 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Website Security Strategy: Protecting against Brute Force Attacks in PHP
Website Security Strategy: Protecting against Brute Force Attacks in PHP
Website Security Strategy: Protecting against Brute Force Attacks in PHP
With the development of the Internet, website security has become a very important topic. As a common server-side programming language, the security of PHP has also attracted much attention. In PHP, protecting against brute force attacks is an essential security strategy. This article will introduce some methods and techniques to protect against brute force attacks in PHP.
Brute force attack refers to hackers using blasting methods to try to log in to websites or other systems using various possible usernames and passwords. This is a common security threat, so steps must be taken to prevent brute force attacks. As a language for developing websites, PHP provides some built-in functions and technologies to deal with this threat.
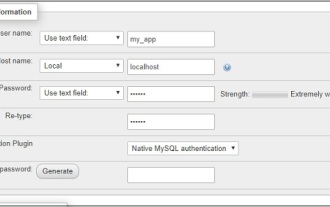
First, a good strategy to protect against brute force attacks is to use strong passwords. A strong password is one that contains a string of letters, numbers, and special characters. This type of password is harder to guess or crack, thereby improving the security of the website. In PHP, passwords can be encrypted and verified using the built-in password hashing function. For example, you can use the password_hash function to hash a password, and then use the password_verify function to verify that the password entered by the user matches the hash value. In this way, even if a hacker obtains the hash value stored in the database, he cannot directly know the original password.
Secondly, brute force attacks can be prevented by implementing a login failure lockout policy. The login failure lockout policy refers to temporarily locking the user account after the user enters incorrect username or password multiple times in a row. This way, hackers cannot use blasting methods to attack. In PHP, you can use the Session function to implement a login failure lockout policy. When a user fails to log in, the number of failures can be recorded in the Session. Once the number of failures exceeds the set limit, the user account can be locked for a period of time.
In addition, verification codes can also be used to prevent brute force attacks. Verification code is a graphical or numerical verification mechanism that requires users to enter the correct verification code when logging in or registering. This way, hackers cannot use automated programs to conduct blasting attacks. In PHP, you can use the GD library or ImageMagick to generate verification code images and store the verification code information in the Session. After the user enters the verification code, the verification code stored in the Session can be compared with the user input for verification.
Finally, be sure to regularly update and fix PHP security patches. The PHP language and related frameworks and libraries also have some security vulnerabilities. Hackers can exploit these vulnerabilities to conduct brute force attacks. Therefore, it is very important to update and fix PHP security patches in a timely manner. You can learn about the latest security patches by regularly visiting the PHP official website or related security blogs and apply them to the website.
To summarize, strategies to protect against brute force attacks in PHP include using strong passwords, implementing a login failure lockout policy, using verification codes, and regularly updating and repairing PHP security patches. By taking these security measures, you can effectively improve the security of the website and protect user information from the threat of brute force attacks. When building and maintaining a website, we should keep the importance of website security in mind and always pay attention to the latest security technologies and strategies to protect the security of the website and users.
The above is the detailed content of Website Security Strategy: Protecting against Brute Force Attacks in PHP. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1371
1371
 52
52
 CakePHP Project Configuration
Sep 10, 2024 pm 05:25 PM
CakePHP Project Configuration
Sep 10, 2024 pm 05:25 PM
In this chapter, we will understand the Environment Variables, General Configuration, Database Configuration and Email Configuration in CakePHP.
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
To work with date and time in cakephp4, we are going to make use of the available FrozenTime class.
 CakePHP Working with Database
Sep 10, 2024 pm 05:25 PM
CakePHP Working with Database
Sep 10, 2024 pm 05:25 PM
Working with database in CakePHP is very easy. We will understand the CRUD (Create, Read, Update, Delete) operations in this chapter.
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP Routing
Sep 10, 2024 pm 05:25 PM
CakePHP Routing
Sep 10, 2024 pm 05:25 PM
In this chapter, we are going to learn the following topics related to routing ?
 CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
Validator can be created by adding the following two lines in the controller.



