What is the onion mode proxy of SQLMAP?
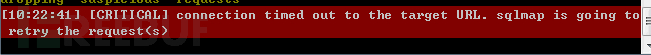
Due to the need to conduct penetration testing on external websites, most websites have access frequency control. Once this frequency is exceeded, the IP will be banned directly. This problem is particularly prominent when running SQLMAP. When SQLMAP is not completely run, it will directly exit with an error and the interface will be red.
So I started to study the proxy mode of SQLMAP. SQLMAP has two proxy modes, one is a normal proxy (HTTP proxy) and the other is an onion proxy.
Although I have the application of ordinary agents to write about, I found that Baidu has already elaborated it in detail, so I will not repeat it again. Sqlmap Extension—External IP Proxy Pool Implementation
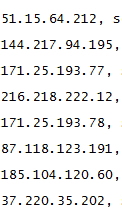
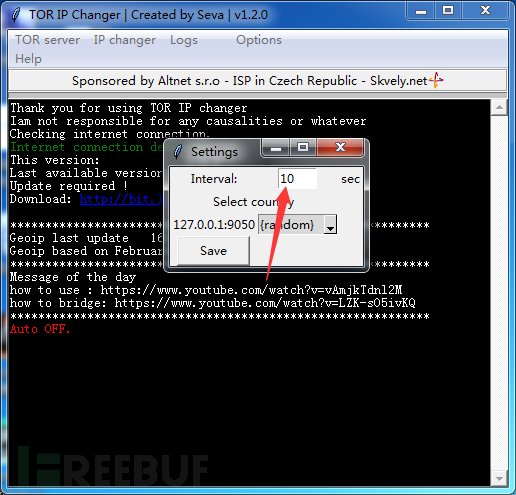
Let’s focus on the onion proxy. At the beginning, when I used onion directly for injection, there was no “aunt red” report. Later, as the number of penetrated websites increased, I found that tor was still There is an error reporting problem. I am thinking whether the tor module in SQLMAP does not have the function of automatically switching IP.
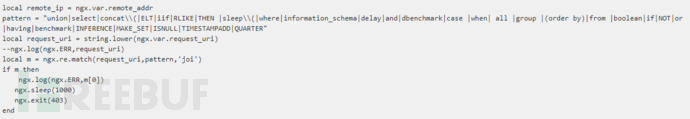
So I wrote a code test to simulate the situation where the IP is directly banned when the intrusion detection system detects the injection. I use a delay of 1000 seconds here, and sqlmap will report an error.
MaxCircuitDirtiness 1
##
The above is the detailed content of What is the onion mode proxy of SQLMAP?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1379
1379
 52
52
 Sample analysis of Sqlmap automated injection
May 13, 2023 pm 03:31 PM
Sample analysis of Sqlmap automated injection
May 13, 2023 pm 03:31 PM
Use sqlmap to automate injection into dvwa, set the dvwa level to low, open dvwa's SQLInjection (SQLInjection(Blind)), open browser debugging, enter the userid and submit, and view the intercepted requests. You can see that it is a GET request, the url "http://192.168.1.222:8089/dvwa/vulnerabilities/sqli/?id=1&Submit=Submit#" We put it directly into salmap to test it, use the -u command -u"http ://192.168.1.22
 How to analyze problems with sqlmap
May 27, 2023 pm 01:07 PM
How to analyze problems with sqlmap
May 27, 2023 pm 01:07 PM
0x00 Overview Recently, I encountered a strange phenomenon when using sqlmap injection testing. The higher version of sqlmap cannot detect the injection, but the lower version can detect the injection, and the data can be run out, which is not a false positive. After comparative testing and viewing the sqlmap source code, Found two small holes. 0x01 scenario reproduction injection point format: json..."whereparams":[{"name":"keyWord","value":"test"}]} Injectable parameters: valuesqlmap command: pythonsqlmap.py-rsqlpk.txt– flush-session-vvsqlmapv1.2.11 cannot inject s
 How to analyze SQLMap and SQLi injection defense
May 11, 2023 pm 06:37 PM
How to analyze SQLMap and SQLi injection defense
May 11, 2023 pm 06:37 PM
Part One: Using Sqlmap 1.1 Introduction to sqlmap 1. I mentioned some basic statements of sql injection, but manual injection is very troublesome. We can use sqlmap, a powerful sql injection tool, to obtain data. 2. Introduction to sqlmap (1)# sqlmap is an open source penetration testing tool that can automatically detect and exploit SQL injection vulnerabilities and servers connected to the database. It has a very powerful detection engine, a penetration tester with multiple features, access the underlying file system through database fingerprinting and execute commands over an out-of-band connection. Official website: sqlmap.org(2)#Supported databases: MySQL, Oracle, PostgreS
 What is the onion mode proxy of SQLMAP?
May 26, 2023 am 09:56 AM
What is the onion mode proxy of SQLMAP?
May 26, 2023 am 09:56 AM
Because it is necessary to conduct penetration testing on external websites, most websites have access frequency control. Once this frequency is exceeded, the IP will be banned directly. Especially when SQLMAP is running, it is even more "aunty red", and an error is reported and exited before SQLMAP is finished running. So I started to study the proxy mode of SQLMAP. SQLMAP has two proxy modes, one is a normal proxy (HTTP proxy) and the other is an onion proxy. I originally wanted to write about the application of ordinary agents, but Baidu saw that this article was detailed enough and stopped talking nonsense. Sqlmap extension - External IP proxy pool implementation Let’s focus on the onion proxy. At the beginning, when onion was used directly for injection, there was no “aunt red” report. Later, as the number of penetrated websites increased,
 What is the sqlmap _dns injection configuration method?
May 12, 2023 pm 12:25 PM
What is the sqlmap _dns injection configuration method?
May 12, 2023 pm 12:25 PM
There are too few related articles on dns injection for sqlmap on the Internet. They only briefly introduce the --dns-domain parameter. The relevant practical articles are either vague or mentioned in one stroke, which is confusing (mainly dishonest, the key is not yet Big boss). Then I did it again by referring to the methods on the Internet. Things that need to be prepared include one sqlmap, windows blind injection, two domain names, and an external network server. One time when I was doing something, I came across a time blind injection. It happened to be a Windows machine, and I remembered the method of dns injection. Before starting, I plan to use the --sql-shell command of sqlmap to test the dns injection payload. First, go to burpsuite.
 How to implement analysis of sqlmap time-based inject
May 12, 2023 pm 12:10 PM
How to implement analysis of sqlmap time-based inject
May 12, 2023 pm 12:10 PM
1. Preface How to detect SQL injection? My answer is: When Party A is doing security, SQL injection detection is relatively easy to do. 1) Error injection detection. 2) Don’t inject bool error reports as false positives are relatively high. 3) Do time-based time injection, contact operation and maintenance to do slow log db recording, monitor sleep, and benchmark keyword monitoring. You can add the ID number of the scanning task to the decimal point of the sleep time to facilitate positioning. (p.s. This method can find 99% of SQL injections) Therefore, when doing time-based time injection, I limit the time error very harshly. However, @chengable is doing security-related work in Party B, based on t
 The idea of sqlmap processing sign encryption
May 14, 2023 am 11:52 AM
The idea of sqlmap processing sign encryption
May 14, 2023 am 11:52 AM
When I tested the company's APP, I found that we added a 32-bit character to all parameter contents and finally performed MD5 encryption. Since the APP processing process first verifies whether the sign is correct, if the signature verification fails, it will not be able to enter the database at all. In order to use SQLMAP to test it, I wrote a script for proxy data. After intercepting the data packet , perform encrypted replacement of its parameter content and 32 characters. Note: This script is suitable for the company's internal system, because you can know the encryption process; or you can get the encryption method of the front-end JS. First, I wrote a program using Django to simulate the company's system. The process was to obtain the POST ID and token, and add a custom encrypted word.
 How to use sqlmapGetshell
May 13, 2023 pm 06:25 PM
How to use sqlmapGetshell
May 13, 2023 pm 06:25 PM
sqlmap reads and writes files –file-read: reads files from the back-end database management system file system –file-write: edits local files on the back-end database management system file system (writes from local) –file-dest : The absolute path to the file written by the back-end database management system (write target path). You can use the above commands to read and write the system file after SQL injection, but the prerequisite is that you need to have read and write permissions and be a dba. permissions, otherwise read and write operations cannot be performed successfully. Taking DVWA as an example, build DVWA under kali to read and write files. Read the file: Check the relevant information in PHPinfo, use -file-r




