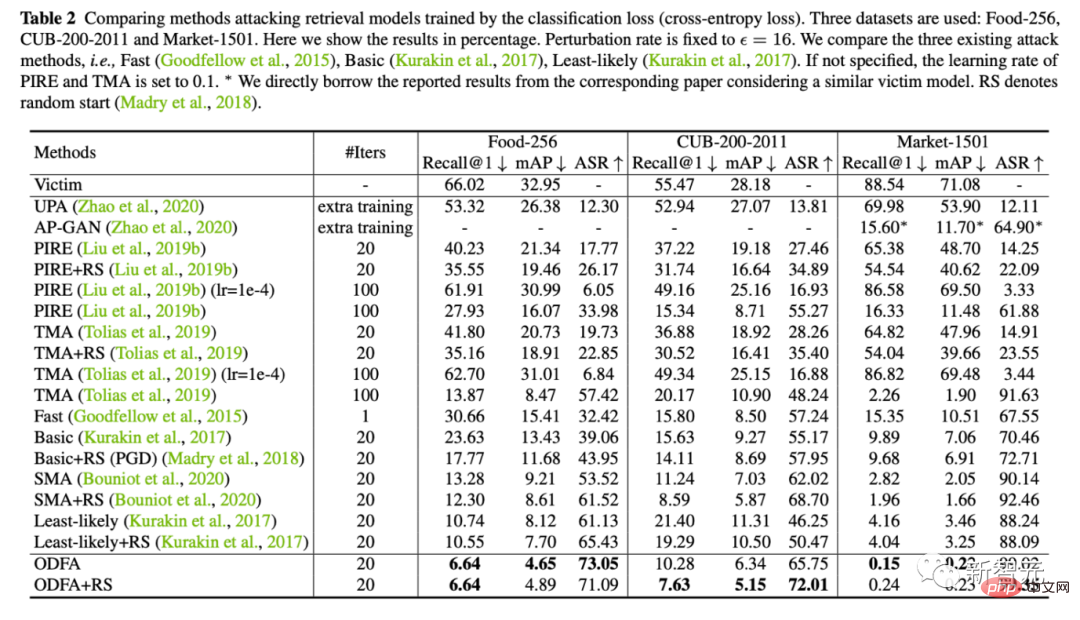
The reversal feature makes the re-id model go from 88.54% to 0.15%
The first version of this article was written in May 2018, and it was recently published in December 2022. I have received a lot of support and understanding from my bosses over the past four years.
(This experience also hopes to give some encouragement to students who are submitting papers. If you write the paper well, you will definitely win. Don’t give up easily!)
arXiv The early version is: Query Attack via Opposite-Direction Feature:Towards Robust Image Retrieval
##paper Link: https://link.springer.com/article/10.1007/s11263-022-01737-y
Paper backup link: https://zdzheng .xyz/files/IJCV_Retrieval_Robustness_CameraReady.pdf
Code: https://github.com/layumi/U_turn
Authors: Zhedong Zheng, Liang Zheng, Yi Yang and Fei Wu
Compared with earlier versions,
- We have made some adjustments to the formula;
- have added many new related works discussions;
- has been added Multi-scale Query attack/black box attack/defense experiments from three different angles;
- Add new methods and comparisons on Food256, Market-1501, CUB, Oxford, Paris and other data sets New ways to visualize.
- Attacked the PCB structure in reid and WiderResNet in Cifar10.
In actual use. For example, for example, we want to attack the image retrieval system of Google or Baidu to make big news (fog). We can download an image of a dog, calculate the features through the imagenet model (or other models, preferably a model close to the retrieval system), and calculate the adversarial noise plus by turning the features around (the method in this article). Back to the dog. Then use the image search function for the dog after the attack. You can see that Baidu and Google’s system cannot return dog-related content. Although we humans can still recognize that this is an image of a dog.
P.S. At that time, I also tried to attack Google to search for images. People can still recognize that it is an image of a dog, but Google often returns "mosaic" related images. I estimate that Google does not all use deep features, or it is quite different from the imagenet model. As a result, after an attack, it often tends to be "mosaic" instead of other entity categories (airplanes and the like). Of course mosaic can be considered a success to some extent!
What#1. The original intention of this article is actually very simple. The existing reid model or landscape retrieval model has reached a Recall-1 recall rate of more than 95%. So can we design a way to attack the retrieval model? On the one hand, let’s explore the background of the REID model. On the other hand, the attack is for better defense. Let’s study the defense anomaly case.
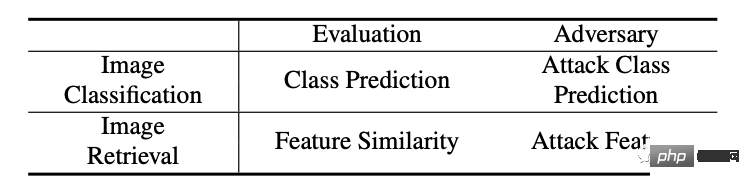
2. The difference between the retrieval model and the traditional classification model is that the retrieval model uses extracted features to compare the results (sorting), which is quite different from the traditional classification model. , as shown in the table below.
3. Another characteristic of the retrieval problem is open set, which means that the categories during testing are often not the same as those during training. seen. If you are familiar with the cub data set, under the retrieval setting, there are more than 100 kinds of birds in the training set during training, and more than 100 kinds of birds in the test set. There are no overlap types in these two 100 kinds. Matching and ranking rely purely on extracted visual features. Therefore, some classification attack methods are not suitable for attacking the retrieval model, because the graident based on category prediction during the attack is often inaccurate.
4. When testing the retrieval model, there are two parts of data: one is the query image query, and the other is the image library gallery (the amount of data is large and generally inaccessible). Considering the practical feasibility, our method will mainly target the image of the attack query to cause wrong retrieval results.
How
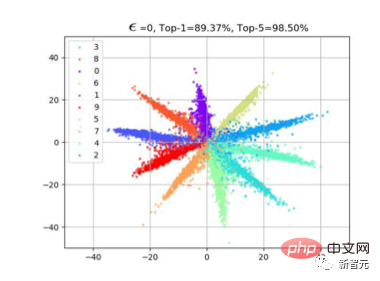
1. A natural idea is to attack features. So how to attack features? Based on our previous observations on cross entropy loss, (please refer to the article large-margin softmax loss). Often when we use classification loss, feature f will have a radial distribution. This is because the cos similarity is calculated between the feature and the weight W of the last classification layer during learning. As shown in the figure below, after we finish learning the model, samples of the same class will be distributed near W of that class, so that f*W can reach the maximum value.
2. So we proposed a very simple method, which is to make the features turn around. As shown in the figure below, there are actually two common classification attack methods that can also be visualized together. For example (a), this is to suppress the category with the highest classification probability (such as Fast Gradient), by giving -Wmax, so there is a red gradient propagation direction along the inverse Wmax; as (b), there is another way to suppress the least likely category. Features of possible categories are pulled up (such as Least-likely), so the red gradient is along Wmin.
3. These two classification attack methods are of course very direct and effective in traditional classification problems. However, since the test sets in the retrieval problem are all unseen categories (unseen bird species), the distribution of natural f does not closely fit Wmax or Wmin. Therefore, our strategy is very simple. Since we have f, then We can just move f to -f, as shown in Figure (c).
In this way, in the feature matching stage, the results that originally ranked high will, ideally, be ranked lowest when calculated as cos similarity with -f, changing from close to 1 to close to -1.
Achieved the effect of our attack retrieval sorting.
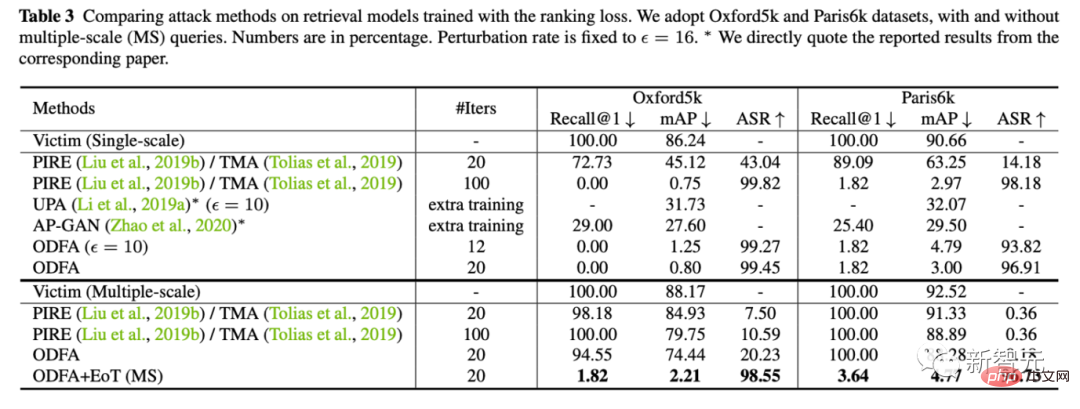
4. A small extension. In retrieval problems, we also often use multi-scale for query augmentation, so we also studied how to maintain the attack effect in this case. (The main difficulty is that the resize operation may smooth some small but critical jitters.)
In fact, our method of dealing with it is also very simple. Just like the model ensemble, we combine multiple Just make the ensemble average of the scale's adversarial gradient.
Experiment
1. Under three data sets and three indicators, we fixed the jitter amplitude, which is the epsilon of the abscissa, and compared which one under the same jitter amplitude. One method can make the retrieval model make more mistakes. Our method is that the yellow lines are all at the bottom, which means the attack effect is better.
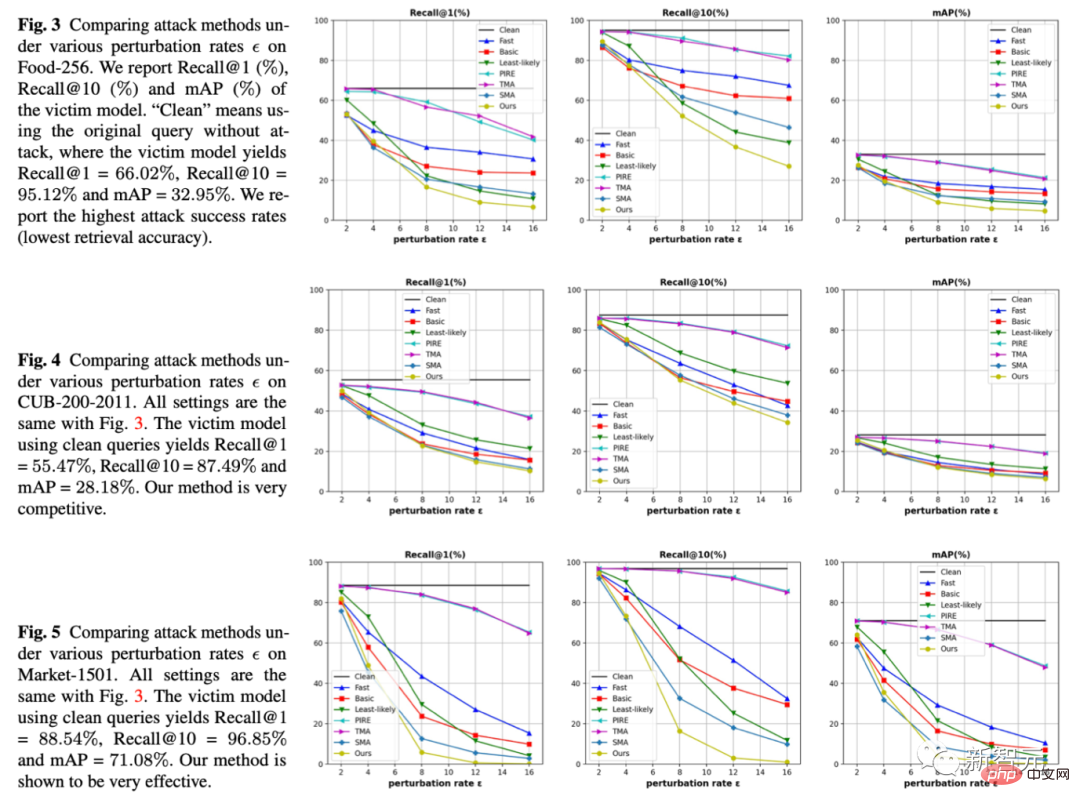
2. At the same time, we also provide quantitative experimental results on 5 data sets (Food, CUB, Market, Oxford, Paris)
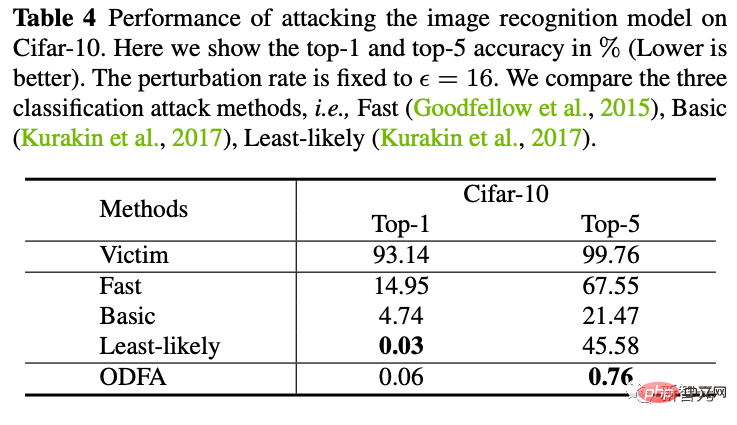
3. In order to demonstrate the mechanism of the model, we also tried to attack the classification model on Cifar10.
You can see that our strategy of changing the characteristics of the last layer also has strong suppression power against the top-5. For top-1, since there is no candidate category, it will be slightly lower than least-likely, but it is almost the same.
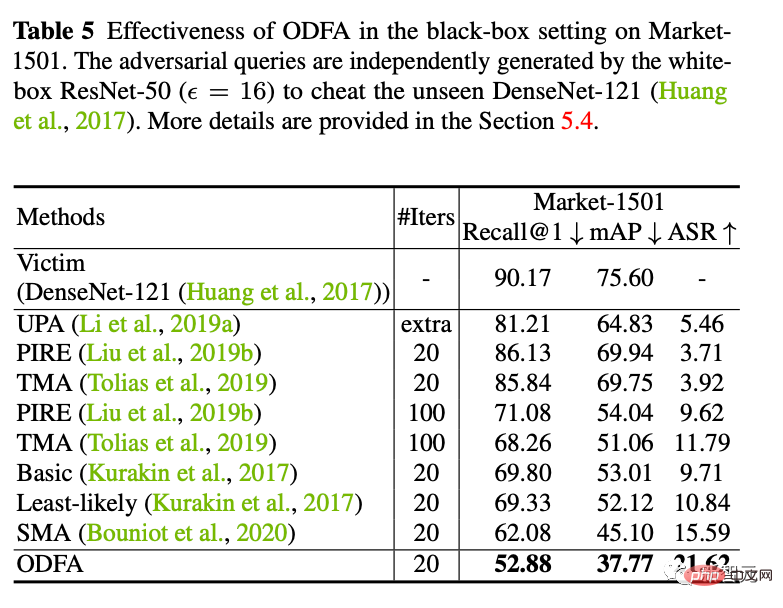
4. Black box attack
We also tried to use the attack sample generated by ResNet50 to attack A black-box DenseNet model (the parameters of this model are not available to us). It is found that better migration attack capabilities can also be achieved.
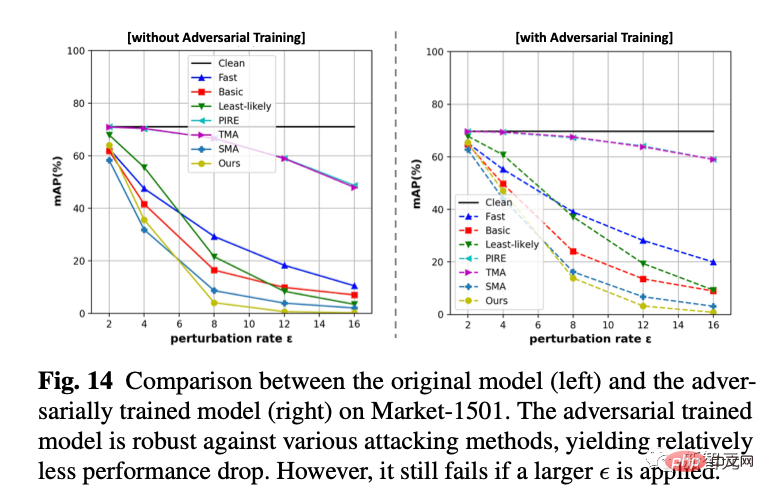
5. Counter Defense
We use online adversarial training to train a defense model. We found that it is still ineffective when accepting new white-box attacks, but it is more stable in small jitters (drops less points) than a completely defenseless model.
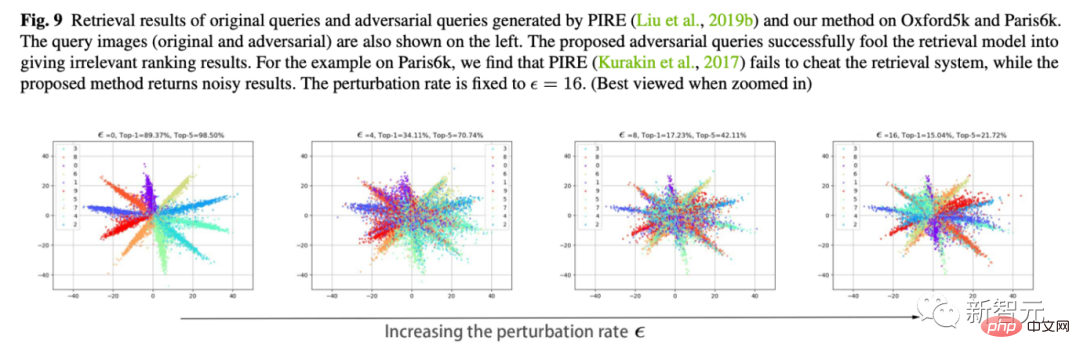
6. Visualization of feature movement
This is also my favorite experiment. We use Cifar10 to change the dimension of the last classification layer to 2 to plot the changes in features of the classification layer.
As shown in the figure below, as the jitter amplitude epsilon increases, we can see that the characteristics of the sample slowly "turn around". For example, most of the orange features have moved to the opposite side.
The above is the detailed content of The reversal feature makes the re-id model go from 88.54% to 0.15%. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 The world's most powerful open source MoE model is here, with Chinese capabilities comparable to GPT-4, and the price is only nearly one percent of GPT-4-Turbo
May 07, 2024 pm 04:13 PM
The world's most powerful open source MoE model is here, with Chinese capabilities comparable to GPT-4, and the price is only nearly one percent of GPT-4-Turbo
May 07, 2024 pm 04:13 PM
Imagine an artificial intelligence model that not only has the ability to surpass traditional computing, but also achieves more efficient performance at a lower cost. This is not science fiction, DeepSeek-V2[1], the world’s most powerful open source MoE model is here. DeepSeek-V2 is a powerful mixture of experts (MoE) language model with the characteristics of economical training and efficient inference. It consists of 236B parameters, 21B of which are used to activate each marker. Compared with DeepSeek67B, DeepSeek-V2 has stronger performance, while saving 42.5% of training costs, reducing KV cache by 93.3%, and increasing the maximum generation throughput to 5.76 times. DeepSeek is a company exploring general artificial intelligence
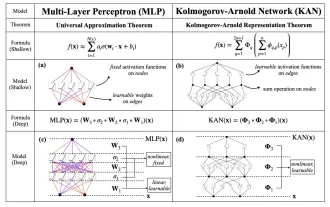 KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
Earlier this month, researchers from MIT and other institutions proposed a very promising alternative to MLP - KAN. KAN outperforms MLP in terms of accuracy and interpretability. And it can outperform MLP running with a larger number of parameters with a very small number of parameters. For example, the authors stated that they used KAN to reproduce DeepMind's results with a smaller network and a higher degree of automation. Specifically, DeepMind's MLP has about 300,000 parameters, while KAN only has about 200 parameters. KAN has a strong mathematical foundation like MLP. MLP is based on the universal approximation theorem, while KAN is based on the Kolmogorov-Arnold representation theorem. As shown in the figure below, KAN has
 Hello, electric Atlas! Boston Dynamics robot comes back to life, 180-degree weird moves scare Musk
Apr 18, 2024 pm 07:58 PM
Hello, electric Atlas! Boston Dynamics robot comes back to life, 180-degree weird moves scare Musk
Apr 18, 2024 pm 07:58 PM
Boston Dynamics Atlas officially enters the era of electric robots! Yesterday, the hydraulic Atlas just "tearfully" withdrew from the stage of history. Today, Boston Dynamics announced that the electric Atlas is on the job. It seems that in the field of commercial humanoid robots, Boston Dynamics is determined to compete with Tesla. After the new video was released, it had already been viewed by more than one million people in just ten hours. The old people leave and new roles appear. This is a historical necessity. There is no doubt that this year is the explosive year of humanoid robots. Netizens commented: The advancement of robots has made this year's opening ceremony look like a human, and the degree of freedom is far greater than that of humans. But is this really not a horror movie? At the beginning of the video, Atlas is lying calmly on the ground, seemingly on his back. What follows is jaw-dropping
 Google is ecstatic: JAX performance surpasses Pytorch and TensorFlow! It may become the fastest choice for GPU inference training
Apr 01, 2024 pm 07:46 PM
Google is ecstatic: JAX performance surpasses Pytorch and TensorFlow! It may become the fastest choice for GPU inference training
Apr 01, 2024 pm 07:46 PM
The performance of JAX, promoted by Google, has surpassed that of Pytorch and TensorFlow in recent benchmark tests, ranking first in 7 indicators. And the test was not done on the TPU with the best JAX performance. Although among developers, Pytorch is still more popular than Tensorflow. But in the future, perhaps more large models will be trained and run based on the JAX platform. Models Recently, the Keras team benchmarked three backends (TensorFlow, JAX, PyTorch) with the native PyTorch implementation and Keras2 with TensorFlow. First, they select a set of mainstream
 AI subverts mathematical research! Fields Medal winner and Chinese-American mathematician led 11 top-ranked papers | Liked by Terence Tao
Apr 09, 2024 am 11:52 AM
AI subverts mathematical research! Fields Medal winner and Chinese-American mathematician led 11 top-ranked papers | Liked by Terence Tao
Apr 09, 2024 am 11:52 AM
AI is indeed changing mathematics. Recently, Tao Zhexuan, who has been paying close attention to this issue, forwarded the latest issue of "Bulletin of the American Mathematical Society" (Bulletin of the American Mathematical Society). Focusing on the topic "Will machines change mathematics?", many mathematicians expressed their opinions. The whole process was full of sparks, hardcore and exciting. The author has a strong lineup, including Fields Medal winner Akshay Venkatesh, Chinese mathematician Zheng Lejun, NYU computer scientist Ernest Davis and many other well-known scholars in the industry. The world of AI has changed dramatically. You know, many of these articles were submitted a year ago.
 Time Series Forecasting NLP Large Model New Work: Automatically Generate Implicit Prompts for Time Series Forecasting
Mar 18, 2024 am 09:20 AM
Time Series Forecasting NLP Large Model New Work: Automatically Generate Implicit Prompts for Time Series Forecasting
Mar 18, 2024 am 09:20 AM
Today I would like to share a recent research work from the University of Connecticut that proposes a method to align time series data with large natural language processing (NLP) models on the latent space to improve the performance of time series forecasting. The key to this method is to use latent spatial hints (prompts) to enhance the accuracy of time series predictions. Paper title: S2IP-LLM: SemanticSpaceInformedPromptLearningwithLLMforTimeSeriesForecasting Download address: https://arxiv.org/pdf/2403.05798v1.pdf 1. Large problem background model
 Tesla robots work in factories, Musk: The degree of freedom of hands will reach 22 this year!
May 06, 2024 pm 04:13 PM
Tesla robots work in factories, Musk: The degree of freedom of hands will reach 22 this year!
May 06, 2024 pm 04:13 PM
The latest video of Tesla's robot Optimus is released, and it can already work in the factory. At normal speed, it sorts batteries (Tesla's 4680 batteries) like this: The official also released what it looks like at 20x speed - on a small "workstation", picking and picking and picking: This time it is released One of the highlights of the video is that Optimus completes this work in the factory, completely autonomously, without human intervention throughout the process. And from the perspective of Optimus, it can also pick up and place the crooked battery, focusing on automatic error correction: Regarding Optimus's hand, NVIDIA scientist Jim Fan gave a high evaluation: Optimus's hand is the world's five-fingered robot. One of the most dexterous. Its hands are not only tactile
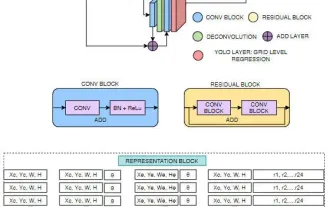 FisheyeDetNet: the first target detection algorithm based on fisheye camera
Apr 26, 2024 am 11:37 AM
FisheyeDetNet: the first target detection algorithm based on fisheye camera
Apr 26, 2024 am 11:37 AM
Target detection is a relatively mature problem in autonomous driving systems, among which pedestrian detection is one of the earliest algorithms to be deployed. Very comprehensive research has been carried out in most papers. However, distance perception using fisheye cameras for surround view is relatively less studied. Due to large radial distortion, standard bounding box representation is difficult to implement in fisheye cameras. To alleviate the above description, we explore extended bounding box, ellipse, and general polygon designs into polar/angular representations and define an instance segmentation mIOU metric to analyze these representations. The proposed model fisheyeDetNet with polygonal shape outperforms other models and simultaneously achieves 49.5% mAP on the Valeo fisheye camera dataset for autonomous driving






