 PHP Framework
PHP Framework
 YII
YII
 Identity authentication and authorization in Yii framework: ensuring application security
Identity authentication and authorization in Yii framework: ensuring application security
Identity authentication and authorization in Yii framework: ensuring application security
In the field of web application development, identity authentication and authorization are two essential links to ensure application security, and the Yii framework provides a complete identity authentication and authorization mechanism to help developers easily implement these functions and ensure Application security.
1. Identity Authentication
1.1 Basic Authentication
The basic authentication mechanism in the Yii framework is implemented using HTTP Basic authentication. When a user accesses a page that requires authentication in the browser, the server will send a 401 Unauthorized response, requiring the user to provide a username and password. After the user provides the correct username and password, the server will return a Cookie containing an encryption token, and the user's subsequent requests will carry the token in the Cookie for verification. The Yii framework provides the base class yiiwebUser to manage user accounts, and you can implement basic authentication by overriding its identityClass attribute.
1.2 Form-based authentication
In form-based authentication, the user enters their username and password through a web form and then sends a request to the server. The Yii framework can implement form-based identity authentication through a highly customized identity authentication mechanism. You need to override the login method in the yiiwebUser class and implement form-based authentication logic in this method.
1.3 OAuth authentication
OAuth is a popular identity authentication standard. In OAuth authentication, users can log in to the application using an existing authentication mechanism (such as Google, Facebook, etc.). The Yii framework easily implements OAuth authentication with the support of the yii uthclientClient base class.
2. Authorization
2.1 Role-based access control
The Yii framework uses role-based access control to implement the authorization mechanism. In this mechanism, we assign different users to different roles and then assign different access rights to these roles. The Yii framework provides a database-based role access control implementation called yiibacDbManager. By accessing the access control database table, the Yii framework easily implements role-based access control.
2.2 Rule-based access control
The Yii framework also supports rule-based access control. By defining a verification function for each rule, it determines whether the rule is satisfied when requesting authorization. If the rule is satisfied, the authorization is successful; otherwise, the authorization is denied. This access control method is generally used in relatively simple business processes.
2.3 ACL Access Control
Access Control List (ACL) is a more flexible authorization mechanism that allows users to achieve fine-grained implementation based on different conditions (such as time, user attributes, etc.) access control. ACL access control is implemented in the Yii framework by implementing the yii iltersAccessControl class.
Conclusion
In modern web development environments, authentication and authorization are key steps to ensure application security. The Yii framework provides a flexible and easily customizable identity authentication and authorization mechanism to help web developers easily implement these key functions and ensure the security of web applications.
The above is the detailed content of Identity authentication and authorization in Yii framework: ensuring application security. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1371
1371
 52
52
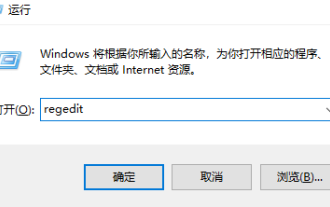 How to upgrade win10 enterprise version 2016 long-term service version to professional version
Jan 03, 2024 pm 11:26 PM
How to upgrade win10 enterprise version 2016 long-term service version to professional version
Jan 03, 2024 pm 11:26 PM
When we no longer want to continue using the current Win10 Enterprise Edition 2016 Long-Term Service Edition, we can choose to switch to the Professional Edition. The method is also very simple. We only need to change some contents and install the system image. How to change win10 enterprise version 2016 long-term service version to professional version 1. Press win+R, and then enter "regedit" 2. Paste the following path directly in the address bar above: Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\WindowsNT\CurrentVersion3 , then find the EditionID and replace the content with "professional" to confirm
 How to use Flask-Security to implement user authentication and authorization
Aug 04, 2023 pm 02:40 PM
How to use Flask-Security to implement user authentication and authorization
Aug 04, 2023 pm 02:40 PM
How to use Flask-Security to implement user authentication and authorization Introduction: In modern web applications, user authentication and authorization are essential functions. To simplify this process, Flask-Security is a very useful extension that provides a series of tools and functions to make user authentication and authorization simple and convenient. This article will introduce how to use Flask-Security to implement user authentication and authorization. 1. Install the Flask-Security extension: at the beginning
 How to use Yii framework in PHP
Jun 27, 2023 pm 07:00 PM
How to use Yii framework in PHP
Jun 27, 2023 pm 07:00 PM
With the rapid development of web applications, modern web development has become an important skill. Many frameworks and tools are available for developing efficient web applications, among which the Yii framework is a very popular framework. Yii is a high-performance, component-based PHP framework that uses the latest design patterns and technologies, provides powerful tools and components, and is ideal for building complex web applications. In this article, we will discuss how to use Yii framework to build web applications. Install Yii framework first,
 How to get authorization for Douyin slices and goods? Is Douyin slicing easy to make?
Mar 07, 2024 pm 10:52 PM
How to get authorization for Douyin slices and goods? Is Douyin slicing easy to make?
Mar 07, 2024 pm 10:52 PM
Douyin, as a popular social media platform at the moment, not only provides people with a wealth of entertainment content, but has also become an important channel for many brands and merchants to promote products and achieve sales. Among them, Douyin’s slicing and selling products has become a novel and efficient marketing method. So, how do you get authorization for Douyin's sliced products? 1. How do you get authorization for Douyin's sliced products? Douyin's sliced products decompose long videos into short video clips and embed product promotion information in them to attract viewers to buy. . When slicing and selling goods on Douyin, the first step is to obtain authorization from the original video. When looking for a suitable licensor, you can consider using various channels such as Douyin platform, social media and industry forums. Find creators or copyright holders with popular video content and actively connect with them,
 UniApp implements detailed analysis of user login and authorization
Jul 05, 2023 pm 11:54 PM
UniApp implements detailed analysis of user login and authorization
Jul 05, 2023 pm 11:54 PM
UniApp implements detailed analysis of user login and authorization. In modern mobile application development, user login and authorization are essential functions. As a cross-platform development framework, UniApp provides a convenient way to implement user login and authorization. This article will explore the details of user login and authorization in UniApp, and attach corresponding code examples. 1. Implementation of user login function Create login page User login function usually requires a login page, which contains a form for users to enter their account number and password and a login button
 How to implement authentication and authorization in PHP applications using JWT
Aug 03, 2023 pm 10:17 PM
How to implement authentication and authorization in PHP applications using JWT
Aug 03, 2023 pm 10:17 PM
How to use JWT to implement authentication and authorization in PHP applications Introduction: With the rapid development of the Internet, authentication and authorization are becoming increasingly important in web applications. JSONWebToken (JWT) is a popular authentication and authorization mechanism that is widely used in PHP applications. This article will introduce how to use JWT to implement authentication and authorization in PHP applications, and provide code examples to help readers better understand the use of JWT. 1. Introduction to JWT JSONWebTo
 Steps to implement web page caching and page chunking using Yii framework
Jul 30, 2023 am 09:22 AM
Steps to implement web page caching and page chunking using Yii framework
Jul 30, 2023 am 09:22 AM
Steps to implement web page caching and page chunking using the Yii framework Introduction: During the web development process, in order to improve the performance and user experience of the website, it is often necessary to cache and chunk the page. The Yii framework provides powerful caching and layout functions, which can help developers quickly implement web page caching and page chunking. This article will introduce how to use the Yii framework to implement web page caching and page chunking. 1. Turn on web page caching. In the Yii framework, web page caching can be turned on through the configuration file. Open the main configuration file co
 What to do if wps authorization has expired and text cannot be entered?
Mar 20, 2024 am 09:00 AM
What to do if wps authorization has expired and text cannot be entered?
Mar 20, 2024 am 09:00 AM
There are many genuine softwares in order to protect their own intellectual property rights. Before using the software, users must obtain some authorizations and obtain permission from the developer before they can use it. Some software has a trial period. After this period, you need to obtain re-authorization before you can use it normally. If wps prompts that the authorization has expired, we cannot perform any operations. How to solve this problem, let’s take a look at the explanation below. 1. I opened the WPS text program and clicked on the red box in the picture above, as shown in the picture below. 2. Click Configuration and Repair Tools. 3. Select "Advanced", as shown in the figure below. 4. Click the product management center and delete the "Expired" prompt content, as shown in the figure below. 5. After clicking "Add", enter the serial number, as shown in the figure below. 6. Then first



