What does buffer underflow in C/C++ programs mean?
1, Buffer Underflow
This article will describe another buffer overflow situation, that is, buffer underflow. Buffer overflow has been analyzed in the previous topic (see Issue 7). The same reasons apply to buffer underflows, so the factors that cause buffer overflows will not be repeated in this article. To put it simply, buffer underflow refers to the situation where the next-level buffer is overwritten when the filling data overflows. This article describes the dangers of buffer underflow, its signs in source code, and how to fix the problem.
2. The dangers of buffer underflow
In C/C programs, buffer underflow is a serious vulnerability type that may cause the program to crash or Consequences such as executing malicious code. From January to October 2018, a total of 494 pieces of CVE vulnerability information were involved. Some of the vulnerabilities are as follows:
| Vulnerability Overview | |
|---|---|
| Libc Realpath buffer underflow vulnerability. The vulnerability occurs because the GNU C library does not correctly handle the relative path returned by the getcwd() system call. Other libraries It is also likely to be affected by this. On affected systems, root privileges can be obtained via the SUID binary. | |
| zutils is a compressed file processing utility package. The program supports compression/decompression, compressed file comparison, and compressed file integrity verification. zcat is one of the decompression utilities. A buffer overflow vulnerability exists in zcat in versions prior to zutils 1.8-pre2. An attacker could exploit this vulnerability to cause a denial of service or execute arbitrary code using a specially crafted compressed file. | |
| strongSwan versions prior to 5.6.3 have a buffer underflow vulnerability in the implementation. An attacker can exploit this vulnerability to exhaust resources, resulting in Denial of service. |
3. Sample code
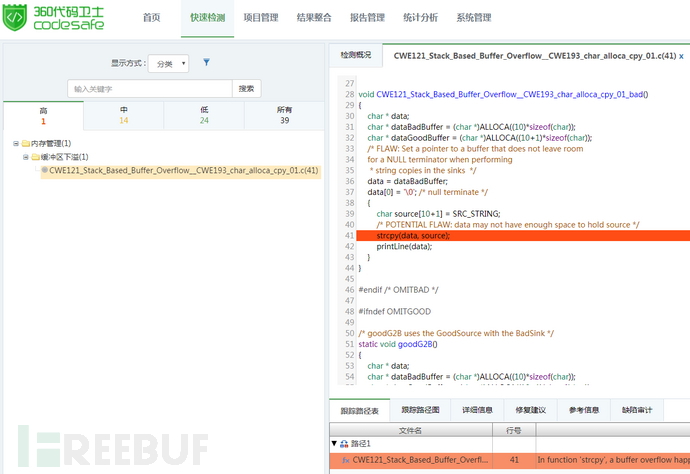
The example comes from Samate Juliet Test Suite for C/C v1.3 (https:// samate.nist.gov/SARD/testsuite.php), source file name: CWE121_Stack_Based_Buffer_Overflow__CWE193_char_alloca_cpy_01.c.3.1 Defect code
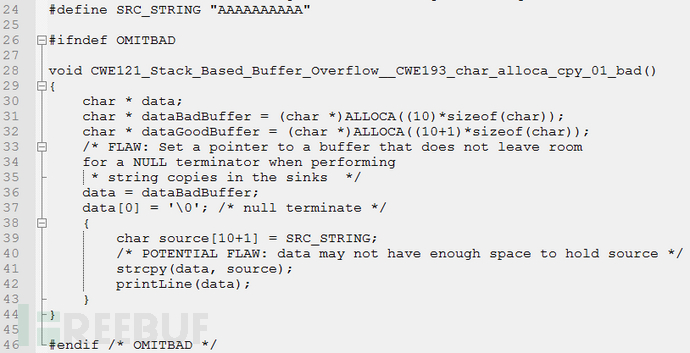
data is executed on line 36 Assignment, through the assignment operation, it can be seen that the pointer data points to dataBadBuffer. When strcpy() is used for memory copy in line 41, the source buffer length is larger than the destination The buffer length thus overflows, and the overflow part exceeds the lower boundary of dataBadBuffer, causing buffer underflow problems.
3.2 Repair code
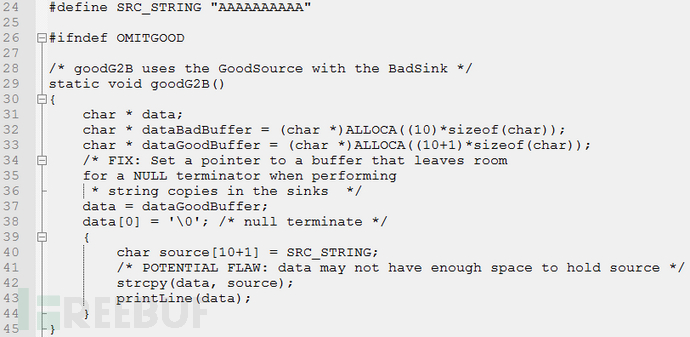
data in line 37, and replace dataPoints to dataGoodBuffer. At this time, the length of data is consistent with source. When strcpy() is used for copy operation in line 42, The source buffer is the same length as the destination buffer, thus avoiding buffer underflow problems. This problem can also be avoided through other methods such as boundary checks.

4. How to avoid buffer underflow
To avoid buffer underflow, you need to pay attention to the following points:(1) Try to avoid using unsafe memory operation functions.(2) For memory operation functions that have a clear indication of the return value, the function return value should be effectively judged to determine whether the operation is successful. (3) Boundary checking must be performed when filling data into the buffer.
The above is the detailed content of What does buffer underflow in C/C++ programs mean?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 C language data structure: data representation and operation of trees and graphs
Apr 04, 2025 am 11:18 AM
C language data structure: data representation and operation of trees and graphs
Apr 04, 2025 am 11:18 AM
C language data structure: The data representation of the tree and graph is a hierarchical data structure consisting of nodes. Each node contains a data element and a pointer to its child nodes. The binary tree is a special type of tree. Each node has at most two child nodes. The data represents structTreeNode{intdata;structTreeNode*left;structTreeNode*right;}; Operation creates a tree traversal tree (predecision, in-order, and later order) search tree insertion node deletes node graph is a collection of data structures, where elements are vertices, and they can be connected together through edges with right or unrighted data representing neighbors.
 The truth behind the C language file operation problem
Apr 04, 2025 am 11:24 AM
The truth behind the C language file operation problem
Apr 04, 2025 am 11:24 AM
The truth about file operation problems: file opening failed: insufficient permissions, wrong paths, and file occupied. Data writing failed: the buffer is full, the file is not writable, and the disk space is insufficient. Other FAQs: slow file traversal, incorrect text file encoding, and binary file reading errors.
 How to output a countdown in C language
Apr 04, 2025 am 08:54 AM
How to output a countdown in C language
Apr 04, 2025 am 08:54 AM
How to output a countdown in C? Answer: Use loop statements. Steps: 1. Define the variable n and store the countdown number to output; 2. Use the while loop to continuously print n until n is less than 1; 3. In the loop body, print out the value of n; 4. At the end of the loop, subtract n by 1 to output the next smaller reciprocal.
 What are the types of return values of c language function? Summary of types of return values of c language function?
Apr 03, 2025 pm 11:18 PM
What are the types of return values of c language function? Summary of types of return values of c language function?
Apr 03, 2025 pm 11:18 PM
The return value types of C language function include int, float, double, char, void and pointer types. int is used to return integers, float and double are used to return floats, and char returns characters. void means that the function does not return any value. The pointer type returns the memory address, be careful to avoid memory leakage.结构体或联合体可返回多个相关数据。
 The concept of c language functions and their definition format
Apr 03, 2025 pm 11:33 PM
The concept of c language functions and their definition format
Apr 03, 2025 pm 11:33 PM
C language functions are reusable code blocks, receive parameters for processing, and return results. It is similar to the Swiss Army Knife, powerful and requires careful use. Functions include elements such as defining formats, parameters, return values, and function bodies. Advanced usage includes function pointers, recursive functions, and callback functions. Common errors are type mismatch and forgetting to declare prototypes. Debugging skills include printing variables and using a debugger. Performance optimization uses inline functions. Function design should follow the principle of single responsibility. Proficiency in C language functions can significantly improve programming efficiency and code quality.
 What are the pointer parameters in the parentheses of the C language function?
Apr 03, 2025 pm 11:48 PM
What are the pointer parameters in the parentheses of the C language function?
Apr 03, 2025 pm 11:48 PM
The pointer parameters of C language function directly operate the memory area passed by the caller, including pointers to integers, strings, or structures. When using pointer parameters, you need to be careful to modify the memory pointed to by the pointer to avoid errors or memory problems. For double pointers to strings, modifying the pointer itself will lead to pointing to new strings, and memory management needs to be paid attention to. When handling pointer parameters to structures or arrays, you need to carefully check the pointer type and boundaries to avoid out-of-bounds access.
 What are the rules for function definition and call in C language?
Apr 03, 2025 pm 11:57 PM
What are the rules for function definition and call in C language?
Apr 03, 2025 pm 11:57 PM
A C language function consists of a parameter list, function body, return value type and function name. When a function is called, the parameters are copied to the function through the value transfer mechanism, and will not affect external variables. Pointer passes directly to the memory address, modifying the pointer will affect external variables. Function prototype declaration is used to inform the compiler of function signatures to avoid compilation errors. Stack space is used to store function local variables and parameters. Too much recursion or too much space can cause stack overflow.
 Tutorial on how to represent the greatest common divisor in C language functions
Apr 03, 2025 pm 11:21 PM
Tutorial on how to represent the greatest common divisor in C language functions
Apr 03, 2025 pm 11:21 PM
Methods to efficiently and elegantly find the greatest common divisor in C language: use phase division to solve by constantly dividing the remainder until the remainder is 0. Two implementation methods are provided: recursion and iteration are concise and clear, and the iterative implementation is higher and more stable. Pay attention to handling negative numbers and 0s, and consider performance optimization, but the phase division itself is efficient enough.






