Operation and Maintenance
Operation and Maintenance
 Safety
Safety
 How to use the Build Events feature to perform code replication
How to use the Build Events feature to perform code replication
How to use the Build Events feature to perform code replication
The specific attack method is to "raise accounts" and then trick security researchers into downloading their POC with malicious code, which will trigger malicious commands and codes during compilation.
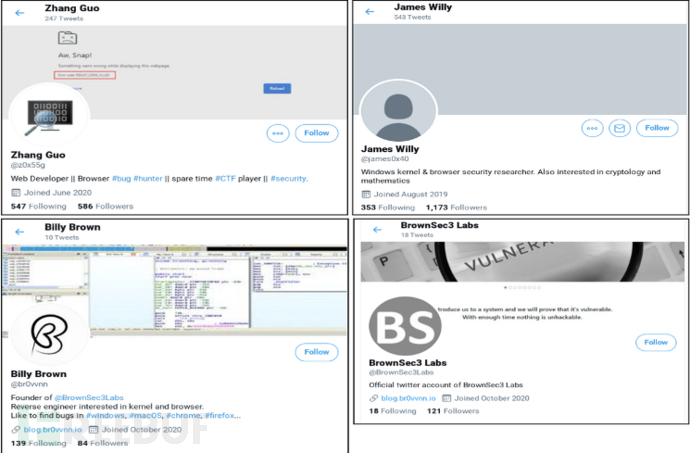
TAG Security Department disclosed a social engineering attack using social media such as Twitter to target security researchers engaged in vulnerability research and development in different companies and organizations. This was analyzed by NSFOCUS Fuying Lab. , confirmed that this incident was a targeted cyber attack against the cybersecurity industry by the Lazarus organization, and speculated that it may have deeper attack intentions and actions. NSFOCUS' attack and countermeasures technology research team M01N
Team also conducted a comprehensive analysis and judgment on this incident and determined that this incident was a typical social engineering attack incident of "openly building plank roads and secretly crossing Chencang", which will also be discussed in the article. Revealing a new indirect command execution attack technique used by the Lazarus organization in this incident.The Lazarus organization is an APT organization from the Korean Peninsula. The organization has been active since 2007 and has long carried out attacks on South Korea, China, the United States, India and other countries. According to investigations by foreign security companies, the Lazarus organization was involved in the hacker attack on Sony Pictures in 2014, the Bangladesh Bank data leakage in 2016, the U.S. defense contractor, the U.S. energy department, the United Kingdom, South Korea and other Bitcoins in 2017. Exchanges were attacked and other incidents. The most notorious security incident that swept the world in 2017, the "Wannacry" ransomware virus, was also suspected to be the work of this organization.
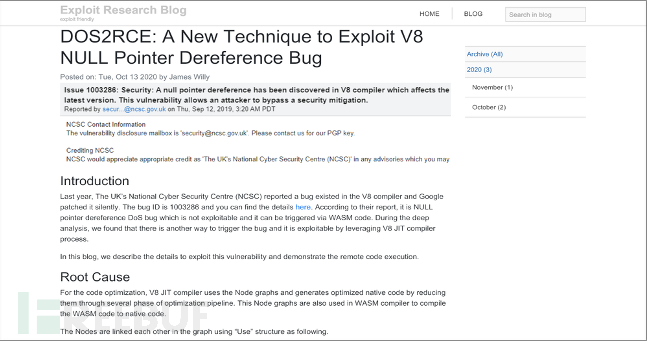
The attackers from the Lazarus organization pretended to be security researchers and established a research blog and multiple Twitter accounts. Most of these disguised accounts were marked with web development, browser vulnerability mining, Windows kernel security and even CTF players. Wait for some identity tags, and publish some security research updates, while commenting and forwarding each other to expand influence.Green Alliance TechnologyIn addition, their blog (https://blog.br0vvnn[.]
io) has published multiple publicly disclosed vulnerability analysis articles, including some Visiting reviews from uninformed security researchers in an attempt to build higher trust among security researchers.
After establishing a certain research influence, attackers will actively seek out target security researchers for communication and express their desire for more in-depth cooperation and exchanges in vulnerability research. Afterwards, the attacker will share a VisualStudio project file with security researchers. This project file is clearly POC code for some vulnerabilities, but secretly contains malicious commands and codes that are waiting for the target researcher to compile and execute to trigger. .
https://mp.weixin.qq.com/s/7RwH5_h2rGn3MxGIngal6A
By specifying a custom build event, you can automatically run commandsbefore a build starts or after it finishes. For example, you can run a
You can run the .bat file before the build starts, or copy the new file to the folder after the build is complete.
.bat file before a build starts or copy new files to a folder after
the build is complete. Build events run only if the build successfully
reaches those points in the build process. The build event will not be run until those points in the process, for example:
This is not difficult to understand.
We continue to look at the information in Microsoft documents and we can know that Build Events has three types of events, namely:
1.Pre-build event command line pre-generates events; execute customization before compilation Task
https://docs.microsoft.com/en-us/visualstudio/ide/specifying-custom-build-events-in-visual-studio?view=vs-2019
2.Post-build event command line pre-link event; perform custom tasks before linking
指定在构建开始之前要执行的所有命令,如果项目是最新的并且未触发任何构建,则预构建事件不会运行。
3.Run the post-build event post-build event; after compilation is completed Execute custom tasks
指定在构建结束后要执行的所有命令
The corresponding XML elements are also given in Microsoft documents. Interested students can take a look by themselves
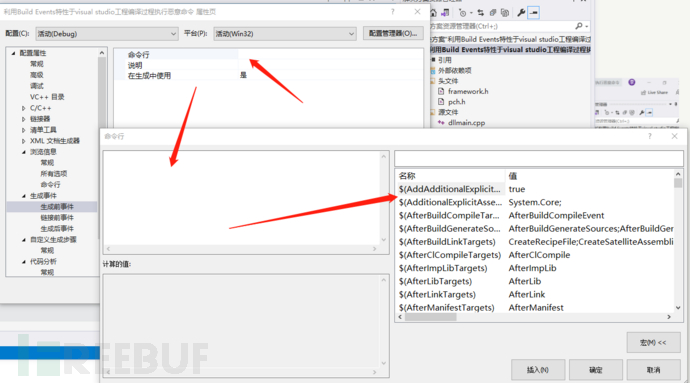
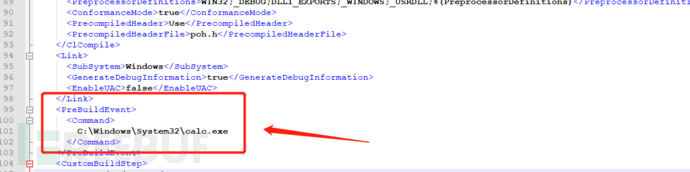
in Lazarus The organization uses Visual Studio for application, so let’s reproduce the application method: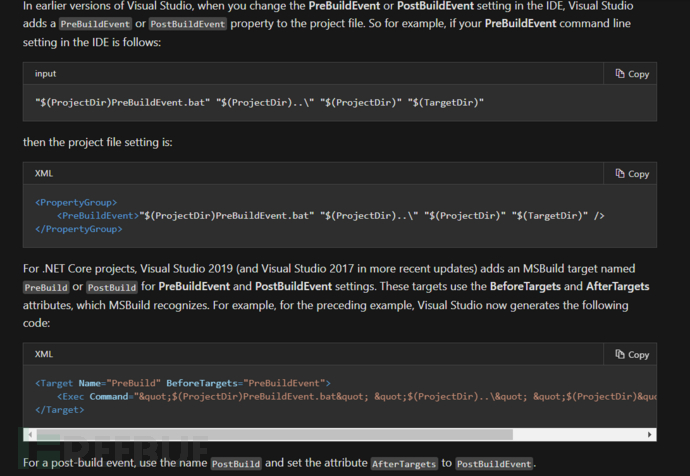
2. Create a new project
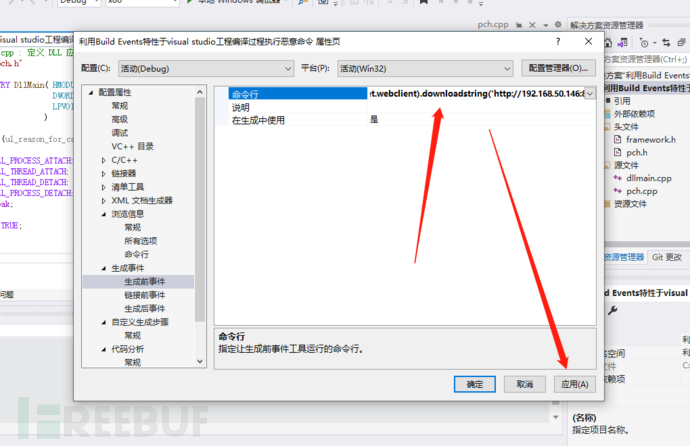
3. Enter the properties of the projectLet’s take a look at the first event
You can see it, as you can see above there are three types of events
第一种可以直接执行命令行也可以执行宏代码:
这里简单复现一下,就不讨论宏代码的一个情况了。
在cobalt strike种直接生成powershell的恶意脚本。
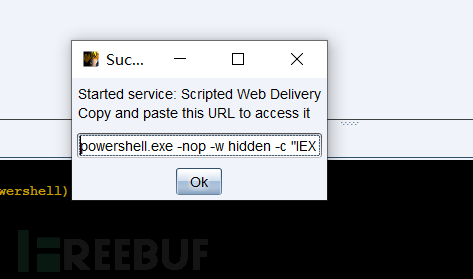
把命令放在visual studio中
应用然后编译
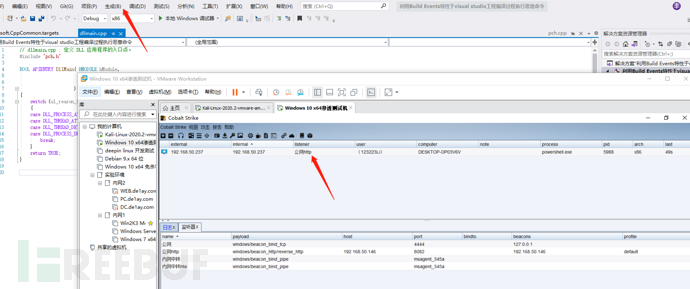
可以看到直接上线。
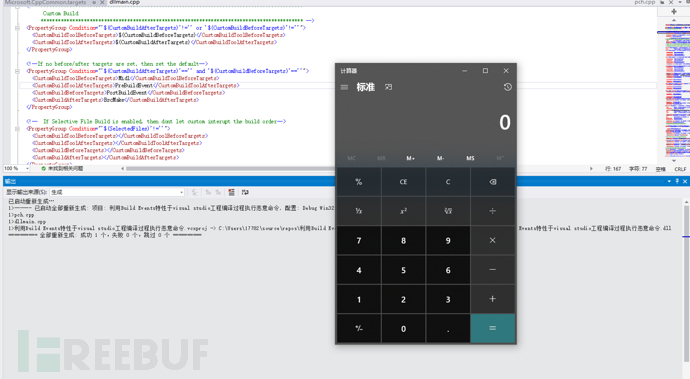
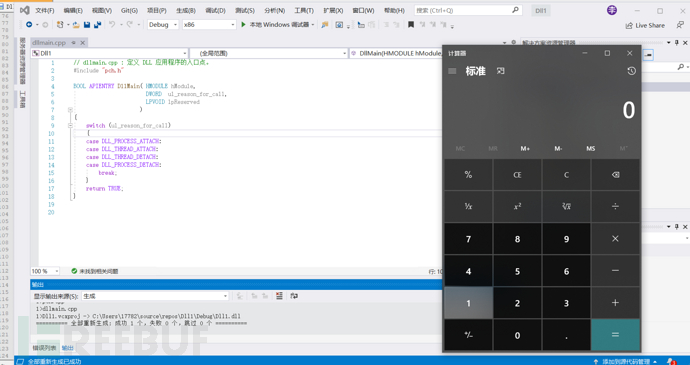
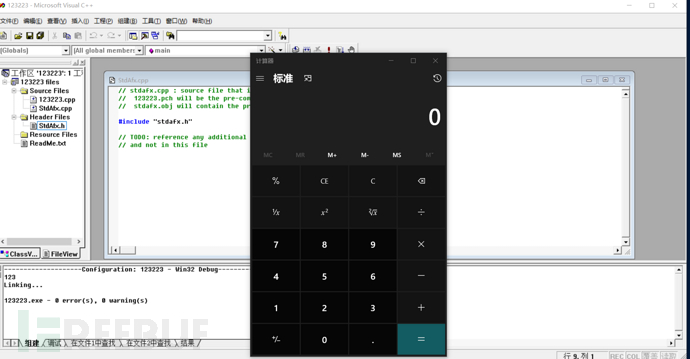
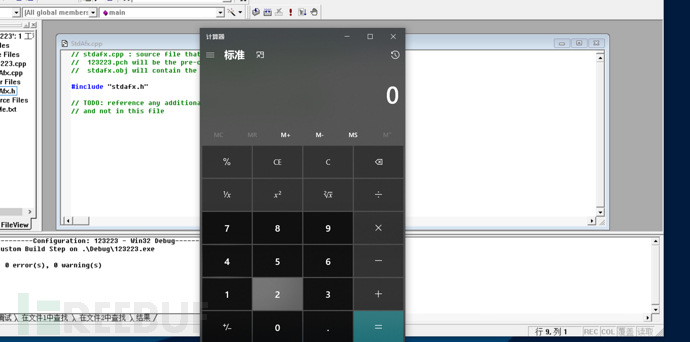
接着是第二种情况,我的电脑性能较差,因此我没有使用cobalt strike上线,我们使用弹计算器来验证可利用性
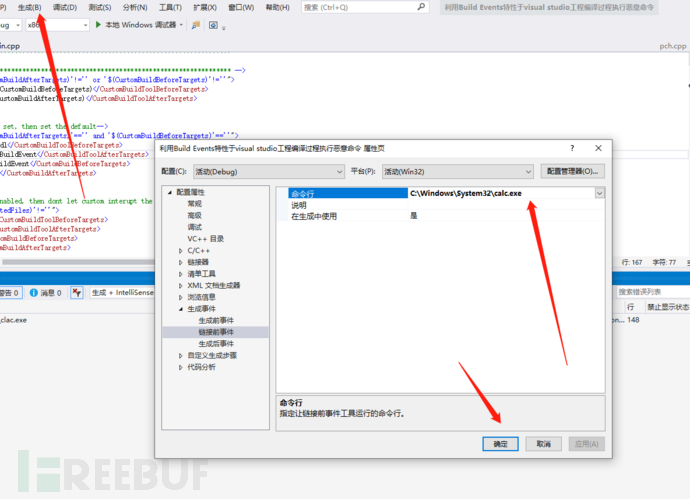
编译
同理,第3种也是
我们也可以在项目文件中直接添加我们需要执行的命令
打开项目目录可以看到
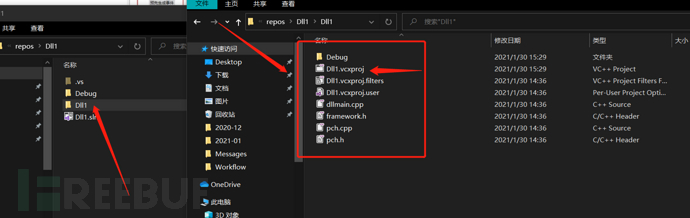
其中以.vcxproj结尾的文件就是我们需要利用的文件。
*.vcxproj:VS2010以及VS2010之后版本的VS工程文件
这里使用notepad++打开,这个文件其实也是一个xml文件。
ok 我们直接查找PreBuildEvent,PreLinkEvent,PostBuildEvent这3个xml元素
这里以PreBuildEvent进行利用
可以看到在PreBuildEvent 具有参数,这里就是可以执行命令的地方,
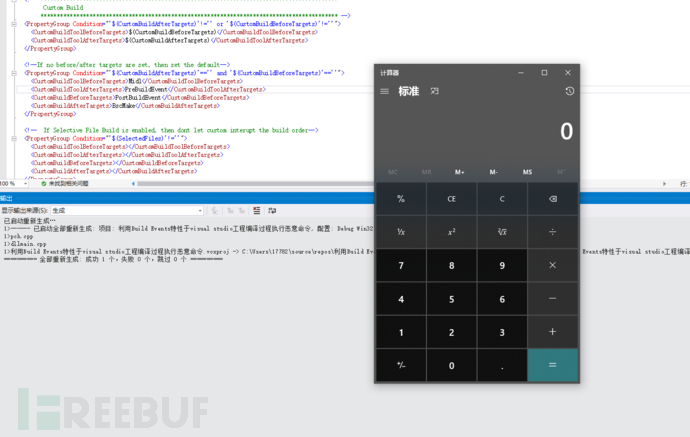
保存一下然后导进vs中进行编译
这里再分享一个手法吧 我看到网上的分析文章都是说PreBuildEvent,PreLinkEvent,PostBuildEvent这三个利用点,都是其实还有一个的地方可以给我们利用
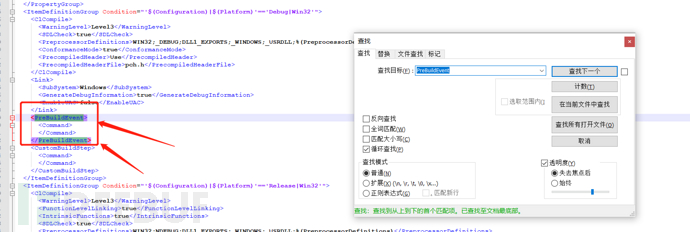
我们可以回看到.vcxproj文件,然后全局查找一下Command可以发现具有4个Command参数,
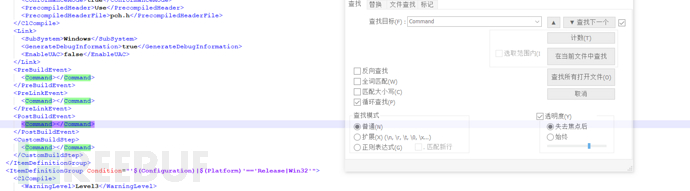
除了3个我们说过的之外,还有一个在中
添加我们需要执行的命令
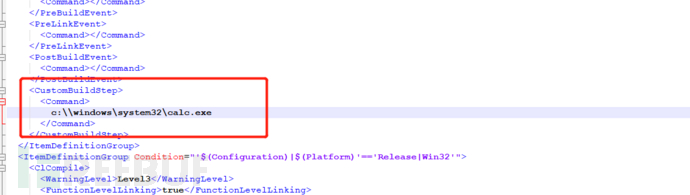
保存然后编译一下,但是发现并不能成功利用,通过查看微软文档知道我们还需要构建一个输出叁数。
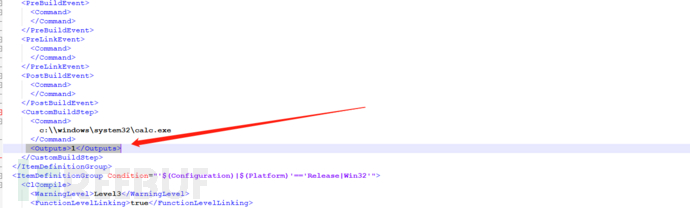
然后编译,弹出计算机
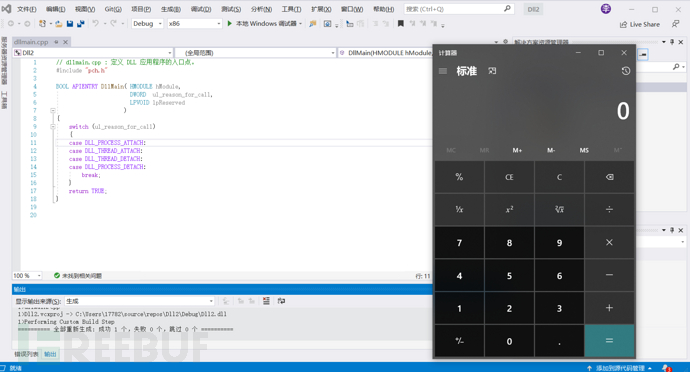
图形化的利用在
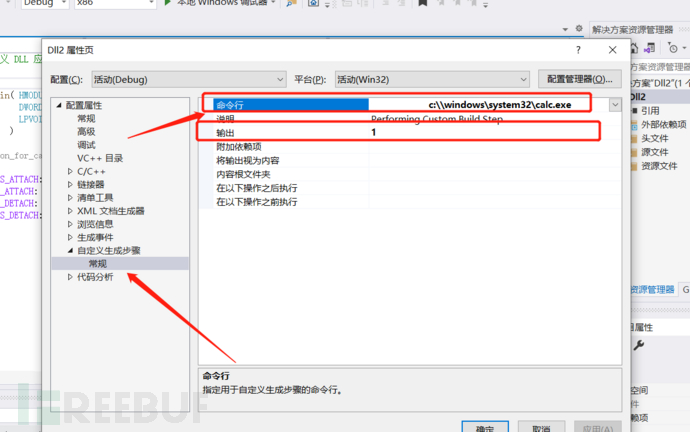
理论上所有的IDE都能这样利用,我们可以看一下在Microsoft Visual中的利用过程吧
打开vc然后新建一个工程,在上面的工具栏找到工程然后是设置
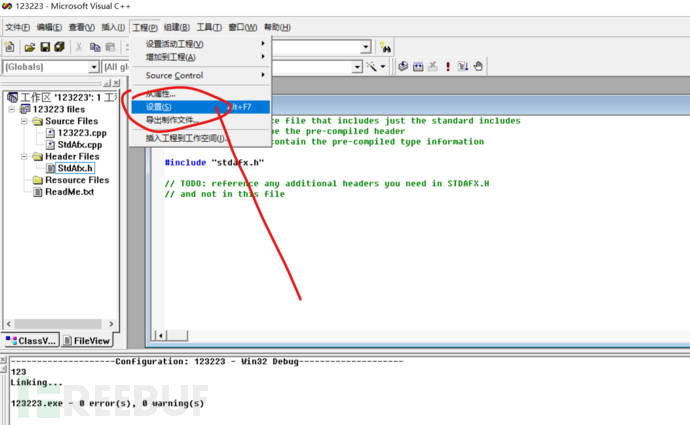
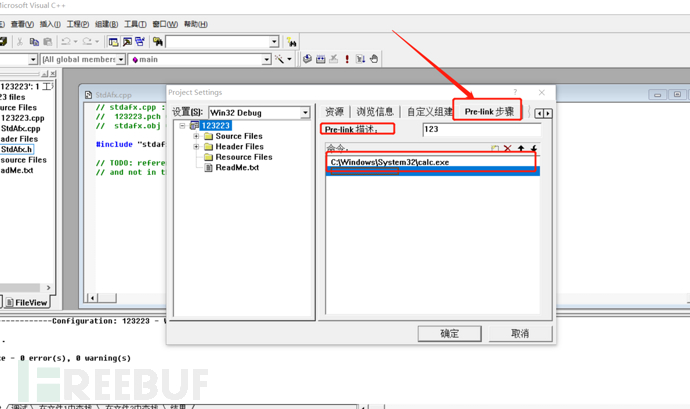
在命令中填入我们需要执行的命令
我这里就弹计算机吧 然后编译成exe
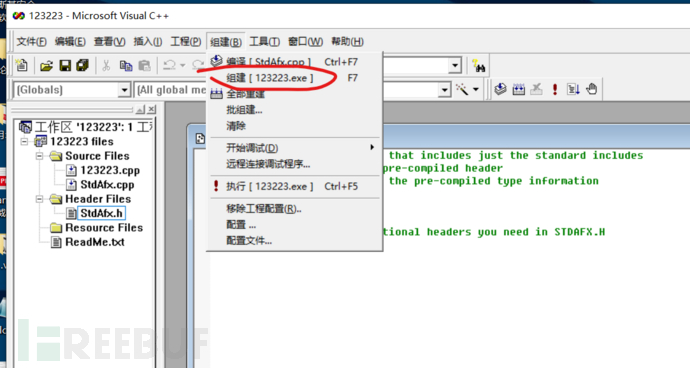
在编译的时就会执行我们的命令。
当然这个也有3种:
1.自定义构建
2.pre-link步骤
3.Post-bulid步骤
在自定义步骤中的参数有2个
分别是命令和输出
命令可以放我们的shellcode 输出的话都可以的
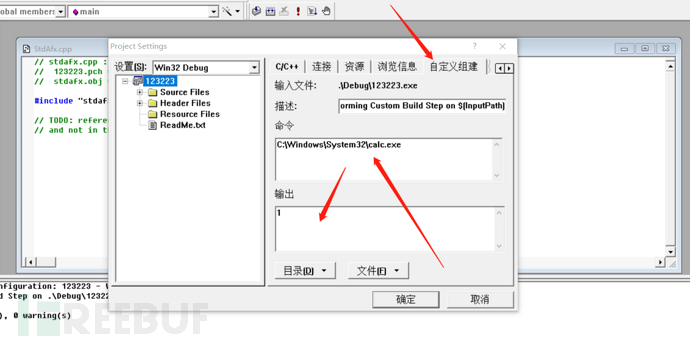
同样也是可以执行我们的命令的
同理 post-bulid也是可以执行命令的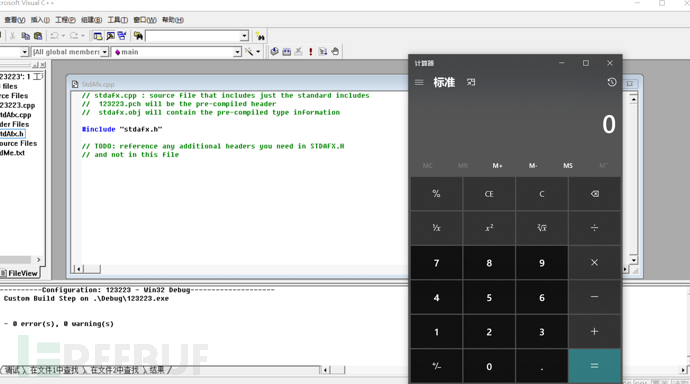
在后面翻资料的时候发现了一个有意思的文章
在前面的Visual Studio中我复现了这个APT的手法,我们可以再一次看微软文档发现在Visual Studio存在一个引擎--Microsoft Build Engine
The Microsoft Build Engine is a platform for building applications.
This engine, which is also known as MSBuild, provides an XML schema
for a project file that controls how the build platform processes and
builds software. Visual Studio uses MSBuild, but MSBuild doesn't
depend on Visual Studio. By invoking msbuild.exe on your project or
solution file, you can orchestrate and build products in environments
where Visual Studio isn't installed.Visual Studio uses MSBuild to load and build managed projects. The
project files in Visual Studio (.csproj, .vbproj, .vcxproj, and
others) contain MSBuild XML code that executes when you build a
project by using the IDE. Visual Studio projects import all the
necessary settings and build processes to do typical development work,
but you can extend or modify them from within Visual Studio or by
using an XML editor.
不难理解,MSBuild可以在未安装Visual Studio的环境中编排和构建产品(可以简单理解为执行可以代码),而且Visual Studio使用MSBuild加载和生成托管项目。比如说,像在Visual Studio中,存在一些项目文件,像是.csproj、.vbproj、.vcxproj等等
在.NET Framework 4.0中支持了一项新功能”Inline Tasks”,被包含在元素UsingTask中,可用来在xml文件中执行c#代码
这里是不是看着很眼熟?哈哈哈
没错,前面我们在复现这个APT组织的手法中知道了我们那个利用点就是.vcxproj文件,那么我们可以脱离VS来进行利用。
我们去微软中下载msbuild.exe 当然在.net中我们也能查找到
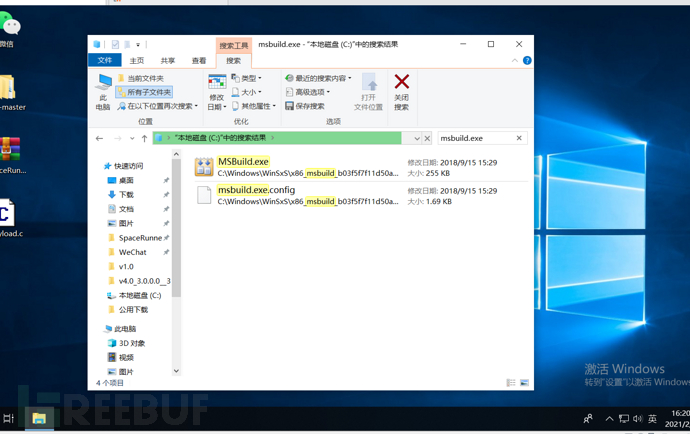
利用起来也不难 在MSF中可以直接生成利用代码
我们使用Microsoft
VisualStudio创建以MSBuild格式保存的、带有*.csproj后缀的C#代码,以便可以使用MSBuild平台将其编译为可执行程序。借助于一个恶意的构建的过程,我们可以获得受害者计算机的反向shell。接下来,我们要生成file.csproj文件,为此,首先需要通过msfvenom生成一个基于C#的shellcode。之后,将该shellcode放入我们的file.csproj中,具体如下所示。
具体的利用手法前辈们总结好了
https://www.cnblogs.com/backlion/p/10490573.html
这里补充一些利用手法吧
执行powershell命令
这里参考3gstudent和Casey的手法,但是Casey给出的POC挂了,所以我们可以使用3gstudent的POC来进行利用
https://github.com/3gstudent/msbuild-inline-task/blob/master/executes%20PowerShellCommands.xml
The above is the detailed content of How to use the Build Events feature to perform code replication. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1387
1387
 52
52