 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Building secure remote access: Protect your Linux servers
Building secure remote access: Protect your Linux servers
Building secure remote access: Protect your Linux servers
Building Secure Remote Access: Protecting Your Linux Server
With the development of the Internet, remote access has become a common way to manage servers. However, remote access also exposes servers to a variety of potential security threats. To protect your Linux server from hackers, this article will cover some basic security measures and code examples.
- Use SSH key authentication
SSH (Secure Shell) is an encrypted remote login protocol that can securely connect to a server remotely. Compared with the traditional username/password login method, SSH key authentication is more secure. Here is sample code for generating and using SSH keys:
# 生成SSH密钥 ssh-keygen -t rsa -b 4096 # 将公钥复制到服务器 ssh-copy-id username@servername # 禁用密码登录 sudo nano /etc/ssh/sshd_config 将 PasswordAuthentication 设置为 no
- Using a firewall
A firewall can help filter and block unauthorized connections. Access to specific ports and IP addresses can be restricted by setting appropriate rules. The following is sample code for setting up firewall rules using iptables:
# 允许所有本地连接 iptables -A INPUT -i lo -j ACCEPT # 允许已建立的连接 iptables -A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT # 允许SSH连接 iptables -A INPUT -p tcp --dport 22 -j ACCEPT # 其他所有连接均拒绝 iptables -A INPUT -j DROP # 保存规则并启用防火墙 iptables-save > /etc/iptables.rules
- Update your system and software regularly
It is important to keep your system and software up to date, as updates often contain security patches. Regularly updating systems and software can reduce the risk of being exploited by known vulnerabilities. The following is sample code for using apt-get to update systems and software:
# 更新软件包列表 sudo apt-get update # 执行系统更新 sudo apt-get upgrade # 定期执行更新任务 sudo crontab -e 添加以下行,每周自动执行更新: 0 0 * * 0 apt-get update && apt-get upgrade -y
- Using non-standard ports
The default SSH port is 22, which is the port most commonly attempted by hackers one. By using a non-standard port (such as 2222) instead of the default port, the risk of being scanned and attacked can be reduced to a certain extent. The following is sample code to modify the SSH port:
# 编辑SSH配置文件 sudo nano /etc/ssh/sshd_config # 将端口号修改为非默认端口 将 Port 22 改为 Port 2222 # 重启SSH服务 sudo service ssh restart
- Configuring the Intrusion Detection System
An intrusion detection system (IDS) can monitor network traffic and system activity on the server and warn you about Suspicious or malicious activity. The following is sample code for configuring an IDS using Snort:
# 安装Snort sudo apt-get install snort # 配置网络接口 sudo ifconfig eth0 promisc # 启动Snort sudo snort -i eth0 -c /etc/snort/snort.conf
When configuring remote access, keep the security of the server in mind. Properly setting access permissions, using strong passwords, regularly backing up data, and monitoring server health are all important security practices.
Summary:
This article introduces some basic measures and code examples to protect the security of remote access to Linux servers. Measures such as using SSH key authentication, setting firewall rules, regularly updating systems and software, using non-standard ports, and configuring intrusion detection systems can effectively reduce the risk of server attacks. In practical applications, it can be appropriately adjusted and improved according to specific needs. By building a secure remote access environment, you can better protect your Linux server from hackers.
The above is the detailed content of Building secure remote access: Protect your Linux servers. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1376
1376
 52
52
 Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
When setting up the firewall, many friends found that their win11 firewall advanced settings were grayed out and unable to be clicked. This may be caused by not adding a control unit, or by not opening the advanced settings in the correct way. Let’s take a look at how to solve it. Win11 firewall advanced settings gray method one: 1. First, click the start menu below, search and open "Control Panel" at the top 2. Then open "Windows Defender Firewall" 3. After entering, you can open "Advanced Settings" in the left column . Method 2: 1. If the above method cannot be opened, you can right-click "Start Menu" and open "Run" 2. Then enter "mmc" and press Enter to confirm opening. 3. After opening, click on the upper left
 How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
On AlpineLinux, you can use the iptables tool to configure and manage firewall rules. Here are the basic steps to enable or disable the firewall on AlpineLinux: Check the firewall status: sudoiptables -L If the output shows rules (for example, there are some INPUT, OUTPUT, or FORWARD rules), the firewall is enabled. If the output is empty, the firewall is currently disabled. Enable firewall: sudoiptables-PINPUTACCEPTsudoiptables-POUTPUTACCEPTsudoiptables-PFORWARDAC
 How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
Many friends who use win10 system find that there is a firewall logo on the icon on the computer desktop. What is going on? This makes many friends with obsessive-compulsive disorder particularly uncomfortable. In fact, we only need to open the control panel and click " It can be solved by changing "Change User Account Control Settings". Let's take a look at the specific tutorial. How to cancel the firewall logo on the desktop icon in Windows 10 1. First, right-click the Start menu button next to the computer startup screen, and then select the Control Panel function from the pop-up menu. 2. Then select the "User Account" option and select the "Change User Account Control Settings" item from the new interface that appears. 3. After adjusting the slider in the window to the bottom, click Confirm to exit.
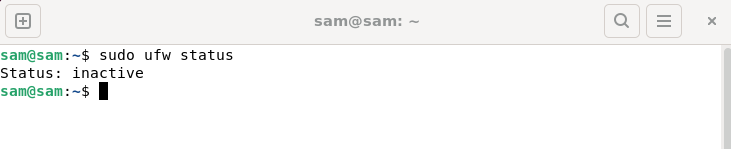 How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
UFW, also known as Uncomplex Firewall, is adopted by many Linux distributions as their firewall system. UFW is designed to make it easy for novice users to manage firewall settings through both the command line interface and the graphical user interface. A UFW firewall is a system that monitors network traffic according to set rules to protect the network from network sniffing and other attacks. If you have UFW installed on your Linux system but its status shows as inactive, there could be several reasons. In this guide, I will share how to resolve the UFW firewall inactive issue on Linux systems. Why UFW Shows Inactive Status on Linux Why UFW Is Inactive by Default on Linux How to Inactive on Linux
 Analysis of Python's underlying technology: How to implement SSL/TLS encrypted communication
Nov 08, 2023 pm 03:14 PM
Analysis of Python's underlying technology: How to implement SSL/TLS encrypted communication
Nov 08, 2023 pm 03:14 PM
Analysis of Python's underlying technology: How to implement SSL/TLS encrypted communication, specific code examples are required. SSL (SecureSocketsLayer) and TLS (TransportLayerSecurity) are protocols used to achieve secure communication on computer networks. During network communication, SSL/TLS can provide functions such as encryption, authentication, and data integrity protection to ensure that data will not be eavesdropped, tampered with, or forged during transmission. Python
 OpenSSH on Windows: Installation, Configuration, and Usage Guide
Mar 08, 2024 am 09:31 AM
OpenSSH on Windows: Installation, Configuration, and Usage Guide
Mar 08, 2024 am 09:31 AM
For most Windows users, Remote Desktop Protocol (RDP) has always been the first choice for remote management because it provides a friendly graphical interface. However, for system administrators who require more granular control, SSH may better suit their needs. Through SSH, administrators can interact with remote devices through the command line, which can make management work more efficient. The advantage of SSH is its security and flexibility, making it easier for administrators to perform remote management and maintenance work, especially when dealing with a large number of devices or performing automated tasks. So while RDP excels in terms of user-friendliness, for system administrators, SSH is superior in terms of power and control. Previously, Windows users needed to borrow
 A deep dive into the definition and characteristics of HTTP status code 525
Feb 19, 2024 am 09:28 AM
A deep dive into the definition and characteristics of HTTP status code 525
Feb 19, 2024 am 09:28 AM
An in-depth analysis of the meaning and characteristics of HTTP status code 525. HTTP status code is an identification code used in the HTTP protocol to indicate whether a request is successful, failed, and the cause of various errors. Among them, status code 525 is a new status code in the HTTP/2 protocol, which indicates that the SSL handshake failed. In a normal HTTPS connection, an SSL handshake process is required between the client (browser) and the server to ensure the security of communication. The SSL handshake includes the client sending ClientHello and the server responding S
 How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve the problem that the Edge browser is blocked by the firewall? Edge browser is Microsoft's own browser. Some users found that this browser was blocked by the firewall during use. So what's going on? Let this site give users a detailed introduction on how to recover the Edge browser if it is blocked by the firewall. How to restore the Edge browser if it is blocked by the firewall? 1. Check the firewall settings: - Click the "Start" button on the Windows taskbar, and then open "Settings". -In the Settings window, select Update & Security. -exist



