 Operation and Maintenance
Operation and Maintenance
 Linux Operation and Maintenance
Linux Operation and Maintenance
 Understand Web interface authentication and permission management on Linux servers.
Understand Web interface authentication and permission management on Linux servers.
Understand Web interface authentication and permission management on Linux servers.
Understand Web interface authentication and permission management on Linux servers
With the rapid development of the Internet, Web applications are becoming more and more popular in enterprises and personal use common. In order to protect the security and confidentiality of web applications, authentication and permission management have become very important. On a Linux server, implementing Web interface authentication and permission management is a key task. This article will introduce how to perform Web interface authentication and permission management on Linux servers, helping you build safe and reliable Web applications.
1. Authentication
Authentication is the process of confirming the user’s identity. In web applications, commonly used authentication methods include basic authentication and digest authentication.
- Basic Authentication
Basic authentication is the simplest authentication method. Its principle is to send the user name and password in the request header in each HTTP request. Clear text to verify user identity. The advantage of this method is that it is simple and easy to understand, but the disadvantage is that the plain text of user information transmission is easily eavesdropped, which poses security risks.
To implement basic authentication on a Linux server, you can use Apache's htpasswd tool. Use the htpasswd tool to create a password file that can store usernames and encrypted passwords. Then, in Apache's configuration file, use the "AuthType", "AuthName", "AuthUserFile" and "Require valid-user" directives to configure basic authentication. This way, every request needs to be authenticated by entering the correct username and password.
- Digest Authentication
Digest authentication is a more secure authentication method than basic authentication. The principle is to use a hash algorithm to calculate a digest value in each HTTP request, which is used to verify the user's identity. In this way, the username and password will not be sent in clear text during transmission, which improves security.
To implement digest authentication on a Linux server, you can use Apache's mod_auth_digest module. By configuring the directives of the mod_auth_digest module, you can define a password file and specify the type of digest algorithm. Then, in the Apache configuration file, use the "AuthType", "AuthName", "AuthDigestDomain", "AuthDigestProvider" and "Require valid-user" directives to configure digest authentication.
2. Permission management
Permission management is to restrict users’ access to functions and resources to protect the security of web applications. On a Linux server, you can use the following methods to implement permission management.
- File system permissions
The file system of the Linux server has a rich permission control mechanism. By setting permissions on files and directories, you can control user access to the file system. For example, use the "chmod" command to set read, write, and execute permissions on files and directories.
In web applications, for different user types, you can create different user groups and set corresponding file system permissions. In this way, users can only access files and directories that they have permission to access, which enhances security.
- Access Control List (ACL)
Access control list is a more refined permission control mechanism in Linux servers. Through ACL, different permissions can be set on specific files and directories. Compared with file system permissions, ACL can set more fine-grained access permissions for users and user groups.
On a Linux server, use the "setfacl" command to set the ACL of files and directories. By specifying users or user groups and corresponding permissions, you can restrict access to specific users or user groups.
- RBAC
RBAC (Role-Based Access Control) is a role-based access control mechanism. In the RBAC model, user permissions are defined as different roles rather than directly related to specific users. Then, assign roles to users to control user permissions.
On Linux servers, you can use PAM (Pluggable Authentication Modules) to implement RBAC. PAM is a flexible authentication module that can integrate different authentication mechanisms. By configuring PAM, you can define different roles and corresponding permissions, and assign these roles to different users.
Summary
Web interface authentication and permission management are key tasks to protect the security of Web applications. On Linux servers, basic authentication and digest authentication are commonly used authentication methods, which can be implemented by configuring the relevant instructions of Apache. In terms of permission management, user access control can be restricted through file system permissions, ACL, and RBAC. By properly configuring authentication and permission management, you can build safe and reliable web applications to protect user privacy and data security.
The above is the detailed content of Understand Web interface authentication and permission management on Linux servers.. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to use PHP scripts to implement cross-server file transfer on Linux servers
Oct 05, 2023 am 09:06 AM
How to use PHP scripts to implement cross-server file transfer on Linux servers
Oct 05, 2023 am 09:06 AM
Title: PHP script implementation of cross-server file transfer 1. Introduction In cross-server file transfer, we usually need to transfer files from one server to another. This article will introduce how to use PHP scripts to implement cross-server file transfer on Linux servers, and give specific code examples. 2. Preparation Before starting to write PHP scripts, we need to ensure that the following environment has been configured on the server: Install PHP: Install PHP on the Linux server and ensure that the PHP version meets the code requirements.
 How to use the Layui framework to develop a permission management system that supports multi-user login
Oct 27, 2023 pm 01:27 PM
How to use the Layui framework to develop a permission management system that supports multi-user login
Oct 27, 2023 pm 01:27 PM
How to use the Layui framework to develop a permission management system that supports multi-user login Introduction: In the modern Internet era, more and more applications need to support multi-user login to achieve personalized functions and permission management. In order to protect the security of the system and the privacy of data, developers need to use certain means to implement multi-user login and permission management functions. This article will introduce how to use the Layui framework to develop a permission management system that supports multi-user login, and give specific code examples. Preparation before starting development
 How to implement data sharing and permission management in React Query?
Sep 27, 2023 pm 04:13 PM
How to implement data sharing and permission management in React Query?
Sep 27, 2023 pm 04:13 PM
How to implement data sharing and permission management in ReactQuery? Advances in technology have made data management in front-end development more complex. In the traditional way, we may use state management tools such as Redux or Mobx to handle data sharing and permission management. However, after the emergence of ReactQuery, we can use it to deal with these problems more conveniently. In this article, we will explain how to implement data sharing and permissions in ReactQuery
 How to implement a permission management system in Laravel
Nov 02, 2023 pm 04:51 PM
How to implement a permission management system in Laravel
Nov 02, 2023 pm 04:51 PM
How to implement a permission management system in Laravel Introduction: With the continuous development of web applications, the permission management system has become one of the basic functions of many applications. Laravel, as a popular PHP framework, provides a wealth of tools and functions to implement permission management systems. This article will introduce how to implement a simple and powerful permission management system in Laravel and provide specific code examples. 1. Design ideas of the permission management system When designing the permission management system, the following key points need to be considered: roles and
 What are the differences between WeChat official account certification and non-certification?
Sep 19, 2023 pm 02:15 PM
What are the differences between WeChat official account certification and non-certification?
Sep 19, 2023 pm 02:15 PM
The difference between WeChat public account authentication and non-authentication lies in the authentication logo, function permissions, push frequency, interface permissions and user trust. Detailed introduction: 1. Certification logo. Certified public accounts will obtain the official certification logo, which is the blue V logo. This logo can increase the credibility and authority of the public account and make it easier for users to identify the real official public account; 2. Function permissions. Certified public accounts have more functions and permissions than uncertified public accounts. For example, certified public accounts can apply to activate the WeChat payment function to achieve online payment and commercial operations, etc.
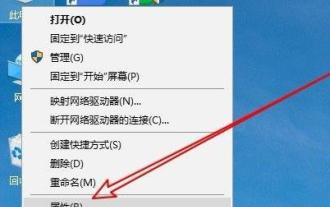 Solve the problem that the temporary folder cannot be installed due to lack of write permissions
Dec 31, 2023 pm 01:24 PM
Solve the problem that the temporary folder cannot be installed due to lack of write permissions
Dec 31, 2023 pm 01:24 PM
The problem that temporary folders cannot be installed without write permissions is a headache for many users. In fact, the operation is not very troublesome. You only need to enter your advanced menu to make changes. Let’s see how to solve the problem of no write permissions. The temporary folder cannot be installed without write permission: 1. First, right-click This Computer on the desktop, and then click "Properties". 2. Then click "Advanced System Settings" below. 3. Then click "Environment Variables" at the bottom of the window. 4. After that, you can open the environment variables window, click on the tmp file and select "Edit". 5. Then click "Browse Files" in the window that opens. 6. Set the new variable folder and click OK. 7. Finally wait until success.
 GitLab permission management and single sign-on integration tips
Oct 21, 2023 am 11:15 AM
GitLab permission management and single sign-on integration tips
Oct 21, 2023 am 11:15 AM
GitLab's permission management and single sign-on integration tips require specific code examples Overview: In GitLab, permission management and single sign-on (SSO) are very important functions. Permission management can control users' access to code repositories, projects, and other resources, while single sign-on integration can provide a more convenient user authentication and authorization method. This article will introduce how to perform permission management and single sign-on integration in GitLab. 1. Permission Management Project Access Permission Control In GitLab, projects can be set to private
 How to optimize the performance and resource utilization of Linux servers
Nov 07, 2023 pm 02:27 PM
How to optimize the performance and resource utilization of Linux servers
Nov 07, 2023 pm 02:27 PM
How to optimize the performance and resource utilization of Linux servers requires specific code examples. Summary: Optimizing Linux server performance and resource utilization is the key to ensuring stable and efficient server operation. This article will introduce some methods to optimize Linux server performance and resource utilization, and provide specific code examples. Introduction: With the rapid development of the Internet, a large number of applications and services are deployed on Linux servers. In order to ensure the efficient and stable operation of the server, we need to optimize the performance and resource utilization of the server to achieve





