harmful number
#A number is considered harmful if it is a positive integer and the set number of digits in its binary expansion is a prime number. The first harmful number is 3 because 3 = (11)2. It can be seen that the binary representation of 3 has a set number of digits of 2, which is a prime number.
The top 10 harmful numbers are 3, 5, 6, 7, 9, 10, 11, 12, 13, and 14. Interestingly, powers of 2 can never be harmful numbers because they always only have 1 bit set. 1 is not a prime number. On the other hand, all numbers that can be represented as 2n1, where n is any natural number, will always be bad numbers because they will have 2 set bits, and we know that 2 is a prime number.
Keeping in mind the properties of these harmful numbers, the following article discusses a way to check whether a number is harmful.
Problem Statement
This question aims to check whether the given number n is a harmful number, i.e. it is a positive number with a prime number of set bits in its binary expansion.
Example
Input: 37
Output: Pernicious
Explanation
is:Explanation
37 = Binary representation of 100101.
Set the number of digits = 3
Since 3 is a prime number, 37 is a bad number.
Input: 22
Output: Pernicious
Explanation
is:Explanation
22 = Binary representation of 10110.
Set number of digits = 3.
Since 3 is a prime number, 22 is a vicious number.
Input: 71
Output: Not Pernicious
Explanation
is:Explanation
The binary representation of71 is 1000111.
Set number of digits = 4.
Since 4 is not a prime number, 71 is not a harmful number either.
Input: 64
Output: Not Pernicious
Explanation
is:Explanation
The binary representation of64 is 1000000.
Set number of digits = 1.
Since 64 = 26, i.e. it is a power of 2, it has 1 set bit. Since 1 is not a prime number, 64 is not a vicious number.
solution
We must know whether the set number of digits is a prime number in order to determine whether a number is malicious. The main task at hand is to calculate the set number of digits in the binary expansion of this number. The following method can be used to calculate a set number of digits and then determine whether the result is a prime number.
This method includes the following steps -
Iterate over all bits of a number using loop and right shift operators.
If the bit value is 1, the count of the set bit is increased by 1.
Check whether the final value of the count is a prime number.
Show answer.
algorithm
Function is_prime()
If (n < 2)< 2)
Return error
for (i from 2 to √a)
If (a%i==0)
Return error
Return true
Function count_set_bits()
Initialization counter = 0
When (n > 0)
If ((n & 1) > 0)
Counter = Counter 1
n = n >> 1
Return Counter
Function is_pernious()
Initialize counter
Counter = count_set_bits(n)
if (is_prime(counter) == true)
return true
other
Return error
Function main()
Initialize n
if (is_pernious())
cout <<"harmful number"<<“harmful number字”
other
cout << "Non-harmful number"
Print output
Example: C program
The program uses the function
is_pernicious()
to determine whether a number is pernicious. It analyzes the least significant bits in each iteration of the loop by right shifting the value by n at the end of each iteration in the functioncount_set_bits()
. Then, it calls the functionis_prime()
to collect whether the set number of digits is a prime number.#include <iostream>
using namespace std;
// this function counts the number of set bits by analyzing the rightmost bit using a while loop till n > 0.
// it performs logical & operation between 1 and n to determine if the rightmost bit is set or not.
// if it is set, count is incremented by 1
// right shift the value of n to make the bit left of the rightmost bit, the new rightmost bit.
int count_set_bits(int n){
int count = 0;
while (n > 0){
// if the rightmost bit is 1: increment count
if ((n & 1) > 0){
count++;
}
// right shift the value of n to examine the next least significant bit
n = n >> 1;
}
return count;
}
// this function determines if count of set bits in the given number is prime
bool is_prime(int count){
if (count < 2)
return false;
for (int i = 2; i * i < count; i++){
if (count % i == 0)
return false;
}
return true;
}
// this functions states if count of set bits is prime -> pernicious
bool is_pernicious(int n){
int count;
count = count_set_bits(n);
// if count is prime return true
if (is_prime(count)){
return true;
}
return false;
}
// main function
int main(){
int n = 11;
if (is_pernicious(n)){
cout << n <<" is Pernicious Number";
}
else{
cout << n << " is Non-Pernicious Number";
}
return 0;
}
Output
11 is Pernicious Number
Space-time analysis
Time complexity: O(log(n) sqrt(count)). In the function count_set_bits(), the loop executes log(n) times as we analyze the number bit by bit. The function is_prime() takes O(sqrt(count)) time to check whether count is prime. Both functions will be called once during execution.
Space complexity: O(1), because no auxiliary space is used in the implementation. Regardless of the size of the input number, the algorithm always uses a constant amount of space.
in conclusion
Harmful numbers are an interesting mathematical concept and they can be easily and effectively identified using the methods discussed above. This article also describes the algorithm to be used, a C program solution, and time and space complexity analysis.
The above is the detailed content of harmful number. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
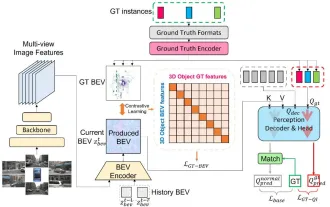 CLIP-BEVFormer: Explicitly supervise the BEVFormer structure to improve long-tail detection performance
Mar 26, 2024 pm 12:41 PM
CLIP-BEVFormer: Explicitly supervise the BEVFormer structure to improve long-tail detection performance
Mar 26, 2024 pm 12:41 PM
Written above & the author’s personal understanding: At present, in the entire autonomous driving system, the perception module plays a vital role. The autonomous vehicle driving on the road can only obtain accurate perception results through the perception module. The downstream regulation and control module in the autonomous driving system makes timely and correct judgments and behavioral decisions. Currently, cars with autonomous driving functions are usually equipped with a variety of data information sensors including surround-view camera sensors, lidar sensors, and millimeter-wave radar sensors to collect information in different modalities to achieve accurate perception tasks. The BEV perception algorithm based on pure vision is favored by the industry because of its low hardware cost and easy deployment, and its output results can be easily applied to various downstream tasks.
 AI subverts mathematical research! Fields Medal winner and Chinese-American mathematician led 11 top-ranked papers | Liked by Terence Tao
Apr 09, 2024 am 11:52 AM
AI subverts mathematical research! Fields Medal winner and Chinese-American mathematician led 11 top-ranked papers | Liked by Terence Tao
Apr 09, 2024 am 11:52 AM
AI is indeed changing mathematics. Recently, Tao Zhexuan, who has been paying close attention to this issue, forwarded the latest issue of "Bulletin of the American Mathematical Society" (Bulletin of the American Mathematical Society). Focusing on the topic "Will machines change mathematics?", many mathematicians expressed their opinions. The whole process was full of sparks, hardcore and exciting. The author has a strong lineup, including Fields Medal winner Akshay Venkatesh, Chinese mathematician Zheng Lejun, NYU computer scientist Ernest Davis and many other well-known scholars in the industry. The world of AI has changed dramatically. You know, many of these articles were submitted a year ago.
 Implementing Machine Learning Algorithms in C++: Common Challenges and Solutions
Jun 03, 2024 pm 01:25 PM
Implementing Machine Learning Algorithms in C++: Common Challenges and Solutions
Jun 03, 2024 pm 01:25 PM
Common challenges faced by machine learning algorithms in C++ include memory management, multi-threading, performance optimization, and maintainability. Solutions include using smart pointers, modern threading libraries, SIMD instructions and third-party libraries, as well as following coding style guidelines and using automation tools. Practical cases show how to use the Eigen library to implement linear regression algorithms, effectively manage memory and use high-performance matrix operations.
 Explore the underlying principles and algorithm selection of the C++sort function
Apr 02, 2024 pm 05:36 PM
Explore the underlying principles and algorithm selection of the C++sort function
Apr 02, 2024 pm 05:36 PM
The bottom layer of the C++sort function uses merge sort, its complexity is O(nlogn), and provides different sorting algorithm choices, including quick sort, heap sort and stable sort.
 Practice and reflections on Jiuzhang Yunji DataCanvas multi-modal large model platform
Oct 20, 2023 am 08:45 AM
Practice and reflections on Jiuzhang Yunji DataCanvas multi-modal large model platform
Oct 20, 2023 am 08:45 AM
1. The historical development of multi-modal large models. The photo above is the first artificial intelligence workshop held at Dartmouth College in the United States in 1956. This conference is also considered to have kicked off the development of artificial intelligence. Participants Mainly the pioneers of symbolic logic (except for the neurobiologist Peter Milner in the middle of the front row). However, this symbolic logic theory could not be realized for a long time, and even ushered in the first AI winter in the 1980s and 1990s. It was not until the recent implementation of large language models that we discovered that neural networks really carry this logical thinking. The work of neurobiologist Peter Milner inspired the subsequent development of artificial neural networks, and it was for this reason that he was invited to participate in this project.
 Improved detection algorithm: for target detection in high-resolution optical remote sensing images
Jun 06, 2024 pm 12:33 PM
Improved detection algorithm: for target detection in high-resolution optical remote sensing images
Jun 06, 2024 pm 12:33 PM
01 Outlook Summary Currently, it is difficult to achieve an appropriate balance between detection efficiency and detection results. We have developed an enhanced YOLOv5 algorithm for target detection in high-resolution optical remote sensing images, using multi-layer feature pyramids, multi-detection head strategies and hybrid attention modules to improve the effect of the target detection network in optical remote sensing images. According to the SIMD data set, the mAP of the new algorithm is 2.2% better than YOLOv5 and 8.48% better than YOLOX, achieving a better balance between detection results and speed. 02 Background & Motivation With the rapid development of remote sensing technology, high-resolution optical remote sensing images have been used to describe many objects on the earth’s surface, including aircraft, cars, buildings, etc. Object detection in the interpretation of remote sensing images
 Can artificial intelligence predict crime? Explore CrimeGPT's capabilities
Mar 22, 2024 pm 10:10 PM
Can artificial intelligence predict crime? Explore CrimeGPT's capabilities
Mar 22, 2024 pm 10:10 PM
The convergence of artificial intelligence (AI) and law enforcement opens up new possibilities for crime prevention and detection. The predictive capabilities of artificial intelligence are widely used in systems such as CrimeGPT (Crime Prediction Technology) to predict criminal activities. This article explores the potential of artificial intelligence in crime prediction, its current applications, the challenges it faces, and the possible ethical implications of the technology. Artificial Intelligence and Crime Prediction: The Basics CrimeGPT uses machine learning algorithms to analyze large data sets, identifying patterns that can predict where and when crimes are likely to occur. These data sets include historical crime statistics, demographic information, economic indicators, weather patterns, and more. By identifying trends that human analysts might miss, artificial intelligence can empower law enforcement agencies
 Application of algorithms in the construction of 58 portrait platform
May 09, 2024 am 09:01 AM
Application of algorithms in the construction of 58 portrait platform
May 09, 2024 am 09:01 AM
1. Background of the Construction of 58 Portraits Platform First of all, I would like to share with you the background of the construction of the 58 Portrait Platform. 1. The traditional thinking of the traditional profiling platform is no longer enough. Building a user profiling platform relies on data warehouse modeling capabilities to integrate data from multiple business lines to build accurate user portraits; it also requires data mining to understand user behavior, interests and needs, and provide algorithms. side capabilities; finally, it also needs to have data platform capabilities to efficiently store, query and share user profile data and provide profile services. The main difference between a self-built business profiling platform and a middle-office profiling platform is that the self-built profiling platform serves a single business line and can be customized on demand; the mid-office platform serves multiple business lines, has complex modeling, and provides more general capabilities. 2.58 User portraits of the background of Zhongtai portrait construction






