical necessity. There is no doubt that this year is the explosive year of humanoid robots. Netizens commented: The advancement of robots has made this year's opening ceremony look like a human, and the degree of freedom is far greater than that of humans. But is this really not a horror movie? At the beginning of the video, Atlas is lying calmly on the ground, seemingly on his back. What follows is jaw-dropping
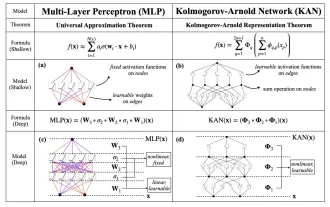 KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
Earlier this month, researchers from MIT and other institutions proposed a very promising alternative to MLP - KAN. KAN outperforms MLP in terms of accuracy and interpretability. And it can outperform MLP running with a larger number of parameters with a very small number of parameters. For example, the authors stated that they used KAN to reproduce DeepMind's results with a smaller network and a higher degree of automation. Specifically, DeepMind's MLP has about 300,000 parameters, while KAN only has about 200 parameters. KAN has a strong mathematical foundation like MLP. MLP is based on the universal approximation theorem, while KAN is based on the Kolmogorov-Arnold representation theorem. As shown in the figure below, KAN has
 Tesla robots work in factories, Musk: The degree of freedom of hands will reach 22 this year!
May 06, 2024 pm 04:13 PM
Tesla robots work in factories, Musk: The degree of freedom of hands will reach 22 this year!
May 06, 2024 pm 04:13 PM
The latest video of Tesla's robot Optimus is released, and it can already work in the factory. At normal speed, it sorts batteries (Tesla's 4680 batteries) like this: The official also released what it looks like at 20x speed - on a small "workstation", picking and picking and picking: This time it is released One of the highlights of the video is that Optimus completes this work in the factory, completely autonomously, without human intervention throughout the process. And from the perspective of Optimus, it can also pick up and place the crooked battery, focusing on automatic error correction: Regarding Optimus's hand, NVIDIA scientist Jim Fan gave a high evaluation: Optimus's hand is the world's five-fingered robot. One of the most dexterous. Its hands are not only tactile
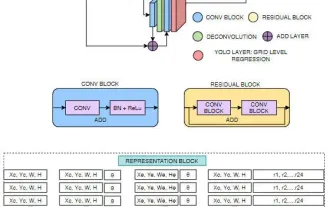 FisheyeDetNet: the first target detection algorithm based on fisheye camera
Apr 26, 2024 am 11:37 AM
FisheyeDetNet: the first target detection algorithm based on fisheye camera
Apr 26, 2024 am 11:37 AM
Target detection is a relatively mature problem in autonomous driving systems, among which pedestrian detection is one of the earliest algorithms to be deployed. Very comprehensive research has been carried out in most papers. However, distance perception using fisheye cameras for surround view is relatively less studied. Due to large radial distortion, standard bounding box representation is difficult to implement in fisheye cameras. To alleviate the above description, we explore extended bounding box, ellipse, and general polygon designs into polar/angular representations and define an instance segmentation mIOU metric to analyze these representations. The proposed model fisheyeDetNet with polygonal shape outperforms other models and simultaneously achieves 49.5% mAP on the Valeo fisheye camera dataset for autonomous driving
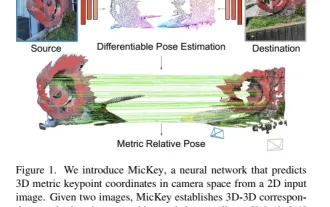 The latest from Oxford University! Mickey: 2D image matching in 3D SOTA! (CVPR\'24)
Apr 23, 2024 pm 01:20 PM
The latest from Oxford University! Mickey: 2D image matching in 3D SOTA! (CVPR\'24)
Apr 23, 2024 pm 01:20 PM
Project link written in front: https://nianticlabs.github.io/mickey/ Given two pictures, the camera pose between them can be estimated by establishing the correspondence between the pictures. Typically, these correspondences are 2D to 2D, and our estimated poses are scale-indeterminate. Some applications, such as instant augmented reality anytime, anywhere, require pose estimation of scale metrics, so they rely on external depth estimators to recover scale. This paper proposes MicKey, a keypoint matching process capable of predicting metric correspondences in 3D camera space. By learning 3D coordinate matching across images, we are able to infer metric relative
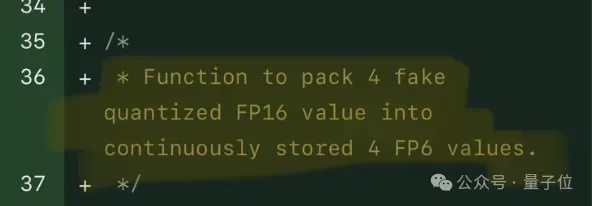 Single card running Llama 70B is faster than dual card, Microsoft forced FP6 into A100 | Open source
Apr 29, 2024 pm 04:55 PM
Single card running Llama 70B is faster than dual card, Microsoft forced FP6 into A100 | Open source
Apr 29, 2024 pm 04:55 PM
FP8 and lower floating point quantification precision are no longer the "patent" of H100! Lao Huang wanted everyone to use INT8/INT4, and the Microsoft DeepSpeed team started running FP6 on A100 without official support from NVIDIA. Test results show that the new method TC-FPx's FP6 quantization on A100 is close to or occasionally faster than INT4, and has higher accuracy than the latter. On top of this, there is also end-to-end large model support, which has been open sourced and integrated into deep learning inference frameworks such as DeepSpeed. This result also has an immediate effect on accelerating large models - under this framework, using a single card to run Llama, the throughput is 2.65 times higher than that of dual cards. one




