 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 User authentication and authorization -- realizing secure user login and permission management
User authentication and authorization -- realizing secure user login and permission management
User authentication and authorization -- realizing secure user login and permission management
User authentication and authorization -- realizing secure user login and permission management
In modern Internet applications, user authentication and authorization are very important functions. User authentication is used to verify the user's identity and ensure that only legitimate users can access system resources. Authorization is to determine which resources a user can access and perform.
This article will introduce how to implement secure user login and permission management functions through code examples.
- User Authentication
User authentication is usually performed using username and password. The following is a simple sample code:
def authenticate(username, password):
# 查询数据库,根据用户名查找用户信息
user = get_user_by_username(username)
if user is None:
return None
# 校验密码是否匹配
if validate_password(password, user.password):
return user
return NoneIn the above code, the get_user_by_username function is used to query user information based on the user name, and the validate_password function is used to verify whether the password matches. . If the username and password are verified successfully, the user authentication is successful, otherwise None is returned.
- User Authorization
After a user successfully logs in, the system needs to determine which resources the user can access and which operations they can perform based on the user's role and permissions. The following is a simple sample code:
def authorize(user, resource):
# 查询数据库,获取用户角色和权限
role = get_role_by_user(user)
if role is None:
return False
# 判断用户是否有权限访问该资源
permissions = get_permissions_by_role(role)
return check_permission(resource, permissions)In the above code, the get_role_by_user function is used to obtain the role to which the user belongs based on the user, and the get_permissions_by_role function is used to obtain the role based on the role. List of permissions for the role. check_permissionThe function is used to determine whether the user has permission to access a resource.
- Security considerations
In the process of implementing user authentication and authorization, security needs to be considered. Here are some security considerations:
- Password storage: User passwords should be stored in a secure manner, usually using an encryption algorithm.
- Password transmission: User passwords should be encrypted and transmitted using a secure protocol (such as HTTPS) during the transmission process to avoid password interception and leakage.
- Prevent brute force cracking: In order to prevent brute force cracking, you can protect it by limiting the number of logins, using verification codes, and increasing login delays.
- Permission control: Fine-grained permission control of system resources is required to ensure that users can only access their authorized resources.
- Audit log: Record user login and operation logs to facilitate future auditing and tracking.
To sum up, user authentication and authorization are important components to ensure the security of application systems. By properly implementing user authentication and authorization functions, the security of application systems can be improved to a certain extent.
Appendix: Function description in the sample code
- get_user_by_username: Function to obtain user information based on user name.
- validate_password: Function to verify whether the password matches.
- get_role_by_user: Function to get the role of the user based on the user.
- get_permissions_by_role: Function to get the role permission list based on the role.
- check_permission: Function to determine whether the user has permission to access a resource.
The above is the detailed content of User authentication and authorization -- realizing secure user login and permission management. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to use the Layui framework to develop a permission management system that supports multi-user login
Oct 27, 2023 pm 01:27 PM
How to use the Layui framework to develop a permission management system that supports multi-user login
Oct 27, 2023 pm 01:27 PM
How to use the Layui framework to develop a permission management system that supports multi-user login Introduction: In the modern Internet era, more and more applications need to support multi-user login to achieve personalized functions and permission management. In order to protect the security of the system and the privacy of data, developers need to use certain means to implement multi-user login and permission management functions. This article will introduce how to use the Layui framework to develop a permission management system that supports multi-user login, and give specific code examples. Preparation before starting development
 How to implement data sharing and permission management in React Query?
Sep 27, 2023 pm 04:13 PM
How to implement data sharing and permission management in React Query?
Sep 27, 2023 pm 04:13 PM
How to implement data sharing and permission management in ReactQuery? Advances in technology have made data management in front-end development more complex. In the traditional way, we may use state management tools such as Redux or Mobx to handle data sharing and permission management. However, after the emergence of ReactQuery, we can use it to deal with these problems more conveniently. In this article, we will explain how to implement data sharing and permissions in ReactQuery
 PHP development skills: How to implement user login restriction function
Sep 21, 2023 am 11:39 AM
PHP development skills: How to implement user login restriction function
Sep 21, 2023 am 11:39 AM
PHP development skills: How to implement user login restriction function In website or application development, user login restriction function is a very important security measure. By limiting the number of login attempts and frequency of users, you can effectively prevent accounts from being maliciously cracked or brute force cracked. This article will introduce how to use PHP to implement user login restriction function and provide specific code examples. 1. Requirements analysis of user login restriction function User login restriction function usually includes the following requirements: Limitation on the number of login attempts: when the user continuously inputs errors
 How to implement a permission management system in Laravel
Nov 02, 2023 pm 04:51 PM
How to implement a permission management system in Laravel
Nov 02, 2023 pm 04:51 PM
How to implement a permission management system in Laravel Introduction: With the continuous development of web applications, the permission management system has become one of the basic functions of many applications. Laravel, as a popular PHP framework, provides a wealth of tools and functions to implement permission management systems. This article will introduce how to implement a simple and powerful permission management system in Laravel and provide specific code examples. 1. Design ideas of the permission management system When designing the permission management system, the following key points need to be considered: roles and
 How to handle user rights management in PHP forms
Aug 10, 2023 pm 01:06 PM
How to handle user rights management in PHP forms
Aug 10, 2023 pm 01:06 PM
How to handle user rights management in PHP forms With the continuous development of web applications, user rights management is one of the important functions. User rights management can control users' operating rights in applications and ensure the security and legality of data. In PHP forms, user rights management can be implemented through some simple code. This article will introduce how to handle user rights management in PHP forms and give corresponding code examples. 1. Definition and management of user roles First of all, defining and managing user roles is a matter of user rights.
 How to send SMS verification code and email notification when user logs in in PHP
Sep 26, 2023 pm 08:40 PM
How to send SMS verification code and email notification when user logs in in PHP
Sep 26, 2023 pm 08:40 PM
How to send SMS verification codes and email notifications when users log in in PHP. With the rapid development of the Internet, more and more applications require user login functions to ensure security and personalized experience. In addition to basic account and password verification, in order to improve user experience and security, many applications will also send mobile phone SMS verification codes and email notifications when users log in. This article will describe how to implement this functionality in PHP and provide corresponding code examples. 1. Send SMS verification code 1. First, you need someone who can send SMS
 How to build a user login and permission management system using Elasticsearch and PHP
Jul 08, 2023 pm 04:15 PM
How to build a user login and permission management system using Elasticsearch and PHP
Jul 08, 2023 pm 04:15 PM
How to use Elasticsearch and PHP to build a user login and permission management system Introduction: In the current Internet era, user login and permission management are one of the necessary functions for every website or application. Elasticsearch is a powerful and flexible full-text search engine, while PHP is a widely used server-side scripting language. This article will introduce how to combine Elasticsearch and PHP to build a simple user login and permission management system
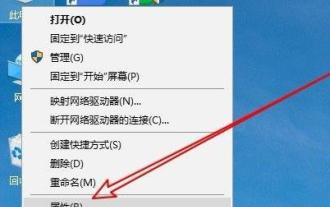 Solve the problem that the temporary folder cannot be installed due to lack of write permissions
Dec 31, 2023 pm 01:24 PM
Solve the problem that the temporary folder cannot be installed due to lack of write permissions
Dec 31, 2023 pm 01:24 PM
The problem that temporary folders cannot be installed without write permissions is a headache for many users. In fact, the operation is not very troublesome. You only need to enter your advanced menu to make changes. Let’s see how to solve the problem of no write permissions. The temporary folder cannot be installed without write permission: 1. First, right-click This Computer on the desktop, and then click "Properties". 2. Then click "Advanced System Settings" below. 3. Then click "Environment Variables" at the bottom of the window. 4. After that, you can open the environment variables window, click on the tmp file and select "Edit". 5. Then click "Browse Files" in the window that opens. 6. Set the new variable folder and click OK. 7. Finally wait until success.





