 Backend Development
Backend Development
 PHP Tutorial
PHP Tutorial
 How to handle hashing and encryption functions in accounting systems - Development methods for hashing and encryption using PHP
How to handle hashing and encryption functions in accounting systems - Development methods for hashing and encryption using PHP
How to handle hashing and encryption functions in accounting systems - Development methods for hashing and encryption using PHP
How to handle hashing and encryption functions in accounting systems - Development methods for hashing and encryption using PHP
Introduction:
With the digital age With the advent of the Internet, the security of various information systems has become more and more important. When designing and developing accounting systems, protecting user privacy data is crucial. Among them, the use of hashing and encryption functions can effectively protect users' sensitive information. This article will introduce how to use PHP to implement hashing and encryption functions in accounting systems, and provide specific code examples.
1. Implementation of hash function
Hash is a one-way encryption algorithm that maps data of any length into a fixed-length hash value. In accounting systems, hashes are often used to store user passwords. The following is the development method of using PHP to implement the hash function:
- Using the hash algorithm library
PHP provides a variety of hash algorithm libraries, such as md5, sha1, sha256, etc. Using these libraries, you can call the corresponding functions in your code to perform hash operations. The following is a sample code that uses the md5 algorithm to hash a password:
$password = "123456"; $hashedPassword = md5($password);
- Add salt value
In order to increase the security of the password, we can add a salt value during the hashing process salt value. The salt is a random string that is hashed together with the user's password. This way even if the user's password is the same, the hash value will be different due to the different salt value. Here is a sample code for adding a salt value:
$password = "123456"; $salt = "sdfioej29ghf03"; $hashedPassword = md5($password.$salt);
- Storing the hash value
After hashing the user's password, we store the hash value in the database. On subsequent verification of the user's login request, the password entered by the user is compared to the stored hash value. The following is a sample code to verify user login:
$password = $_POST['password'];
$hashedPassword = getPasswordFromDatabase(); // 从数据库中获取存储的哈希值
if(md5($password) == $hashedPassword){
// 验证通过
}else{
// 验证失败
}2. Implementation of encryption function
Compared with hashing, encryption is a two-way operation that can encrypt and encrypt data through a key. Decrypt. In accounting systems, encryption is often used to protect the transmission and storage of sensitive data. The following is the development method for using PHP to implement encryption functions:
- Using encryption algorithm libraries
PHP provides a variety of encryption algorithm libraries, such as AES, DES, RSA, etc. Using these libraries, you can call the corresponding functions in your code to perform encryption and decryption operations. The following is a sample code that uses the AES algorithm to encrypt and decrypt data:
$data = "敏感数据"; $encryptionKey = "sdfioej29ghf03"; $encryptedData = openssl_encrypt($data, "AES-128-CBC", $encryptionKey); $decryptedData = openssl_decrypt($encryptedData, "AES-128-CBC", $encryptionKey);
- Storing encrypted data
After encrypting the user's sensitive data, we will Stored in database. When the data needs to be used, the encrypted data is decrypted and used. The following is a sample code that stores and uses encrypted data:
$data = "敏感数据"; $encryptionKey = "sdfioej29ghf03"; $encryptedData = openssl_encrypt($data, "AES-128-CBC", $encryptionKey); saveEncryptedDataToDatabase($encryptedData); $encryptedDataFromDatabase = getEncryptedDataFromDatabase(); $decryptedData = openssl_decrypt($encryptedDataFromDatabase, "AES-128-CBC", $encryptionKey);
Summary:
When designing and developing accounting systems, it is very important to protect user privacy data, where hashing and encryption Features are one of the common means of protecting user data. This article describes how to use PHP to implement hashing and encryption functions in accounting systems, and provides specific code examples. I hope this article will be helpful to you when developing your accounting system.
The above is the detailed content of How to handle hashing and encryption functions in accounting systems - Development methods for hashing and encryption using PHP. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1389
1389
 52
52
 PHP format rows to CSV and write file pointer
Mar 22, 2024 am 09:00 AM
PHP format rows to CSV and write file pointer
Mar 22, 2024 am 09:00 AM
This article will explain in detail how PHP formats rows into CSV and writes file pointers. I think it is quite practical, so I share it with you as a reference. I hope you can gain something after reading this article. Format rows to CSV and write to file pointer Step 1: Open file pointer $file=fopen("path/to/file.csv","w"); Step 2: Convert rows to CSV string using fputcsv( ) function converts rows to CSV strings. The function accepts the following parameters: $file: file pointer $fields: CSV fields as an array $delimiter: field delimiter (optional) $enclosure: field quotes (
 PHP changes current umask
Mar 22, 2024 am 08:41 AM
PHP changes current umask
Mar 22, 2024 am 08:41 AM
This article will explain in detail about changing the current umask in PHP. The editor thinks it is quite practical, so I share it with you as a reference. I hope you can gain something after reading this article. Overview of PHP changing current umask umask is a php function used to set the default file permissions for newly created files and directories. It accepts one argument, which is an octal number representing the permission to block. For example, to prevent write permission on newly created files, you would use 002. Methods of changing umask There are two ways to change the current umask in PHP: Using the umask() function: The umask() function directly changes the current umask. Its syntax is: intumas
 PHP calculates MD5 hash of file
Mar 21, 2024 pm 01:42 PM
PHP calculates MD5 hash of file
Mar 21, 2024 pm 01:42 PM
This article will explain in detail about PHP calculating the MD5 hash of files. The editor thinks it is quite practical, so I share it with you as a reference. I hope you can gain something after reading this article. PHP calculates the MD5 hash of a file MD5 (MessageDigest5) is a one-way encryption algorithm that converts messages of arbitrary length into a fixed-length 128-bit hash value. It is widely used to ensure file integrity, verify data authenticity and create digital signatures. Calculating the MD5 hash of a file in PHP PHP provides multiple methods to calculate the MD5 hash of a file: Use the md5_file() function. The md5_file() function directly calculates the MD5 hash value of the file and returns a 32-character
 PHP returns an array with key values flipped
Mar 21, 2024 pm 02:10 PM
PHP returns an array with key values flipped
Mar 21, 2024 pm 02:10 PM
This article will explain in detail how PHP returns an array after key value flipping. The editor thinks it is quite practical, so I share it with you as a reference. I hope you can gain something after reading this article. PHP Key Value Flip Array Key value flip is an operation on an array that swaps the keys and values in the array to generate a new array with the original key as the value and the original value as the key. Implementation method In PHP, you can perform key-value flipping of an array through the following methods: array_flip() function: The array_flip() function is specially used for key-value flipping operations. It receives an array as argument and returns a new array with the keys and values swapped. $original_array=[
 PHP truncate file to given length
Mar 21, 2024 am 11:42 AM
PHP truncate file to given length
Mar 21, 2024 am 11:42 AM
This article will explain in detail how PHP truncates files to a given length. The editor thinks it is quite practical, so I share it with you as a reference. I hope you can gain something after reading this article. Introduction to PHP file truncation The file_put_contents() function in PHP can be used to truncate files to a specified length. Truncation means removing part of the end of a file, thereby shortening the file length. Syntax file_put_contents($filename,$data,SEEK_SET,$offset);$filename: the file path to be truncated. $data: Empty string to be written to the file. SEEK_SET: designated as the beginning of the file
 PHP determines whether a specified key exists in an array
Mar 21, 2024 pm 09:21 PM
PHP determines whether a specified key exists in an array
Mar 21, 2024 pm 09:21 PM
This article will explain in detail how PHP determines whether a specified key exists in an array. The editor thinks it is very practical, so I share it with you as a reference. I hope you can gain something after reading this article. PHP determines whether a specified key exists in an array: In PHP, there are many ways to determine whether a specified key exists in an array: 1. Use the isset() function: isset($array["key"]) This function returns a Boolean value, true if the specified key exists, false otherwise. 2. Use array_key_exists() function: array_key_exists("key",$arr
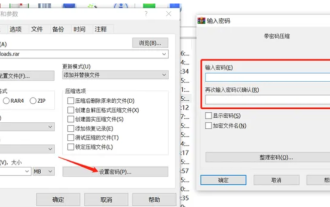 How to encrypt the compressed package in winrar-winrar encrypted compressed package method
Mar 23, 2024 pm 12:10 PM
How to encrypt the compressed package in winrar-winrar encrypted compressed package method
Mar 23, 2024 pm 12:10 PM
The editor will introduce to you three methods of encryption and compression: Method 1: Encryption The simplest encryption method is to enter the password you want to set when encrypting the file, and the encryption and compression are completed. Method 2: Automatic encryption Ordinary encryption method requires us to enter a password when encrypting each file. If you want to encrypt a large number of compressed packages and the passwords are the same, then we can set automatic encryption in WinRAR, and then just When compressing files normally, WinRAR will add a password to each compressed package. The method is as follows: Open WinRAR, click Options-Settings in the setting interface, switch to [Compression], click Create Default Configuration-Set Password Enter the password we want to set here, click OK to complete the setting, we only need to correct
 PHP returns the numeric encoding of the error message in the previous MySQL operation
Mar 22, 2024 pm 12:31 PM
PHP returns the numeric encoding of the error message in the previous MySQL operation
Mar 22, 2024 pm 12:31 PM
This article will explain in detail the numerical encoding of the error message returned by PHP in the previous Mysql operation. The editor thinks it is quite practical, so I share it with you as a reference. I hope you can gain something after reading this article. . Using PHP to return MySQL error information Numeric Encoding Introduction When processing mysql queries, you may encounter errors. In order to handle these errors effectively, it is crucial to understand the numerical encoding of error messages. This article will guide you to use php to obtain the numerical encoding of Mysql error messages. Method of obtaining the numerical encoding of error information 1. mysqli_errno() The mysqli_errno() function returns the most recent error number of the current MySQL connection. The syntax is as follows: $erro



