 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Create a secure Linux server environment: Master these commands
Create a secure Linux server environment: Master these commands
Create a secure Linux server environment: Master these commands
Create a secure Linux server environment: Master these commands
Introduction:
In the Internet age, protecting server security is crucial. As a stable, secure and customizable operating system, Linux has become the first choice for many servers. This article will introduce some commonly used Linux commands to help administrators create a secure Linux server environment.
- Update system software:
First, make sure all software on the server is up to date. This can be done with the following command:
sudo apt update sudo apt upgrade
The above command will check for available software updates and install them.
- Add a new user:
It is dangerous to use the root user to perform tasks on the server. In order to improve security, we should create an independent account for each user and restrict its permissions. Here are some useful commands for adding and managing users:
- Create new user:
sudo adduser username
- Grant sudo permissions:
sudo usermod -aG sudo username
- Delete existing users:
sudo deluser username
- Configure firewall:
The firewall is a key component to protect the server from malicious access. Linux servers often use iptables as a firewall tool. The following are some commonly used commands:
- Display the current firewall rules:
sudo iptables -L
- Allow specific ports through the firewall:
sudo iptables -A INPUT -p tcp --dport port_number -j ACCEPT
- Block specific IP addresses:
sudo iptables -A INPUT -s IP_address -j DROP
- Save firewall configuration:
sudo iptables-save > /etc/iptables/rules.v4 (IPv4) sudo ip6tables-save > /etc/iptables/rules.v6 (IPv6)
- Encrypt data transmission:
To protect sensitive data on the server, encryption protocols such as SSL/TLS should be used. Here are some relevant commands:
- Generate SSL certificate and private key:
sudo openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout /etc/ssl/private/key.key -out /etc/ssl/certs/cert.crt
- Configure NGINX to use SSL:
sudo nano /etc/nginx/sites-available/default 在server块中添加以下行: listen 443 ssl; ssl_certificate /etc/ssl/certs/cert.crt; ssl_certificate_key /etc/ssl/private/key.key; 保存并退出文件。重启NGINX: sudo systemctl restart nginx
- Regular backup of data:
Regular backup is an important means to restore the server system and data. The following are some backup-related commands:
- Copy files and directories:
cp -r /path/to/source /path/to/destination
- Compress files and directories:
tar -czvf archive_name.tar.gz /path/to/directory_or_file
- Delete old backups:
find /path/to/backups -mtime +7 -type f -delete
- Update and monitor logs:
Monitoring system logs is an important way to discover potential security issues. Here are some related commands:
- Update log:
sudo journalctl --vacuum-size=50M
- Monitoring log:
sudo tail -f /var/log/syslog
- View single Log file:
sudo cat /var/log/auth.log
Conclusion:
Creating a secure Linux server environment requires mastering some basic commands and techniques. This article introduces some commonly used commands, but it's just the tip of the iceberg. Further learning and mastering Linux commands and security technologies will help build a more secure and reliable server environment.
The above is the detailed content of Create a secure Linux server environment: Master these commands. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1387
1387
 52
52
 Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
When setting up the firewall, many friends found that their win11 firewall advanced settings were grayed out and unable to be clicked. This may be caused by not adding a control unit, or by not opening the advanced settings in the correct way. Let’s take a look at how to solve it. Win11 firewall advanced settings gray method one: 1. First, click the start menu below, search and open "Control Panel" at the top 2. Then open "Windows Defender Firewall" 3. After entering, you can open "Advanced Settings" in the left column . Method 2: 1. If the above method cannot be opened, you can right-click "Start Menu" and open "Run" 2. Then enter "mmc" and press Enter to confirm opening. 3. After opening, click on the upper left
 How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
On AlpineLinux, you can use the iptables tool to configure and manage firewall rules. Here are the basic steps to enable or disable the firewall on AlpineLinux: Check the firewall status: sudoiptables -L If the output shows rules (for example, there are some INPUT, OUTPUT, or FORWARD rules), the firewall is enabled. If the output is empty, the firewall is currently disabled. Enable firewall: sudoiptables-PINPUTACCEPTsudoiptables-POUTPUTACCEPTsudoiptables-PFORWARDAC
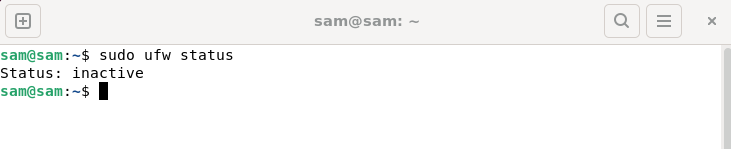 How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
UFW, also known as Uncomplex Firewall, is adopted by many Linux distributions as their firewall system. UFW is designed to make it easy for novice users to manage firewall settings through both the command line interface and the graphical user interface. A UFW firewall is a system that monitors network traffic according to set rules to protect the network from network sniffing and other attacks. If you have UFW installed on your Linux system but its status shows as inactive, there could be several reasons. In this guide, I will share how to resolve the UFW firewall inactive issue on Linux systems. Why UFW Shows Inactive Status on Linux Why UFW Is Inactive by Default on Linux How to Inactive on Linux
 How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
Many friends who use win10 system find that there is a firewall logo on the icon on the computer desktop. What is going on? This makes many friends with obsessive-compulsive disorder particularly uncomfortable. In fact, we only need to open the control panel and click " It can be solved by changing "Change User Account Control Settings". Let's take a look at the specific tutorial. How to cancel the firewall logo on the desktop icon in Windows 10 1. First, right-click the Start menu button next to the computer startup screen, and then select the Control Panel function from the pop-up menu. 2. Then select the "User Account" option and select the "Change User Account Control Settings" item from the new interface that appears. 3. After adjusting the slider in the window to the bottom, click Confirm to exit.
 How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve the problem that the Edge browser is blocked by the firewall? Edge browser is Microsoft's own browser. Some users found that this browser was blocked by the firewall during use. So what's going on? Let this site give users a detailed introduction on how to recover the Edge browser if it is blocked by the firewall. How to restore the Edge browser if it is blocked by the firewall? 1. Check the firewall settings: - Click the "Start" button on the Windows taskbar, and then open "Settings". -In the Settings window, select Update & Security. -exist
 Win11 user permissions setting tutorial: How to configure Win11 user permissions
Jan 29, 2024 pm 08:33 PM
Win11 user permissions setting tutorial: How to configure Win11 user permissions
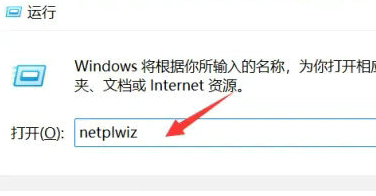
Jan 29, 2024 pm 08:33 PM
Some users will create multiple accounts when using computers, but some users' accounts do not have permissions, which means some operations cannot be performed directly? How to set user permissions in Win11? Users who are not sure can come to this site to see related strategies. How to set user permissions in Win11 1. Directly create the run function through the shortcut key combination [win+R], then enter [netplwiz] in the search box and click OK. 3. In the properties window that opens, click Group Members in the upper menu bar. 5. A window prompt will appear. Just click [Yes] to log out and restart the account to complete the settings.
 How to use PHP scripts for log monitoring in Linux systems
Oct 05, 2023 am 11:36 AM
How to use PHP scripts for log monitoring in Linux systems
Oct 05, 2023 am 11:36 AM
How to use PHP scripts for log monitoring in Linux systems. With the widespread application of Linux systems, system monitoring and log analysis have become more and more important. Among them, using PHP scripts for log monitoring is a common way. This article will introduce how to use PHP scripts to implement simple log monitoring and provide specific code examples. 1. Create a PHP script file. First, create a file named "log_monitor.php" on the Linux system. This file will be used to monitor the specified
 Fix: Recording video in Snipping Tool does not work
Sep 17, 2023 pm 08:09 PM
Fix: Recording video in Snipping Tool does not work
Sep 17, 2023 pm 08:09 PM
While the concept behind the Snipping Tool in Windows 11 is great, one of its main features, recording video, is really disappointing. The screen recording feature is still relatively new, so it can be hard to get by with glitches. Nonetheless, let's take a look at the problem and try to find a solution. So why doesn’t the screenshot tool’s video recording function work? You may not have the latest version of Windows 11 installed. The snipping tool may be corrupted or corrupted. Third-party software such as antivirus software may prevent it from recording your screen. Your computer does not have enough RAM or hard drive space to store the screen recording. Viruses or malware on your computer interfere with the way programs work. How to get Snipping Tool to record my screen in Windows 11



