 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 How to use PHP to strengthen CAPTCHA and anti-bot technology security
How to use PHP to strengthen CAPTCHA and anti-bot technology security
How to use PHP to strengthen CAPTCHA and anti-bot technology security
How to use PHP to strengthen the security of verification code and anti-bot technology
In today's Internet era, verification code and anti-bot technology are widely used in various websites and applications to ensure the security of users and data confidentiality. As a widely used server-side scripting language, PHP has powerful and flexible functions that can effectively implement verification codes and anti-bot technology.
1. Use the GD library to generate verification code images
The GD library is an extension library of PHP that can be used to generate verification code images. By using the GD library, we can easily generate pictures with random characters and display them to the user. At the same time, you can also add interference lines, noise and other effects to the verification code image to improve the security of the verification code.
The steps to use the GD library to generate a verification code are as follows:
- Create a blank image and set the background color.
- Generate random characters and set the font, font size, and color.
- Randomly generate interference lines and noise on the picture.
- Output the verification code image and save it to a temporary folder.
2. Verify the verification code through the session mechanism
After the verification code image is generated, the verification code entered by the user needs to be verified with it. PHP provides a session mechanism (Session) that can easily save and obtain verification codes.
The steps to use the session mechanism to verify the verification code are as follows:
- When generating the verification code image, save the verification code to the session.
- When the user submits the form, the verification code is obtained from the session and compared with the verification code entered by the user.
- If the verification code matches successfully, it means that the user input is correct and you can continue to the next step. If they don't match, the user needs to be prompted to re-enter.
3. Use IP address and timestamp to limit access frequency
In order to prevent robots from violently cracking the verification code, you can use IP address and timestamp to limit access frequency. If the number of consecutive requests for verification codes in a short period of time exceeds the set threshold, it can be considered a robot behavior and corresponding processing can be carried out, such as prohibiting access to the IP address.
The steps to limit access frequency using IP address and timestamp are as follows:
- Get the user's IP address and access time.
- Save the IP address and access time to the database or cache.
- Whenever a verification code is requested, first check the number of visits and time interval of the IP address.
- If the set threshold is exceeded, corresponding processing will be carried out, such as prohibiting access to the IP address.
4. Use human-machine verification technology
In addition to the traditional verification code, in some special scenarios, more advanced human-machine verification technology can be used, such as face recognition, image Classification, etc., to determine whether the user is a real human being.
The steps for using human-machine verification technology are as follows:
- Call the image processing library to realize face recognition or image classification functions.
- Process the pictures or videos provided by the user through the API and return the recognition results.
- Based on the recognition results, determine whether the user is a real human being. If so, verification passes; if not, further verification is required or access is denied.
Summary:
Through the above steps, we can use PHP to strengthen the security of verification codes and anti-bot technology. However, we should also be aware that security technology is constantly developing and evolving, and new attack methods and solutions are constantly emerging. Therefore, we need to pay attention to the latest security technology in a timely manner and continuously upgrade and improve the security of our websites and applications to protect user privacy and data confidentiality.
The above is the detailed content of How to use PHP to strengthen CAPTCHA and anti-bot technology security. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
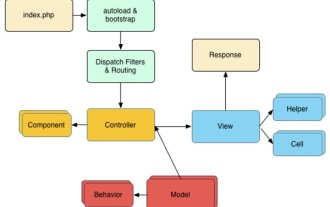 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total



