Artificial Intelligence in Cybersecurity: Pros and Cons

We can use artificial intelligence to automate complex, repetitive tasks faster than humans can.
Artificial intelligence technology can logically sort complex and repeated inputs. This is why artificial intelligence is used in facial recognition and self-driving cars. But this capability also paves the way for AI cybersecurity. This is particularly useful for assessing threats in complex organizations. When business structures are constantly changing, administrators often fail to identify weaknesses.
In addition, the network structure of enterprises is becoming more and more complex. This means there are more vulnerabilities that cybercriminals can exploit against us. We can see this in highly automated Manufacturing 3.0 enterprises or integrated companies such as the oil and gas industry. To this end, various security companies have developed AI cybersecurity tools to help protect businesses.
This article will take an in-depth look at what artificial intelligence is and how it is applied to cybersecurity. We will also look at the advantages and disadvantages of this promising technology. Next, let’s first take a look at what artificial intelligence is!
What is artificial intelligence?
Artificial intelligence is a rationalization method that uses statistical weighting matrices. This matrix is also called a neural network. You can first think of this network as a decision matrix, where the nodes have weighted biases for each filtering process. The neural network will receive a database of precompiled data. The data will also contain answers to potential questions that AI can solve. In this way, AI can become biased.
For example, a database containing different images. Suppose it has a face image and other watermelon images. Additionally, each image has a tag to check each item. As the AI "learns" whether its guesses are correct, the system increases node weights. This process continues until the system reaches a predefined error rate. This is often called deep learning, which refers to the creation of deep layers of decision-making.
Next, look at the steps used to process the data.
Key steps in artificial intelligence data processing
The entire data workflow can be condensed into the following process:
1. Input the sensor to receive data.
2. The data passes through the CPU and is redirected to the artificial intelligence process.
3. Data enters the statistical weighting matrix of the artificial intelligence solution. Each node processes this information and then makes a decision using each respective filter.
4. The data reaches the last node of the statistical weighting matrix. This determines the final decision.
However, this process is slightly different from deep learning. Step 1 will include data from the precompiled database, tagged with the correct response. Additionally, deep learning will repeat steps 1 to 4 to reach a predefined fault tolerance value.
Let’s look at this through an example of how to process AI data.
AI data filtering example
Suppose a picture reaches an AI node. This node will filter the data into a usable format, such as 255 grayscale. Then, a script is run to identify the characteristics. If these characteristics match other characteristics in the filter, the node can make a decision. For example, it will indicate whether it found a face or a watermelon.
Then, the data goes to the next node. This particular node can have a color filter confirming the first decision. This process continues until the data reaches the last node. At that point, the AI will make the final decision to ensure it finds a face or a watermelon.
The important thing is that artificial intelligence systems will always have a certain degree of error. Nothing is absolutely correct, ever. But sometimes, the error percentage is acceptable.
After understanding how artificial intelligence works, let’s take a look at artificial intelligence’s network security solutions.
Artificial Intelligence in Cybersecurity
Artificial intelligence in cybersecurity addresses the need to automatically assess threats in complex environments. Specifically, here are two AI use cases in cybersecurity:
1. Detect anomalies. Artificial intelligence often detects anomalies in the day-to-day operations of a network. This helps understand when and where users access the network. The gateway device also features AI integration for analytics. Some solutions lock out users if unusual behavior occurs. Other solutions only send alerts.
2. Classified data. Artificial intelligence is actually a classification utility. This speeds up the screening process for malware or bad behavior. This is useful in organizations with large amounts of data.
These are the two main uses of artificial intelligence in network security. Let’s take a look at its advantages and disadvantages!
The advantages and disadvantages of artificial intelligence
As before As mentioned, artificial intelligence has many benefits. It can run repetitive tasks to identify anomalies or classify data. That said, some big drawbacks may outweigh its benefits. So let’s look at the shortcomings.
AI Accuracy vs Resource Requirements
The first disadvantage is the accuracy of AI cybersecurity solutions. This accuracy also depends on many factors. This includes the size of the neural network and the decisions defined for filtering. It also depends on the number of iterations required to reach a predefined error rate.
Suppose there is a three-level decision tree. Each layer has multiple nodes for each decision path. Even though this is a fairly simple matrix, it requires a lot of calculations. The system's limited resources compromise the intelligence of the solution.
Artificial intelligence cybersecurity solution providers may hinder the intelligence/accuracy of their solutions to satisfy the target population. But sometimes, the problem isn't IQ. Instead, it has low latency and security vulnerabilities. When looking for AI cybersecurity solutions, consider its security within the network.
Static and Continuous Training
Once the artificial intelligence statistical weighting matrix is trained, it is usually not retrained in the service. This was found to be caused by a lack of available processing resources in the hardware. Sometimes the system learns something that makes the situation worse, making it less efficient. In contrast, humans learn iteratively. This means a lot of accidents. Therefore, solution providers must ensure that the software meets specification requirements during use.
Cybersecurity often needs to be updated to respond to new attacks. To do this, a lot of power is needed to train the AI. Additionally, AI cybersecurity vendors will need regular updates to address cyber threats.
That is, the artificial intelligence component of an artificial intelligence cybersecurity solution is used to classify data and evaluate anomalies in baseline data. Therefore, it does not cause problems with malware list updates. This means AI cybersecurity can still be used.
After reading the advantages and disadvantages of artificial intelligence network security, let’s take a look at some uses of this technology!
Where to find AI network security
As before As mentioned above, highly automated enterprise network security is the weakest. Generally speaking, automation environments overlap information technology (IT), operational technology (OT), and the Internet of Things (IoT). This is to increase productivity, reduce the unit cost of the product, and undercut the competition.
But this can also create loopholes. To this end, AI cybersecurity can be helpful in uncovering potential vulnerabilities in these companies. The solution is to either notify the administrator or apply the patch automatically.
However, this may not be enough. Cybercriminals are currently targeting large, highly integrated companies. To do this, they leverage OT without security. This OT is for wired networks to send commands to hardware, such as factory equipment. This means it never constituted a security vulnerability. But today, attackers use OT to gain access to the rest of the network or take factory equipment offline.
OT Risk Management for Manufacturing and Automated Factories
OT risk management tools are becoming more and more popular due to the above reasons. These systems effectively take a live clone of the production environment and then run countless simulations to find vulnerabilities.
Vulnerabilities are often found in the AI part of the system. In this case, the administrator will provide a solution. OT risk management software continuously operates as manufacturing plant schedules change to meet order, project, or supply needs.
In this case, the AI system uses known malware from antivirus lists to try to find an entry path into the system. This task requires the automated, repetitive capabilities of complex systems, which is ideally suited for artificial intelligence.
So, when should you implement AI cybersecurity?
When should you use AI cybersecurity
As mentioned above, businesses using manufacturing and factory equipment should Using artificial intelligence for cybersecurity. In most cases, one also needs to look for an OT risk management solution to reduce the risks associated with OT.
If enterprises use IoT and IT, they can also use artificial intelligence cybersecurity. In this way, the risk of network attacks can be reduced. IoT devices are often sold at a lower price than competitors, so the cost of adding adequate security measures is also eliminated.
Finally, even companies that only use IT can also use AI. Artificial intelligence can help assess irregular traffic to protect gateways. In addition, AI data analysis can also be used. This way, you can tell if someone is using the hardware maliciously.
In summary, that’s all about artificial intelligence network security, a brief summary!
Summary
We may use artificial intelligence wherever repetitive tasks need to be automated intelligent. Artificial intelligence also helps in decision-making on complex tasks. This is why many cybersecurity solution providers use artificial intelligence. In fact, these providers' tools help address the challenges of highly complex and poorly secured systems.
We can always benefit from AI cybersecurity, no matter how integrated the business technology is. AI capabilities are also great for classifying data using intelligent operations. This way, you can speed up your search for malware. AI cybersecurity can also help detect abnormal usage of the network.
The above is the detailed content of Artificial Intelligence in Cybersecurity: Pros and Cons. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1376
1376
 52
52
 Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
This site reported on June 27 that Jianying is a video editing software developed by FaceMeng Technology, a subsidiary of ByteDance. It relies on the Douyin platform and basically produces short video content for users of the platform. It is compatible with iOS, Android, and Windows. , MacOS and other operating systems. Jianying officially announced the upgrade of its membership system and launched a new SVIP, which includes a variety of AI black technologies, such as intelligent translation, intelligent highlighting, intelligent packaging, digital human synthesis, etc. In terms of price, the monthly fee for clipping SVIP is 79 yuan, the annual fee is 599 yuan (note on this site: equivalent to 49.9 yuan per month), the continuous monthly subscription is 59 yuan per month, and the continuous annual subscription is 499 yuan per year (equivalent to 41.6 yuan per month) . In addition, the cut official also stated that in order to improve the user experience, those who have subscribed to the original VIP
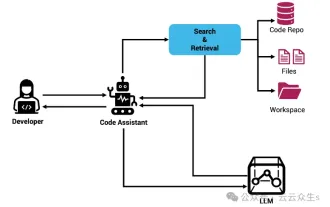 Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Improve developer productivity, efficiency, and accuracy by incorporating retrieval-enhanced generation and semantic memory into AI coding assistants. Translated from EnhancingAICodingAssistantswithContextUsingRAGandSEM-RAG, author JanakiramMSV. While basic AI programming assistants are naturally helpful, they often fail to provide the most relevant and correct code suggestions because they rely on a general understanding of the software language and the most common patterns of writing software. The code generated by these coding assistants is suitable for solving the problems they are responsible for solving, but often does not conform to the coding standards, conventions and styles of the individual teams. This often results in suggestions that need to be modified or refined in order for the code to be accepted into the application
 Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
To learn more about AIGC, please visit: 51CTOAI.x Community https://www.51cto.com/aigc/Translator|Jingyan Reviewer|Chonglou is different from the traditional question bank that can be seen everywhere on the Internet. These questions It requires thinking outside the box. Large Language Models (LLMs) are increasingly important in the fields of data science, generative artificial intelligence (GenAI), and artificial intelligence. These complex algorithms enhance human skills and drive efficiency and innovation in many industries, becoming the key for companies to remain competitive. LLM has a wide range of applications. It can be used in fields such as natural language processing, text generation, speech recognition and recommendation systems. By learning from large amounts of data, LLM is able to generate text
 Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Large Language Models (LLMs) are trained on huge text databases, where they acquire large amounts of real-world knowledge. This knowledge is embedded into their parameters and can then be used when needed. The knowledge of these models is "reified" at the end of training. At the end of pre-training, the model actually stops learning. Align or fine-tune the model to learn how to leverage this knowledge and respond more naturally to user questions. But sometimes model knowledge is not enough, and although the model can access external content through RAG, it is considered beneficial to adapt the model to new domains through fine-tuning. This fine-tuning is performed using input from human annotators or other LLM creations, where the model encounters additional real-world knowledge and integrates it
 To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
Editor |ScienceAI Question Answering (QA) data set plays a vital role in promoting natural language processing (NLP) research. High-quality QA data sets can not only be used to fine-tune models, but also effectively evaluate the capabilities of large language models (LLM), especially the ability to understand and reason about scientific knowledge. Although there are currently many scientific QA data sets covering medicine, chemistry, biology and other fields, these data sets still have some shortcomings. First, the data form is relatively simple, most of which are multiple-choice questions. They are easy to evaluate, but limit the model's answer selection range and cannot fully test the model's ability to answer scientific questions. In contrast, open-ended Q&A
 Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Machine learning is an important branch of artificial intelligence that gives computers the ability to learn from data and improve their capabilities without being explicitly programmed. Machine learning has a wide range of applications in various fields, from image recognition and natural language processing to recommendation systems and fraud detection, and it is changing the way we live. There are many different methods and theories in the field of machine learning, among which the five most influential methods are called the "Five Schools of Machine Learning". The five major schools are the symbolic school, the connectionist school, the evolutionary school, the Bayesian school and the analogy school. 1. Symbolism, also known as symbolism, emphasizes the use of symbols for logical reasoning and expression of knowledge. This school of thought believes that learning is a process of reverse deduction, through existing
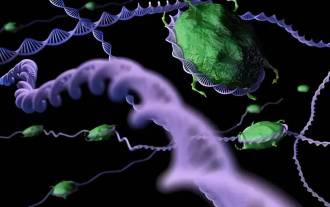 SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
Editor | KX In the field of drug research and development, accurately and effectively predicting the binding affinity of proteins and ligands is crucial for drug screening and optimization. However, current studies do not take into account the important role of molecular surface information in protein-ligand interactions. Based on this, researchers from Xiamen University proposed a novel multi-modal feature extraction (MFE) framework, which for the first time combines information on protein surface, 3D structure and sequence, and uses a cross-attention mechanism to compare different modalities. feature alignment. Experimental results demonstrate that this method achieves state-of-the-art performance in predicting protein-ligand binding affinities. Furthermore, ablation studies demonstrate the effectiveness and necessity of protein surface information and multimodal feature alignment within this framework. Related research begins with "S
 Laying out markets such as AI, GlobalFoundries acquires Tagore Technology's gallium nitride technology and related teams
Jul 15, 2024 pm 12:21 PM
Laying out markets such as AI, GlobalFoundries acquires Tagore Technology's gallium nitride technology and related teams
Jul 15, 2024 pm 12:21 PM
According to news from this website on July 5, GlobalFoundries issued a press release on July 1 this year, announcing the acquisition of Tagore Technology’s power gallium nitride (GaN) technology and intellectual property portfolio, hoping to expand its market share in automobiles and the Internet of Things. and artificial intelligence data center application areas to explore higher efficiency and better performance. As technologies such as generative AI continue to develop in the digital world, gallium nitride (GaN) has become a key solution for sustainable and efficient power management, especially in data centers. This website quoted the official announcement that during this acquisition, Tagore Technology’s engineering team will join GLOBALFOUNDRIES to further develop gallium nitride technology. G




