 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to deal with the intrusion and spread of malware and viruses in Linux systems
How to deal with the intrusion and spread of malware and viruses in Linux systems
How to deal with the intrusion and spread of malware and viruses in Linux systems
How to deal with the intrusion and spread of malware and viruses in Linux systems
With the rapid development of information technology, malware and viruses have become important factors posing threats. Traditionally, Windows systems have been the main target of malware and viruses, while Linux systems are considered relatively safe. However, as Linux systems are widely used in servers and embedded devices, it has also become a target for attackers. Therefore, it is crucial to protect your Linux system from the intrusion and spread of malware and viruses.
In response to the problems of malware and virus intrusion and spread in Linux systems, the following are some countermeasures:
- Update the system and software in a timely manner: Regularly updating the operating system and software is the key to maintaining the system Important steps for safety. Updating with patches that fix vulnerabilities and security vulnerabilities can prevent attackers from exploiting system weaknesses. Make sure to enable automatic updates and install available updates promptly.
- Install trusted antivirus software: Although Linux systems are relatively secure, they can still be attacked by malware and viruses. Installing trusted antivirus software can help detect and remove potential malware and viruses. Ensure that virus databases are updated in a timely manner and regular full scans are performed.
- Use strong passwords and strict access permissions: Setting strong passwords and changing them regularly can effectively prevent unauthorized access. In addition, strict access permissions will limit access to systems and sensitive files, reducing the risk of the spread of malware and viruses.
- Install a firewall and intrusion detection system: Configure a firewall to filter malicious network traffic and unnecessary connections. Intrusion detection systems (IDS) can monitor abnormal activities in the system and promptly detect and prevent the intrusion of malware and viruses.
- Obtain and install software only from trusted sources: Only download and install software from trusted software sources to ensure the security and integrity of the software. Avoid getting software from unofficial or untrusted sources to prevent the spread of malware and viruses.
- Regularly back up critical data: Regularly backing up your system and important data is an important measure to reduce the damage caused by malware and virus intrusions. After malware intrusion, system and data can be restored by restoring backups.
- Increase employee training and awareness: It is important to increase employee awareness of malware and virus threats and train them on how to avoid clicking spam links or downloading suspicious files. Employees should be told to only download and open files from trusted sources and to pay close attention to potential security risks.
- Monitor system logs and network traffic: Regularly monitor system logs and network traffic to detect and block suspicious activities in time. By monitoring your system, potential malware and virus intrusions can be quickly identified and dealt with.
To summarize, protecting Linux systems from the intrusion and spread of malware and viruses requires a series of preventive and response measures. Keep systems and software updated, install trusted anti-virus software, use strong passwords and strict access rights, install firewalls and intrusion detection systems, only obtain and install software from trusted sources, regularly back up critical data, and enhance employee training and awareness , monitoring system logs and network traffic and other measures are essential. By taking these measures together, we can more effectively protect our Linux systems from the intrusion and spread of malware and viruses.
The above is the detailed content of How to deal with the intrusion and spread of malware and viruses in Linux systems. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
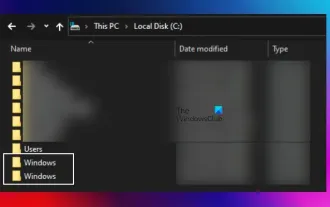 There are two Windows folders in the C drive; what should I do?
Mar 06, 2024 am 11:55 AM
There are two Windows folders in the C drive; what should I do?
Mar 06, 2024 am 11:55 AM
The Windows folder contains the Windows operating system and is an important folder in a Windows computer. By default, Windows is installed on the C drive. Therefore, C is the default directory for Windows folders. Every Windows computer has a Windows folder. However, some users reported that two Windows folders were found in the C drive. In this article, we will explain what you can do if you encounter such a situation. Two Windows folders in C drive It is rare to have two Windows folders in C drive. However, if you encounter such a situation, you can use the following suggestions: Run an anti-malware scan to try to find the correct
 How to completely remove viruses from mobile phones Recommended methods to deal with viruses in mobile phones
Feb 29, 2024 am 10:52 AM
How to completely remove viruses from mobile phones Recommended methods to deal with viruses in mobile phones
Feb 29, 2024 am 10:52 AM
After a mobile phone is infected with a certain Trojan virus, it cannot be detected and killed by anti-virus software. This principle is just like a computer infected with a stubborn virus. The virus can only be completely removed by formatting the C drive and reinstalling the system. , then I will explain how to completely clean the virus after the mobile phone is infected with a stubborn virus. Method 1: Open the phone and click "Settings" - "Other Settings" - "Restore Phone" to restore the phone to factory settings. Note: Before restoring factory settings, you must back up important data in the phone. The factory settings are equivalent to those of the computer. "It's the same as formatting and reinstalling the system". After the recovery, the data in the phone will be cleared. Method 2 (1) First turn off the phone, then press and hold the "power button" + "volume + button or volume - button" on the phone at the same time.
 What should I do if the edge browser detects a virus and cannot download it?
Jan 31, 2024 pm 06:51 PM
What should I do if the edge browser detects a virus and cannot download it?
Jan 31, 2024 pm 06:51 PM
What should I do if the edge browser detects a virus and cannot download it? The edge browser is the default browser software for our Microsoft system computers, and it is also a browser software used by many friends. When downloading a file in the edge browser, it will be scanned by the computer's default security protection. If it is determined to be a risky file, it cannot be downloaded normally. If you must download the file, follow the editor to see if it cannot be downloaded. Let’s introduce the solution to the file. What should I do if the edge browser detects a virus and cannot download? 1. Open the edge browser settings and find private search and services - scroll down to find "Security" - turn off Microsoft Defender Smartscreen; 2. Then open our
 Detailed explanation of the location of win10 virus isolation
Dec 25, 2023 pm 01:45 PM
Detailed explanation of the location of win10 virus isolation
Dec 25, 2023 pm 01:45 PM
Files isolated by Win10 viruses are generally stored in fixed locations. Many users want to open the quarantined files and restore their own files, but they don’t know where they are stored. In fact, they can usually be found in the isolation folder of the C drive security software. Where is the win10 virus quarantine file? Answer: In the C:\ProgramData\Microsoft\WindowsDefender\Quarantine folder, we can open this computer and directly copy and paste the file path to the path bar above to find it. Introduction to the virus isolation folder in win10: 1. In win10, the "Quarantine" file usually requires certain permissions to open. It is recommended to open the file as an administrator. 2,
 How to use Microsoft Defender offline scanning to powerfully remove stubborn viruses
Mar 03, 2024 am 09:10 AM
How to use Microsoft Defender offline scanning to powerfully remove stubborn viruses
Mar 03, 2024 am 09:10 AM
Microsoft Defender Antivirus provides comprehensive security protection for Windows users. It not only detects and removes viruses and malware, but also provides an important but often overlooked "offline scanning" function. This feature can effectively discover and remove stubborn malware that is difficult to deal with, providing reliable protection for users' devices. Below, we will introduce in detail how to use Microsoft Defender's offline scanning function in "Windows Security Center" to deeply detect and remove viruses and malware that may be present in your computer. Through this process, you can ensure a more secure and reliable computing environment. This feature can be run while the system is offline, ensuring system
 0x80016CFA Windows Defender Error: How to Fix It
Jul 09, 2023 pm 07:54 PM
0x80016CFA Windows Defender Error: How to Fix It
Jul 09, 2023 pm 07:54 PM
The internet is largely unsafe unless you possess some technical acumen and the ability to identify online threats. And it's often difficult to distinguish a legitimate mistake from a scam. An example here is the pop-up Microsoft Defender error 0x80016CFA. While you are browsing the web, a pop-up window will appear stating that a critical failure has been detected. It lists a mobile phone number of a so-called Microsoft certified technician who can be contacted to resolve the issue. If you're seeing this message on your browser too, keep reading! Is WindowsDefender error 0x80016CFA a scam? Yes, the Windows Defender error message in your browser is a scam
 How to protect your CentOS server from malware using antivirus software
Jul 05, 2023 pm 09:00 PM
How to protect your CentOS server from malware using antivirus software
Jul 05, 2023 pm 09:00 PM
How to Use Antivirus Software to Protect CentOS Servers from Malware In today’s digital age, server security is crucial. The intrusion of malware may lead to the leakage of personal information, system failure and even hacker attacks. To protect CentOS servers from these risks, we can use antivirus software to increase the security of the server. This article will introduce how to use antivirus software to protect CentOS servers, and attach some code examples for reference. Choosing the right antivirus software First, I
 Exploring Golang programming capabilities: Can it be used to write viruses?
Mar 19, 2024 pm 09:09 PM
Exploring Golang programming capabilities: Can it be used to write viruses?
Mar 19, 2024 pm 09:09 PM
With the rapid development of Internet technology, programming languages are also constantly emerging and evolving. Among them, Golang (Go language) has attracted much attention as an efficient and easy-to-use programming language. However, there is some controversy over whether Golang can be used to write viruses. In this article, we will explore Golang’s programming capabilities, explore whether it can be used to write viruses, and give some specific code examples. First, let us briefly introduce Golang. Golang is developed by Google





