 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Teach you how to use PHP and Vue.js to develop applications that defend against information hijacking attacks
Teach you how to use PHP and Vue.js to develop applications that defend against information hijacking attacks
Teach you how to use PHP and Vue.js to develop applications that defend against information hijacking attacks
Teach you how to use PHP and Vue.js to develop applications that defend against information hijacking attacks
Introduction:
With the development of network technology, information hijacking attacks have become a common type in the field of network security threats. Information hijacking attack refers to an attack method in which hackers obtain sensitive user information by tampering with network data packets or maliciously injecting malicious code. In order to protect user privacy and data security, we need to take appropriate defensive measures when developing applications. This article will use PHP and Vue.js as examples to teach you how to develop an application that defends against information hijacking attacks.
1. Understand the principles of information hijacking attacks
Before carrying out defense work, we first need to understand the principles of information hijacking attacks. Information hijacking attacks can occur on the front end or the back end, so we need to defend on both fronts.
- Front-end defense:
Front-end defense is mainly to prevent tampering with network data packets. Hackers may tamper with network packets to inject malicious code or obtain sensitive information. We can defend in the following ways: - Use HTTPS protocol: By using HTTPS protocol, we can ensure the security of data transmission and prevent hackers from eavesdropping and hijacking data.
- Control network request headers: We can set safe request headers, such as restricting Referer, User-Agent, etc., to prevent illegal network requests.
- Input verification and filtering: Verify and filter user input on the front end to prevent the injection of malicious code.
- Back-end defense:
Back-end defense is mainly to prevent the injection of malicious code. Hackers may inject malicious code to obtain sensitive user information or perform malicious operations. We can defend in the following ways: - Input verification and filtering: Verify and filter user input on the backend to prevent the injection of malicious code.
- Use safe database operation methods: such as using PDO or prepared statements to perform database operations to prevent SQL injection attacks.
2. Develop an application that defends against information hijacking attacks
Next we will use PHP and Vue.js to develop a simple message board application and add the function of defending against information hijacking attacks. In this application, users can post messages, but we will validate and filter user input to prevent malicious code injection.
- Back-end development
First we need to create a back-end interface to handle the user's message operation.
<?php
header('Content-Type: application/json');
$data = json_decode(file_get_contents('php://input'), true);
// 验证用户输入
if(isset($data['message']) && !empty($data['message'])){
$message = filter_var($data['message'], FILTER_SANITIZE_STRING);
// 将留言存入数据库或其他存储方式
$messageId = saveMessageToDatabase($message);
echo json_encode(array('status' => 'success', 'messageId' => $messageId));
}else{
echo json_encode(array('status' => 'error', 'message' => 'Invalid input'));
}In this code, we first obtain the user's input data, and then use the filter_var function to validate and filter the input data. Finally, the verified data is saved to the database and a JSON response containing the processing results is returned.
- Front-end development
In front-end development, we use Vue.js to build the user interface, and we can also use Vue.js to verify and filter user input.
<div id="app">
<textarea v-model="message" rows="4" cols="50"></textarea>
<button @click="submit">提交</button>
</div>
<script src="https://cdn.jsdelivr.net/npm/vue/dist/vue.js"></script>
<script>
new Vue({
el: '#app',
data: {
message: ''
},
methods: {
submit: function(){
// 验证用户输入
if(this.message.trim() !== ''){
// 提交留言
axios.post('http://your-backend-url', {
message: this.message
}).then(function(response){
if(response.data.status === 'success'){
alert('留言提交成功');
}else{
alert('留言提交失败');
}
}).catch(function(error){
alert('留言提交失败');
});
}else{
alert('请输入留言内容');
}
}
}
});
</script>In this code, we use the v-model directive of Vue.js to implement two-way data binding with the textarea element. When the user clicks the submit button, we will determine whether the user input is empty. If not, use the axios.post method to send message data to the backend.
It should be noted here that we use the axios library to make network requests because it supports cross-domain requests and CSRF protection.
3. Summary
Through the introduction and sample code of this article, I believe that everyone has a certain understanding of how to use PHP and Vue.js to develop applications that defend against information hijacking attacks. During the development process, we need to fully understand the principles of information hijacking attacks and take corresponding defensive measures. The use of HTTPS protocol, reasonable control of network request headers, input verification and filtering, and secure database operation methods are all common defense measures.
Of course, there are various ways of information hijacking attacks, and different application scenarios may also present different threats. Therefore, when developing applications, we also need to combine other security technologies and best practices to carry out comprehensive security protection based on the actual situation.
The above is the detailed content of Teach you how to use PHP and Vue.js to develop applications that defend against information hijacking attacks. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an
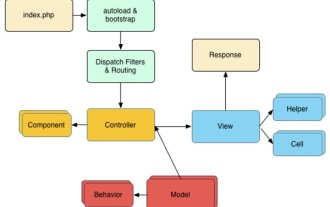 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 7 PHP Functions I Regret I Didn't Know Before
Nov 13, 2024 am 09:42 AM
7 PHP Functions I Regret I Didn't Know Before
Nov 13, 2024 am 09:42 AM
If you are an experienced PHP developer, you might have the feeling that you’ve been there and done that already.You have developed a significant number of applications, debugged millions of lines of code, and tweaked a bunch of scripts to achieve op



