 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to use file integrity checking to detect file modifications on CentOS systems
How to use file integrity checking to detect file modifications on CentOS systems
How to use file integrity checking to detect file modifications on CentOS systems
How to use file integrity checking to detect file modifications on CentOS systems
Introduction:
In modern computer systems, file integrity checking is one of the important means to ensure system security. By periodically checking the integrity of system files, tampered or damaged files can be discovered and repaired in a timely manner, preventing the system from unknown security threats. In this article, we will explain how to use the file integrity check feature on CentOS systems.
1. File integrity checking tool in CentOS system
CentOS system comes with a powerful file integrity checking tool——tripwire. This tool can perform hash calculations on specified files and save the results in the file database. When a file is modified or the hash value is changed, tripwire will sound an alert and alert the administrator to take action.
2. Installation and configurationtripwire
-
Installation
tripwire:sudo yum install tripwire
Copy after login Initialization
tripwire:sudo tripwire-setup-keyfiles sudo tripwire --init
Copy after login- Parameter settings in the configuration file (
/etc/tripwire/twcfg.txt): -
ROOT: The path to the root directory, the default is/, generally does not need to be modified unless there are special requirements. POLFILE: The path to the policy file, which defines the files or directories that need to be checked. The default is/etc/tripwire/twpol.txt.SITEKEYFILE: The path to store thetripwirekey, the default is/etc/tripwire/site.key.
3. Create a policy file (/etc/tripwire/twpol.txt)
According to actual needs, you can specify files that need to be integrity checked in the policy file. or directory. Take checking the /etc/passwd file as an example. The content of the policy file is as follows:
(
rulename = "etc_passwd", # 规则名称
severity = $(SIG_HI), # 严重级别
emailto = "admin@example.com", # 发送警报的邮件地址
files = (
"/etc/passwd", # 需要检查的文件路径
),
)4. Generate configuration files and database files
Generate configuration File:
sudo twadmin --create-cfgfile -P tripwire.cfg
Copy after loginGenerate database file:
sudo tripwire --update -P tripwire.cfg /etc/tripwire/twpol.txt
Copy after login
5. Regular inspection and automation
Manually run the check:
sudo tripwire --check -P tripwire.cfg
Copy after login- Set up regular tasks:
Usecronor other scheduled task tools to run thetripwirecheck command regularly to Implement automated inspections and reporting.
6. Operation Example
View detailed inspection results of
tripwire:sudo tripwire --check | more
Copy after login- View alarm Logs:
Alert logs are saved by default in the/var/lib/tripwire/<hostname>-<date>.twrfile.
Conclusion:
By using the tripwire tool, we can automatically check and monitor file integrity on CentOS systems. This helps us protect the security of our systems and detect and address any potential security issues promptly. At the same time, reasonable setting of inspection strategies and regular automation can reduce the operational pressure of administrators and improve work efficiency. Hopefully this article has been helpful for you to use file integrity checking to detect file modifications on CentOS systems.
The above is the detailed content of How to use file integrity checking to detect file modifications on CentOS systems. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to use the audit log of a CentOS system to detect unauthorized access to the system
Jul 05, 2023 pm 02:30 PM
How to use the audit log of a CentOS system to detect unauthorized access to the system
Jul 05, 2023 pm 02:30 PM
How to use the audit log of the CentOS system to monitor unauthorized access to the system. With the development of the Internet, network security issues have become increasingly prominent, and many system administrators have paid more and more attention to the security of the system. As a commonly used open source operating system, CentOS's audit function can help system administrators monitor system security, especially for unauthorized access. This article will introduce how to use the audit log of the CentOS system to monitor unauthorized access to the system and provide code examples. 1. Start the audit day
 CentOS 6.6 system installation and configuration full illustrated tutorial
Jan 12, 2024 pm 04:27 PM
CentOS 6.6 system installation and configuration full illustrated tutorial
Jan 12, 2024 pm 04:27 PM
The server-related settings are as follows: Operating system: CentOS6.6 64-bit IP address: 192.168.21.129 Gateway: 192.168.21.2 DNS: 8.8.8.88.8.4.4 Remarks: CentOS6.6 system image has two versions, 32-bit and 64-bit, and There is also a minimal version of the production server that is specially optimized for servers. If the production server has large memory (4G) 1. The computer memory on which CentOS6.6 system is installed must be equal to or greater than 628M (minimum memory 628M) before the graphical installation mode can be enabled; 2. CentOS6.6 The system installation methods are divided into: graphical installation mode and text installation mode.
 How to set up your CentOS system to regularly update security patches
Jul 05, 2023 pm 04:17 PM
How to set up your CentOS system to regularly update security patches
Jul 05, 2023 pm 04:17 PM
How to set up CentOS systems to regularly update security patches As network security risks continue to increase, regularly updating security patches for the operating system is crucial to protecting the security of servers and terminal devices. This article will introduce how to set up automatic and regular security patch updates on CentOS systems and provide corresponding code examples. Using the yum-cron tool CentOS system provides a tool called yum-cron, which can help us automatically update system software packages and security patches. Use the following command to install
 How to identify and deal with security vulnerabilities in CentOS systems
Jul 05, 2023 pm 09:00 PM
How to identify and deal with security vulnerabilities in CentOS systems
Jul 05, 2023 pm 09:00 PM
How to identify and deal with security vulnerabilities in CentOS systems In the Internet era, security vulnerabilities are crucial to the protection of systems and data. As a popular Linux distribution, CentOS is also different from other operating systems in that it requires users to identify and repair security vulnerabilities in a timely manner. This article will introduce readers to how to identify and deal with security vulnerabilities in CentOS systems, and provide some code examples for vulnerability repair. 1. Vulnerability Identification Using Vulnerability Scanning Tools Vulnerability scanning tools are a common method for identifying security vulnerabilities existing in the system.
 How to configure a CentOS system to protect web applications from cross-site scripting attacks
Jul 05, 2023 pm 06:10 PM
How to configure a CentOS system to protect web applications from cross-site scripting attacks
Jul 05, 2023 pm 06:10 PM
How to configure a CentOS system to protect web applications from cross-site scripting attacks. With the increasing popularity and usage of web applications, cross-site scripting (XSS) attacks have become an important security concern for many web developers. question. In order to protect web applications from XSS attacks, we can take some configuration measures to improve the security of the system. This article will introduce how to perform relevant configurations on CentOS systems. Configure the firewall first,
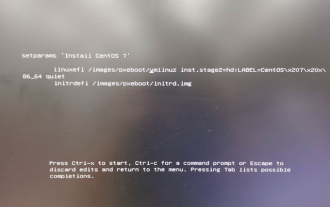 Install centos system to USB disk
Mar 18, 2024 pm 12:19 PM
Install centos system to USB disk
Mar 18, 2024 pm 12:19 PM
Today I received a request to install the Centos7.7 system on an already assembled host and use it as a server, which will later be used for program development. #Process Steps 1. First go to the official website to download the ISO image. The download address of the official website: https://www.centos.org/download/2. Burn the downloaded U disk to install the system. The tool I use here is Softdisk download address: https://cn.ultraiso.net/xiazai.html3. Insert the U disk for boot installation #Problems encountered during boot installation and solutions: Because I use the U disk to install using UEFI. The following occurred when booting the system
 How to set up your CentOS system to prevent the download and execution of malicious code
Jul 05, 2023 pm 01:12 PM
How to set up your CentOS system to prevent the download and execution of malicious code
Jul 05, 2023 pm 01:12 PM
How to set up a CentOS system to prevent the download and execution of malicious code? The downloading and execution of malicious code is a very important issue in network security. To protect your CentOS system from such attacks, there are some measures you can take. This article will introduce you to some basic security settings and configurations, as well as some commonly used protection technologies and tools. Keep your operating system and software packages updated: Regularly updating your operating system and software packages is an important step in preventing malicious code attacks. CentOS systems occasionally release security patches and updates to fix known
 How to use file integrity checking to detect file modifications on CentOS systems
Jul 05, 2023 pm 09:37 PM
How to use file integrity checking to detect file modifications on CentOS systems
Jul 05, 2023 pm 09:37 PM
How to use file integrity checking to detect file modifications on CentOS systems Introduction: In modern computer systems, file integrity checking is one of the important means to ensure system security. By periodically checking the integrity of system files, tampered or damaged files can be discovered and repaired in a timely manner, preventing the system from unknown security threats. In this article, we will introduce how to use the file integrity check feature on CentOS systems. 1. File integrity checking tool Cen in CentOS system





