 Technology peripherals
Technology peripherals
 AI
AI
 Awakening of Digital Self-Defense Will Privacy Technology Kill Artificial Intelligence?
Awakening of Digital Self-Defense Will Privacy Technology Kill Artificial Intelligence?
Awakening of Digital Self-Defense Will Privacy Technology Kill Artificial Intelligence?
The development and application of artificial intelligence requires the use of large amounts of data. The more data you feed machine learning algorithms, the better they can discover patterns, make decisions, predict behavior, personalize content, diagnose medical conditions, achieve intelligence, and detect cyber threats and fraud.
In fact, artificial intelligence and data have reached such a relationship: "Algorithms without data are blind, and data without algorithms are stupid." However, the use of artificial intelligence technology may face risks, not Everyone wants to share their information or data, at least under the current rules of digital engagement. Therefore, some digital self-defense measures are required.

Some people completely cut off contact with the outside world and become digital hermits; others play it safe and use digital self-defense, a privacy-enhancing technology (PET), to respond to digital leaks.
People who use digital self-defense distrust website privacy notices and instead use tools like Privacy Level Extension to verify them. Instead of communicating their preferences, they use specialized tools—such as AI-powered privacy-preserving search engines and browsers—to conduct anonymous searches. These tools block invisible trackers from tracking across pages and help them explore the world, collaborate, and store data in new ways.
The Rising Digital Self-Defense
People can adopt some tools to deal with the collection and analysis of privacy by artificial intelligence algorithms. This is called digital self-defense, or also known as surveillance self-defense.
Users who adopt digital self-defense are often tired of the ubiquitous tracking of their online behavior that has even entered their offline lives. Digital self-defense is not an act of espionage, but self-protection of privacy.
This behavior began with the U.S. government’s sweeping surveillance program revealed by former U.S. agent Edward Snowden in 2013, which gave the NSA unprecedented access to people’s communications and information, including from Apple , steal emails, photos, videos, real-time chat and other information from the servers of technology giants such as Google, Skype and Facebook.
Similarly intrusive tactics of the British intelligence agency GCHQ were also disclosed, which triggered a higher awareness of privacy security, changed the development trajectory of EU data protection regulations, and promoted the implementation of consumer-oriented regulations. central, privacy-centric culture such as GDPR regulations.
Tech giants are scrambling to prove their privacy credentials, making encryption the default and declaring user privacy a priority. They position themselves as trusted data guardians who consumers can trust without having to defend themselves digitally.
But the Cambridge Analytica data breach scandal in 2018 revealed something that may be even more disturbing than government surveillance: "surveillance capitalism." Driven by adtech, people's digital identities are scraped, packaged, analyzed, profiled, auctioned, exchanged, and weaponized by online trackers and improper data to provide "precision marketing" to influence people's consumer behavior.
It turns out that Amazon may know people better than they know themselves. Facebook can predict what people will say next on social media, and what’s even more frightening is that it can predict voters’ voting tendencies. The Cambridge scandal revealed how ad tech "microtargeting" was combined with fake news and psychological warfare tactics to sway voters' decisions, leading Facebook Inc to ban political ads from its platform earlier this year.
The new darling of ad tech is location-based marketing, which tracks and maps users’ behavior, tracking them into the offline world and inferring intimate details by combining app data with data from other sources they collect and compile. to create rich profiles and segment users by race, personality, financial status, age, eating habits, substance abuse history, political affiliation, social networks, social networks, etc., and then peddle them on the dark web on real-time bidding platforms , so it may have adverse effects.
People
And ad tech collecting personal data isn’t always accurate, and targeting decisions can be offensive.
For example, bail bond ads in the United States target users with African-American names, and big brands such as Pepsi-Cola are promoted on extremely radical websites. A social media user who said she was constantly bombarded with parenting ads during her pregnancy and miscarriage publicly called on tech giants to fix their algorithm, saying “the algorithm was smart enough to know I was pregnant. And after I miscarried, it sent me Sending hospital ads, that's creepy."
Precision marketing is effective, but it can also be harmful because it doesn't really work. Anthropologist Tricia Wang points out that this is commodifying human relationships at the expense of customer understanding. She said that 70% of CMOs believe that ad technology does not provide valuable customer insights. Big data gives a big picture (it’s an incomplete and inaccurate picture) but lacks the human narrative.
Ironically, ad tech is in danger of purging customer-centricity from marketing because it cannot see the “human zeros and ones.”
Learn Digital Self-Defense
Pernille Tranberg, co-founder of Data Ethics, is helping consumers and businesses find win-win alternatives to surveillance. She teaches consumers the basics of digital self-defense so they can protect their data using tools like Digi.Me and Tapx and trade it for fair market value on their own terms.
Website tools like Blockthrough block unknown or unsafe third-party trackers while allowing privacy-friendly trackers. Brave helps businesses generate more browsing revenue by rewarding visits so visitors can get paid for viewing privacy-friendly ads. Analytics providers like Matomo provide website owners with the rich data they have, as well as the privacy controls they can take advantage of.
Is there a confrontational relationship between consumers and advertisers? Yes, but not entirely. Advertisers need to respect people's choices and not disable ad blockers or trick users into agreeing to deceptive interfaces and black box models. They should work together, not against each other, and advertisers need to understand their customers, otherwise they will ultimately fail.
Will privacy kill artificial intelligence?
It can be seen from the above that if people are not careful, advertising technology that uses artificial intelligence to analyze data can invade their privacy. For this reason people want to take back their agency. They are tired of being spied on and are monitoring advertiser behavior in turn.
Data shows that 1.7 billion people now use ad blocking tools to block ads, which is "the largest boycott in human history." As companies like Apple and Google move away from third-party cookies, advertisers will need to find new ways to leverage consumer data while maintaining trust.
Privacy security makes artificial intelligence human, and it can save ad tech. For example, privacy-friendly tools level the playing field and can encourage people to share more information. Advertisers will analyze anonymized or encrypted data and reprogram it into artificial intelligence systems to unlock false customer insights that ad tech cannot provide.
In short, people’s awareness of digital self-defense is awakening, and the traditional artificial intelligence method of abusing data needs to evolve!
The above is the detailed content of Awakening of Digital Self-Defense Will Privacy Technology Kill Artificial Intelligence?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1664
1664
 14
14
 1423
1423
 52
52
 1318
1318
 25
25
 1269
1269
 29
29
 1248
1248
 24
24
 Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
This site reported on June 27 that Jianying is a video editing software developed by FaceMeng Technology, a subsidiary of ByteDance. It relies on the Douyin platform and basically produces short video content for users of the platform. It is compatible with iOS, Android, and Windows. , MacOS and other operating systems. Jianying officially announced the upgrade of its membership system and launched a new SVIP, which includes a variety of AI black technologies, such as intelligent translation, intelligent highlighting, intelligent packaging, digital human synthesis, etc. In terms of price, the monthly fee for clipping SVIP is 79 yuan, the annual fee is 599 yuan (note on this site: equivalent to 49.9 yuan per month), the continuous monthly subscription is 59 yuan per month, and the continuous annual subscription is 499 yuan per year (equivalent to 41.6 yuan per month) . In addition, the cut official also stated that in order to improve the user experience, those who have subscribed to the original VIP
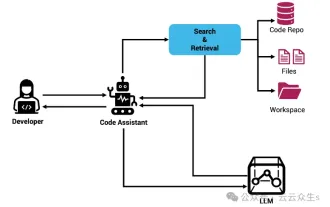 Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Improve developer productivity, efficiency, and accuracy by incorporating retrieval-enhanced generation and semantic memory into AI coding assistants. Translated from EnhancingAICodingAssistantswithContextUsingRAGandSEM-RAG, author JanakiramMSV. While basic AI programming assistants are naturally helpful, they often fail to provide the most relevant and correct code suggestions because they rely on a general understanding of the software language and the most common patterns of writing software. The code generated by these coding assistants is suitable for solving the problems they are responsible for solving, but often does not conform to the coding standards, conventions and styles of the individual teams. This often results in suggestions that need to be modified or refined in order for the code to be accepted into the application
 Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
To learn more about AIGC, please visit: 51CTOAI.x Community https://www.51cto.com/aigc/Translator|Jingyan Reviewer|Chonglou is different from the traditional question bank that can be seen everywhere on the Internet. These questions It requires thinking outside the box. Large Language Models (LLMs) are increasingly important in the fields of data science, generative artificial intelligence (GenAI), and artificial intelligence. These complex algorithms enhance human skills and drive efficiency and innovation in many industries, becoming the key for companies to remain competitive. LLM has a wide range of applications. It can be used in fields such as natural language processing, text generation, speech recognition and recommendation systems. By learning from large amounts of data, LLM is able to generate text
 Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Large Language Models (LLMs) are trained on huge text databases, where they acquire large amounts of real-world knowledge. This knowledge is embedded into their parameters and can then be used when needed. The knowledge of these models is "reified" at the end of training. At the end of pre-training, the model actually stops learning. Align or fine-tune the model to learn how to leverage this knowledge and respond more naturally to user questions. But sometimes model knowledge is not enough, and although the model can access external content through RAG, it is considered beneficial to adapt the model to new domains through fine-tuning. This fine-tuning is performed using input from human annotators or other LLM creations, where the model encounters additional real-world knowledge and integrates it
 Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Machine learning is an important branch of artificial intelligence that gives computers the ability to learn from data and improve their capabilities without being explicitly programmed. Machine learning has a wide range of applications in various fields, from image recognition and natural language processing to recommendation systems and fraud detection, and it is changing the way we live. There are many different methods and theories in the field of machine learning, among which the five most influential methods are called the "Five Schools of Machine Learning". The five major schools are the symbolic school, the connectionist school, the evolutionary school, the Bayesian school and the analogy school. 1. Symbolism, also known as symbolism, emphasizes the use of symbols for logical reasoning and expression of knowledge. This school of thought believes that learning is a process of reverse deduction, through existing
 To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
Editor |ScienceAI Question Answering (QA) data set plays a vital role in promoting natural language processing (NLP) research. High-quality QA data sets can not only be used to fine-tune models, but also effectively evaluate the capabilities of large language models (LLM), especially the ability to understand and reason about scientific knowledge. Although there are currently many scientific QA data sets covering medicine, chemistry, biology and other fields, these data sets still have some shortcomings. First, the data form is relatively simple, most of which are multiple-choice questions. They are easy to evaluate, but limit the model's answer selection range and cannot fully test the model's ability to answer scientific questions. In contrast, open-ended Q&A
 SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
According to news from this site on August 1, SK Hynix released a blog post today (August 1), announcing that it will attend the Global Semiconductor Memory Summit FMS2024 to be held in Santa Clara, California, USA from August 6 to 8, showcasing many new technologies. generation product. Introduction to the Future Memory and Storage Summit (FutureMemoryandStorage), formerly the Flash Memory Summit (FlashMemorySummit) mainly for NAND suppliers, in the context of increasing attention to artificial intelligence technology, this year was renamed the Future Memory and Storage Summit (FutureMemoryandStorage) to invite DRAM and storage vendors and many more players. New product SK hynix launched last year
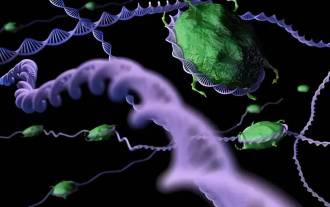 SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
Editor | KX In the field of drug research and development, accurately and effectively predicting the binding affinity of proteins and ligands is crucial for drug screening and optimization. However, current studies do not take into account the important role of molecular surface information in protein-ligand interactions. Based on this, researchers from Xiamen University proposed a novel multi-modal feature extraction (MFE) framework, which for the first time combines information on protein surface, 3D structure and sequence, and uses a cross-attention mechanism to compare different modalities. feature alignment. Experimental results demonstrate that this method achieves state-of-the-art performance in predicting protein-ligand binding affinities. Furthermore, ablation studies demonstrate the effectiveness and necessity of protein surface information and multimodal feature alignment within this framework. Related research begins with "S



