You can do machine learning using just SQL
The MindsDB[1] project I saw on GitHub recently made my eyes light up. It can perform machine learning related operations in the database. In other words, it can be built, trained, optimized and deployed using only SQL. With machine learning models, to get predictions, just query the data and the ML model.
MindsDB brings machine learning to the database by adopting the concept of AI tables. AI tables are machine learning models stored as virtual tables in a database. They help in making predictions based on data. You can perform time series, regression, and classification predictions in your database and get output almost instantly by querying an AI table using simple SQL statements.
Next, let’s look at a simple example provided by the official.
1. Apply for a free MindsDB cloud account so that you can experience it immediately. If you prefer local deployment, you can install their Docker version.
2. Connect to MindsDB from SQL client.
3. Use CREATE DATABASE to connect to the database. MindsDB has a sample database ready to use. Please use the CREATE DATABASE statement, as shown below:
CREATE DATABASE example_data
WITH ENGINE = "postgres",
PARAMETERS = {
"user": "demo_user",
"password": "demo_password",
"host": "3.220.66.106",
"port": "5432",
"database": "demo"
};After execution, you can get the following results:
Query OK, 0 rows affected (3.22 sec)
4. You can use standard SQL to preview the data, as shown below:
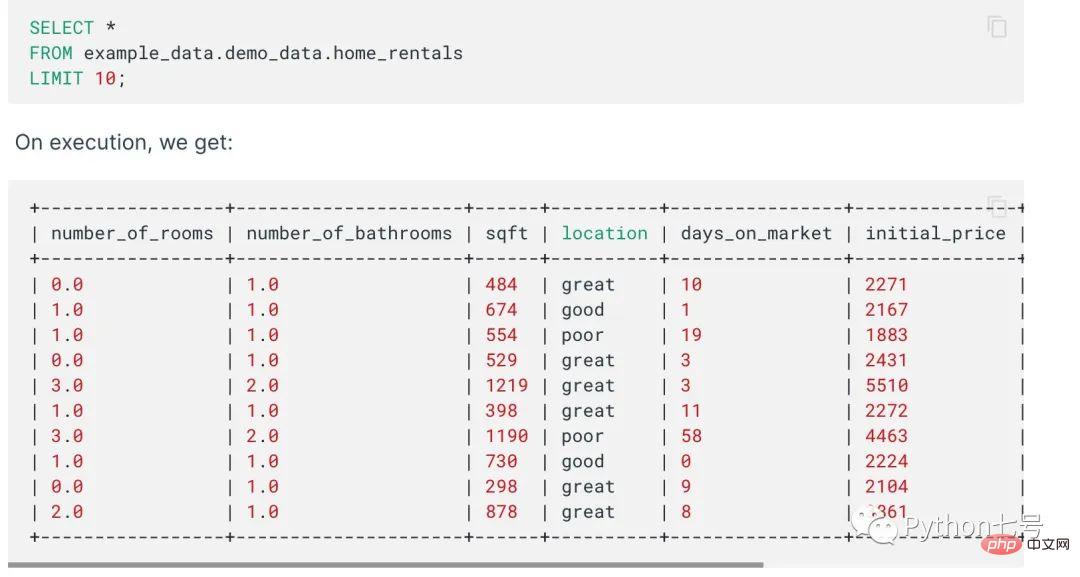
5. Use CREATE PREDICTOR to create a predictor:
CREATE PREDICTOR mindsdb.home_rentals_predictor FROM example_data (SELECT * FROM demo_data.home_rentals) PREDICT rental_price;
After execution:
Query OK, 0 rows affected (9.79 sec)
6. Check the status of the predictor:
SELECT status FROM mindsdb.predictors WHERE name='home_rentals_predictor';
You will get the status of training or completed:
+----------+ | status | +----------+ | training | +----------+
or
+----------+ | status | +----------+ | complete | +----------+
7. Execute prediction
The SELECT statement allows you to predict based on features, where the features are The input variable or column used to make the prediction. Now predict how much a 1000 square foot house with two bathrooms will rent for.
SELECT rental_price FROM mindsdb.home_rentals_predictor WHERE number_of_bathrooms=2 AND sqft=1000;
The results are as follows:
+--------------+ | rental_price | +--------------+ | 1130 | +--------------+
At this step, you have successfully trained a prediction model using SQL and obtained predicted data!
Features
1. Automatic data preprocessing, feature engineering and encoding
2. Classification, regression, time series tasks
3. No need for "traditional Deploy" to put the model into production
4. Get the model accuracy score and confidence interval for each prediction
5. You can join the ML model with existing data
6. Anomaly detection
7. Model interpretability analysis
8. Support GPU training
Support integration with the following databases:

Final words
It is really convenient to use machine learning using only SQL. For the technical details of MindsDB, you can visit the official document [2]. If it is helpful, please click to share with more friend.
Reference materials:
[1]MindsDB: https://github.com/mindsdb/mindsdb
[2]Documentation: docs.mindsdb.com
The above is the detailed content of You can do machine learning using just SQL. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1379
1379
 52
52
 Debian mail server firewall configuration tips
Apr 13, 2025 am 11:42 AM
Debian mail server firewall configuration tips
Apr 13, 2025 am 11:42 AM
Configuring a Debian mail server's firewall is an important step in ensuring server security. The following are several commonly used firewall configuration methods, including the use of iptables and firewalld. Use iptables to configure firewall to install iptables (if not already installed): sudoapt-getupdatesudoapt-getinstalliptablesView current iptables rules: sudoiptables-L configuration
 How to set the Debian Apache log level
Apr 13, 2025 am 08:33 AM
How to set the Debian Apache log level
Apr 13, 2025 am 08:33 AM
This article describes how to adjust the logging level of the ApacheWeb server in the Debian system. By modifying the configuration file, you can control the verbose level of log information recorded by Apache. Method 1: Modify the main configuration file to locate the configuration file: The configuration file of Apache2.x is usually located in the /etc/apache2/ directory. The file name may be apache2.conf or httpd.conf, depending on your installation method. Edit configuration file: Open configuration file with root permissions using a text editor (such as nano): sudonano/etc/apache2/apache2.conf
 How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
How debian readdir integrates with other tools
Apr 13, 2025 am 09:42 AM
The readdir function in the Debian system is a system call used to read directory contents and is often used in C programming. This article will explain how to integrate readdir with other tools to enhance its functionality. Method 1: Combining C language program and pipeline First, write a C program to call the readdir function and output the result: #include#include#include#includeintmain(intargc,char*argv[]){DIR*dir;structdirent*entry;if(argc!=2){
 How to optimize the performance of debian readdir
Apr 13, 2025 am 08:48 AM
How to optimize the performance of debian readdir
Apr 13, 2025 am 08:48 AM
In Debian systems, readdir system calls are used to read directory contents. If its performance is not good, try the following optimization strategy: Simplify the number of directory files: Split large directories into multiple small directories as much as possible, reducing the number of items processed per readdir call. Enable directory content caching: build a cache mechanism, update the cache regularly or when directory content changes, and reduce frequent calls to readdir. Memory caches (such as Memcached or Redis) or local caches (such as files or databases) can be considered. Adopt efficient data structure: If you implement directory traversal by yourself, select more efficient data structures (such as hash tables instead of linear search) to store and access directory information
 How to implement file sorting by debian readdir
Apr 13, 2025 am 09:06 AM
How to implement file sorting by debian readdir
Apr 13, 2025 am 09:06 AM
In Debian systems, the readdir function is used to read directory contents, but the order in which it returns is not predefined. To sort files in a directory, you need to read all files first, and then sort them using the qsort function. The following code demonstrates how to sort directory files using readdir and qsort in Debian system: #include#include#include#include#include//Custom comparison function, used for qsortintcompare(constvoid*a,constvoid*b){returnstrcmp(*(
 Debian mail server SSL certificate installation method
Apr 13, 2025 am 11:39 AM
Debian mail server SSL certificate installation method
Apr 13, 2025 am 11:39 AM
The steps to install an SSL certificate on the Debian mail server are as follows: 1. Install the OpenSSL toolkit First, make sure that the OpenSSL toolkit is already installed on your system. If not installed, you can use the following command to install: sudoapt-getupdatesudoapt-getinstallopenssl2. Generate private key and certificate request Next, use OpenSSL to generate a 2048-bit RSA private key and a certificate request (CSR): openss
 How to perform digital signature verification with Debian OpenSSL
Apr 13, 2025 am 11:09 AM
How to perform digital signature verification with Debian OpenSSL
Apr 13, 2025 am 11:09 AM
Using OpenSSL for digital signature verification on Debian systems, you can follow these steps: Preparation to install OpenSSL: Make sure your Debian system has OpenSSL installed. If not installed, you can use the following command to install it: sudoaptupdatesudoaptininstallopenssl to obtain the public key: digital signature verification requires the signer's public key. Typically, the public key will be provided in the form of a file, such as public_key.pe
 How Debian OpenSSL prevents man-in-the-middle attacks
Apr 13, 2025 am 10:30 AM
How Debian OpenSSL prevents man-in-the-middle attacks
Apr 13, 2025 am 10:30 AM
In Debian systems, OpenSSL is an important library for encryption, decryption and certificate management. To prevent a man-in-the-middle attack (MITM), the following measures can be taken: Use HTTPS: Ensure that all network requests use the HTTPS protocol instead of HTTP. HTTPS uses TLS (Transport Layer Security Protocol) to encrypt communication data to ensure that the data is not stolen or tampered during transmission. Verify server certificate: Manually verify the server certificate on the client to ensure it is trustworthy. The server can be manually verified through the delegate method of URLSession




