How to intercept uri in nginx location
Explanation: The root and alias
root commands in
location just set the searched root to the root setting directory, that is, the uri will not be truncated, but the original uri will be used to jump to the directory to find the file
ais command will truncate the matching uri, and then use the path set by alias to add Search the remaining uri as a subpath
location proxy_pass's uri
If the proxy_pass url does not have a uri
If the tail is "/", the matching uri will be truncated
If the tail is not "/", the matching uri will not be truncated
If the url of proxy_pass contains uri, the matching uri will be truncated
examples
root## in location
#
root@pts/1 $ ls -ld /data/web/lctest*|awk '{print $nf}'
/data/web/lctest
/data/web/lctest2
/data/web/lctest3
/data/web/lctest4
location /lctest {
root /data/web/;
}
location /lctest2/ {
root /data/web/;
}
location /lctest3 {
root /data/web;
}
location /lctest4/ {
root /data/web;
}curl test results are as follows
root@pts/1 $ curl http://tapi.xxxx.com/lctest/ hello world root@pts/1 $ curl http://tapi.xxxx.com/lctest2/ hello world 2 root@pts/1 $ curl http://tapi.xxxx.com/lctest3/ 3 hello world root@pts/1 $ curl http://tapi.xxxx.com/lctest4/ hello world 4
location alias
location /lctest5 {
alias /data/web/;
}
location /lctest6/ {
alias /data/web/;
}
location /lctest7 {
alias /data/web;
}
## 403 /data/web forbidden
location /lctest8/ {
alias /data/web;
}curl test results are as follows
curl 'http://tapi.kaishustory.com/lctest5/' curl 'http://tapi.kaishustory.com/lctest6/' curl 'http://tapi.kaishustory.com/lctest7/' 结果都是 /data/web/index.html的输出 root@pts/1 $ curl 'http://tapi.kaishustory.com/lctest8/' <html> <head><title>403 forbidden</title></head> <body bgcolor="white"> <center><h1>403 forbidden</h1></center> <hr><center>nginx</center> </body> </html>
location proxy_pass
#--------proxy_pass配置---------------------
location /t1/ { proxy_pass http://servers; } #正常,不截断
location /t2/ { proxy_pass http://servers/; } #正常,截断
location /t3 { proxy_pass http://servers; } #正常,不截断
location /t4 { proxy_pass http://servers/; } #正常,截断
location /t5/ { proxy_pass http://servers/test/; } #正常,截断
location /t6/ { proxy_pass http://servers/test; } #缺"/",截断
location /t7 { proxy_pass http://servers/test/; } #含"//",截断
location /t8 { proxy_pass http://servers/test; } #正常,截断Test script
for i in $(seq 8) do url=http://tapi.xxxx.com/t$i/doc/index.html echo "-----------$url-----------" curl url done
Test result
----------http://tapi.xxxx.com/t1/doc/index.html------------ /t1/doc/index.html ----------http://tapi.xxxx.com/t2/doc/index.html------------ /doc/index.html ----------http://tapi.xxxx.com/t3/doc/index.html------------ /t3/doc/index.html ----------http://tapi.xxxx.com/t4/doc/index.html------------ /doc/index.html ----------http://tapi.xxxx.com/t5/doc/index.html------------ /test/doc/index.html ----------http://tapi.xxxx.com/t6/doc/index.html------------ /testdoc/index.html ----------http://tapi.xxxx.com/t7/doc/index.html------------ /test//doc/index.html ----------http://tapi.xxxx.com/t8/doc/index.html------------ /test/doc/index.html
The above is the detailed content of How to intercept uri in nginx location. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 How to allow external network access to tomcat server
Apr 21, 2024 am 07:22 AM
How to allow external network access to tomcat server
Apr 21, 2024 am 07:22 AM
To allow the Tomcat server to access the external network, you need to: modify the Tomcat configuration file to allow external connections. Add a firewall rule to allow access to the Tomcat server port. Create a DNS record pointing the domain name to the Tomcat server public IP. Optional: Use a reverse proxy to improve security and performance. Optional: Set up HTTPS for increased security.
 How to generate URL from html file
Apr 21, 2024 pm 12:57 PM
How to generate URL from html file
Apr 21, 2024 pm 12:57 PM
Converting an HTML file to a URL requires a web server, which involves the following steps: Obtain a web server. Set up a web server. Upload HTML file. Create a domain name. Route the request.
 How to deploy nodejs project to server
Apr 21, 2024 am 04:40 AM
How to deploy nodejs project to server
Apr 21, 2024 am 04:40 AM
Server deployment steps for a Node.js project: Prepare the deployment environment: obtain server access, install Node.js, set up a Git repository. Build the application: Use npm run build to generate deployable code and dependencies. Upload code to the server: via Git or File Transfer Protocol. Install dependencies: SSH into the server and use npm install to install application dependencies. Start the application: Use a command such as node index.js to start the application, or use a process manager such as pm2. Configure a reverse proxy (optional): Use a reverse proxy such as Nginx or Apache to route traffic to your application
 Can nodejs be accessed from the outside?
Apr 21, 2024 am 04:43 AM
Can nodejs be accessed from the outside?
Apr 21, 2024 am 04:43 AM
Yes, Node.js can be accessed from the outside. You can use the following methods: Use Cloud Functions to deploy the function and make it publicly accessible. Use the Express framework to create routes and define endpoints. Use Nginx to reverse proxy requests to Node.js applications. Use Docker containers to run Node.js applications and expose them through port mapping.
 How to deploy and maintain a website using PHP
May 03, 2024 am 08:54 AM
How to deploy and maintain a website using PHP
May 03, 2024 am 08:54 AM
To successfully deploy and maintain a PHP website, you need to perform the following steps: Select a web server (such as Apache or Nginx) Install PHP Create a database and connect PHP Upload code to the server Set up domain name and DNS Monitoring website maintenance steps include updating PHP and web servers, and backing up the website , monitor error logs and update content.
 How to use Fail2Ban to protect your server from brute force attacks
Apr 27, 2024 am 08:34 AM
How to use Fail2Ban to protect your server from brute force attacks
Apr 27, 2024 am 08:34 AM
An important task for Linux administrators is to protect the server from illegal attacks or access. By default, Linux systems come with well-configured firewalls, such as iptables, Uncomplicated Firewall (UFW), ConfigServerSecurityFirewall (CSF), etc., which can prevent a variety of attacks. Any machine connected to the Internet is a potential target for malicious attacks. There is a tool called Fail2Ban that can be used to mitigate illegal access on the server. What is Fail2Ban? Fail2Ban[1] is an intrusion prevention software that protects servers from brute force attacks. It is written in Python programming language
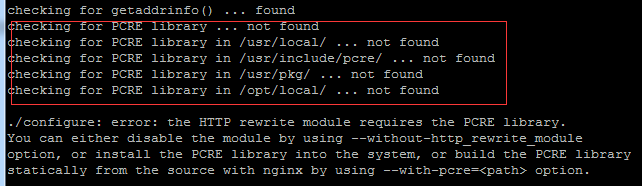 Come with me to learn Linux and install Nginx
Apr 28, 2024 pm 03:10 PM
Come with me to learn Linux and install Nginx
Apr 28, 2024 pm 03:10 PM
Today, I will lead you to install Nginx in a Linux environment. The Linux system used here is CentOS7.2. Prepare the installation tools 1. Download Nginx from the Nginx official website. The version used here is: 1.13.6.2. Upload the downloaded Nginx to Linux. Here, the /opt/nginx directory is used as an example. Run "tar-zxvfnginx-1.13.6.tar.gz" to decompress. 3. Switch to the /opt/nginx/nginx-1.13.6 directory and run ./configure for initial configuration. If the following prompt appears, it means that PCRE is not installed on the machine, and Nginx needs to
 Several points to note when building high availability with keepalived+nginx
Apr 23, 2024 pm 05:50 PM
Several points to note when building high availability with keepalived+nginx
Apr 23, 2024 pm 05:50 PM
After yum installs keepalived, configure the keepalived configuration file. Note that in the keepalived configuration files of master and backup, the network card name is the network card name of the current machine. VIP is selected as an available IP. It is usually used in high availability and LAN environments. There are many, so this VIP is an intranet IP in the same network segment as the two machines. If used in an external network environment, it does not matter whether it is on the same network segment, as long as the client can access it. Stop the nginx service and start the keepalived service. You will see that keepalived pulls the nginx service to start. If it cannot start and fails, it is basically a problem with the configuration files and scripts, or a prevention problem.




