What is H3C port security technology?
As the Internet becomes increasingly developed today, security is a topic that must be paid attention to. In the enterprise, there are many threats to switch ports, including unauthorized users randomly connecting hosts in the enterprise network. For example, if employees own their own laptops, they can unplug the network cable of a certain host without the administrator's consent, plug it into the laptop they brought, and then connect it to the corporate network. This will bring great security risks. , it is very likely to cause the loss of confidential information. Another example is installing hubs and other network equipment without consent. In order to increase the number of network terminals, some employees will do so without authorization. Plug devices such as hubs and switches into the office network interface. Doing so will increase the traffic on the switch interface corresponding to the network interface, thereby reducing network performance. How can administrators better prevent these problems?
Port security is a security mechanism that controls network access based on MAC address. It is an expansion of the existing 802.1X authentication and MAC address authentication. This mechanism controls the access of unauthorized devices to the network by detecting the source MAC address in the data frames received by the port, and controls the access to the unauthorized device by detecting the destination MAC address in the data frames sent from the port.
The main function of port security is to define various port security modes so that the device can learn the legal source MAC address to achieve the corresponding network management effect. After the port security function is enabled, when an illegal message is discovered, the system will trigger the corresponding features and process it in a pre-specified manner, which not only facilitates user management but also improves system security.
Here we will introduce some configuration issues of H3C equipment.
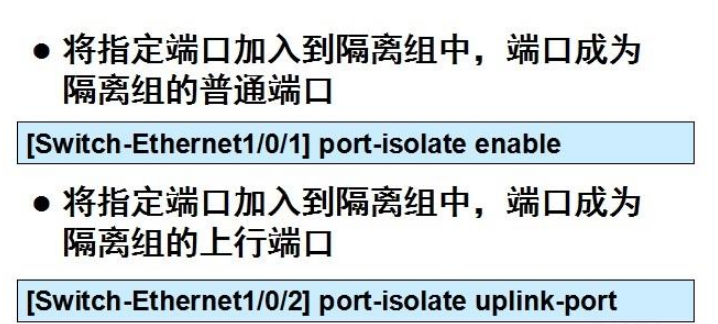
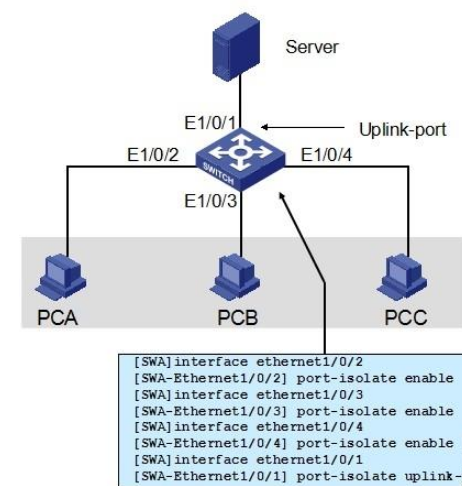
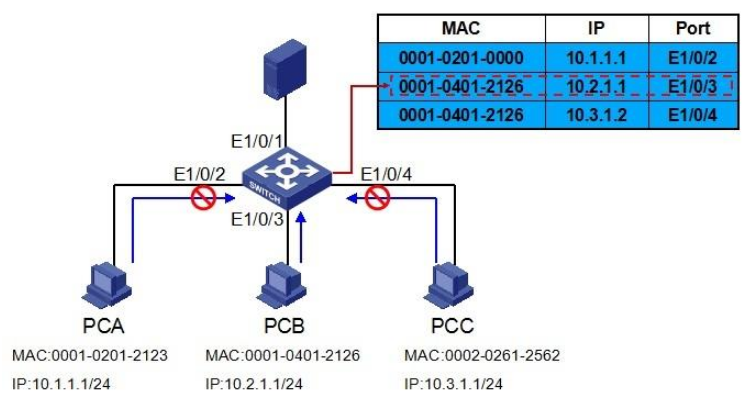
1. Port isolation technology. The port isolation method to achieve Layer 2 isolation between packets can add different ports to different VLANs, but this will waste limited VLAN resources. The port isolation feature can be used to isolate ports within the same VLAN. Adding a port to an isolation group can achieve Layer 2 data isolation between ports in the isolation group. The port isolation function provides users with a safer and more flexible networking solution.
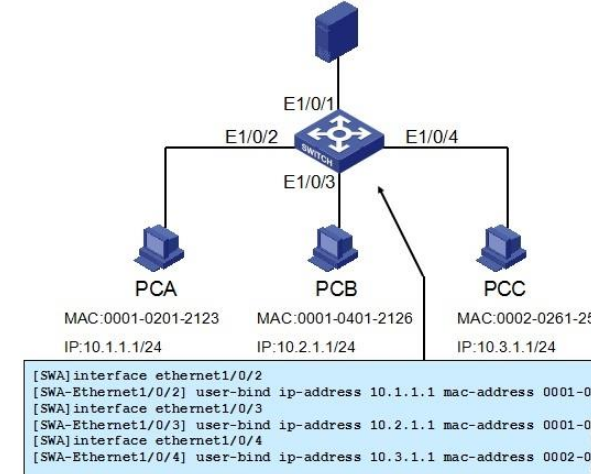
2. The port binding of the switch is to bind a certain port of the switch to the MAC address and IP address of the computer connected below. Binding, so that even if another computer secretly connects to this port, it cannot be used. This increases security.
The above is the detailed content of What is H3C port security technology?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1382
1382
 52
52


