 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Methods and techniques for debugging and solving Linux network security issues
Methods and techniques for debugging and solving Linux network security issues
Methods and techniques for debugging and solving Linux network security issues
How to debug and solve network security problems in Linux systems
With the rapid development of the Internet, network security has become an increasingly important topic. As one of the most popular operating systems, Linux systems have certain advantages in network security. However, even Linux systems are not completely immune to cyberattacks. Therefore, it is crucial to know how to debug and resolve network security issues in Linux systems.
This article will introduce some common network security problems and provide some suggestions and tips to debug and solve these problems.
- Network scanning
Network scanning is one of the most common intrusion methods used by hackers. By scanning the network, hackers can obtain information about the system and attempt to exploit vulnerabilities in the system. To debug and resolve network scanning issues, you can take the following measures: - Perform network scans regularly and record the scan results. This helps detect unusual activity and potential security risks.
- Install and configure a firewall to restrict unauthorized access to the network.
- Close unnecessary network services and ports to reduce the attack surface of the system.
- Weak Passwords
Weak passwords can easily be cracked by hackers and used to gain unauthorized access to the system. To address the problem of weak passwords, the following measures should be taken: - Use complex passwords. Passwords should contain uppercase and lowercase letters, numbers, and special characters, and be of sufficient length.
- Change your password regularly. Passwords should be changed at least every three months.
- It is forbidden to use commonly used passwords and passwords that are easy to guess.
- Malware and Viruses
Malware and viruses can damage your system and cause data loss or leakage. To resolve malware and virus issues, you can take the following steps: - Install and update antivirus software. Scan the system regularly to detect and remove potential threats.
- Only download and install software from trusted sources.
- Avoid opening email attachments from unknown sources as they may contain malware.
- Denial of Service Attack
Denial of service attacks are designed to prevent a system from functioning properly by overloading system resources. To solve the problem of denial of service attacks, you can take the following measures: - Configure a firewall to restrict access to system resources.
- Monitor system performance and identify abnormal traffic patterns. If abnormal traffic is discovered, timely measures should be taken to deal with the attack.
- Use traffic analysis tools to detect and block malicious traffic.
- Social Engineering
Social engineering is an attack method that obtains sensitive information by deceiving and manipulating human behavior. To address social engineering issues, you can take the following steps: - Conduct security training for employees to improve their ability to recognize and prevent social engineering.
- Implement strong authentication mechanisms to ensure that only authorized personnel have access to the system.
- Regularly review and update system security policies.
When debugging and troubleshooting network security issues in Linux systems, you need to pay close attention to system logs and utilize tools to identify potential risks and vulnerabilities. In addition, system updates and patch installations are performed regularly to ensure system security.
In short, network security issues are an eternal challenge for Linux systems. Only by remaining vigilant and taking appropriate security measures can we effectively debug and solve network security problems and protect systems and data from attacks.
The above is the detailed content of Methods and techniques for debugging and solving Linux network security issues. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
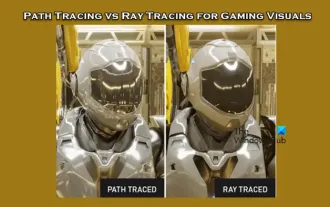 Path tracing and ray tracing for game visual effects
Feb 19, 2024 am 11:36 AM
Path tracing and ray tracing for game visual effects
Feb 19, 2024 am 11:36 AM
The decision to use path tracing or ray tracing is a critical choice for game developers. Although they both perform well visually, there are some differences in practical applications. Therefore, game enthusiasts need to carefully weigh the advantages and disadvantages of both to determine which technology is more suitable for achieving the visual effects they want. What is ray tracing? Ray tracing is a complex rendering technique used to simulate the propagation and interaction of light in virtual environments. Unlike traditional rasterization methods, ray tracing generates realistic lighting and shadow effects by tracing the path of light, providing a more realistic visual experience. This technology not only produces more realistic images, but also simulates more complex lighting effects, making scenes look more realistic and vivid. its main concepts
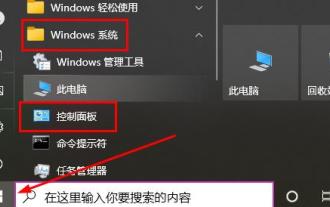 How to uninstall Win10 patches
Dec 25, 2023 pm 08:49 PM
How to uninstall Win10 patches
Dec 25, 2023 pm 08:49 PM
After the system is patched, these patches will remain in the computer and will occupy a lot of memory over time. Therefore, many users want to know how to uninstall win10 patches. It is actually very simple. Let’s take a look. How to uninstall the win10 patch: 1. First click on the lower left corner to start, then find "Windows System" and open the "Control Panel". 2. Then click "Uninstall a program" below. 3. Then click "View installed updates" on the left. 4. Now you can see all the patches, right-click and click "Uninstall".
 Error 87 prevents kb4474419 patch from being installed
Jan 03, 2024 pm 03:28 PM
Error 87 prevents kb4474419 patch from being installed
Jan 03, 2024 pm 03:28 PM
If there is a problem with the kb4474419 patch, automatic updates cannot be performed. Generally speaking, it is solved by re-downloading the patch and installing it. However, many friends reported that they encountered installation errors. In fact, the solution is very simple. Let’s take a look. kb4474419 patch installation error 87: 1. First, click on the portal to download the latest kb4474419 patch. 2. Unzip the downloaded compressed package resources. 3. You can use the shortcut key "win+R" to open the command prompt, and then enter "cmd". You can also enter "command prompt" in the system search and run it as an administrator. 4. First enter C:\Windows\System32 and enter
 How to use logging to track program execution in C#
Oct 09, 2023 pm 03:51 PM
How to use logging to track program execution in C#
Oct 09, 2023 pm 03:51 PM
How to use logging to track program operation in C# requires specific code examples. Introduction: When developing software, it is often necessary to track and record the operation of the program so that the problem can be accurately found when a problem occurs. Logging is an important technical means that can record the running status, error information and debugging information of the program to facilitate abnormal location and troubleshooting. This article will introduce how to use logging to track the operation of the program in C#, and provide specific code examples. 1. Selection of logging libraries In C#, there are many excellent ones
 What to do if Win7 update patch prompts error code 0x80070643
Jun 29, 2023 pm 12:58 PM
What to do if Win7 update patch prompts error code 0x80070643
Jun 29, 2023 pm 12:58 PM
What should I do if the Win7 update patch prompts error code 0x80070643? Win7 system upgrade is a way of daily maintenance of Windows. We often install the latest update patches on computers to strengthen the system. However, recently some Win7 users have encountered the error code 0x80070643 when updating patches. So how to solve it? Woolen cloth? Many friends don’t know how to operate in detail. The editor has compiled the solutions to the Win7 update patch prompt error code 0x80070643. If you are interested, follow the editor to take a look below! Solution to the Win7 update patch error code 0x80070643 1. Open the Start menu on the desktop.
 Win11 KB5035942 update patch released: multiple new shortcut methods added
Mar 28, 2024 am 11:20 AM
Win11 KB5035942 update patch released: multiple new shortcut methods added
Mar 28, 2024 am 11:20 AM
new features! This update introduces voice shortcuts or custom commands. You can use them to create your own commands in supported English dialects. To get started, say What Can I Say and click the Speech Shortcuts tab on the left panel. You can also use the Show Voice Shortcuts command to open the Voice Shortcuts page. Click Create new shortcut. Create commands using voice or other input. Give it a name and select one or more actions. After filling in the necessary information, click Create. The command is now available. To see all voice shortcuts you've created, go to the command help page or use a voice command to show voice shortcuts. Narrator new features! You can now listen to previews of ten natural voices before downloading. See September 2023 for list
 Implementation method of order status tracking function of food shopping system developed in PHP
Nov 02, 2023 pm 02:28 PM
Implementation method of order status tracking function of food shopping system developed in PHP
Nov 02, 2023 pm 02:28 PM
Implementation method of order status tracking function of vegetable shopping system developed in PHP With the rapid development of e-commerce, more and more people begin to purchase daily necessities online, including daily ingredients and vegetables. In order to facilitate users to purchase vegetables, many vegetable shopping systems have begun to emerge, providing users with online purchase, payment and delivery services. In the grocery shopping system, the order status tracking function is particularly important, allowing users to understand the status of their orders in real time, thereby improving the user's shopping experience. This article will introduce the implementation of the order status tracking function of the grocery shopping system developed in PHP.
 WIN7 system patch cleaning operation method
Mar 26, 2024 pm 08:10 PM
WIN7 system patch cleaning operation method
Mar 26, 2024 pm 08:10 PM
1. Double-click the mouse to open [Computer]. 2. In the interface, right-click [Properties]. 3. In the window, click [Disk Cleanup] and you will see that disk cleanup is in progress. 4. Check the files to be deleted and click [OK]. 5. Then in the prompt box, select [Delete Files], and you will see that the disk cleanup is in progress.



