 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 How to configure a CentOS system to restrict user access to system processes
How to configure a CentOS system to restrict user access to system processes
How to configure a CentOS system to restrict user access to system processes
How to configure the CentOS system to restrict user access to system processes
In a Linux system, users can access and control system processes through the command line or other methods. However, sometimes we need to restrict certain users' access to system processes to enhance system security and prevent malicious behavior. This article will introduce how to configure on CentOS systems to restrict user access to system processes.
- Use PAM configuration restrictions
PAM, Pluggable Authentication Modules, is a modular authentication mechanism in Linux systems. By modifying the PAM configuration file, we can implement restrictions on users. Here are the steps on how to configure PAM to restrict user access to system processes:
First, edit the /etc/security/access.conf file:
sudo vi /etc/security/access.conf
Add the following content to the file:
-:user:ALL, EXCEPT root systemd
This will prevent the 'user' user from accessing all system processes except root and systemd users.
Next, edit the /etc/pam.d/login file:
sudo vi /etc/pam.d/login
Add the following at the end of the file:
account required pam_access.so
This will check when the user logs in/ Access rules in the etc/security/access.conf file.
Finally, restart the system to make the PAM configuration take effect:
sudo reboot
- Use the Linux system permission management tool
In addition to PAM, the Linux system also provides Other permission management tools such as selinux and sudoers files. Here's how to use these two tools to limit user access to system processes:
SELinux is a security subsystem that implements mandatory access control. By modifying the selinux configuration file, we can restrict user access to system processes. Edit the /etc/selinux/config file:
sudo vi /etc/selinux/config
Set the value of SELINUX to enforcing:
SELINUX=enforcing
Save and close the file.
Then, restart the system for the configuration to take effect:
sudo reboot
sudoers is a configuration file used to manage user permissions. By modifying the sudoers file, we can assign specific permissions to users. Edit the sudoers file:
sudo visudo
Add the following content in the file:
user ALL=(ALL) ALL user ALL=!/bin/kill
This will allow the 'user' user to use sudo commands and restrict its access to the kill command (used to kill processes) access permission.
Save and close the file.
- Use ACL to set process access permissions
ACL, or Access Control List, is an additional permission setting in the Linux system. By using ACLs, we can set access permissions for specific processes for specific users or user groups. The following are the steps on how to use ACL to restrict user access to system processes:
First, install the acl package:
sudo yum install acl
Then, use setfacl for files that need to restrict process access The command sets ACL rules for users or user groups. For example, to restrict the 'user1' user's access to process 1:
sudo setfacl -m u:user1:--- /proc/1
This will disable the 'user1' user's access to process 1.
You can use the getfacl command to check whether the ACL rules have taken effect:
getfacl /proc/1
After the configuration is completed, the user's access to system processes will be restricted.
Summary:
This article describes how to configure on CentOS systems to restrict user access to system processes. By using PAM configuration files, selinux and sudoers files, and ACL settings, we can effectively prevent malicious users from accessing and operating system processes. These measures can further improve the security and stability of the system. In actual use, please choose the appropriate configuration method based on actual needs and follow security best practices.
The above is the detailed content of How to configure a CentOS system to restrict user access to system processes. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 Win11 user permissions setting tutorial: How to configure Win11 user permissions
Jan 29, 2024 pm 08:33 PM
Win11 user permissions setting tutorial: How to configure Win11 user permissions
Jan 29, 2024 pm 08:33 PM
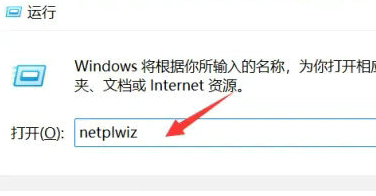
Some users will create multiple accounts when using computers, but some users' accounts do not have permissions, which means some operations cannot be performed directly? How to set user permissions in Win11? Users who are not sure can come to this site to see related strategies. How to set user permissions in Win11 1. Directly create the run function through the shortcut key combination [win+R], then enter [netplwiz] in the search box and click OK. 3. In the properties window that opens, click Group Members in the upper menu bar. 5. A window prompt will appear. Just click [Yes] to log out and restart the account to complete the settings.
 How to implement user login and permission control in PHP?
Jun 29, 2023 pm 02:28 PM
How to implement user login and permission control in PHP?
Jun 29, 2023 pm 02:28 PM
How to implement user login and permission control in PHP? When developing web applications, user login and permission control are one of the very important functions. Through user login, we can authenticate the user and perform a series of operational controls based on the user's permissions. This article will introduce how to use PHP to implement user login and permission control functions. 1. User login function Implementing the user login function is the first step in user verification. Only users who have passed the verification can perform further operations. The following is a basic user login implementation process: Create
 How to set up a CentOS system to restrict network access and protect privacy
Jul 05, 2023 pm 09:13 PM
How to set up a CentOS system to restrict network access and protect privacy
Jul 05, 2023 pm 09:13 PM
How to set up a CentOS system to restrict network access and protect privacy. With the development of the Internet, we need to pay more attention to network access and privacy protection issues when using the operating system. This article will introduce how to set up a CentOS system to restrict network access and protect privacy, thereby improving system security. Install necessary software tools First, you need to install some software tools to help you set up network access and protect privacy. Open a terminal and enter the following command to install the required software: sudoyuminstall
 Node.js development: How to implement user rights management functions
Nov 08, 2023 am 09:17 AM
Node.js development: How to implement user rights management functions
Nov 08, 2023 am 09:17 AM
Title: Node.js Development: User Rights Management Function Implementation and Code Examples Abstract: As the complexity of web applications and systems continues to increase, user rights management has become an important function that cannot be ignored. This article will introduce how to implement user rights management functions in Node.js development and give specific code examples. Introduction: As an efficient and lightweight development platform, Node.js has a wide range of application scenarios. In the development of many Node.js applications, user rights management is often an essential function.
 Reasons for Linux permission denied exception
Feb 20, 2024 am 10:43 AM
Reasons for Linux permission denied exception
Feb 20, 2024 am 10:43 AM
The Linux operating system is an open source operating system that is widely used on various devices such as servers and personal computers. When using Linux, you often encounter "PermissionDenied" exceptions. This article will explore the causes of this exception and give specific code examples. Each file and directory in Linux has corresponding permission settings to control the user's read, write and execution permissions. Permissions are divided into three levels: user permissions, group permissions and other user permissions. When used
 Windows 10 Home Edition standard user changed to administrator
Feb 14, 2024 pm 09:12 PM
Windows 10 Home Edition standard user changed to administrator
Feb 14, 2024 pm 09:12 PM
I upgraded to Windows 10 some time ago. I accidentally changed the administrator to a standard user a few days ago. I found that I couldn't open many software, couldn't play games, and couldn't perform operations related to the administrator. Then I finally found a way. Let's take a look. . Change the standard user of Windows 10 Home Edition to an administrator 1. First open the new notification in the lower right corner of the desktop and click All Settings 2. After opening, click Update and Maintenance 3. Click Recovery, click Restart Now under Advanced Startup 4. After restarting, Enter this interface, and then select Troubleshooting. 5. In the troubleshooting interface, click Advanced Options to open the interface. 6. Click Start Settings. There is a restart button under the interface. Click 7. Select 4 to start safe mode. 8. Click Afterwards, the system restarts,
 How to configure a CentOS system to restrict user access to system processes
Jul 08, 2023 pm 01:05 PM
How to configure a CentOS system to restrict user access to system processes
Jul 08, 2023 pm 01:05 PM
How to configure the CentOS system to restrict user access to system processes In a Linux system, users can access and control system processes through the command line or other methods. However, sometimes we need to restrict certain users' access to system processes to enhance system security and prevent malicious behavior. This article will introduce how to configure on CentOS systems to restrict user access to system processes. Use PAM configuration to restrict PAM, namely PluggableAuthentication
 Permission control in Yii framework: controlling user access permissions
Jun 21, 2023 pm 06:54 PM
Permission control in Yii framework: controlling user access permissions
Jun 21, 2023 pm 06:54 PM
In web applications, security is crucial. To protect the confidentiality of user data and applications, access control is necessary. In many cases, users only have access to the resources or information they need. The Yii framework's permission management component provides a simple and effective way to achieve this. The RBAC (Role-BasedAccessControl) solution of the Yii framework aims to define access control as permissions that are both clear and flexible. The core of the RBAC program is in the application



