How to use PHP to prevent registration attacks?
How to use PHP to prevent registration attacks?
With the development of the Internet, the registration function has become one of the necessary functions for almost all websites. However, bad elements also took this opportunity to carry out registration attacks and maliciously registered a large number of fake accounts, causing many problems to the website. In order to prevent registration brush attacks, we can use some effective technical means. This article will introduce a method to prevent registration attacks using the PHP programming language and provide corresponding code examples.
1. IP address restriction
Registration attacks usually come from the same IP address. Therefore, we can prevent attacks by limiting the number of registrations of the same IP address within a certain period of time. The following is a code example of IP address restriction implemented using PHP:
<?php
// 获取客户端IP地址
$ip = $_SERVER['REMOTE_ADDR'];
// 设定时间间隔,单位为秒
$interval = 60;
// 检查指定IP在指定时间间隔内的注册次数
function checkRegistrationCount($ip, $interval) {
$file = 'registration_counts.txt';
$counts = unserialize(file_get_contents($file));
if ($counts[$ip] && time() - $counts[$ip]['time'] <= $interval) {
// 注册次数超过限制
if ($counts[$ip]['count'] >= 3) {
return false;
} else {
$counts[$ip]['count']++;
}
} else {
$counts[$ip] = array('count' => 1, 'time' => time());
}
file_put_contents($file, serialize($counts));
return true;
}
// 检查IP地址是否超过注册次数限制
if (!checkRegistrationCount($ip, $interval)) {
echo "注册次数超过限制,请稍后再试!";
exit;
}
?>The above code uses the client's IP address as the key, the number of registrations and the registration time as the values, and stores them in a file called registration_counts.txt in the file. Each time there is a new registration request, the code checks whether the number of registrations for that IP address within the specified time interval exceeds the set limit.
2. Verification code verification
Using verification code can effectively prevent robot registration attacks. The following is a sample code that uses the PHP GD library to generate an image verification code:
<?php
session_start();
// 生成随机验证码
function generateCaptcha() {
$length = 4;
$chars = "abcdefghijklmnopqrstuvwxyzABCDEFGHIJKLMNOPQRSTUVWXYZ0123456789";
$captcha = "";
for ($i = 0; $i < $length; $i++) {
$captcha .= $chars[rand(0, strlen($chars) - 1)];
}
return $captcha;
}
$captcha = generateCaptcha();
// 存储验证码到session中
$_SESSION['captcha'] = $captcha;
// 创建一张图片并写入验证码
$image = imagecreatetruecolor(100, 30);
$bg_color = imagecolorallocate($image, 255, 255, 255);
$text_color = imagecolorallocate($image, 0, 0, 0);
imagefilledrectangle($image, 0, 0, 100, 30, $bg_color);
imagestring($image, 5, 25, 8, $captcha, $text_color);
header('Content-type: image/png');
imagepng($image);
imagedestroy($image);
?>The above code generates a random 4-digit verification code and stores it in $_SESSION. Then, create a picture with a verification code through the PHP GD library and output it to the user.
In the registration page, we can quote the above script that generates the verification code so that the user can fill in the verification code and submit the registration request. We can then determine the legitimacy of the registration request by verifying whether the verification code submitted by the user matches the verification code stored in $_SESSION.
To sum up, through the two technical means of IP address restriction and verification code verification, we can effectively prevent registration-swiping attacks. I hope the code examples provided in this article can help you prevent registration attacks using PHP.
The above is the detailed content of How to use PHP to prevent registration attacks?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 Installation and Upgrade guide for Ubuntu and Debian
Dec 24, 2024 pm 04:42 PM
PHP 8.4 brings several new features, security improvements, and performance improvements with healthy amounts of feature deprecations and removals. This guide explains how to install PHP 8.4 or upgrade to PHP 8.4 on Ubuntu, Debian, or their derivati
 Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
Discuss CakePHP
Sep 10, 2024 pm 05:28 PM
CakePHP is an open-source framework for PHP. It is intended to make developing, deploying and maintaining applications much easier. CakePHP is based on a MVC-like architecture that is both powerful and easy to grasp. Models, Views, and Controllers gu
 CakePHP File upload
Sep 10, 2024 pm 05:27 PM
CakePHP File upload
Sep 10, 2024 pm 05:27 PM
To work on file upload we are going to use the form helper. Here, is an example for file upload.
 How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
How To Set Up Visual Studio Code (VS Code) for PHP Development
Dec 20, 2024 am 11:31 AM
Visual Studio Code, also known as VS Code, is a free source code editor — or integrated development environment (IDE) — available for all major operating systems. With a large collection of extensions for many programming languages, VS Code can be c
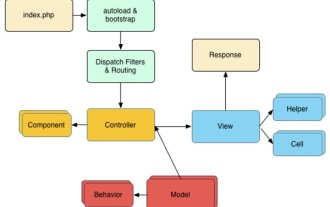 CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP Quick Guide
Sep 10, 2024 pm 05:27 PM
CakePHP is an open source MVC framework. It makes developing, deploying and maintaining applications much easier. CakePHP has a number of libraries to reduce the overload of most common tasks.
 How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
How do you parse and process HTML/XML in PHP?
Feb 07, 2025 am 11:57 AM
This tutorial demonstrates how to efficiently process XML documents using PHP. XML (eXtensible Markup Language) is a versatile text-based markup language designed for both human readability and machine parsing. It's commonly used for data storage an
 Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
Explain JSON Web Tokens (JWT) and their use case in PHP APIs.
Apr 05, 2025 am 12:04 AM
JWT is an open standard based on JSON, used to securely transmit information between parties, mainly for identity authentication and information exchange. 1. JWT consists of three parts: Header, Payload and Signature. 2. The working principle of JWT includes three steps: generating JWT, verifying JWT and parsing Payload. 3. When using JWT for authentication in PHP, JWT can be generated and verified, and user role and permission information can be included in advanced usage. 4. Common errors include signature verification failure, token expiration, and payload oversized. Debugging skills include using debugging tools and logging. 5. Performance optimization and best practices include using appropriate signature algorithms, setting validity periods reasonably,
 PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
PHP Program to Count Vowels in a String
Feb 07, 2025 pm 12:12 PM
A string is a sequence of characters, including letters, numbers, and symbols. This tutorial will learn how to calculate the number of vowels in a given string in PHP using different methods. The vowels in English are a, e, i, o, u, and they can be uppercase or lowercase. What is a vowel? Vowels are alphabetic characters that represent a specific pronunciation. There are five vowels in English, including uppercase and lowercase: a, e, i, o, u Example 1 Input: String = "Tutorialspoint" Output: 6 explain The vowels in the string "Tutorialspoint" are u, o, i, a, o, i. There are 6 yuan in total




