 Technology peripherals
Technology peripherals
 AI
AI
 Artificial intelligence is ready to take off, security meets opportunities and challenges
Artificial intelligence is ready to take off, security meets opportunities and challenges
Artificial intelligence is ready to take off, security meets opportunities and challenges
In recent years, with the improvement of its status, artificial intelligence has attracted more and more attention from the country. In July 2015, "artificial intelligence" was included in the "Guiding Opinions of the State Council on Actively Promoting the "Internet" Action"; in March 2016, the term "artificial intelligence" was included in the "13th Five-Year Plan" outline; in May 2016 In March, four departments including the National Development and Reform Commission jointly issued the "Three-Year Action Plan for "Internet" Artificial Intelligence"; in March 2017, "artificial intelligence" was included in the government work report. It can be said that artificial intelligence has reached a new height in promoting economic development, and many artificial intelligence concept stocks also performed well during the two sessions.
The "Artificial Intelligence Development Report 2016" shows that China's total number of artificial intelligence applications has reached 15,745, ranking second; investment in the field of artificial intelligence ranks third. It can be expected that in the next 5 to 10 years, artificial intelligence will be like water and electricity*, and a new era of "artificial intelligence" is coming.
Some analysts mentioned that the three to five years starting from 2017 will be the peak period when a large number of artificial intelligence professionals graduate and begin to enter the industry. The introduction of artificial intelligence technology into various industries brings huge opportunities. From an industrial point of view, the next few years will also be a period when artificial intelligence will fully penetrate into big data industries such as finance, medical care, education, and sensory interaction fields. Security, finance, medical care, automobiles, education, information security, retail and other industries are more electronic. The data is high, the data is concentrated and the data quality is high, so a large number of artificial intelligence scenario applications will emerge in these industries.
Those value stocks with stable profitability, clear business models, and reasonable valuations are naturally more popular. When making relevant thematic investment stock selections, you can consider it from three levels: first, continued policy support, second, technological innovation driving profit enhancement, and third, business model innovation. Observed from this point of view, it is not surprising that because artificial intelligence is in the rapid development period of the industry and because of its huge role in improving economic efficiency, it has received high support from policies and received focus from various institutions.
Looking again, there are some catalysts that may appear in the near future: First, the artificial intelligence plan is expected to be released in the near future; in addition, the 2017 IT Summit will be held on April 1, and the theme of the conference is "Moving into the New Era of Intelligence" "; Ke Jie and other human chess players will compete against AlphaGo again in April, etc. These are all factors that continue to catalyze the development of artificial intelligence.
What does artificial intelligence mean to security?
The development of artificial intelligence has certainly attracted the attention of the security industry. As one of the important application areas in the IT industry, the application of artificial intelligence in the security industry has a certain foundation. Even at the 215th IT Gantry Array hosted by TechWeb on March 14, Zhao Yong, founder of Gelin Shen Tong, also said that security monitoring must be the first area where artificial intelligence will generate commercial value on a large scale. This can already be seen in 2016. It can be seen that 2017 will be at least 10 times more than last year.
In fact, with the development of artificial intelligence technology, with video content analysis and recognition technology as the core, through structured description of unstructured data, condensed and summarized information is extracted to achieve rapid retrieval and search. , and carrying out big data analysis and information collision through thinking similar to the human brain are currently hot topics in the security industry.
According to industry forecasts, through big data technology, different types of data such as videos, pictures, WIFI signals, and electronic license plates can be analyzed, collided, potential connections discovered, valuable information extracted, and visualized. The results show that artificial intelligence will be applied in the following security fields:
Personnel analysis application relies on the results output by the artificial intelligence system's personnel characteristic identification service to conduct data analysis to realize personnel identification, personnel deployment, personnel deployment, and personnel identification. Face tracking and other functions.
The vehicle analysis application can meet the needs of full map operations and realize visual applications, including: trajectory analysis, car following analysis, collision analysis, frequency analysis, deck analysis, hidden vehicle mining and other functions.
Multi-resource spatio-temporal application can be based on the command and dispatch of GIS maps, realize the integrated management of various video resources through the geographical information system, and realize the intuitive visualization application of monitoring images. Achieve quick retrieval of images of monitoring points or monitoring areas that need attention, and achieve online tracking of targets. Through video layer overlay, video resource search and video positioning, road conditions, resource distribution, personnel distribution, geographical coordinate information, and police deployment are displayed in a graphical form to intuitively display global information in a comprehensive and multi-dimensional manner. , making command and dispatch more intuitive.
View content warning and automatic warning linkage application to automatically warn the content of the video. When the pre-set plan is triggered, the linked cameras will open the surveillance images at the same time, forming a surveillance blockade of the crime scene and alarming in real time. The control intelligent rule analysis functions include: regional intrusion, tripwire detection, illegal parking, loitering detection, fight detection, items, item loss, illegal tailgating, crowd gathering, traffic flow statistics, license plate feature recognition, fireworks detection, etc.
Video real-time annotation application can use real-time video for real-time structuring, including feature extraction of people, vehicles, and moving targets. Real-time video annotation converts video data into intelligence used by public security in actual combat, realizing the transformation of video data into information , transformation of information.
Facial portrait comparison and search application can compare suspects, quickly confirm the identity of the target, and provide intelligent, fast face comparison and complete video image big data analysis and mining applications. Comprehensive solution to personnel management and monitoring problems such as real-time portrait tracking, monitoring and early warning, rapid identification of personnel, retrieval and approval, personnel historical trajectory tracking and retrieval, etc.
The video image intelligent analysis and judgment application can use image processing algorithms suitable for various scenes and situations on videos and pictures in various formats to achieve clear processing of blurred images. It also provides video intelligent annotation services and retrieval services to achieve intelligent (the system automatically extracts description information) structured descriptions of suspect targets in videos and pictures, reducing the workload of manual annotation of entered structured description information, and meeting a variety of searches at the same time. This method improves the speed and efficiency of video viewing, achieves the purpose of quickly finding and locating suspect targets, and reduces the possibility of missing suspect target information in incident videos.
Vehicle data collision mining application can perform secondary identification of vehicle data in bayonet pictures, including license plate number, vehicle brand, vehicle sub-brand, vehicle year, vehicle color, license plate color, vehicle type, and license plate type , annual inspection standards, sun visors, seat belts and other detailed vehicle information, and conduct data collision and comparison on the vehicle's operating trajectory, activity patterns, etc., so as to mine hidden clues of the case and implement visual applications. The functions include: trajectory analysis, car following analysis , collision analysis, frequency analysis, deck analysis, hidden vehicle mining, etc.
The vehicle real-time deployment and control application can be used to target stolen vehicles, illegal vehicles, vehicles involved in crimes, high-risk personnel vehicles, key vehicles, etc., by analyzing the characteristic attributes of specific moving target objects (such as license plate number, model, color, space, etc.) area, etc.) and their combinations to perform online real-time deployment and control functions.
How to integrate artificial intelligence into security?
These are the advancement and diversification development trends shown by the security video surveillance market under the integration of cutting-edge technologies such as artificial intelligence. Future industry development, centered on the business development of video surveillance, will present a trend of integration of text, picture, geographical space and other information videoization and video data structuring, which will be brought about by the certainty of the development of security technology and the diversified development of business. The uncertain environment will bring opportunities and challenges to security companies in market competition.
From a technical perspective, the reason for promoting the development of intelligent security is the maturity of artificial intelligence in the fields of algorithms and chips and the decline in costs, which has made the commercialization of intelligence more popular. At the market level, the situation in which surveillance intelligence is flourishing is the result of the market seeking differentiated competition. In the future development and changes of the intelligent surveillance market, the popularization of high-definition will be a very critical link. Only when the collection end obtains high-definition video data sources can targeted analysis of events in the monitored area be carried out.
To this end, in the process surrounding the entire intelligent development of security, it is the ecological evolution of the entire industry chain from collection to processing, transmission, storage, and analysis. The evolution of this industry is to drive the upgrading of equipment and systems. motivation. In this process, mainstream equipment solution providers have made great efforts to deploy and achieved good results in actual combat. The industry threshold for this particular application may bring greater shock to the market structure.
The above is the detailed content of Artificial intelligence is ready to take off, security meets opportunities and challenges. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
This site reported on June 27 that Jianying is a video editing software developed by FaceMeng Technology, a subsidiary of ByteDance. It relies on the Douyin platform and basically produces short video content for users of the platform. It is compatible with iOS, Android, and Windows. , MacOS and other operating systems. Jianying officially announced the upgrade of its membership system and launched a new SVIP, which includes a variety of AI black technologies, such as intelligent translation, intelligent highlighting, intelligent packaging, digital human synthesis, etc. In terms of price, the monthly fee for clipping SVIP is 79 yuan, the annual fee is 599 yuan (note on this site: equivalent to 49.9 yuan per month), the continuous monthly subscription is 59 yuan per month, and the continuous annual subscription is 499 yuan per year (equivalent to 41.6 yuan per month) . In addition, the cut official also stated that in order to improve the user experience, those who have subscribed to the original VIP
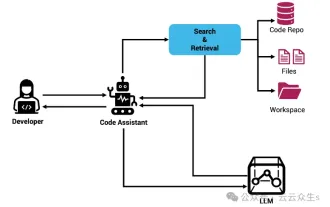 Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Improve developer productivity, efficiency, and accuracy by incorporating retrieval-enhanced generation and semantic memory into AI coding assistants. Translated from EnhancingAICodingAssistantswithContextUsingRAGandSEM-RAG, author JanakiramMSV. While basic AI programming assistants are naturally helpful, they often fail to provide the most relevant and correct code suggestions because they rely on a general understanding of the software language and the most common patterns of writing software. The code generated by these coding assistants is suitable for solving the problems they are responsible for solving, but often does not conform to the coding standards, conventions and styles of the individual teams. This often results in suggestions that need to be modified or refined in order for the code to be accepted into the application
 Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
To learn more about AIGC, please visit: 51CTOAI.x Community https://www.51cto.com/aigc/Translator|Jingyan Reviewer|Chonglou is different from the traditional question bank that can be seen everywhere on the Internet. These questions It requires thinking outside the box. Large Language Models (LLMs) are increasingly important in the fields of data science, generative artificial intelligence (GenAI), and artificial intelligence. These complex algorithms enhance human skills and drive efficiency and innovation in many industries, becoming the key for companies to remain competitive. LLM has a wide range of applications. It can be used in fields such as natural language processing, text generation, speech recognition and recommendation systems. By learning from large amounts of data, LLM is able to generate text
 Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Large Language Models (LLMs) are trained on huge text databases, where they acquire large amounts of real-world knowledge. This knowledge is embedded into their parameters and can then be used when needed. The knowledge of these models is "reified" at the end of training. At the end of pre-training, the model actually stops learning. Align or fine-tune the model to learn how to leverage this knowledge and respond more naturally to user questions. But sometimes model knowledge is not enough, and although the model can access external content through RAG, it is considered beneficial to adapt the model to new domains through fine-tuning. This fine-tuning is performed using input from human annotators or other LLM creations, where the model encounters additional real-world knowledge and integrates it
 To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
Editor |ScienceAI Question Answering (QA) data set plays a vital role in promoting natural language processing (NLP) research. High-quality QA data sets can not only be used to fine-tune models, but also effectively evaluate the capabilities of large language models (LLM), especially the ability to understand and reason about scientific knowledge. Although there are currently many scientific QA data sets covering medicine, chemistry, biology and other fields, these data sets still have some shortcomings. First, the data form is relatively simple, most of which are multiple-choice questions. They are easy to evaluate, but limit the model's answer selection range and cannot fully test the model's ability to answer scientific questions. In contrast, open-ended Q&A
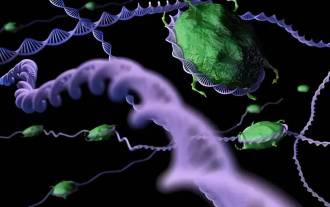 SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
Editor | KX In the field of drug research and development, accurately and effectively predicting the binding affinity of proteins and ligands is crucial for drug screening and optimization. However, current studies do not take into account the important role of molecular surface information in protein-ligand interactions. Based on this, researchers from Xiamen University proposed a novel multi-modal feature extraction (MFE) framework, which for the first time combines information on protein surface, 3D structure and sequence, and uses a cross-attention mechanism to compare different modalities. feature alignment. Experimental results demonstrate that this method achieves state-of-the-art performance in predicting protein-ligand binding affinities. Furthermore, ablation studies demonstrate the effectiveness and necessity of protein surface information and multimodal feature alignment within this framework. Related research begins with "S
 Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Machine learning is an important branch of artificial intelligence that gives computers the ability to learn from data and improve their capabilities without being explicitly programmed. Machine learning has a wide range of applications in various fields, from image recognition and natural language processing to recommendation systems and fraud detection, and it is changing the way we live. There are many different methods and theories in the field of machine learning, among which the five most influential methods are called the "Five Schools of Machine Learning". The five major schools are the symbolic school, the connectionist school, the evolutionary school, the Bayesian school and the analogy school. 1. Symbolism, also known as symbolism, emphasizes the use of symbols for logical reasoning and expression of knowledge. This school of thought believes that learning is a process of reverse deduction, through existing
 SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
According to news from this site on August 1, SK Hynix released a blog post today (August 1), announcing that it will attend the Global Semiconductor Memory Summit FMS2024 to be held in Santa Clara, California, USA from August 6 to 8, showcasing many new technologies. generation product. Introduction to the Future Memory and Storage Summit (FutureMemoryandStorage), formerly the Flash Memory Summit (FlashMemorySummit) mainly for NAND suppliers, in the context of increasing attention to artificial intelligence technology, this year was renamed the Future Memory and Storage Summit (FutureMemoryandStorage) to invite DRAM and storage vendors and many more players. New product SK hynix launched last year





