
Encryption refers to using a special algorithm to change the original information data, so that even if unauthorized users obtain the encrypted information, they will not know the information. The method of decryption still cannot understand the content of the message. Common encryption algorithms can be mainly divided into: symmetric encryption, asymmetric encryption, and one-way encryption. Various encryption algorithms are used in different scenarios. Choose the appropriate algorithm based on the characteristics of the encryption algorithm, such as computing speed, security, and key management methods. However, security is an important indicator to measure the quality of the encryption algorithm. Encryption that is easily cracked Algorithms are called weak encryption algorithms, such as the DES algorithm that can be cracked in a limited time using exhaustive methods. This article takes the JAVA language source code as an example to analyze the causes of weak encryption and how to repair it.
For encryption algorithms that are weak in attack resistance, once exploited, personal privacy information may be leaked and even property losses may occur. From January 2018 to April 2019, there were a total of 2 vulnerability information related to it in CVE. The vulnerability information is as follows:
| Vulnerability Overview | |
|---|---|
| Weak encryption is used when transmitting passwords in CA Privileged AccessManager 2.x, which reduces the complexity of password cracking. | |
| In Easy Hosting Control Panel (EHCP) v0.37.12.b, it makes it easier for attackers to Crack database password. |
3. Sample code
The sample code used below comes from Benchmark (https://www.owasp.org/index .php/Benchmark), source file name: BenchmarkTest00019.java.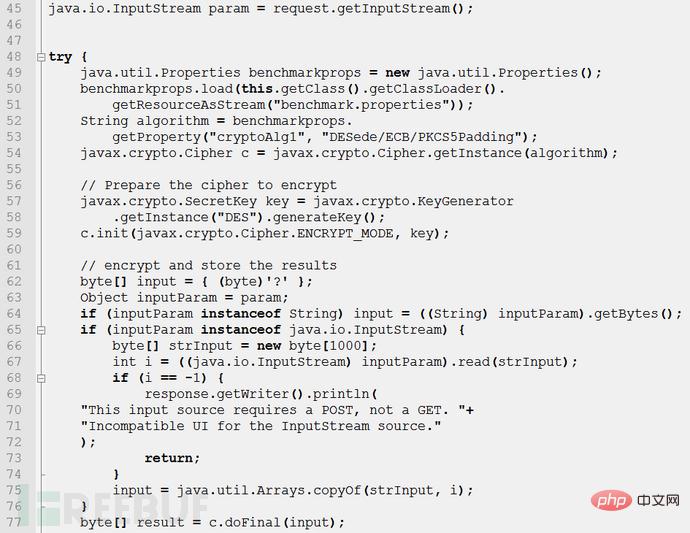
benchmarkprops. Load the configuration file on line 50, and read the attribute cryptoAlg1 in the configuration file on lines 52 to 53. If there is no such attribute, the default is to use DESede/ECB/PKCS5Padding to algorithm Assignment. Line 54 will use algorithm as the encryption algorithm to construct the encryption object c. Next prepare the encrypted password. Lines 57~58 instantiate a key generator for the DES encryption algorithm. Line 59 specifies that the operation mode of encryption object c is encryption, where key is the key. Lines 62 to 76 convert the input stream in the request into a byte array input, and line 77 encrypts the input. The encryption result is a byte array result. The key generated using the DES algorithm is short, only 56 bits, and the operation speed is slow. Moreover, the DES algorithm completely relies on the key and is vulnerable to exhaustive search attacks.
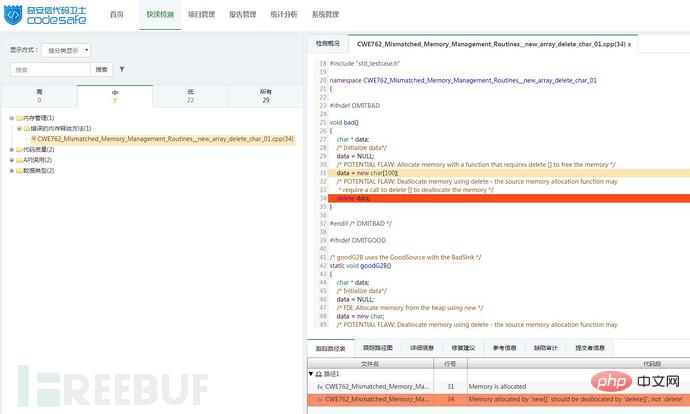


##Figure 2: Detection results after repair
The above is the detailed content of How to avoid weak encryption in C language. For more information, please follow other related articles on the PHP Chinese website!




