How to implement Redis distributed cache and flash sales
1. Problems with single-point Redis
1. Data loss problem
Redis data persistence.
2. Concurrency issue
Our master-slave cluster realizes the separation of reading and writing.
3. Failure recovery issues
Use Redis Sentinel to implement health detection and automatic recovery.
4. Storage capacity issue
Build a sharded cluster and use the slot mechanism to achieve dynamic expansion.
2. RDB
RDB's full name is Redis Database Backup file (Redis data backup file), also called Redis data snapshot. To put it simply, all the data in the memory is recorded to the disk. When the Redis instance fails and restarts, the snapshot file is read from the disk and the data is restored.
The snapshot file is called an RDB file and is saved in the current running directory by default.
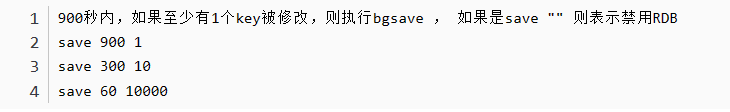
There is a mechanism to trigger RDB inside Redis, which can be found in the redis.conf file. The format is as follows:
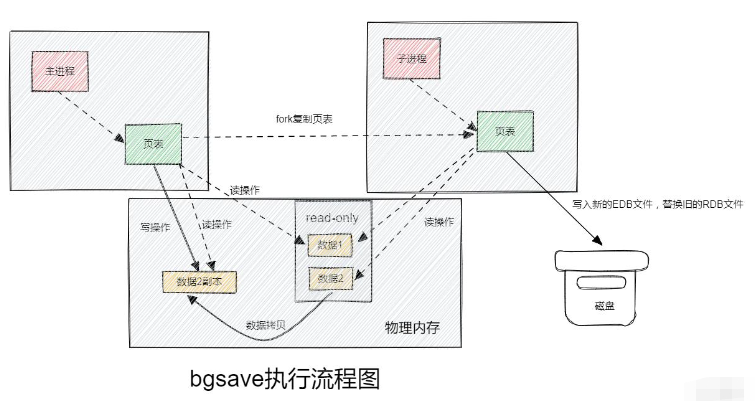
When the bgsave command is executed, fork will be passed. The system call creates a child process that shares memory data with the main process. After completing the fork, read the memory data and write it to the RDB file.
Fork uses copy-on-write technology:
When the main process performs a read operation, it accesses the shared memory;
When the main process performs a write operation, it will copy a copy of the data and perform the write operation;
The basic process of RDB mode bgsave?
Fork the main process to get a child process and share the memory space;
The child process reads the memory data and writes a new RDB file;
Replace the old RDB file with the new RDB file;
When will RDB be executed? What does save 60 1000 mean?
The default is when the service is stopped;
means that RDB will be triggered if at least 1000 modifications are performed within 60 seconds;
Disadvantages of RDB?
The RDB execution interval is long, and there is a risk of data loss between two RDB writes;
fork sub-process, compression, write It is time-consuming to export RDB files;
The frequency of AOF command recording can also be configured through the redis.conf file:
3. AOF
AOF stands for Append Only File. Every write command processed by Redis will be recorded in the AOF file, which can be regarded as a command log file.
AOF is turned off by default. You need to modify the redis.conf configuration file to enable AOF:

The frequency of AOF command recording can also be passed through redis.conf File to match:
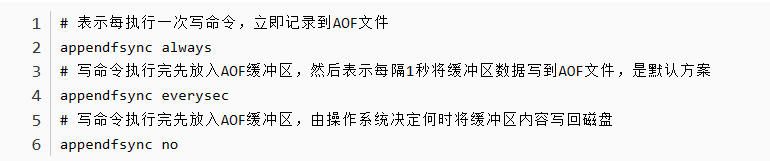
| Configuration items | Flush timing | Advantages | Disadvantages |
|---|---|---|---|
| Always | Synchronous disk flush | High reliability, almost no data loss | Great impact on performance |
| everysec | Flash disk per second | Moderate performance | Lost data for up to one minute |
| no | Operating system control | Best performance | Poor reliability, may lose a lot of data |
Because it is a recording command, the AOF file will be much larger than the RDB file. Although AOF will record multiple write operations to the same key, only the last write operation among them is meaningful. You can use the bgrewriteaof command to complete the AOF file rewriting function with the minimum number of commands.
set id 1 set name nezha set id 2 bgrewriteaof mset name nezha id 2
Redis will also automatically rewrite the AOF file when the threshold is triggered. The threshold can also be configured in redis.conf:
# If the AOF file grows by more than the last file, the rewrite will be triggered. auto-aof-rewrite-percentage 100# What is the minimum size of the AOF file? Trigger rewrite auto-aof-rewrite-min-size 64mb
RDB and AOF each have their own advantages and disadvantages. If the data security requirements are high, the two are often combined in actual development to use.
| AOF | ||
|---|---|---|
| Regular snapshots of the entire memory | Record every executed command | |
| Incomplete, between two backups Will lose | Relatively complete, depends on the brushing strategy | |
| There will be compression, the file size is small | records command, the file size is very large | |
| Quickly | Slow | |
| Low, because data integrity is not low | High, because data integrity is higher | |
| High, a lot of CPU and memory consumption | Low, mainly disk IO resources, but AOF rewriting will occupy a lot of CPU and memory resources | |
| Can tolerate data loss for several minutes and pursue faster startup speed | Common with higher requirements for data security |
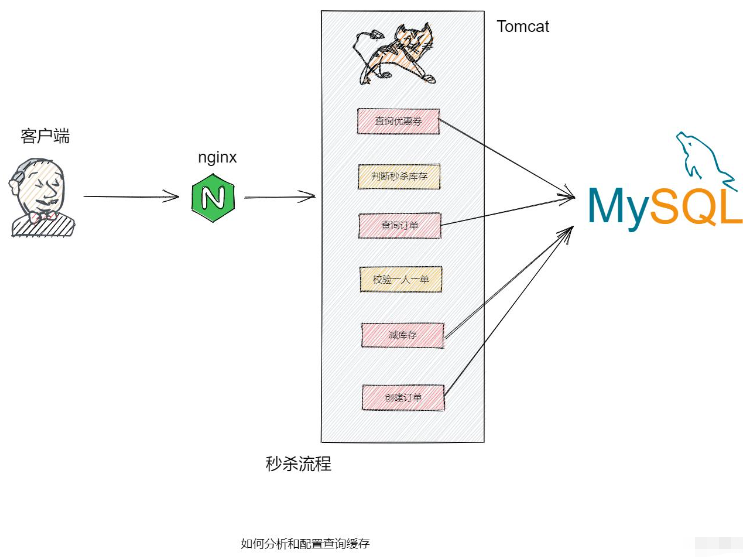
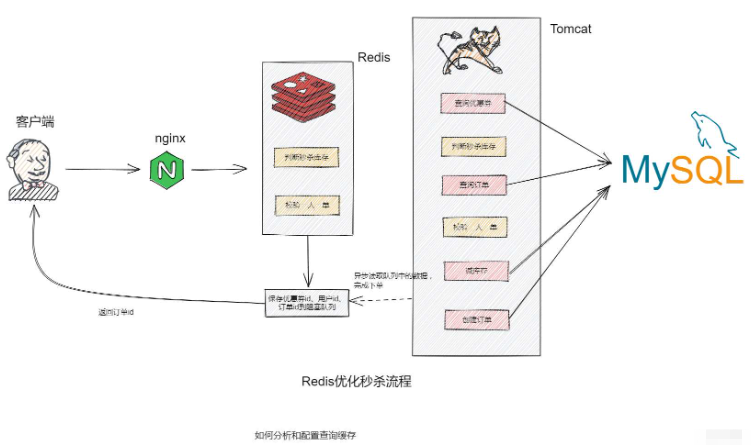
- Query coupons;
- Judge flash sale product inventory;
- Query order
- Verify one order per person;
- Reduce inventory;
- Create an order;
- Add flash sale coupons and save the coupon information to Redis;
- Based on Lua script, determine the flash sale product inventory, one person per order, determine whether the user's flash sale is successful;
- If the flash sale is successful, encapsulate the coupon id, user id, and product id into the blocking queue;
- Start the asynchronous task and continuously remove the items from the blocking queue Read information and implement asynchronous ordering function;
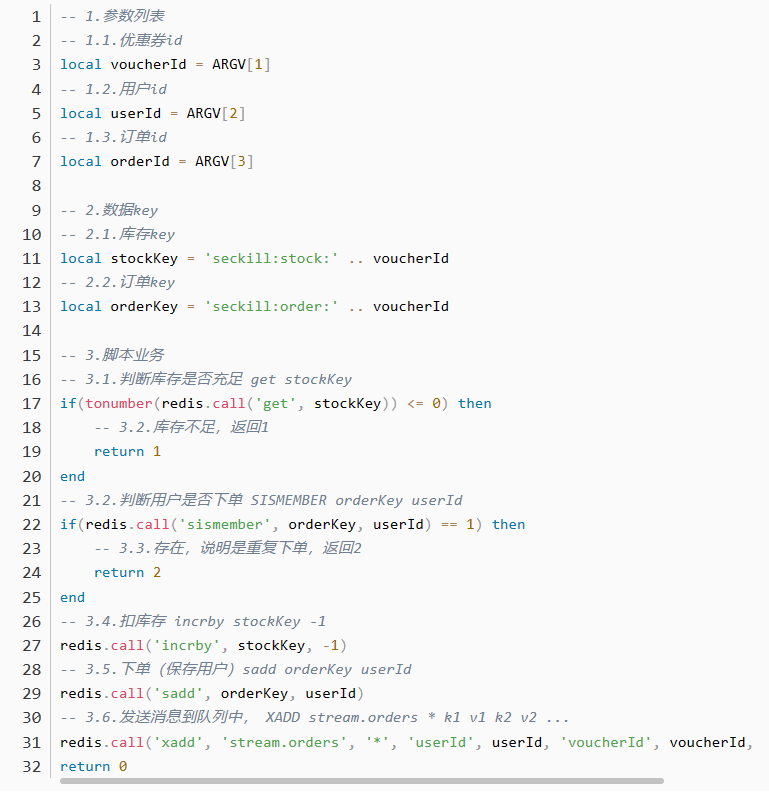
public Result seckillVoucher(Long voucherId) {
Long userId = UserHolder.getUser().getId();
long orderId = redisIdWorker.nextId("order");
// 1.执行lua脚本
Long result = stringRedisTemplate.execute(
SECKILL_SCRIPT,
Collections.emptyList(),
voucherId.toString(), userId.toString(), String.valueOf(orderId)
);
int r = result.intValue();
// 2.判断结果是否为0
if (r != 0) {
// 2.1.不为0 ,代表没有购买资格
return Result.fail(r == 1 ? "库存不足" : "不能重复下单");
}
// 3.返回订单id
return Result.ok(orderId);
}Copy after login
5. Through the thread pool, operate the blocking queuepublic Result seckillVoucher(Long voucherId) {
Long userId = UserHolder.getUser().getId();
long orderId = redisIdWorker.nextId("order");
// 1.执行lua脚本
Long result = stringRedisTemplate.execute(
SECKILL_SCRIPT,
Collections.emptyList(),
voucherId.toString(), userId.toString(), String.valueOf(orderId)
);
int r = result.intValue();
// 2.判断结果是否为0
if (r != 0) {
// 2.1.不为0 ,代表没有购买资格
return Result.fail(r == 1 ? "库存不足" : "不能重复下单");
}
// 3.返回订单id
return Result.ok(orderId);
}// 线程池
private static final ExecutorService SECKILL_ORDER_EXECUTOR = Executors.newSingleThreadExecutor();
/**
* 在类初始化完成后执行
*/
@PostConstruct
private void init() {
SECKILL_ORDER_EXECUTOR.submit(new VoucherOrderHandler());
}
// 阻塞队列
private BlockingQueue<VoucherOrder> orderTasks = new ArrayBlockingQueue<>(1024 * 1024);
private class OrderHandler implements Runnable{
@Override
public void run() {
while (true){
try {
doSomething();
} catch (Exception e) {
log.error("处理订单异常", e);
}
}
}
}Copy after login
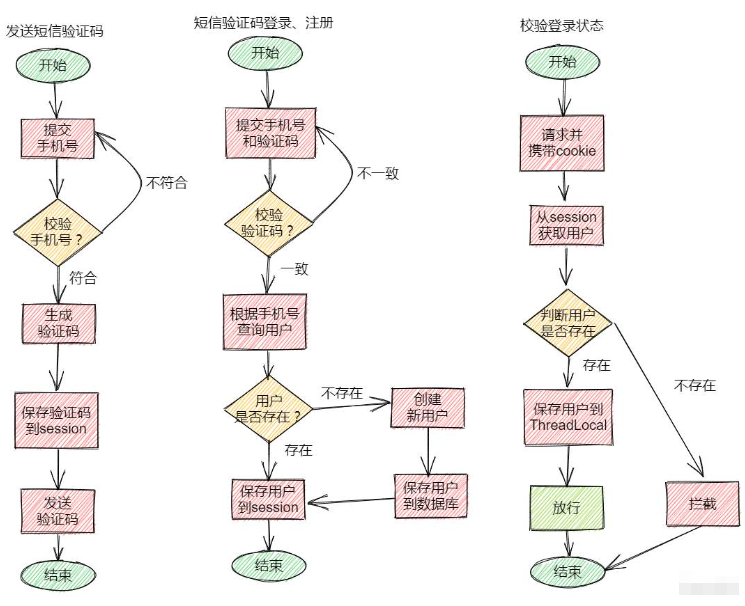
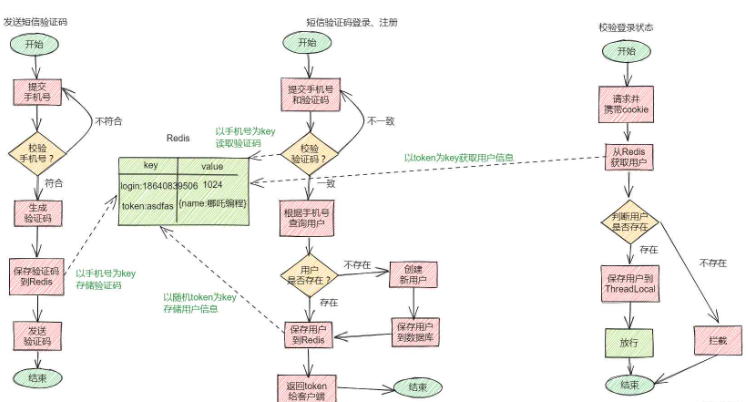
5. Implement shared session login based on RedisLogin based on session // 线程池
private static final ExecutorService SECKILL_ORDER_EXECUTOR = Executors.newSingleThreadExecutor();
/**
* 在类初始化完成后执行
*/
@PostConstruct
private void init() {
SECKILL_ORDER_EXECUTOR.submit(new VoucherOrderHandler());
}
// 阻塞队列
private BlockingQueue<VoucherOrder> orderTasks = new ArrayBlockingQueue<>(1024 * 1024);
private class OrderHandler implements Runnable{
@Override
public void run() {
while (true){
try {
doSomething();
} catch (Exception e) {
log.error("处理订单异常", e);
}
}
}
}
public class RefreshTokenInterceptor implements HandlerInterceptor {
private StringRedisTemplate stringRedisTemplate;
public RefreshTokenInterceptor(StringRedisTemplate stringRedisTemplate) {
this.stringRedisTemplate = stringRedisTemplate;
}
@Override
public boolean preHandle(HttpServletRequest request, HttpServletResponse response, Object handler) throws Exception {
// 1、获取请求头中的token
String token = request.getHeader("authorization");
if (StrUtil.isBlank(token)) {
return true;
}
// 2、基于TOKEN获取redis中的用户
String key = LOGIN_USER_KEY + token;
Map<Object, Object> userMap = stringRedisTemplate.opsForHash().entries(key);
// 3、判断用户是否存在
if (userMap.isEmpty()) {
return true;
}
// 5、将查询到的hash数据转为UserDTO
UserDTO userDTO = BeanUtil.fillBeanWithMap(userMap, new UserDTO(), false);
// 6、存在,保存用户信息到 ThreadLocal
UserHolder.saveUser(userDTO);
// 7、刷新token有效期
stringRedisTemplate.expire(key, LOGIN_USER_TTL, TimeUnit.MINUTES);
// 8、放行
return true;
}
@Override
public void afterCompletion(HttpServletRequest request, HttpServletResponse response, Object handler, Exception ex) throws Exception {
// 移除用户
UserHolder.removeUser();
}
}
The above is the detailed content of How to implement Redis distributed cache and flash sales. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1385
1385
 52
52
 How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
How to build the redis cluster mode
Apr 10, 2025 pm 10:15 PM
Redis cluster mode deploys Redis instances to multiple servers through sharding, improving scalability and availability. The construction steps are as follows: Create odd Redis instances with different ports; Create 3 sentinel instances, monitor Redis instances and failover; configure sentinel configuration files, add monitoring Redis instance information and failover settings; configure Redis instance configuration files, enable cluster mode and specify the cluster information file path; create nodes.conf file, containing information of each Redis instance; start the cluster, execute the create command to create a cluster and specify the number of replicas; log in to the cluster to execute the CLUSTER INFO command to verify the cluster status; make
 How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear redis data
Apr 10, 2025 pm 10:06 PM
How to clear Redis data: Use the FLUSHALL command to clear all key values. Use the FLUSHDB command to clear the key value of the currently selected database. Use SELECT to switch databases, and then use FLUSHDB to clear multiple databases. Use the DEL command to delete a specific key. Use the redis-cli tool to clear the data.
 How to use the redis command
Apr 10, 2025 pm 08:45 PM
How to use the redis command
Apr 10, 2025 pm 08:45 PM
Using the Redis directive requires the following steps: Open the Redis client. Enter the command (verb key value). Provides the required parameters (varies from instruction to instruction). Press Enter to execute the command. Redis returns a response indicating the result of the operation (usually OK or -ERR).
 How to use redis lock
Apr 10, 2025 pm 08:39 PM
How to use redis lock
Apr 10, 2025 pm 08:39 PM
Using Redis to lock operations requires obtaining the lock through the SETNX command, and then using the EXPIRE command to set the expiration time. The specific steps are: (1) Use the SETNX command to try to set a key-value pair; (2) Use the EXPIRE command to set the expiration time for the lock; (3) Use the DEL command to delete the lock when the lock is no longer needed.
 How to read redis queue
Apr 10, 2025 pm 10:12 PM
How to read redis queue
Apr 10, 2025 pm 10:12 PM
To read a queue from Redis, you need to get the queue name, read the elements using the LPOP command, and process the empty queue. The specific steps are as follows: Get the queue name: name it with the prefix of "queue:" such as "queue:my-queue". Use the LPOP command: Eject the element from the head of the queue and return its value, such as LPOP queue:my-queue. Processing empty queues: If the queue is empty, LPOP returns nil, and you can check whether the queue exists before reading the element.
 How to implement the underlying redis
Apr 10, 2025 pm 07:21 PM
How to implement the underlying redis
Apr 10, 2025 pm 07:21 PM
Redis uses hash tables to store data and supports data structures such as strings, lists, hash tables, collections and ordered collections. Redis persists data through snapshots (RDB) and append write-only (AOF) mechanisms. Redis uses master-slave replication to improve data availability. Redis uses a single-threaded event loop to handle connections and commands to ensure data atomicity and consistency. Redis sets the expiration time for the key and uses the lazy delete mechanism to delete the expiration key.
 How to read the source code of redis
Apr 10, 2025 pm 08:27 PM
How to read the source code of redis
Apr 10, 2025 pm 08:27 PM
The best way to understand Redis source code is to go step by step: get familiar with the basics of Redis. Select a specific module or function as the starting point. Start with the entry point of the module or function and view the code line by line. View the code through the function call chain. Be familiar with the underlying data structures used by Redis. Identify the algorithm used by Redis.
 How to make message middleware for redis
Apr 10, 2025 pm 07:51 PM
How to make message middleware for redis
Apr 10, 2025 pm 07:51 PM
Redis, as a message middleware, supports production-consumption models, can persist messages and ensure reliable delivery. Using Redis as the message middleware enables low latency, reliable and scalable messaging.




