The hot GPT-4 is here!
On March 14, the artificial intelligence company OpenAI released the upgraded version GPT-4 of ChatGPT (GPT-3.5 stage), which once again ushered in "explosive hot discussion" on the ChatGPT topic that had been slightly silent. It became a hot search on social platforms in suspense. Topics such as "AI will eventually replace humans" and "90% of humans in countries with strong GPP-4 exam ability" have attracted more and more attention from users.

Compared with the previous ChatGPT, this upgrade of GPT-4 can be called a "heavyweight": it adopts a "super multi-modal model" and the answer accuracy is It has been greatly improved; the output text expansion capability has been enhanced, and the processing limit has been increased to 2.5W words; image recognition has been added on the basis of pure text input; creativity has been greatly improved, and it can handle more subtle instructions...
Compared with ChatGPT, GPT-4 is so good, but the terrible result is: the OpenAI payment system crashed due to users' crazy orders.
After throwing away Chat, GPT-4 has become more powerful
If ChatGPT based on the GPT-3.5 model is still a "poor student" hovering at the passing line, then The strength of GPT-4 is expected to enter the ranks of "top students". It is not only more intelligent, but also more difficult to be "cheated".
After throwing away the prefix of Chat, GPT-4’s capabilities have changed significantly. Simply put, as OpenAI continues to expand in the direction of deep learning, GPT-4 has taken a big step in the direction of being "more human-like". It has even participated in the Uniform Bar Exam and law school admissions. Examinations such as LSAT, with scores ranking in the top 20%; there are also users who use GPT-4 to live broadcast on YouTube to write articles, write code, file taxes, write poetry, tell jokes...
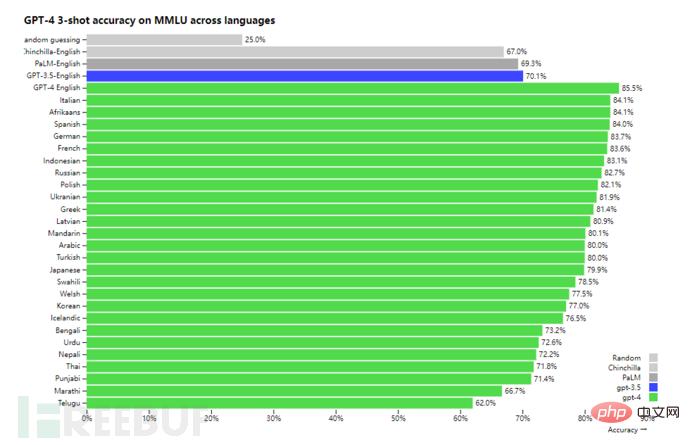
By conducting tests in 26 languages In the test, GPT-4 outperformed other large language models such as GPT-3.5 in 24 languages, including low-resource languages such as Latvian, Welsh and Swahili, among which the accuracy of Chinese recognition reached 80.1% (below).
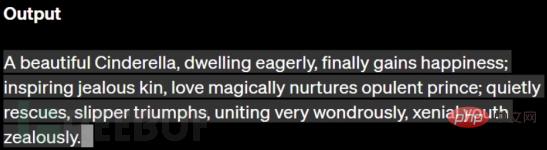
OpenAI demonstrated a summary of the story of "Cinderella" written in 26 words using GPT-4. The first letters of these 26 words exactly correspond to the 26 letters starting from The correct ordering from A to Z is enough to prove the power of GPT-4 in terms of vocabulary and language creation.
But the biggest update is that GPT-4 supports image recognition, which can give logical answers based on understanding the content of the image. For example, when a user asks what is special about the picture below, GPT-4 can directly describe it as "a man ironing clothes on the ironing board on the roof of a moving taxi."

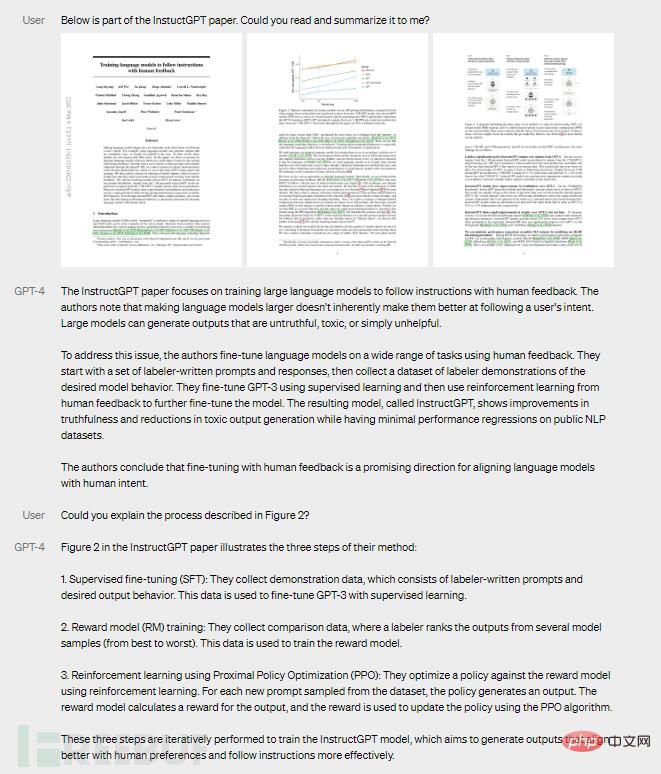
In another example, GPT-4 can provide a summary based on "understanding" the paper according to user requirements, and can provide a summary of one of the experiments. A concise description of the process.
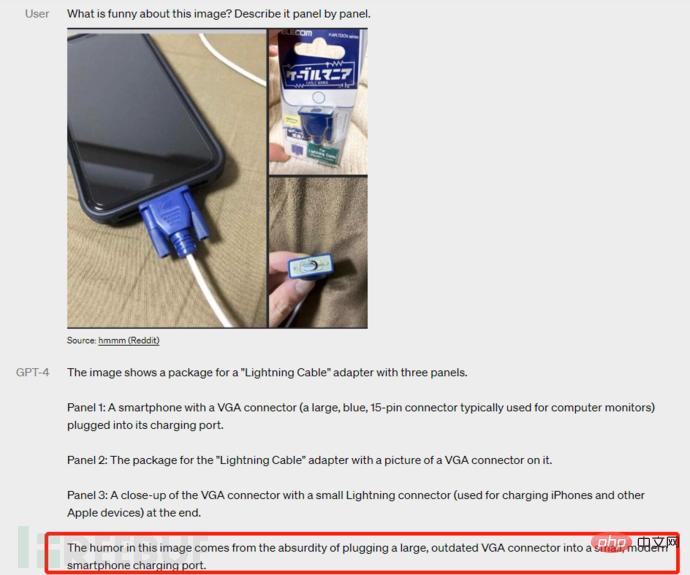
In addition, GPT-4 can also understand to a certain extent the popular funny "memes" on the Internet. For example, it can describe the funny thing about the picture below. The absurdity of plugging a large, outdated VGA connector into a small, modern smartphone charging port."
Will GPT-4 become a sharp sword in the hands of hackers?
First of all, we must be aware of a problem. Will the increasingly intelligent GPT-4 bring more terrible security risks, or become a "sharp sword" in the hands of cybercriminal organizations?
In the ChatGPT version, FreeBuf has deeply discussed its use in cybercrimes and the security risks it may bring to cyberspace.
The first is its own risks.
For example, security experts found text that was very similar to internal company secrets in the content generated by ChatGPT. The reason may be that Amazon employees entered the company's internal data information when using ChatGPT to generate code and text. Then, in GPT-4, such security risks will still exist, and major giants will still defend GPT.
In terms of network security policy, GPT-4 also faces the danger of stepping on the red line. For example, whether it violates the "minimum data" principle of GDPR, whether it meets the "right to be forgotten" or "right to delete", whether the use of public data is compliant, and whether the collection of academic and intellectual property information is suitable and consistent with current laws, regulations.
At present, my country's "Cybersecurity Law", "Data Protection Law" and "Personal Information Protection Law" have detailed regulations on the collection and use of data. Judging from the existing situation alone, it is obvious that GPT-4 cannot meet all requirements. these requirements. Moreover, in the future, the global legal system will be further refined in the direction of "data protection", and GPT will face more severe compliance pressure at that time.
Secondly, there may be more hidden vulnerabilities in using GPT-4 to edit code.
In the ChatGPT-3.5 stage, some companies and developers are already trying to use it to write code and troubleshoot vulnerabilities. In a Kaspersky experiment, analysts found that ChatGPT can be used to gather forensic information for companies that do not run endpoint detection and response (EDR) systems, detect code obfuscation, or reverse engineer code binaries.
The smarter GPT-4 has also been given high hopes by many people. When more and more developers use GPT-4 to write code, the hidden vulnerabilities will become more terrifying time bombs. Being exploited by attackers will bring untold disasters to the entire network security space, especially in the field of supply chain security, which requires heightened vigilance.
Finally, how to prevent GPT-4 from being used by hackers, thus bringing new pressure to network security defense.
A very obvious fact is that since the ChatGPT stage, there have been more and more cases of GPT being used in black industry, cybercrime, hacker attacks and other fields, and it may even become the norm in the future.
For example, researchers from Cybernews once discovered that ChatGPT can be used by hackers to find security vulnerabilities in websites. With their help, the researchers conducted a penetration test on an ordinary website and combined with ChatGPT to provide Suggestions and code change examples complete the hack.
ChatGPT already has such capabilities, let alone the more intelligent GPT-4? It seems difficult to use GPT-4 to substantially strengthen the network security system in the short term, but its use in cyber crimes is imminent. How to deal with similar security risks has become an issue that must be considered now.
Of course, OpenAI is also continuing to work hard on security. For example, they hired more than 50 experts from the fields of artificial intelligence docking risks, cybersecurity, biorisks, trust and security, and international security to conduct adversarial testing of the model and train various high-risk scenarios to provide guidance for mitigation measures and model development. Provide basis for improvement. For example, by collecting additional specialized data to improve GPT-4's ability to reject requests about how to synthesize hazardous chemicals.
But relying on these alone is obviously unable to meet the security requirements. This also means that we need to enhance the security capabilities of artificial intelligence represented by GPT-4 from many aspects, including formulating policies. regulations, and the use of technical means to curb the risks of evildoing, etc.
Written at the end
In any case, technological progress has an immeasurable effect on human development, but at the same time we need to have a clear understanding of risks. . In other words, we embrace GPT-4 with a positive attitude, but we must be prepared to deal with risks.
As a World War II leader said: We cannot change other people’s minds. Since they want to prepare for war, we must also prepare for war. The same is true for GPT-4, we cannot change others to use it for "evil", but we can decide how to use it for "good".
The sword of AI is also extremely sharp in the hands of network security.
We are ready!
The above is the detailed content of The hot GPT-4 is here!. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 What are the types of return values of c language function? Summary of types of return values of c language function?
Apr 03, 2025 pm 11:18 PM
What are the types of return values of c language function? Summary of types of return values of c language function?
Apr 03, 2025 pm 11:18 PM
The return value types of C language function include int, float, double, char, void and pointer types. int is used to return integers, float and double are used to return floats, and char returns characters. void means that the function does not return any value. The pointer type returns the memory address, be careful to avoid memory leakage.结构体或联合体可返回多个相关数据。
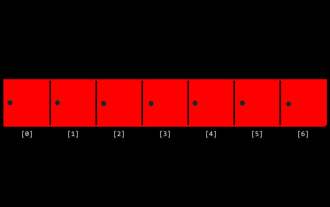 CS-Week 3
Apr 04, 2025 am 06:06 AM
CS-Week 3
Apr 04, 2025 am 06:06 AM
Algorithms are the set of instructions to solve problems, and their execution speed and memory usage vary. In programming, many algorithms are based on data search and sorting. This article will introduce several data retrieval and sorting algorithms. Linear search assumes that there is an array [20,500,10,5,100,1,50] and needs to find the number 50. The linear search algorithm checks each element in the array one by one until the target value is found or the complete array is traversed. The algorithm flowchart is as follows: The pseudo-code for linear search is as follows: Check each element: If the target value is found: Return true Return false C language implementation: #include#includeintmain(void){i
 How to use C language function pointer to find the maximum value of a one-dimensional array
Apr 03, 2025 pm 11:45 PM
How to use C language function pointer to find the maximum value of a one-dimensional array
Apr 03, 2025 pm 11:45 PM
Flexible application of function pointers: use comparison functions to find the maximum value of an array. First, define the comparison function type CompareFunc, and then write the comparison function compareMax(a, b). The findMax function accepts array, array size, and comparison function parameters, and uses the comparison function to loop to compare array elements to find the maximum value. This method has strong code reusability, reflects the idea of higher-order programming, and is conducive to solving more complex problems.
 What are c language function pointers and pointer functions? What's the difference?
Apr 03, 2025 pm 11:54 PM
What are c language function pointers and pointer functions? What's the difference?
Apr 03, 2025 pm 11:54 PM
A function pointer is a pointer to a function, and a pointer function is a function that returns a pointer. Function pointers point to functions, used to select and execute different functions; pointer functions return pointers to variables, arrays or other functions; when using function pointers, pay attention to parameter matching and checking pointer null values; when using pointer functions, pay attention to memory management and free dynamically allocated memory; understand the differences and characteristics of the two to avoid confusion and errors.
 What are the formats of function definition in C language?
Apr 03, 2025 pm 11:51 PM
What are the formats of function definition in C language?
Apr 03, 2025 pm 11:51 PM
The key elements of C function definition include: return type (defining the value returned by the function), function name (following the naming specification and determining the scope), parameter list (defining the parameter type, quantity and order accepted by the function) and function body (implementing the logic of the function). It is crucial to clarify the meaning and subtle relationship of these elements, and can help developers avoid "pits" and write more efficient and elegant code.
 What are the pointer parameters in the parentheses of the C language function?
Apr 03, 2025 pm 11:48 PM
What are the pointer parameters in the parentheses of the C language function?
Apr 03, 2025 pm 11:48 PM
The pointer parameters of C language function directly operate the memory area passed by the caller, including pointers to integers, strings, or structures. When using pointer parameters, you need to be careful to modify the memory pointed to by the pointer to avoid errors or memory problems. For double pointers to strings, modifying the pointer itself will lead to pointing to new strings, and memory management needs to be paid attention to. When handling pointer parameters to structures or arrays, you need to carefully check the pointer type and boundaries to avoid out-of-bounds access.
 Integers in C: a little history
Apr 04, 2025 am 06:09 AM
Integers in C: a little history
Apr 04, 2025 am 06:09 AM
Integers are the most basic data type in programming and can be regarded as the cornerstone of programming. The job of a programmer is to give these numbers meanings. No matter how complex the software is, it ultimately comes down to integer operations, because the processor only understands integers. To represent negative numbers, we introduced two's complement; to represent decimal numbers, we created scientific notation, so there are floating-point numbers. But in the final analysis, everything is still inseparable from 0 and 1. A brief history of integers In C, int is almost the default type. Although the compiler may issue a warning, in many cases you can still write code like this: main(void){return0;} From a technical point of view, this is equivalent to the following code: intmain(void){return0;}
 What do nested calls and recursive calls of c language functions mean respectively?
Apr 03, 2025 pm 11:09 PM
What do nested calls and recursive calls of c language functions mean respectively?
Apr 03, 2025 pm 11:09 PM
C language function calls can be divided into nested calls and recursive calls. Nested calls refer to calling other functions within a function, nesting them layer by layer. Recursive calls refer to the function itself calling itself, which can be used to deal with self-similar structure problems. The key difference is that the functions in nested calls are called in sequence, with independent interaction scopes, while the functions in recursive calls are constantly called, so you need to pay attention to the recursive basis and stack overflow issues. Which calling method to choose depends on the specific requirements and performance requirements of the problem.






