 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 Implementation of PHP security verification and authorization technology
Implementation of PHP security verification and authorization technology
Implementation of PHP security verification and authorization technology
Implementation of PHP security verification and authorization technology
Introduction:
With the rapid development of the Internet, security has become an important issue in website and application development. an important aspect. Especially for websites and applications developed using the PHP language, the implementation of security verification and authorization technology is essential. This article will introduce some common PHP security verification and authorization technologies and give corresponding code examples.
1. User login authentication and verification
User login authentication and verification is one of the most basic and commonly used security verification technologies. By verifying a user's username and password, we ensure that only legitimate users have access to the website's sensitive information and functionality. The following is a simple code example for user login authentication verification:
<?php
session_start();
// 用户登录验证
function login($username, $password){
// 假设从数据库中取得用户信息
$userData = getUserData($username);
// 验证用户名和密码
if($userData && $userData['password'] == md5($password)){
$_SESSION['username'] = $username;
return true;
}else{
return false;
}
}
// 检查用户是否已登录
function checkLogin(){
return isset($_SESSION['username']);
}
// 获取当前登录用户信息
function getCurrentUser(){
return getUserData($_SESSION['username']);
}
// 退出登录
function logout(){
unset($_SESSION['username']);
session_destroy();
}
// 获取用户信息,这里仅作示例
function getUserData($username){
// 假设数据库查询用户信息
$userData = array(
'username' => 'admin',
'password' => md5('123456'),
'email' => 'admin@example.com'
// 其他用户相关信息
);
return $userData;
}
?>Using the above code, you can first call the checkLogin() function to check whether the user is logged in on the page that needs to verify the user's login. , if you are not logged in, you can jump to the login page, if you are logged in, you can continue to execute business logic. During the form submission process on the login page, call the login() function to verify whether the user name and password entered by the user are correct.
2. Access Control List (ACL)
Access Control List (ACL) is a commonly used authorization technology used to restrict different users' access to websites. ACL technology can be used to flexibly control users' access rights to different pages, functions and resources. The following is a simple ACL code example:
<?php
// 假设当前登录用户
$user = getCurrentUser();
// 访问控制列表
$acl = array(
'admin' => array('admin.php', 'user.php', 'post.php'),
'user' => array('user.php', 'post.php'),
'guest' => array('index.php')
);
// 检查用户是否有权限访问当前页面
function checkAccess($user, $page){
global $acl;
if(isset($acl[$user])){
return in_array($page, $acl[$user]);
}
return false;
}
// 使用示例
if(checkAccess($user['role'], 'user.php')){
// 用户有权限访问user.php页面
// 执行相应的业务逻辑
}else{
// 用户没有权限访问user.php页面
// 返回错误提示或者跳转到其他页面
}
?>In the above code, $user['role'] represents the role of the currently logged in user (such as: 'admin', 'user' , 'guest', etc.), the $acl array represents the accessible pages corresponding to different user roles. In actual applications, you can modify the $acl array according to actual needs to adapt to your own authorization needs.
Summary:
This article introduces the implementation of PHP security verification and authorization technology, and gives corresponding code examples. User login authentication verification and access control lists (ACLs) are common security verification and authorization technologies that are critical to ensuring the security of websites and applications. Developers should flexibly adopt corresponding technologies based on actual needs and strengthen the security protection of user input and sensitive information.
The above is the detailed content of Implementation of PHP security verification and authorization technology. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
CakePHP Date and Time
Sep 10, 2024 pm 05:27 PM
To work with date and time in cakephp4, we are going to make use of the available FrozenTime class.
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
CakePHP Creating Validators
Sep 10, 2024 pm 05:26 PM
Validator can be created by adding the following two lines in the controller.
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
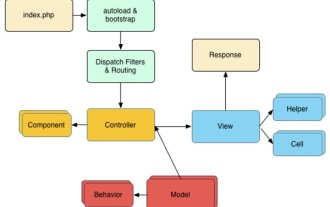 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an



