 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to implement more secure SSH login on CentOS server using key authentication
How to implement more secure SSH login on CentOS server using key authentication
How to implement more secure SSH login on CentOS server using key authentication
How to use key authentication to achieve more secure SSH login on CentOS server
In server management, ensuring system security is crucial. SSH (Secure Shell) is an encrypted network protocol used for remote login to Linux and UNIX servers. To further strengthen the security of the server, we can use key authentication instead of password login. This article will introduce how to implement a more secure SSH login on a CentOS server and provide corresponding code examples.
Step 1: Generate a key pair
First, generate a key pair on the local machine. Open a terminal window and enter the following command:
ssh-keygen -t rsa
This command will use the RSA algorithm to generate a key pair. Press Enter to confirm the key saving path and file name. You will then be asked to enter the password for your key. You can choose to set a password or leave it blank and press Enter to continue generating the key.
After successful generation, you will find two files under the specified path: id_rsa (private key) and id_rsa.pub (public key).
Step 2: Copy the public key to the server
Next, copy the public key to the CentOS server. Copy the public key to the server using the following command:
ssh-copy-id user@server_ip_address
Replace "user" with your username on the CentOS server and "server_ip_address" with the server's IP address. You will be asked to enter your password to authenticate.
After successfully copying the public key, you will get the following output:
Number of key(s) added: 1
Step 3: Configure SSH service
On the server, open the SSH configuration file to set it up. Open the file with the following command:
sudo vi /etc/ssh/sshd_config
Locate and ensure that the following lines are uncommented and set the values as follows:
PubkeyAuthentication yes PasswordAuthentication no PermitRootLogin no
Uncommenting means allow public key authentication, disable password authentication, and prohibit Log in directly as root user. After making changes, save and close the file.
Next, restart the SSH service to apply the changes:
sudo systemctl restart sshd
Step 4: Test SSH login
Now, you have completed the configuration. You can test whether the SSH login is successful using the following command:
ssh user@server_ip_address
Replace "user" with your username and "server_ip_address" with the server's IP address. The system will attempt to authenticate using your private key.
If everything is set up correctly, you will successfully log in to your CentOS server without entering a password.
Extra Tip:
- To further enhance server security, you can use Passphrase to protect the private key. In this way, even if the private key is stolen, the authentication cannot be passed.
- Make sure the permissions of the private key file are set to 600, that is, only the owner can read and write.
- Use different key pairs to authenticate multiple users.
- Replace the key pair regularly to increase security.
Summary:
Using key authentication can greatly improve the security of the server and prevent malicious logins and password brute force cracking. This article describes how to implement a more secure SSH login on a CentOS server and provides corresponding code examples. By following these steps, you can easily set up key authentication for your server and keep your system secure.
The above is the detailed content of How to implement more secure SSH login on CentOS server using key authentication. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
![Telnet in Windows 11 Complete Tutorial [Installation/Enablement and Troubleshooting]](https://img.php.cn/upload/article/000/000/164/168476253791019.jpg?x-oss-process=image/resize,m_fill,h_207,w_330) Telnet in Windows 11 Complete Tutorial [Installation/Enablement and Troubleshooting]
May 22, 2023 pm 09:35 PM
Telnet in Windows 11 Complete Tutorial [Installation/Enablement and Troubleshooting]
May 22, 2023 pm 09:35 PM
<p>Telnet is the abbreviation of "Terminal Network". It is a protocol that users can use to connect one computer to a local computer. </p><p>Here, the local computer refers to the device that initiates the connection, and the computer connected to the local computer is called the remote computer. </p><p>Telnet runs on a client/server principal, and although it is outdated, it is still used by many people in 2022. Many people have already switched to Windows 11 operating system, which is the latest operating system offered by Microsoft. &
 How to SSH from iPad to Mac
Apr 14, 2023 pm 12:22 PM
How to SSH from iPad to Mac
Apr 14, 2023 pm 12:22 PM
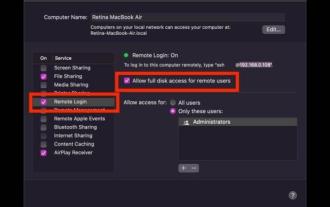
How to SSH from iPad to Mac This is a two-part walkthrough. First, you'll enable the SSH server on your Mac, and then you'll use the ssh client app to connect to it from your iPad. On Mac, start an SSH server You can enable an SSH server on your Mac by turning on a feature called Remote Login. Go to Apple Menu > System Preferences > Sharing > Enable "Remote Login" and check the "Allow remote users full access to disk" box Your Mac is now an SSH server, providing you with a shell to connect from your iPad. Notice
 Python server programming: Using Paramiko to implement SSH remote operation
Jun 18, 2023 pm 01:10 PM
Python server programming: Using Paramiko to implement SSH remote operation
Jun 18, 2023 pm 01:10 PM
With the development of cloud computing and the Internet of Things, remote operation of servers has become increasingly important. In Python, we can use the Paramiko module to easily implement SSH remote operations. In this article, we will introduce the basic usage of Paramiko and how to use Paramiko in Python to remotely manage servers. What is Paramiko Paramiko is a Python module for SSHv1 and SSHv2 that can be used to connect and control SSH clients
 How to use an IP blacklist to block malicious IP addresses from accessing your CentOS server
Jul 05, 2023 am 11:30 AM
How to use an IP blacklist to block malicious IP addresses from accessing your CentOS server
Jul 05, 2023 am 11:30 AM
How to use IP blacklists to prevent malicious IP addresses from accessing CentOS servers Servers operating on the Internet often face attacks from malicious IP addresses, and these attacks may cause server performance degradation or even system crashes. In order to protect the security and stability of the server, CentOS server provides a simple and effective way to block access from malicious IP addresses, that is, using an IP blacklist. An IP blacklist is a list of IP addresses that are considered threatening or malicious. When the server receives data from these IP
 OpenSSH on Windows: Installation, Configuration, and Usage Guide
Mar 08, 2024 am 09:31 AM
OpenSSH on Windows: Installation, Configuration, and Usage Guide
Mar 08, 2024 am 09:31 AM
For most Windows users, Remote Desktop Protocol (RDP) has always been the first choice for remote management because it provides a friendly graphical interface. However, for system administrators who require more granular control, SSH may better suit their needs. Through SSH, administrators can interact with remote devices through the command line, which can make management work more efficient. The advantage of SSH is its security and flexibility, making it easier for administrators to perform remote management and maintenance work, especially when dealing with a large number of devices or performing automated tasks. So while RDP excels in terms of user-friendliness, for system administrators, SSH is superior in terms of power and control. Previously, Windows users needed to borrow
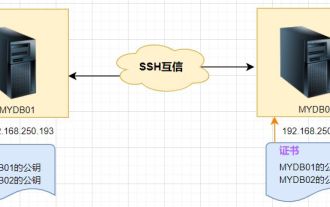 Linux SSH login mutual trust configuration
Feb 19, 2024 pm 07:48 PM
Linux SSH login mutual trust configuration
Feb 19, 2024 pm 07:48 PM
1. The purpose of ssh mutual trust 1. SSH mutual trust is required when building a cluster, which is conducive to convenient operation on another node. 2. When using scp remote copy operation, you need to enter the user name and password of the target server. At this time, you can configure SSH mutual trust between Linux servers, so that you can log in without a password when operating between multiple Linux servers. 2. The principle of ssh mutual trust configuration. In short, the server stores the certificate of the target host so that authentication can be completed automatically without entering a password. 3. SSH mutual trust configuration steps 1. Each node generates its own public key and private key pair. 2. Send your public key file to the other party. 3. Verify whether the mutual trust configuration is successful. 4. Configure ssh mutual trust here with MYDB01 and
 How to connect to Mysql database remotely using Python based on ssh
May 27, 2023 pm 04:07 PM
How to connect to Mysql database remotely using Python based on ssh
May 27, 2023 pm 04:07 PM
Background: If you need to access the Mysql database of a remote server, but for the security period of the Mysql database, the security measures are set to only allow local connections (that is, you need to log in to the server to use it), and other remote connections cannot be accessed directly, and The corresponding port has also been modified, so you need to connect to the database based on ssh. Connecting to the database in this way is the same as the interface in Navicat based on ssh connection. Navicat connects to the database installation support library. If you want to connect to Mysql, you first need to install pymysqlpipinstallpymysql to install the ssh-based library sshtunnelpipinstallsshtunnel#
 How to Protect CentOS Servers Using Network Intrusion Detection Systems (NIDS)
Jul 05, 2023 pm 02:13 PM
How to Protect CentOS Servers Using Network Intrusion Detection Systems (NIDS)
Jul 05, 2023 pm 02:13 PM
How to Protect CentOS Servers Using Network Intrusion Detection Systems (NIDS) Introduction: In modern network environments, server security is crucial. Attackers use a variety of means to try to break into our servers and steal sensitive data or compromise systems. To ensure server security, we can use a Network Intrusion Detection System (NIDS) for real-time monitoring and detection of potential attacks. This article will introduce how to configure and use NIDS on a CentOS server to protect the server. Step 1: Install and configure SN



