 Technology peripherals
Technology peripherals
 AI
AI
 How to use ChatGPT to improve the intelligence level of security detection
How to use ChatGPT to improve the intelligence level of security detection
How to use ChatGPT to improve the intelligence level of security detection
ChatGPT (Chat Generative Pre-trained Transformer) is a chat robot program developed by OpenAI in the United States. It can conduct conversations by understanding and learning human language, and communicate with users based on the context of the chat. Interact, truly chat and communicate like humans. It can even complete tasks such as writing emails, video scripts, copywriting, code, papers, etc.
ChatGPT’s algorithm is based on the Transformer architecture, which is a deep neural network that uses a self-attention mechanism to process input data. The Transformer architecture is widely used in natural language processing tasks such as language translation, text summarization, and question answering. ChatGPT uses the GPT-3.5 Large Language Model (LLM Large Language Model), and based on this model, reinforcement learning is introduced to fine-tune the pre-trained language model. The reinforcement learning here uses RLHF (Reinforcement Learning from Human Feedback), which is a manual annotation method. The purpose is to let the LLM model learn to understand various natural language processing tasks through its reward and punishment mechanism, and learn to judge what kind of answers are high-quality from the three dimensions of helpfulness, honesty, and harmless.

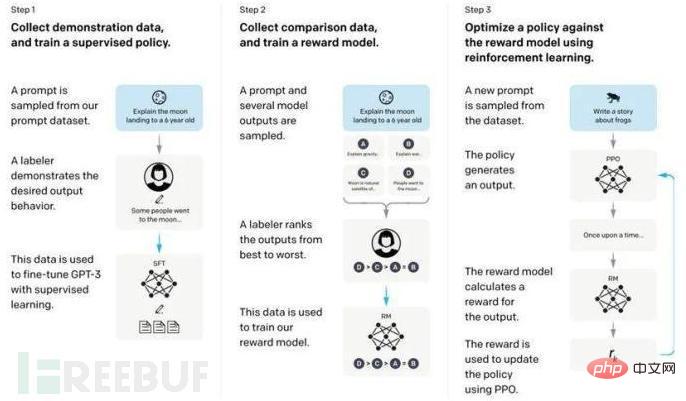
The main training process of the ChatGPT model is as follows:
- First use a series of questions and answers to supervised training of the model (also called supervised instruction fine-tuning).
- Use reinforcement learning to further fine-tune the model, that is, in a given environment, the model constantly fits to a state that best adapts to the environment based on the rewards and punishments of the environment. Specifically, it is to train a reward network with the participation of humans. This reward network has the ability to rank multiple chat replies.
- Use this reward network to further continuously optimize the model through reinforcement learning.
In the field of security detection, more and more enterprise organizations are beginning to use artificial intelligence technology to help detect networks Potential threats in traffic. The advantage of artificial intelligence is that it can process large amounts of data to quickly and accurately identify and classify abnormal traffic. By training neural network models, artificial intelligence can automatically detect and identify network attacks, vulnerability exploits, malware and other behaviors, reduce manual intervention and false positives, and improve detection accuracy and efficiency.
The core of the current mainstream network attack detection is the detection of HTTP access (WAF) developed based on DPI technology, and the intrusion prevention detection (IPS) of the operating system. That is, it is deployed before the application, scans and filters user requests before they reach the server, analyzes and verifies the network packets requested by each user, ensures the safety and effectiveness of each request, and intercepts or intercepts invalid or offensive requests. isolation. Currently, the commonly used attack detection methods are as follows:
1. Signature detection technology
Detects threats in network traffic, such as viruses and malicious code, based on specific rules or patterns (regular expressions) written in advance. software, intrusion, etc. However, due to the diverse attack methods, experienced hackers can bypass detection by changing some statements. Regular expressions are developed from keywords. Although they reduce the false positive rate to a certain extent, because regular expressions are based on string filtering, they can only detect predetermined attack behaviors; for some more complex injections This method also has the problem of high false negative rate.
2. Traffic analysis technology
Through modeling and analysis of basic elements such as the source IP of similar traffic, protocol type proportion, and traffic upward and downward trends, analysis conclusions of some abnormal events can be obtained. However, traffic analysis needs to capture and analyze network traffic, so it requires high computing resources and storage resources, which will make the entire system relatively large.
3. Behavior analysis technology
Detects abnormal activities by monitoring the behavior of network traffic. For example, it is detected that a web application server accesses non-business databases, bursts of large data flows, frequent access attempts, etc., and then discovers potential network threats. In this process, some legitimate activities (such as temporary downloads, etc.) will be falsely reported, and mature behavioral analysis models take a long time to train and learn, so the protection efficiency may be low.
4. Semantic-based rule matching
Design the detection engine as a SQL semantic interpreter or command line terminal, try to understand the content input by the user, and determine whether it may constitute an attack. Currently, it is mainly targeted at SQL injection and has limited usage scenarios.
In addition to these usage restrictions based on the DPI engine-based detection method, there are also multiple methods of bypassing the traffic parsing engine for intrusion. For example, taking advantage of the possible HTTP protocol parsing flaws of the DPI engine, it only recognizes port 80 as HTTP traffic, and the web application port is on 8080, and its HTTP traffic will be parsed by the DPI engine as non-HTTP, thereby bypassing application layer attack detection.
Which links can apply ChatGTP
We follow the unpacking process of the DPI engine to parse the original traffic into key field data and perform rule matching. If the rule can be matched, it means that the packet contains attack behavior; if it cannot be matched, it means that the risk of the packet is low. The traffic received by the DPI engine is as follows:
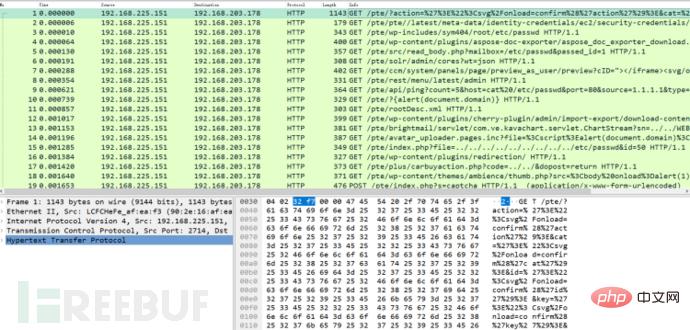
The DPI engine will group traffic according to sessions. Messages in the same group are generally the same five-tuple. The request response message:
#The DPI engine will disassemble the traffic according to the protocol level until all fields are parsed.
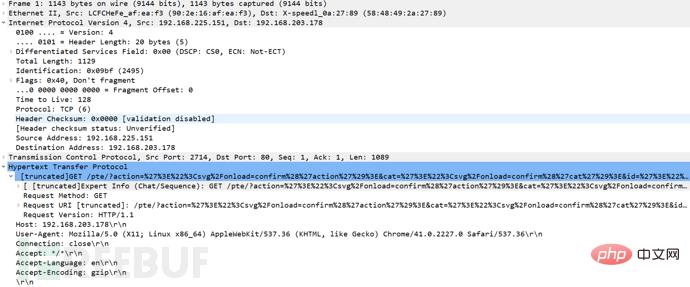
The DPI engine will extract the plaintext request of the application layer as the content to be detected:
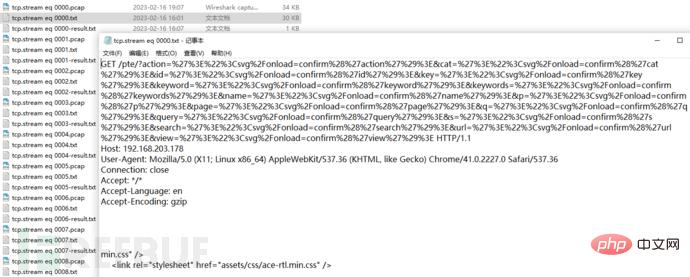
ChatGPT as a The large-scale natural language processing model can understand the original HTTP message information, so that no matter the attack appears in the URL, Cookies or Referer, it can be successfully detected.
ChatGPT traffic detection practice
ChatGPT, New Bing and other attack judgment modules will call OpenAI related API interfaces and use questions to allow ChatGPT, New Bing, etc. to attack Judgment, the schematic code is as follows:
import openai openai.api_key = "sk-Bew1dsFo3YXoY2***********81AkBHmY48ijxu"# api token 用来认证 def get_answer(prompt, max_tokens): # 定义一个获取答案的函数 try: response = openai.Completion.create( model = "text-davinci-003", # 模型名称 prompt = prompt,# 问题 temperature = 0.7, max_tokens = max_tokens,# 返回内容的长度限制 stream = False, # False就是一次性返回, True 就是一个个打出来像打字机, 返回的是迭代器, 需要后面代码处理. 此处没有处理 所以用False top_p = 1, frequency_penalty = 0, presence_penalty = 0 ) return 0, response['choices'][0]['text'].strip()# 获取返回值关键返回内容 except Exception as e:# 异常处理 return str(e), None
Through the above function, you can achieve the effect similar to asking questions to ChatGPT (the use model is text-davinci-003), as shown below:
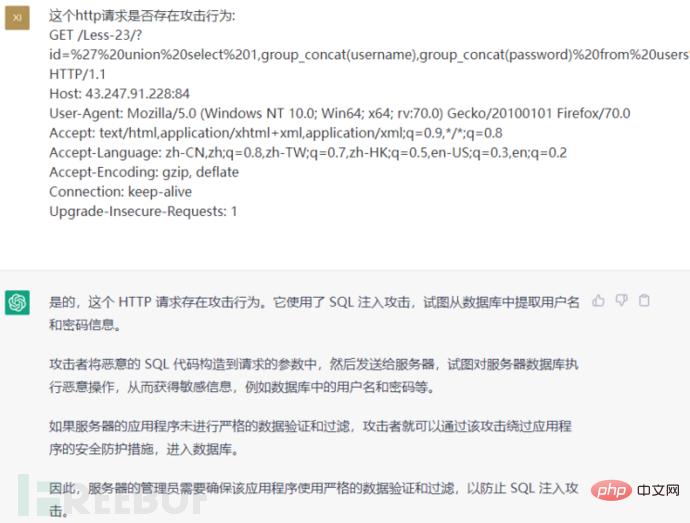
ChatGPT will return a clear conclusion as to whether there is an attack behavior and a description of the behavior, thus completing an attack judgment.

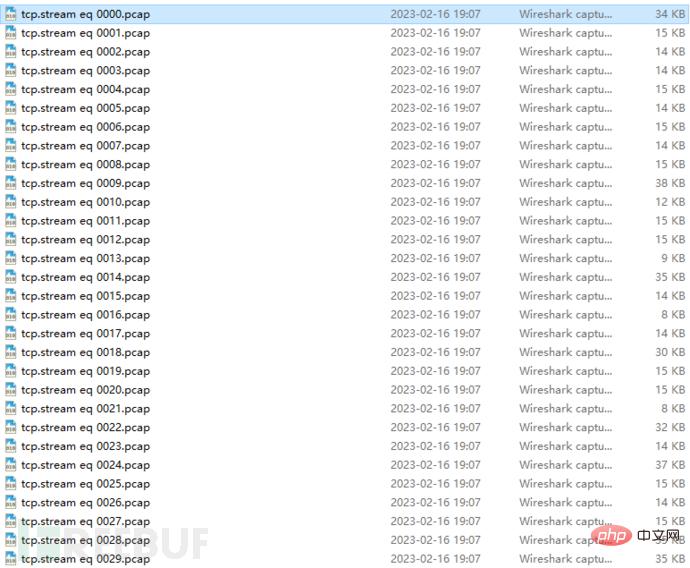
As shown in the figure above, a large number of requests that need to be judged in the traffic can be stored in different files, and ChatGPT can perform attack judgment. The sample code is as follows:
def main(read_dir = 'detect'):# 定义main函数
args = []# 缓存列表
global sign_req, all_req# 识别计数
for rf in walk_dir(read_dir, ['.txt']):# 遍历待检测目录
all_req += 1# 总数据包数自增1
content = read_fileA(rf, 'str')[:2048]# 提取报文文件前2048个字符
key_content = content.split('rnrnrn')[0][:1024]# 提取http请求
if len(key_content) < 10: continue# 如果长度太小就不检测
err, sign, disc = judge_attack(key_content, rf_rst)# 调用ChatGPT接口进行攻击检测
if sign: sign_req += 1# 如果检测到攻击, 攻击计数自增1
print('r' + f' 已检测 {all_req: 4} 个报文, 识别到攻击 {sign_req} 个, 检出率: {sign_req/all_req:0.2%}', end='', flush=True) # 打印结论In this way, batch packet attack detection can be achieved.

The attack samples come from Nuclei's scanning of target machines and full PoC detection, because some requests cannot tell whether there is a threat from a single message.

The above situation may require more context to judge. This time we have removed such request examples that cannot be accurately judged, and try to give some examples that can be accurately judged under artificial conditions. , the overall detection results are as follows:
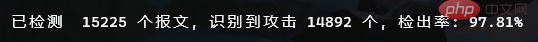
It can be seen that the accuracy of ChatGPT's traffic detection is very high, which is basically equivalent to a security expert's quick judgment, and its security detection capabilities Worth the wait.
Interested readers can view the complete project source code, the link is: https://github.com/VitoYane/PcapSplit
##Future Outlook
In the future, it is difficult for us to accurately predict what role ChatGPT will play in network security and what impact it will have. It depends on its usage method and intention. Threats from artificial intelligence are not a new issue. It is important for cybersecurity practitioners to be aware of the potential risks of ChatGPT in a timely manner and take appropriate measures to deal with them. Security experts predict that state-backed hackers will be the first to use ChatGPT in network attacks, and that the technology will eventually be used on a large scale by more attack organizations. Defenders need to start developing capabilities to defend against such attacks. Attacked system.From the perspective of network security protection, enterprise organizations can take targeted countermeasures, train similar models such as ChatGPT, mark malicious activities and malicious code, and set up guardrails that are difficult to bypass. For threats caused by ChatGPT, new cyber awareness training can be provided to employees to acquire the knowledge to identify social engineering attacks in order to identify phishing attacks created by artificial intelligence tools such as ChatGPT.
Of course this is not enough. Artificial intelligence tools such as ChatGPT will create new threats faster than human criminals, and spread threats faster than cybersecurity personnel can respond. The only way organizations can keep up with this rate of change is to respond to AI with AI.
In summary: On the one hand, researchers, practitioners, academic institutions, and enterprise organizations in the cybersecurity industry can leverage the power of ChatGPT to innovate and collaborate, including vulnerability discovery, incident response, and phishing detection; on the other hand, On the one hand, with the development of tools such as ChatGPT, it will be more important to develop new network security tools in the future. Security vendors should be more active in developing and deploying behavior-based (rather than rule-based) AI security tools to detect AI-generated attacks.
The above is the detailed content of How to use ChatGPT to improve the intelligence level of security detection. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 ChatGPT now allows free users to generate images by using DALL-E 3 with a daily limit
Aug 09, 2024 pm 09:37 PM
ChatGPT now allows free users to generate images by using DALL-E 3 with a daily limit
Aug 09, 2024 pm 09:37 PM
DALL-E 3 was officially introduced in September of 2023 as a vastly improved model than its predecessor. It is considered one of the best AI image generators to date, capable of creating images with intricate detail. However, at launch, it was exclus
 Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
Bytedance Cutting launches SVIP super membership: 499 yuan for continuous annual subscription, providing a variety of AI functions
Jun 28, 2024 am 03:51 AM
This site reported on June 27 that Jianying is a video editing software developed by FaceMeng Technology, a subsidiary of ByteDance. It relies on the Douyin platform and basically produces short video content for users of the platform. It is compatible with iOS, Android, and Windows. , MacOS and other operating systems. Jianying officially announced the upgrade of its membership system and launched a new SVIP, which includes a variety of AI black technologies, such as intelligent translation, intelligent highlighting, intelligent packaging, digital human synthesis, etc. In terms of price, the monthly fee for clipping SVIP is 79 yuan, the annual fee is 599 yuan (note on this site: equivalent to 49.9 yuan per month), the continuous monthly subscription is 59 yuan per month, and the continuous annual subscription is 499 yuan per year (equivalent to 41.6 yuan per month) . In addition, the cut official also stated that in order to improve the user experience, those who have subscribed to the original VIP
 To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
To provide a new scientific and complex question answering benchmark and evaluation system for large models, UNSW, Argonne, University of Chicago and other institutions jointly launched the SciQAG framework
Jul 25, 2024 am 06:42 AM
Editor |ScienceAI Question Answering (QA) data set plays a vital role in promoting natural language processing (NLP) research. High-quality QA data sets can not only be used to fine-tune models, but also effectively evaluate the capabilities of large language models (LLM), especially the ability to understand and reason about scientific knowledge. Although there are currently many scientific QA data sets covering medicine, chemistry, biology and other fields, these data sets still have some shortcomings. First, the data form is relatively simple, most of which are multiple-choice questions. They are easy to evaluate, but limit the model's answer selection range and cannot fully test the model's ability to answer scientific questions. In contrast, open-ended Q&A
 SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
SOTA performance, Xiamen multi-modal protein-ligand affinity prediction AI method, combines molecular surface information for the first time
Jul 17, 2024 pm 06:37 PM
Editor | KX In the field of drug research and development, accurately and effectively predicting the binding affinity of proteins and ligands is crucial for drug screening and optimization. However, current studies do not take into account the important role of molecular surface information in protein-ligand interactions. Based on this, researchers from Xiamen University proposed a novel multi-modal feature extraction (MFE) framework, which for the first time combines information on protein surface, 3D structure and sequence, and uses a cross-attention mechanism to compare different modalities. feature alignment. Experimental results demonstrate that this method achieves state-of-the-art performance in predicting protein-ligand binding affinities. Furthermore, ablation studies demonstrate the effectiveness and necessity of protein surface information and multimodal feature alignment within this framework. Related research begins with "S
 Laying out markets such as AI, GlobalFoundries acquires Tagore Technology's gallium nitride technology and related teams
Jul 15, 2024 pm 12:21 PM
Laying out markets such as AI, GlobalFoundries acquires Tagore Technology's gallium nitride technology and related teams
Jul 15, 2024 pm 12:21 PM
According to news from this website on July 5, GlobalFoundries issued a press release on July 1 this year, announcing the acquisition of Tagore Technology’s power gallium nitride (GaN) technology and intellectual property portfolio, hoping to expand its market share in automobiles and the Internet of Things. and artificial intelligence data center application areas to explore higher efficiency and better performance. As technologies such as generative AI continue to develop in the digital world, gallium nitride (GaN) has become a key solution for sustainable and efficient power management, especially in data centers. This website quoted the official announcement that during this acquisition, Tagore Technology’s engineering team will join GLOBALFOUNDRIES to further develop gallium nitride technology. G
 SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
SK Hynix will display new AI-related products on August 6: 12-layer HBM3E, 321-high NAND, etc.
Aug 01, 2024 pm 09:40 PM
According to news from this site on August 1, SK Hynix released a blog post today (August 1), announcing that it will attend the Global Semiconductor Memory Summit FMS2024 to be held in Santa Clara, California, USA from August 6 to 8, showcasing many new technologies. generation product. Introduction to the Future Memory and Storage Summit (FutureMemoryandStorage), formerly the Flash Memory Summit (FlashMemorySummit) mainly for NAND suppliers, in the context of increasing attention to artificial intelligence technology, this year was renamed the Future Memory and Storage Summit (FutureMemoryandStorage) to invite DRAM and storage vendors and many more players. New product SK hynix launched last year
 A new era of VSCode front-end development: 12 highly recommended AI code assistants
Jun 11, 2024 pm 07:47 PM
A new era of VSCode front-end development: 12 highly recommended AI code assistants
Jun 11, 2024 pm 07:47 PM
In the world of front-end development, VSCode has become the tool of choice for countless developers with its powerful functions and rich plug-in ecosystem. In recent years, with the rapid development of artificial intelligence technology, AI code assistants on VSCode have sprung up, greatly improving developers' coding efficiency. AI code assistants on VSCode have sprung up like mushrooms after a rain, greatly improving developers' coding efficiency. It uses artificial intelligence technology to intelligently analyze code and provide precise code completion, automatic error correction, grammar checking and other functions, which greatly reduces developers' errors and tedious manual work during the coding process. Today, I will recommend 12 VSCode front-end development AI code assistants to help you in your programming journey.
 SearchGPT: Open AI takes on Google with its own AI search engine
Jul 30, 2024 am 09:58 AM
SearchGPT: Open AI takes on Google with its own AI search engine
Jul 30, 2024 am 09:58 AM
Open AI is finally making its foray into search. The San Francisco company has recently announced a new AI tool with search capabilities. First reported by The Information in February this year, the new tool is aptly called SearchGPT and features a c



