How to prevent clickjacking (UI redirect) attacks using PHP
How to use PHP to prevent clickjacking (UI redirect) attacks
Clickjacking (Clickjacking) is an attack method in which hackers overlay harmful content on the upper layer of tempting buttons or links on a website. Enticing the user to click triggers the attack. Clickjacking can be used to steal a user's sensitive information, perform malicious actions, or tamper with a user's personal settings without their knowledge. To protect the security of our website and our users, we need to take appropriate measures to prevent clickjacking attacks.
In this article, we will introduce how to use the PHP programming language to prevent clickjacking attacks. Here are some common ways to defend against clickjacking attacks:
-
Add the X-Frame-Options header to the HTTP header information: X-Frame-Options is an HTTP response header used to Indicates whether the browser allows embedding the page into an iframe. By setting the X-Frame-Options header, we can prevent the page from being embedded in an iframe on another website, thereby preventing clickjacking attacks. PHP code example:
header("X-Frame-Options: SAMEORIGIN");Copy after login Detect whether the page is loaded in an iframe: We can use PHP to detect whether the current page is loaded in an iframe. If so, you can take appropriate action, such as reloading the page or displaying a warning message. PHP code example:
if (isset($_SERVER['HTTP_REFERER']) && strpos($_SERVER['HTTP_REFERER'], $_SERVER['SERVER_NAME']) === false) { // 页面在iframe中加载,执行相应的操作 }Copy after loginUse a transparent layer to prevent clickjacking attacks: We can use CSS or JavaScript to create a transparent layer that covers the page and prevents users from clicking on the hijacked element. This transparency layer can be achieved by adding a transparency attribute to the element or using the z-index attribute. PHP with JavaScript code example:
<?php echo "<div id='transparentLayer' style='position: absolute; top: 0; left: 0; width: 100%; height: 100%; background-color: rgba(0, 0, 0, 0); z-index: 9999;'></div>"; ?> <script> window.onload = function() { var transparentLayer = document.getElementById("transparentLayer"); transparentLayer.style.backgroundColor = "rgba(0, 0, 0, 0.5)"; transparentLayer.style.pointerEvents = "none"; } </script>Copy after loginUsing the X-Content-Type-Options header: X-Content-Type-Options is another HTTP response header that indicates whether the browser Allows MIME sniffing based on content type. By setting the X-Content-Type-Options header to nosniff, you can prevent the browser from performing MIME sniffing and thereby reduce the risk of clickjacking attacks. PHP code example:
header("X-Content-Type-Options: nosniff");Copy after loginUsing Frame Buster script: By embedding a Frame Buster script in the page, you can prevent the page from loading in an iframe. This script will detect if the page is loading in an iframe and automatically redirect to other pages if detected. PHP and JavaScript code example:
<?php echo "<script src='framebuster.js'></script>"; ?>
Copy after loginframebuster.js script content:
if (top.location !== self.location) { top.location = self.location; }Copy after login
Before implementing the above measures, please ensure that you have conducted appropriate testing and understand Applicable scenarios and potential impact of each method. In addition, updating PHP versions and frameworks in a timely manner to ensure their security is also an important step in preventing clickjacking attacks.
By taking the above methods of defending against clickjacking attacks, we can enhance the security of our website and protect our users' personal information. However, keep in mind that different attack methods may arise in different environments, so working with security experts and regularly updating your defenses is key to keeping your website secure.
The above is the detailed content of How to prevent clickjacking (UI redirect) attacks using PHP. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Working with Flash Session Data in Laravel
Mar 12, 2025 pm 05:08 PM
Working with Flash Session Data in Laravel
Mar 12, 2025 pm 05:08 PM
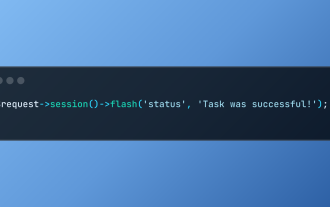
Laravel simplifies handling temporary session data using its intuitive flash methods. This is perfect for displaying brief messages, alerts, or notifications within your application. Data persists only for the subsequent request by default: $request-
 cURL in PHP: How to Use the PHP cURL Extension in REST APIs
Mar 14, 2025 am 11:42 AM
cURL in PHP: How to Use the PHP cURL Extension in REST APIs
Mar 14, 2025 am 11:42 AM
The PHP Client URL (cURL) extension is a powerful tool for developers, enabling seamless interaction with remote servers and REST APIs. By leveraging libcurl, a well-respected multi-protocol file transfer library, PHP cURL facilitates efficient execution of various network protocols, including HTTP, HTTPS, and FTP. This extension offers granular control over HTTP requests, supports multiple concurrent operations, and provides built-in security features.
 Simplified HTTP Response Mocking in Laravel Tests
Mar 12, 2025 pm 05:09 PM
Simplified HTTP Response Mocking in Laravel Tests
Mar 12, 2025 pm 05:09 PM
Laravel provides concise HTTP response simulation syntax, simplifying HTTP interaction testing. This approach significantly reduces code redundancy while making your test simulation more intuitive. The basic implementation provides a variety of response type shortcuts: use Illuminate\Support\Facades\Http; Http::fake([ 'google.com' => 'Hello World', 'github.com' => ['foo' => 'bar'], 'forge.laravel.com' =>
 12 Best PHP Chat Scripts on CodeCanyon
Mar 13, 2025 pm 12:08 PM
12 Best PHP Chat Scripts on CodeCanyon
Mar 13, 2025 pm 12:08 PM
Do you want to provide real-time, instant solutions to your customers' most pressing problems? Live chat lets you have real-time conversations with customers and resolve their problems instantly. It allows you to provide faster service to your custom
 Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Explain the concept of late static binding in PHP.
Mar 21, 2025 pm 01:33 PM
Article discusses late static binding (LSB) in PHP, introduced in PHP 5.3, allowing runtime resolution of static method calls for more flexible inheritance.Main issue: LSB vs. traditional polymorphism; LSB's practical applications and potential perfo
 PHP Logging: Best Practices for PHP Log Analysis
Mar 10, 2025 pm 02:32 PM
PHP Logging: Best Practices for PHP Log Analysis
Mar 10, 2025 pm 02:32 PM
PHP logging is essential for monitoring and debugging web applications, as well as capturing critical events, errors, and runtime behavior. It provides valuable insights into system performance, helps identify issues, and supports faster troubleshoot
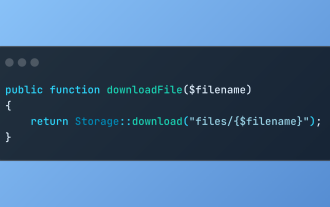 Discover File Downloads in Laravel with Storage::download
Mar 06, 2025 am 02:22 AM
Discover File Downloads in Laravel with Storage::download
Mar 06, 2025 am 02:22 AM
The Storage::download method of the Laravel framework provides a concise API for safely handling file downloads while managing abstractions of file storage. Here is an example of using Storage::download() in the example controller:
 HTTP Method Verification in Laravel
Mar 05, 2025 pm 04:14 PM
HTTP Method Verification in Laravel
Mar 05, 2025 pm 04:14 PM
Laravel simplifies HTTP verb handling in incoming requests, streamlining diverse operation management within your applications. The method() and isMethod() methods efficiently identify and validate request types. This feature is crucial for building






