Analysis of commands related to redis's list data type and how to use them
#List introduction
list is a string array sorted in insertion order (in layman terms, it still stores strings ). You can add an element to the head (left) or tail (right) of a list, and a list can contain up to ^32-1 elements (over 4 billion elements per list).
The list in Redis is very similar to the LinkedList in Java. The bottom layer is a linked list structure. The insertion and deletion operations of the list are very fast, with a time complexity of 0(1). Unlike array structure insertion and deletion operations, data needs to be moved. Although still ostensibly a list, the underlying implementation of lists in Redis is not limited to simple doubly linked lists.
When the amount of data is small, its underlying storage structure is a piece of continuous memory, called ziplist (compressed list), which stores all elements closely together and allocates is a continuous piece of memory; when the amount of data is large, it will become a quicklist (quick linked list) structure.
But a simple linked list is also flawed. The prev and next pointers of the linked list will occupy more memory, waste space, and increase memory fragmentation. Since Redis 3.2, Redis uses the hybrid data structure quicklist (quick linked list), which consists of ziplist and linked list.
Common commands
Add command
lpush key value
Insert an element from the left Or multiple values are inserted into the head of the list)
127.0.0.1:6379> lpush ids 1 (integer) 1 127.0.0.1:6379> lrange ids 0 -1 1) "1" 127.0.0.1:6379> lpush ids 2 (integer) 2 127.0.0.1:6379> lrange ids 0 -1 1) "2" 2) "1"
rpush key value
Insert elements from the right (Insert one or more values into the tail of the list (most Right))
127.0.0.1:6379> rpush ids 3 (integer) 3 127.0.0.1:6379> lrange ids 0 -1 1) "2" 2) "1" 3) "3"
linsert key BEFORE|AFTER pivot value
Insert an element before/after an element. The return result is the length of the current list. Note that the list does not exist or the specified element If it does not exist in the list, no action will be performed.
//元素3前插入0 127.0.0.1:6379> linsert ids before 3 0 (integer) 4 127.0.0.1:6379> lrange ids 0 -1 1) "2" 2) "1" 3) "0" 4) "3" //元素3后插入0 127.0.0.1:6379> linsert ids after 3 4 (integer) 5 127.0.0.1:6379> lrange ids 0 -1 1) "2" 2) "1" 3) "0" 4) "3" 5) "4"
Query command
lrange key start end
Get the list of elements within the specified range in the list; if the start value is greater than the list end value, an empty list is returned
As shown above
lindex key index
Get the element at the specified index in the list
127.0.0.1:6379> lindex ids 0 "2" 127.0.0.1:6379> lindex ids -1 "4"
llen key
Get the length of the list; if the list does not exist, return 0
127.0.0.1:6379> llen ids (integer) 5
Pop/delete command
lpop key
Pop the element from the left side of the list and return the head element
127.0.0.1:6379> lpop ids "2" 127.0.0.1:6379> lrange ids 0 -1 1) "1" 2) "0" 3) "3" 4) "4"
rpop key
Pop the element from the right side of the list and return the tail element
127.0.0.1:6379> rpop ids "4" 127.0.0.1:6379> lrange ids 0 -1 1) "1" 2) "0" 3) "3"
lrem key count value
From the list Find the element equal to value and delete it. There are three situations according to the count:
count > 0, starting from the head of the table to the end of the table, remove count elements;
count < 0, Starting from the end of the table to the head, remove the absolute value of count elements;
count = 0, remove all values in the table that are equal to value
127.0.0.1:6379> lrem ids 0 3 (integer) 1 127.0.0.1:6379> lrange ids 0 -1 1) "1" 2) "0"
ltrim key start end
Trim a list, that is, let the list only retain elements within the specified range, and elements not within the specified range will be deleted
127.0.0.1:6379> ltrim ids 0 0 OK 127.0.0.1:6379> lrange ids 0 -1 1) "1"
Modify command
lset key index value
Modify the value of the element with the specified subscript and set it to value
127.0.0.1:6379> lset ids 0 0 OK 127.0.0.1:6379> lrange ids 0 -1 1) "0"
Block pop-up command
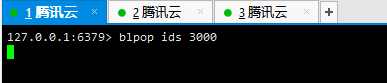
blpop key [key …] timeout
Remove and get the first element of the list. If there is no element in the list, the list will be blocked until the waiting timeout (in seconds) or a pop-up element is found
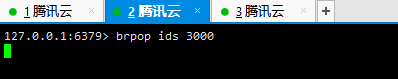
brpop key [key …] timeout
Remove and get the last element of the list. If there is no element in the list, the list will be blocked until the wait times out or a pop-up element is found.
Demo:
Open three reids connection windows, the first one executes blpop, the second Execute brpop, and add the third execution:
You can see that windows 1 and 2 have been blocked here after execution. This is because there are no elements in ids
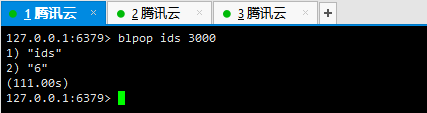
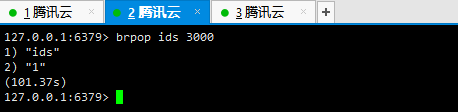
Window 3 executes the addition: lpush ids 1 2 3 4 5 6
You can see that the corresponding elements pop up immediately in windows 1 and 2:
Application scenarios
Message queue: lpop and rpush (or conversely, lpush and rpop) can realize the function of the queue
Like list of friends circle , comment list, ranking list: The lpush command and the lrange command can realize the function of the latest list. Each time, a new element is inserted into the list through the lpush command, and then the latest element list is read through the lrange command.
The above is the detailed content of Analysis of commands related to redis's list data type and how to use them. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1382
1382
 52
52
 How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
Redis cluster mode deploys Redis instances to multiple servers through sharding, improving scalability and availability. The construction steps are as follows: Create odd Redis instances with different ports; Create 3 sentinel instances, monitor Redis instances and failover; configure sentinel configuration files, add monitoring Redis instance information and failover settings; configure Redis instance configuration files, enable cluster mode and specify the cluster information file path; create nodes.conf file, containing information of each Redis instance; start the cluster, execute the create command to create a cluster and specify the number of replicas; log in to the cluster to execute the CLUSTER INFO command to verify the cluster status; make
 How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear Redis data: Use the FLUSHALL command to clear all key values. Use the FLUSHDB command to clear the key value of the currently selected database. Use SELECT to switch databases, and then use FLUSHDB to clear multiple databases. Use the DEL command to delete a specific key. Use the redis-cli tool to clear the data.
 How to use the redis command
Apr 10, 2025 pm 08:45 PM
How to use the redis command
Apr 10, 2025 pm 08:45 PM
Using the Redis directive requires the following steps: Open the Redis client. Enter the command (verb key value). Provides the required parameters (varies from instruction to instruction). Press Enter to execute the command. Redis returns a response indicating the result of the operation (usually OK or -ERR).
 How to use redis lock
Apr 10, 2025 pm 08:39 PM
How to use redis lock
Apr 10, 2025 pm 08:39 PM
Using Redis to lock operations requires obtaining the lock through the SETNX command, and then using the EXPIRE command to set the expiration time. The specific steps are: (1) Use the SETNX command to try to set a key-value pair; (2) Use the EXPIRE command to set the expiration time for the lock; (3) Use the DEL command to delete the lock when the lock is no longer needed.
 How to read redis queue
Apr 10, 2025 pm 10:12 PM
How to read redis queue
Apr 10, 2025 pm 10:12 PM
To read a queue from Redis, you need to get the queue name, read the elements using the LPOP command, and process the empty queue. The specific steps are as follows: Get the queue name: name it with the prefix of "queue:" such as "queue:my-queue". Use the LPOP command: Eject the element from the head of the queue and return its value, such as LPOP queue:my-queue. Processing empty queues: If the queue is empty, LPOP returns nil, and you can check whether the queue exists before reading the element.
 How to implement the underlying redis
Apr 10, 2025 pm 07:21 PM
How to implement the underlying redis
Apr 10, 2025 pm 07:21 PM
Redis uses hash tables to store data and supports data structures such as strings, lists, hash tables, collections and ordered collections. Redis persists data through snapshots (RDB) and append write-only (AOF) mechanisms. Redis uses master-slave replication to improve data availability. Redis uses a single-threaded event loop to handle connections and commands to ensure data atomicity and consistency. Redis sets the expiration time for the key and uses the lazy delete mechanism to delete the expiration key.
 How to read the source code of redis
Apr 10, 2025 pm 08:27 PM
How to read the source code of redis
Apr 10, 2025 pm 08:27 PM
The best way to understand Redis source code is to go step by step: get familiar with the basics of Redis. Select a specific module or function as the starting point. Start with the entry point of the module or function and view the code line by line. View the code through the function call chain. Be familiar with the underlying data structures used by Redis. Identify the algorithm used by Redis.
 How to make message middleware for redis
Apr 10, 2025 pm 07:51 PM
How to make message middleware for redis
Apr 10, 2025 pm 07:51 PM
Redis, as a message middleware, supports production-consumption models, can persist messages and ensure reliable delivery. Using Redis as the message middleware enables low latency, reliable and scalable messaging.




