How to manage AI risk and safety?
Large, sensitive data sets are often used to train AI models, creating privacy and data leakage risks. The use of artificial intelligence increases an organization’s threat vectors and expands its attack surface. AI further creates new opportunities for benign errors to adversely impact models and business results.

Risks that are not understood cannot be mitigated. A recent Gartner survey of chief information security officers revealed that most organizations have not considered the new security and business risks posed by artificial intelligence or the new controls they must put in place to mitigate those risks. Artificial intelligence requires new risk and safety management measures and mitigation frameworks.
Here are the top five priorities security and risk leaders should focus on to effectively manage AI risk and security within their organizations:
1. Capture AI exposure
Machine learning models are opaque to most users, and unlike general software systems, their inner workings are unknown to even the most skilled experts. Data scientists and model developers often understand what their machine learning models are trying to do, but they cannot always decipher the internal structure or algorithmic means by which the model processes the data.
This lack of understanding severely limits an organization’s ability to manage AI risks. The first step in AI risk management is to list all AI models used in the organization, whether they are components of third-party software, developed in-house, or accessed through software-as-a-service applications. This should include identifying interdependencies between the various models. Models are then ranked based on operational impact, taking into account that risk management controls can be applied incrementally based on identified priorities.
Once the models are laid out, the next step is to make them as interpretable or explainable as possible. “Explainability” means the ability to generate details, reasons, or explanations that clarify the functionality of the model for a specific audience. This will provide risk and security managers with an environment to manage and mitigate business, social, liability and security risks arising from model outcomes.
2. Improve employee awareness through artificial intelligence risk education activities
Employee awareness is an important component of artificial intelligence risk management. First, let all players, including CISOs, chief privacy officers, chief data officers, and legal and compliance officers, recalibrate their mindsets about AI. They should understand that AI is “unlike any other application” – it poses unique risks and requires specific controls to mitigate such risks. Then, engage with business stakeholders to expand understanding of the AI risks that need to be managed.
Work with these stakeholders to determine the best way to build AI knowledge across teams and over time. For example, see if you can add a course on basic AI concepts to your enterprise’s learning management system. Work with application and data security departments to help develop AI knowledge among all organizational members.
3. Eliminate AI data exposure with a privacy plan
According to a recent Gartner survey, privacy and security have been viewed as artificial. The main obstacles to the realization of intelligence. Adopting data protection and privacy procedures can effectively eliminate the exposure of internal and shared data within AI.
There are a range of methods that can be used to access and share essential data while still meeting privacy and data protection requirements. Determine which data privacy technology, or combination of technologies, makes the most sense for your organization’s specific use cases. For example, investigate techniques such as data masking, synthetic data generation, or differential privacy.
Data privacy requirements should be met when exporting or importing data to external organizations. In these scenarios, techniques like fully homomorphic encryption and secure multi-party computation should be more useful than protecting data from internal users and data scientists.
4. Incorporate risk management into model operations
AI models require special-purpose processes as part of model operations or ModelOps to enable human Smart, reliable and efficient. As environmental factors continue to change, AI models must continuously monitor for business value leakage and unpredictable (and sometimes adverse) outcomes.
Effective monitoring requires an understanding of AI models. Dedicated risk management processes must become an integral part of ModelOps to make AI more trustworthy, accurate, fair, and resilient to adversarial attacks or benign errors.
Controls should be applied continuously—for example, throughout model development, testing and deployment, and ongoing operations. Effective controls will detect malicious behavior, benign errors, and unintended changes in AI data or models that lead to unfairness, corruption, inaccuracies, poor model performance and predictions, and other unintended consequences.
5. Use artificial intelligence security measures to deal with adversarial attacks
Detecting and blocking attacks on artificial intelligence requires new technologies. Malicious attacks on AI can result in significant organizational damage and loss, including financial, reputational, or data related to intellectual property, sensitive customer data, or proprietary data. Application leaders working with security must add controls to their AI applications to detect anomalous data input, malicious attacks, and benign input errors.
Implement a comprehensive set of traditional enterprise security controls around AI models and data, as well as new integrity measures for AI, such as training models that tolerate adversarial AI. Finally, use fraud, anomaly detection and bot detection technologies to prevent AI data poisoning or input error detection.
The above is the detailed content of How to manage AI risk and safety?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
This site reported on June 27 that Jianying is a video editing software developed by FaceMeng Technology, a subsidiary of ByteDance. It relies on the Douyin platform and basically produces short video content for users of the platform. It is compatible with iOS, Android, and Windows. , MacOS and other operating systems. Jianying officially announced the upgrade of its membership system and launched a new SVIP, which includes a variety of AI black technologies, such as intelligent translation, intelligent highlighting, intelligent packaging, digital human synthesis, etc. In terms of price, the monthly fee for clipping SVIP is 79 yuan, the annual fee is 599 yuan (note on this site: equivalent to 49.9 yuan per month), the continuous monthly subscription is 59 yuan per month, and the continuous annual subscription is 499 yuan per year (equivalent to 41.6 yuan per month) . In addition, the cut official also stated that in order to improve the user experience, those who have subscribed to the original VIP
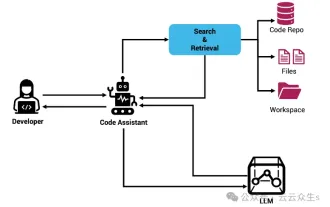 Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Context-augmented AI coding assistant using Rag and Sem-Rag
Jun 10, 2024 am 11:08 AM
Improve developer productivity, efficiency, and accuracy by incorporating retrieval-enhanced generation and semantic memory into AI coding assistants. Translated from EnhancingAICodingAssistantswithContextUsingRAGandSEM-RAG, author JanakiramMSV. While basic AI programming assistants are naturally helpful, they often fail to provide the most relevant and correct code suggestions because they rely on a general understanding of the software language and the most common patterns of writing software. The code generated by these coding assistants is suitable for solving the problems they are responsible for solving, but often does not conform to the coding standards, conventions and styles of the individual teams. This often results in suggestions that need to be modified or refined in order for the code to be accepted into the application
 Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
Seven Cool GenAI & LLM Technical Interview Questions
Jun 07, 2024 am 10:06 AM
To learn more about AIGC, please visit: 51CTOAI.x Community https://www.51cto.com/aigc/Translator|Jingyan Reviewer|Chonglou is different from the traditional question bank that can be seen everywhere on the Internet. These questions It requires thinking outside the box. Large Language Models (LLMs) are increasingly important in the fields of data science, generative artificial intelligence (GenAI), and artificial intelligence. These complex algorithms enhance human skills and drive efficiency and innovation in many industries, becoming the key for companies to remain competitive. LLM has a wide range of applications. It can be used in fields such as natural language processing, text generation, speech recognition and recommendation systems. By learning from large amounts of data, LLM is able to generate text
 Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Can fine-tuning really allow LLM to learn new things: introducing new knowledge may make the model produce more hallucinations
Jun 11, 2024 pm 03:57 PM
Large Language Models (LLMs) are trained on huge text databases, where they acquire large amounts of real-world knowledge. This knowledge is embedded into their parameters and can then be used when needed. The knowledge of these models is "reified" at the end of training. At the end of pre-training, the model actually stops learning. Align or fine-tune the model to learn how to leverage this knowledge and respond more naturally to user questions. But sometimes model knowledge is not enough, and although the model can access external content through RAG, it is considered beneficial to adapt the model to new domains through fine-tuning. This fine-tuning is performed using input from human annotators or other LLM creations, where the model encounters additional real-world knowledge and integrates it
 To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
Editor |ScienceAI Question Answering (QA) data set plays a vital role in promoting natural language processing (NLP) research. High-quality QA data sets can not only be used to fine-tune models, but also effectively evaluate the capabilities of large language models (LLM), especially the ability to understand and reason about scientific knowledge. Although there are currently many scientific QA data sets covering medicine, chemistry, biology and other fields, these data sets still have some shortcomings. First, the data form is relatively simple, most of which are multiple-choice questions. They are easy to evaluate, but limit the model's answer selection range and cannot fully test the model's ability to answer scientific questions. In contrast, open-ended Q&A
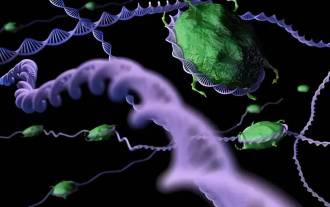 SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
Editor | KX In the field of drug research and development, accurately and effectively predicting the binding affinity of proteins and ligands is crucial for drug screening and optimization. However, current studies do not take into account the important role of molecular surface information in protein-ligand interactions. Based on this, researchers from Xiamen University proposed a novel multi-modal feature extraction (MFE) framework, which for the first time combines information on protein surface, 3D structure and sequence, and uses a cross-attention mechanism to compare different modalities. feature alignment. Experimental results demonstrate that this method achieves state-of-the-art performance in predicting protein-ligand binding affinities. Furthermore, ablation studies demonstrate the effectiveness and necessity of protein surface information and multimodal feature alignment within this framework. Related research begins with "S
 Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Five schools of machine learning you don't know about
Jun 05, 2024 pm 08:51 PM
Machine learning is an important branch of artificial intelligence that gives computers the ability to learn from data and improve their capabilities without being explicitly programmed. Machine learning has a wide range of applications in various fields, from image recognition and natural language processing to recommendation systems and fraud detection, and it is changing the way we live. There are many different methods and theories in the field of machine learning, among which the five most influential methods are called the "Five Schools of Machine Learning". The five major schools are the symbolic school, the connectionist school, the evolutionary school, the Bayesian school and the analogy school. 1. Symbolism, also known as symbolism, emphasizes the use of symbols for logical reasoning and expression of knowledge. This school of thought believes that learning is a process of reverse deduction, through existing
 SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
According to news from this site on August 1, SK Hynix released a blog post today (August 1), announcing that it will attend the Global Semiconductor Memory Summit FMS2024 to be held in Santa Clara, California, USA from August 6 to 8, showcasing many new technologies. generation product. Introduction to the Future Memory and Storage Summit (FutureMemoryandStorage), formerly the Flash Memory Summit (FlashMemorySummit) mainly for NAND suppliers, in the context of increasing attention to artificial intelligence technology, this year was renamed the Future Memory and Storage Summit (FutureMemoryandStorage) to invite DRAM and storage vendors and many more players. New product SK hynix launched last year






