Development practice of PHP MySQL user permission control
PHP Development Practice: Using PHP and MySQL to Implement User Permission Control
With the development of the Internet, more and more websites and applications need to implement user permission control functions to ensure that users can only access them Authorized resources. As a widely used server-side programming language, PHP provides a wealth of tools and functions to implement user permission control. Combined with the MySQL database, we can quickly build a flexible and secure permission control system.
In this article, we will introduce how to use PHP and MySQL to implement user permission control. We will proceed as follows:
- Create database and table
- Registration and login function
- User permission control
- Permission management page
- Authentication process
The first step is to create the database and tables. We need to create a database to store user information and permission information. Using MySQL or another database management tool, create a database and name it "user_perm", and then create two tables in the database: "users" and "permissions".
The users table will store users’ basic information, such as username, password, email, etc. It will also contain a field called "role" that identifies the user's role.
The permissions table will store different permission types and their related information. Each permission will be associated with a role. The permissions listed in the table determine the resources a user can access.
The second step is the registration and login functions. We can use PHP to implement user registration and login functions. When a user registers, we verify the information provided by the user and save it to the users table in the database. When a user logs in, we verify their username and password and generate a Session to keep the user logged in throughout the session.
It is worth noting here that for password storage, we should use an encryption algorithm (such as bcrypt) to encrypt the user's password and store it in the database. In this way, even if the database is illegally accessed, the user password will not be leaked.
The third step is user permission control. In the users table, we added a field called "role" that identifies the user's role. We can assign different roles to users, such as "Administrator", "Editor", "General User", etc. Each role will be assigned a set of permissions.
We can use session variables in PHP to store the current user's role information. When a user logs in, we can save their role information in a session variable and use that role to determine whether the user has the right to access a resource.
The fourth step is the rights management page. In order to facilitate the management of permissions, we can create a permission management page. Administrators can use this page to add, modify, or remove permissions. When the administrator makes any changes, we need to update the permissions table in the database, and the next time the user logs in, update their session variables.
The fifth step is the authentication process. When a user attempts to access a protected resource, we need to perform authentication verification. This can be done at the top of each protected page or script. We can check the role of the current user and determine whether access to the resource is allowed based on its role.
For example, if only administrator roles can access a page, we can use the following code for authentication verification:
session_start();
if($_SESSION['role'] != 'admin'){
// 未授权访问
echo "Access denied!";
exit;
}In this way, when ordinary users try to access the page, they will be It prompts "Access denied!" and access is denied.
To sum up, using PHP and MySQL to implement user permission control can provide flexible and secure access control functions. We can create databases and tables to store user and permission information, implement registration and login functions, and manage user roles and permissions. Through the verification and authentication process, we can ensure that users can only access the resources for which they are authorized.
This practice of user permission control is critical to the security of websites and applications. It not only prevents unauthorized access and potential information leakage, but also helps us implement more fine-grained access control on the system to meet the needs of different users. Therefore, it is very important for PHP developers to learn and master this practical technology.
The above is the detailed content of Development practice of PHP MySQL user permission control. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1371
1371
 52
52
 Unable to log in to mysql as root
Apr 08, 2025 pm 04:54 PM
Unable to log in to mysql as root
Apr 08, 2025 pm 04:54 PM
The main reasons why you cannot log in to MySQL as root are permission problems, configuration file errors, password inconsistent, socket file problems, or firewall interception. The solution includes: check whether the bind-address parameter in the configuration file is configured correctly. Check whether the root user permissions have been modified or deleted and reset. Verify that the password is accurate, including case and special characters. Check socket file permission settings and paths. Check that the firewall blocks connections to the MySQL server.
 mysql whether to change table lock table
Apr 08, 2025 pm 05:06 PM
mysql whether to change table lock table
Apr 08, 2025 pm 05:06 PM
When MySQL modifys table structure, metadata locks are usually used, which may cause the table to be locked. To reduce the impact of locks, the following measures can be taken: 1. Keep tables available with online DDL; 2. Perform complex modifications in batches; 3. Operate during small or off-peak periods; 4. Use PT-OSC tools to achieve finer control.
 The relationship between mysql user and database
Apr 08, 2025 pm 07:15 PM
The relationship between mysql user and database
Apr 08, 2025 pm 07:15 PM
In MySQL database, the relationship between the user and the database is defined by permissions and tables. The user has a username and password to access the database. Permissions are granted through the GRANT command, while the table is created by the CREATE TABLE command. To establish a relationship between a user and a database, you need to create a database, create a user, and then grant permissions.
 Query optimization in MySQL is essential for improving database performance, especially when dealing with large data sets
Apr 08, 2025 pm 07:12 PM
Query optimization in MySQL is essential for improving database performance, especially when dealing with large data sets
Apr 08, 2025 pm 07:12 PM
1. Use the correct index to speed up data retrieval by reducing the amount of data scanned select*frommployeeswherelast_name='smith'; if you look up a column of a table multiple times, create an index for that column. If you or your app needs data from multiple columns according to the criteria, create a composite index 2. Avoid select * only those required columns, if you select all unwanted columns, this will only consume more server memory and cause the server to slow down at high load or frequency times For example, your table contains columns such as created_at and updated_at and timestamps, and then avoid selecting * because they do not require inefficient query se
 Can mysql run on android
Apr 08, 2025 pm 05:03 PM
Can mysql run on android
Apr 08, 2025 pm 05:03 PM
MySQL cannot run directly on Android, but it can be implemented indirectly by using the following methods: using the lightweight database SQLite, which is built on the Android system, does not require a separate server, and has a small resource usage, which is very suitable for mobile device applications. Remotely connect to the MySQL server and connect to the MySQL database on the remote server through the network for data reading and writing, but there are disadvantages such as strong network dependencies, security issues and server costs.
 How to optimize MySQL performance for high-load applications?
Apr 08, 2025 pm 06:03 PM
How to optimize MySQL performance for high-load applications?
Apr 08, 2025 pm 06:03 PM
MySQL database performance optimization guide In resource-intensive applications, MySQL database plays a crucial role and is responsible for managing massive transactions. However, as the scale of application expands, database performance bottlenecks often become a constraint. This article will explore a series of effective MySQL performance optimization strategies to ensure that your application remains efficient and responsive under high loads. We will combine actual cases to explain in-depth key technologies such as indexing, query optimization, database design and caching. 1. Database architecture design and optimized database architecture is the cornerstone of MySQL performance optimization. Here are some core principles: Selecting the right data type and selecting the smallest data type that meets the needs can not only save storage space, but also improve data processing speed.
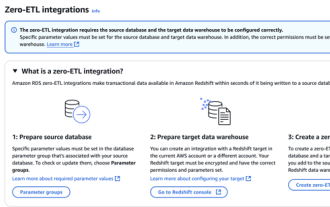 RDS MySQL integration with Redshift zero ETL
Apr 08, 2025 pm 07:06 PM
RDS MySQL integration with Redshift zero ETL
Apr 08, 2025 pm 07:06 PM
Data Integration Simplification: AmazonRDSMySQL and Redshift's zero ETL integration Efficient data integration is at the heart of a data-driven organization. Traditional ETL (extract, convert, load) processes are complex and time-consuming, especially when integrating databases (such as AmazonRDSMySQL) with data warehouses (such as Redshift). However, AWS provides zero ETL integration solutions that have completely changed this situation, providing a simplified, near-real-time solution for data migration from RDSMySQL to Redshift. This article will dive into RDSMySQL zero ETL integration with Redshift, explaining how it works and the advantages it brings to data engineers and developers.
 Do mysql need to pay
Apr 08, 2025 pm 05:36 PM
Do mysql need to pay
Apr 08, 2025 pm 05:36 PM
MySQL has a free community version and a paid enterprise version. The community version can be used and modified for free, but the support is limited and is suitable for applications with low stability requirements and strong technical capabilities. The Enterprise Edition provides comprehensive commercial support for applications that require a stable, reliable, high-performance database and willing to pay for support. Factors considered when choosing a version include application criticality, budgeting, and technical skills. There is no perfect option, only the most suitable option, and you need to choose carefully according to the specific situation.




