 Technology peripherals
Technology peripherals
 AI
AI
 Paper QR codes can also be tampered with in the air: a traceless attack from a hundred meters away can instantly turn them into a malicious website entrance
Paper QR codes can also be tampered with in the air: a traceless attack from a hundred meters away can instantly turn them into a malicious website entrance
Paper QR codes can also be tampered with in the air: a traceless attack from a hundred meters away can instantly turn them into a malicious website entrance
Now, the printed paper QR code may not be safe!
Through laser irradiation, an attacker can tamper in minutes from one hundred meters away. What’s even more frightening is that this kind of laser is completely invisible to the naked eye
. A normal QR code may inadvertently become the entrance to a malicious website. .
Recently, researchers from Tokai University in Japan developed a long-range, ultra-covert QR code tampering method.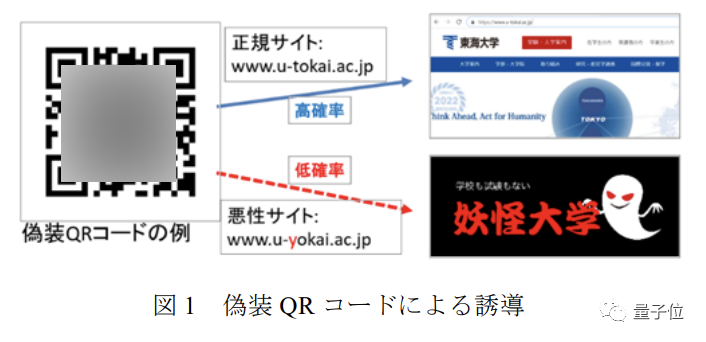 The QR code after the attack is not only invisible during the attack, but even with the naked eye, it is no different from the normal one.
The QR code after the attack is not only invisible during the attack, but even with the naked eye, it is no different from the normal one.
Such an attack is for ordinary users and devices. Almost impossible to prevent
So, how do scientific researchers "sneak the chance to change the situation" without attracting attention?
Laser irradiation changes the "color" of the information point
To explain this problem, we need to first understand the basic principles of QR code scanning
(in this article "QR code" refers to our most common QR type QR code)Usually the QR code we see consists of anchor point, format and mask information area, information area and correction area Error area compositionThe 2 (size) M (error correction level) type QR code in the figure below is an example. It consists of 25×25 grid points, of which 7× in the upper left, lower left, and lower right Area 7 is the anchor point.
D1~D28 and E1~E16 in the figure represent data and error correction fields respectively, while the blue area is the area for format and mask information
The data field is first grouped by the original text, and then converted into a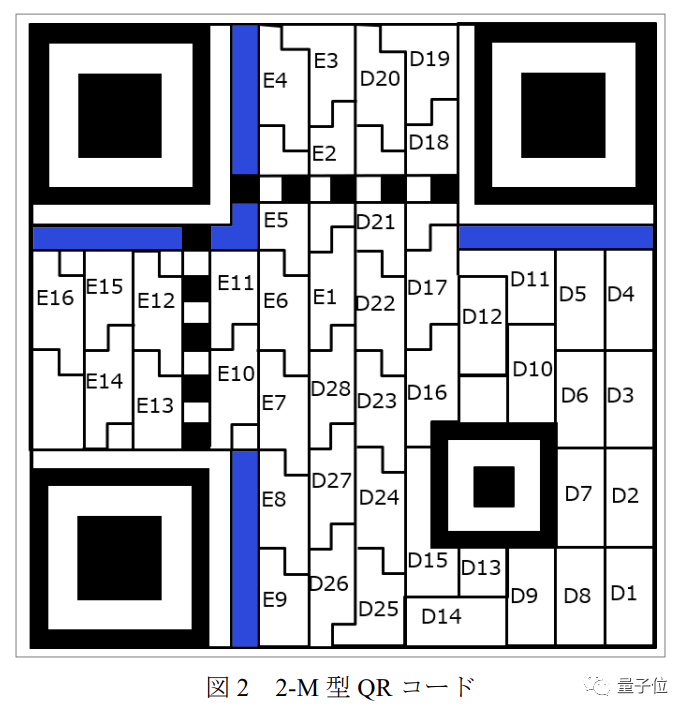 binary string
binary string
using a certain processing method, which is black in the QR code and white represent 1 and 0 respectively. Error correction field, as the name suggests, is designed to avoid errors during the generation and scanning process. It is composed of data fields based on the Reed-Solomon algorithmGeneration, the length also differs according to the error correction level.
The format and mask information area stores the encoding method of the QR code (from plain text to binary string) and the mask operation The mask is to avoid certain patterns that affect the scanning results. , the transformation operation is performed on the original lattice according to certain rules, and the operation method is stored in the mask information area.
The reading process is to first
capture the positioning point
, then correct and reduce noise on the image, and thendetermine the format and mask The location of the area and read it to learn the way of decoding the data field. In this experiment, the researcher constructed a hybrid intermediate between two QR codes by gradually covering the QR code information
.
This intermediate contains a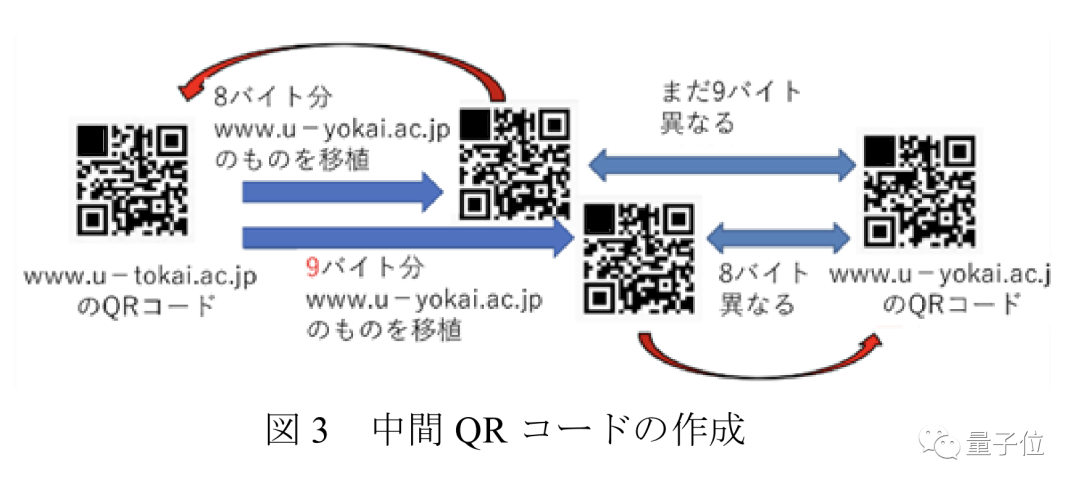 key color block
key color block
, its color determines the actual two-dimensional image that is read Which code is it?
Scientists can irradiate this color block with a laser invisible to the naked eye to determine the recognition result of the camera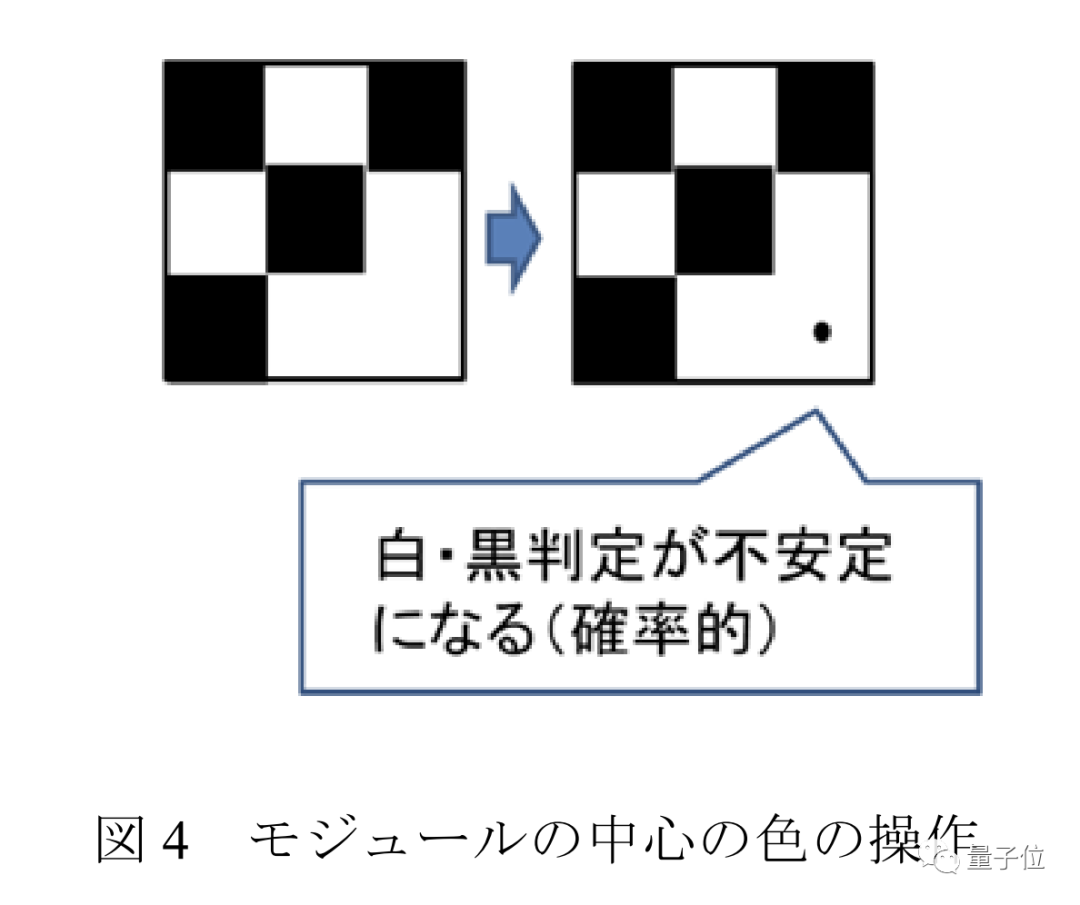 After irradiation, although
After irradiation, although
The difference is not visible to the naked eye, but from the perspective of the camera, the originally black module will be recognized as white
.
The following figure compares the range of wavelengths that the human eye and the camera can recognize: In a low-light environment, the human eye can hardly recognize light exceeding 600 nanometers, even in bright In the environment, it is impossible to see light exceeding 700 nanometers . However, the camera still has a capture rate of more than 50% at the wavelength of 700 nanometers.
. However, the camera still has a capture rate of more than 50% at the wavelength of 700 nanometers.
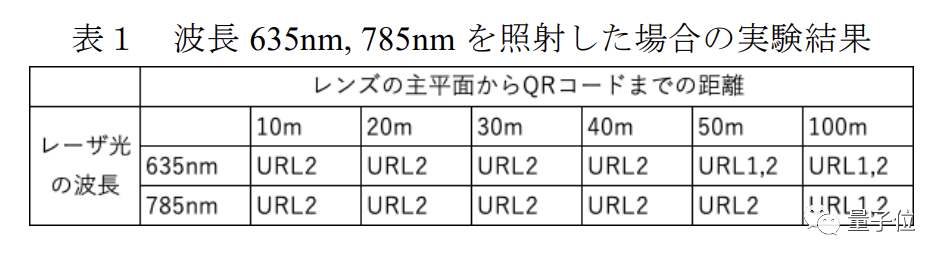
In this experiment, the researchers used 10 milliwatts of 635 nm (red visible light) and 785 nm (infrared) light to illuminate the QR code at different distances
Here 0~50 meters is the actual distance, while the distance of 100 meters is achieved through specular reflection
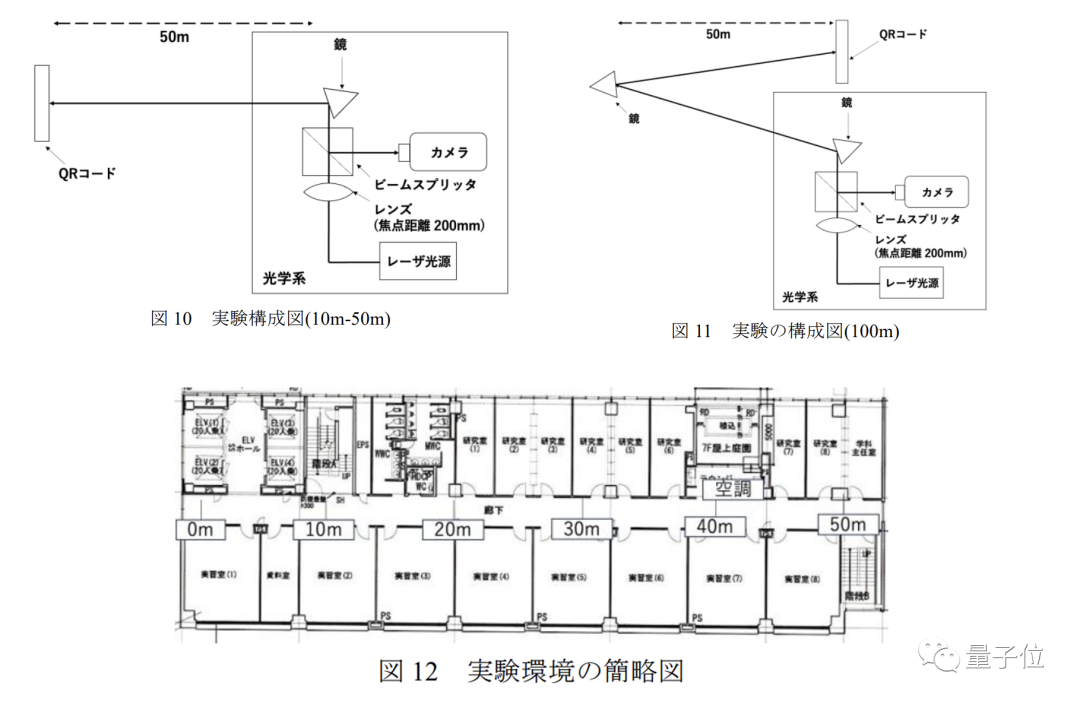
The results show that at 10~40 meters, both wavelengths of light are The link pointed to by the QR code can be successfully changed to a false URL;
At 50 meters, the QR code processed by visible light can scan out both URLs, but the infrared light can still be successfully tampered with ;
At a distance of 100 meters, after two wavelengths of light are irradiated, the display results of the QR code appear alternately
In the future, researchers will also It is planned to increase the attack distance to 1 kilometer.
However, in this experiment, a lens is needed to focus the laser to determine the location of the tampered information point.
If the airflow disturbance in the light path is obvious, it will have an impact on this process, so there are more uncertain factors in long-distance attacks.
As long as the airflow in front of the QR code is disturbed from time to time, the laser will not be able to find its position. This is also a possibility provided to defend against this kind of attack.
Some netizens joked that in the QR code, It may be more effective to fan the laser in front to "dry away" the laser
#In the paper, the author mentioned that in addition to airflow disturbance, the QR code owner also Tamper-proof materials can be used to avoid attacks
One More Thing
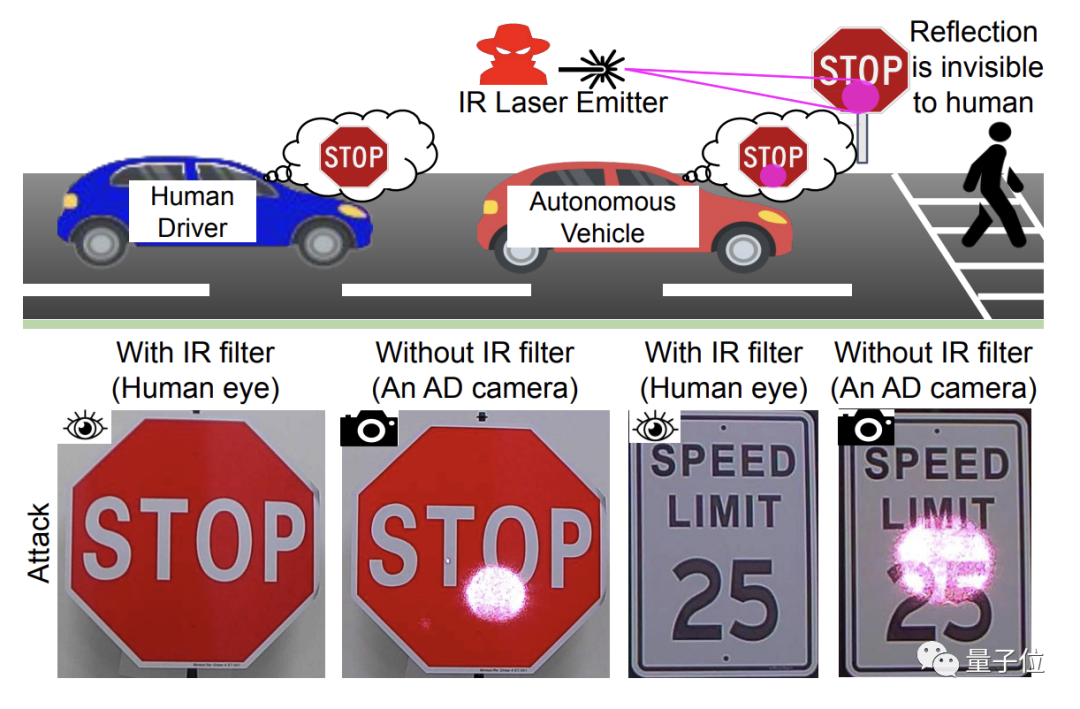
There are some cases of interfering with autonomous driving systems by tampering with QR codes or shining lasers on traffic signs
This laser is also invisible to the naked eye, but can be recognized by the camera, thus causing misleading.
Relevant research shows that in indoor environments, the success rate of this attack on stop signs and speed limit signs is almost 100%.
Paper address (Japanese): http://id.nii.ac.jp/1001/00228597/
The above is the detailed content of Paper QR codes can also be tampered with in the air: a traceless attack from a hundred meters away can instantly turn them into a malicious website entrance. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Open source! Beyond ZoeDepth! DepthFM: Fast and accurate monocular depth estimation!
Apr 03, 2024 pm 12:04 PM
Open source! Beyond ZoeDepth! DepthFM: Fast and accurate monocular depth estimation!
Apr 03, 2024 pm 12:04 PM
0.What does this article do? We propose DepthFM: a versatile and fast state-of-the-art generative monocular depth estimation model. In addition to traditional depth estimation tasks, DepthFM also demonstrates state-of-the-art capabilities in downstream tasks such as depth inpainting. DepthFM is efficient and can synthesize depth maps within a few inference steps. Let’s read about this work together ~ 1. Paper information title: DepthFM: FastMonocularDepthEstimationwithFlowMatching Author: MingGui, JohannesS.Fischer, UlrichPrestel, PingchuanMa, Dmytr
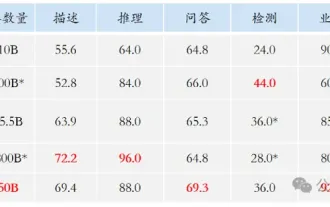
 The world's most powerful open source MoE model is here, with Chinese capabilities comparable to GPT-4, and the price is only nearly one percent of GPT-4-Turbo
May 07, 2024 pm 04:13 PM
The world's most powerful open source MoE model is here, with Chinese capabilities comparable to GPT-4, and the price is only nearly one percent of GPT-4-Turbo
May 07, 2024 pm 04:13 PM
Imagine an artificial intelligence model that not only has the ability to surpass traditional computing, but also achieves more efficient performance at a lower cost. This is not science fiction, DeepSeek-V2[1], the world’s most powerful open source MoE model is here. DeepSeek-V2 is a powerful mixture of experts (MoE) language model with the characteristics of economical training and efficient inference. It consists of 236B parameters, 21B of which are used to activate each marker. Compared with DeepSeek67B, DeepSeek-V2 has stronger performance, while saving 42.5% of training costs, reducing KV cache by 93.3%, and increasing the maximum generation throughput to 5.76 times. DeepSeek is a company exploring general artificial intelligence
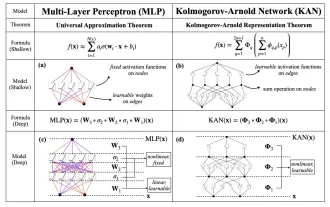 KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
KAN, which replaces MLP, has been extended to convolution by open source projects
Jun 01, 2024 pm 10:03 PM
Earlier this month, researchers from MIT and other institutions proposed a very promising alternative to MLP - KAN. KAN outperforms MLP in terms of accuracy and interpretability. And it can outperform MLP running with a larger number of parameters with a very small number of parameters. For example, the authors stated that they used KAN to reproduce DeepMind's results with a smaller network and a higher degree of automation. Specifically, DeepMind's MLP has about 300,000 parameters, while KAN only has about 200 parameters. KAN has a strong mathematical foundation like MLP. MLP is based on the universal approximation theorem, while KAN is based on the Kolmogorov-Arnold representation theorem. As shown in the figure below, KAN has
 Hello, electric Atlas! Boston Dynamics robot comes back to life, 180-degree weird moves scare Musk
Apr 18, 2024 pm 07:58 PM
Hello, electric Atlas! Boston Dynamics robot comes back to life, 180-degree weird moves scare Musk
Apr 18, 2024 pm 07:58 PM
Boston Dynamics Atlas officially enters the era of electric robots! Yesterday, the hydraulic Atlas just "tearfully" withdrew from the stage of history. Today, Boston Dynamics announced that the electric Atlas is on the job. It seems that in the field of commercial humanoid robots, Boston Dynamics is determined to compete with Tesla. After the new video was released, it had already been viewed by more than one million people in just ten hours. The old people leave and new roles appear. This is a historical necessity. There is no doubt that this year is the explosive year of humanoid robots. Netizens commented: The advancement of robots has made this year's opening ceremony look like a human, and the degree of freedom is far greater than that of humans. But is this really not a horror movie? At the beginning of the video, Atlas is lying calmly on the ground, seemingly on his back. What follows is jaw-dropping
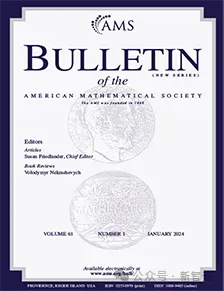 AI subverts mathematical research! Fields Medal winner and Chinese-American mathematician led 11 top-ranked papers | Liked by Terence Tao
Apr 09, 2024 am 11:52 AM
AI subverts mathematical research! Fields Medal winner and Chinese-American mathematician led 11 top-ranked papers | Liked by Terence Tao
Apr 09, 2024 am 11:52 AM
AI is indeed changing mathematics. Recently, Tao Zhexuan, who has been paying close attention to this issue, forwarded the latest issue of "Bulletin of the American Mathematical Society" (Bulletin of the American Mathematical Society). Focusing on the topic "Will machines change mathematics?", many mathematicians expressed their opinions. The whole process was full of sparks, hardcore and exciting. The author has a strong lineup, including Fields Medal winner Akshay Venkatesh, Chinese mathematician Zheng Lejun, NYU computer scientist Ernest Davis and many other well-known scholars in the industry. The world of AI has changed dramatically. You know, many of these articles were submitted a year ago.
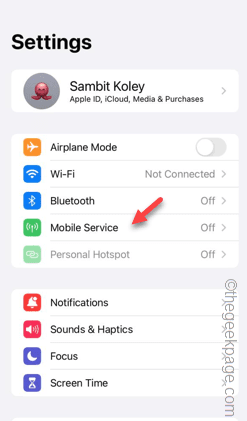 Slow Cellular Data Internet Speeds on iPhone: Fixes
May 03, 2024 pm 09:01 PM
Slow Cellular Data Internet Speeds on iPhone: Fixes
May 03, 2024 pm 09:01 PM
Facing lag, slow mobile data connection on iPhone? Typically, the strength of cellular internet on your phone depends on several factors such as region, cellular network type, roaming type, etc. There are some things you can do to get a faster, more reliable cellular Internet connection. Fix 1 – Force Restart iPhone Sometimes, force restarting your device just resets a lot of things, including the cellular connection. Step 1 – Just press the volume up key once and release. Next, press the Volume Down key and release it again. Step 2 – The next part of the process is to hold the button on the right side. Let the iPhone finish restarting. Enable cellular data and check network speed. Check again Fix 2 – Change data mode While 5G offers better network speeds, it works better when the signal is weaker
 The vitality of super intelligence awakens! But with the arrival of self-updating AI, mothers no longer have to worry about data bottlenecks
Apr 29, 2024 pm 06:55 PM
The vitality of super intelligence awakens! But with the arrival of self-updating AI, mothers no longer have to worry about data bottlenecks
Apr 29, 2024 pm 06:55 PM
I cry to death. The world is madly building big models. The data on the Internet is not enough. It is not enough at all. The training model looks like "The Hunger Games", and AI researchers around the world are worrying about how to feed these data voracious eaters. This problem is particularly prominent in multi-modal tasks. At a time when nothing could be done, a start-up team from the Department of Renmin University of China used its own new model to become the first in China to make "model-generated data feed itself" a reality. Moreover, it is a two-pronged approach on the understanding side and the generation side. Both sides can generate high-quality, multi-modal new data and provide data feedback to the model itself. What is a model? Awaker 1.0, a large multi-modal model that just appeared on the Zhongguancun Forum. Who is the team? Sophon engine. Founded by Gao Yizhao, a doctoral student at Renmin University’s Hillhouse School of Artificial Intelligence.
 The U.S. Air Force showcases its first AI fighter jet with high profile! The minister personally conducted the test drive without interfering during the whole process, and 100,000 lines of code were tested for 21 times.
May 07, 2024 pm 05:00 PM
The U.S. Air Force showcases its first AI fighter jet with high profile! The minister personally conducted the test drive without interfering during the whole process, and 100,000 lines of code were tested for 21 times.
May 07, 2024 pm 05:00 PM
Recently, the military circle has been overwhelmed by the news: US military fighter jets can now complete fully automatic air combat using AI. Yes, just recently, the US military’s AI fighter jet was made public for the first time and the mystery was unveiled. The full name of this fighter is the Variable Stability Simulator Test Aircraft (VISTA). It was personally flown by the Secretary of the US Air Force to simulate a one-on-one air battle. On May 2, U.S. Air Force Secretary Frank Kendall took off in an X-62AVISTA at Edwards Air Force Base. Note that during the one-hour flight, all flight actions were completed autonomously by AI! Kendall said - "For the past few decades, we have been thinking about the unlimited potential of autonomous air-to-air combat, but it has always seemed out of reach." However now,





