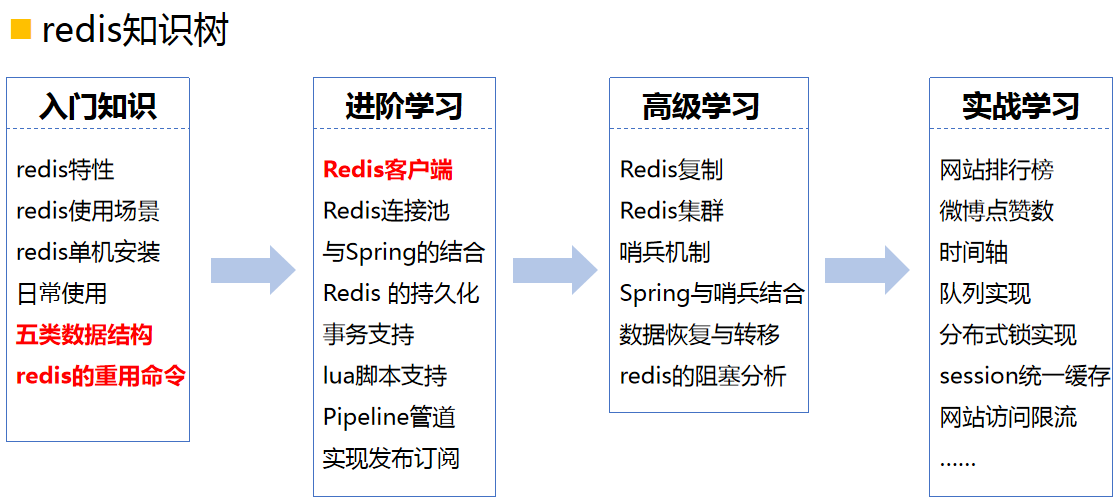
What are the high-end technologies of Java?
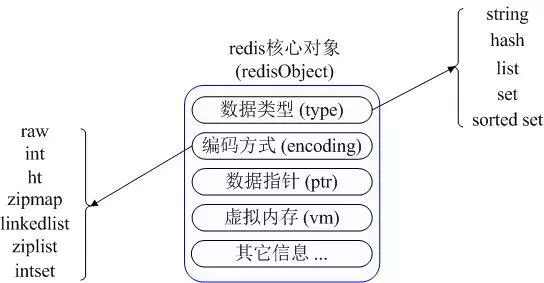
Commonly used data types in Redis
The five commonly used data types in Redis are: String, Hash, List, Set and Sorted set
Redis usage scenarios
1.Counting
2.Display the top list of the latest, hottest, highest click rate, highest activity, etc.
3.The user’s recent access records are also Very good application scenarios of redis list
4. Write and consume the queue through the lpop and lpush interfaces of the list
5. The functional expansion of Redis's Lua actually brings more application scenarios to Redis. You You can write several command combinations as a small non-blocking transaction or update logic
6. The master-slave data synchronization function provided by Redis is actually a powerful functional extension of the cache
Summary
So many applications are inseparable from all the features of Redis
Uncover the mystery of Redis
Redis is an open source (KEY-VALUE key-value pair) , an in-memory data structure server that can be used as a database, cache, and message queue agent. It adopts a single-process single-thread model and has strong concurrency capabilities. It is the mainstream distributed caching tool in the current Internet architecture.
Redis high-performance cache architecture design
1. Architecture design
Since redis is a single point, the project If you need to use it, you must implement distribution yourself. The basic architecture diagram is as follows:
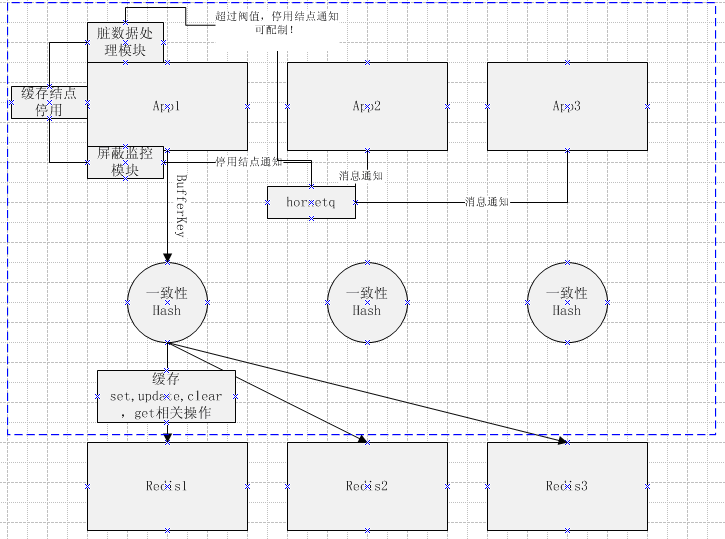
2. Distributed implementation
Do consistent hashing through key to achieve key correspondence The distribution of redis nodes.
Implementation of consistent hashing:
Hash value calculation: By supporting two calculation methods, MD5 and MurmurHash, MurmurHash is used by default for efficient hash calculation.
Achievement of consistency: simulate the ring structure through java's TreeMap to achieve uniform distribution
3.Client selection
For jedis modification The main thing is the modification of the partition module, so that it supports partitioning based on BufferKey. Different ShardInfo can be initialized based on different redis node information. At the same time, the underlying implementation of JedisPool is also modified so that the connection pool pool supports following data. The construction method of key and value creates different jedis connection clients according to different ShardInfos to achieve the effect of partitioning and is called by the application layer
4. Module description
Dirty data processing module, handles failed cache operations.
Shield monitoring module, for abnormal monitoring of jedis operations, when an abnormality occurs in a node, it can control the removal of redis nodes and other operations.
The entire distributed module uses hornetq to remove abnormal redis nodes. The addition of new nodes can also be achieved through the reload method. (This module can also be easily implemented for adding new nodes)
The above is the detailed content of What are the high-end technologies of Java?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1359
1359
 52
52
 Square Root in Java
Aug 30, 2024 pm 04:26 PM
Square Root in Java
Aug 30, 2024 pm 04:26 PM
Guide to Square Root in Java. Here we discuss how Square Root works in Java with example and its code implementation respectively.
 Perfect Number in Java
Aug 30, 2024 pm 04:28 PM
Perfect Number in Java
Aug 30, 2024 pm 04:28 PM
Guide to Perfect Number in Java. Here we discuss the Definition, How to check Perfect number in Java?, examples with code implementation.
 Random Number Generator in Java
Aug 30, 2024 pm 04:27 PM
Random Number Generator in Java
Aug 30, 2024 pm 04:27 PM
Guide to Random Number Generator in Java. Here we discuss Functions in Java with examples and two different Generators with ther examples.
 Armstrong Number in Java
Aug 30, 2024 pm 04:26 PM
Armstrong Number in Java
Aug 30, 2024 pm 04:26 PM
Guide to the Armstrong Number in Java. Here we discuss an introduction to Armstrong's number in java along with some of the code.
 Weka in Java
Aug 30, 2024 pm 04:28 PM
Weka in Java
Aug 30, 2024 pm 04:28 PM
Guide to Weka in Java. Here we discuss the Introduction, how to use weka java, the type of platform, and advantages with examples.
 Smith Number in Java
Aug 30, 2024 pm 04:28 PM
Smith Number in Java
Aug 30, 2024 pm 04:28 PM
Guide to Smith Number in Java. Here we discuss the Definition, How to check smith number in Java? example with code implementation.
 Java Spring Interview Questions
Aug 30, 2024 pm 04:29 PM
Java Spring Interview Questions
Aug 30, 2024 pm 04:29 PM
In this article, we have kept the most asked Java Spring Interview Questions with their detailed answers. So that you can crack the interview.
 Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Break or return from Java 8 stream forEach?
Feb 07, 2025 pm 12:09 PM
Java 8 introduces the Stream API, providing a powerful and expressive way to process data collections. However, a common question when using Stream is: How to break or return from a forEach operation? Traditional loops allow for early interruption or return, but Stream's forEach method does not directly support this method. This article will explain the reasons and explore alternative methods for implementing premature termination in Stream processing systems. Further reading: Java Stream API improvements Understand Stream forEach The forEach method is a terminal operation that performs one operation on each element in the Stream. Its design intention is




