mysql新添加用户与删除用户具体操作命令_MySQL
方法1 :使用mysql root(root权限)用户登陆直接赋权也可以创建用户
/usr/bin/mysqladmin -u root password 123456
mysql -uroot -p
密码
查看所有用户名与密码
select host ,user ,password from user;
grant all on ec.* to 'root'@'%' identified by '123456';
grant all privileges on ec.* to 'cockpit'@'%' identified by '123456';
grant all on ec.* to 'cockpit'@'%' identified by '123456';
grant all privileges on ec.* to 'cockpit'@'%' identified by '123456';
flush privileges;;
更改数据库密码
user mysql
修改mysql数据库的密码
UPDATE user SET Password=PASSWORD('123456') where USER='root';
mysql root密码为空 登陆的时候不需要密码
UPDATE user SET Password=PASSWORD(null) where USER='root';
flush privileges;
方法二:
1.新建用户。
//登录MYSQL
@>mysql -u root -p
@>密码
//首先为用户创建一个数据库(testDB)
mysql>create database testDB default character set utf8;;
//创建用户
mysql> insert into mysql.user(Host,User,Password) values("localhost","test",password("1234"));
//刷新系统权限表
mysql>flush privileges;
这样就创建了一个名为:test 密码为:1234 的用户。
然后登录一下。
mysql>exit;
@>mysql -u phplamp -p
@>输入密码
mysql>登录成功
2.为用户授权。
格式:grant 权限 on 数据库.* to 用户名@登录主机 identified by "密码";
>grant all privileges on phplampDB.* to phplamp@localhost identified by '1234";
授权test用户拥有所有数据库的某些权限:
mysql>grant select,delete,update,create,drop on *.* to test@"%" identified by "1234";
//test用户对所有数据库都有select,delete,update,create,drop 权限。
//@"%" 表示对所有非本地主机授权,不包括localhost。(localhost地址设为127.0.0.1,如果设为真实的本地地址,不知道是否可以,没有验证。)
//对localhost授权:加上一句grant all privileges on testDB.* to test@localhost identified by '1234';即可。
3.删除用户。
@>mysql -u root -p
@>密码
mysql>DELETE FROM user WHERE User="test" and Host="localhost";
mysql>flush privileges;
//删除用户的数据库
mysql>drop database testDB;
4.修改指定用户密码。
@>mysql -u root -p
@>密码
mysql>update mysql.user set password=password('新密码') where User="test" and Host="localhost";
mysql>flush privileges;
delete from user where User="test" and Host="localhost";
也可以试试:
删除账户及权限:>drop user 用户名@'%';
>drop user 用户名@ localhost;

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How to use Xiaohongshu account to find users? Can I find my mobile phone number?
Mar 22, 2024 am 08:40 AM
How to use Xiaohongshu account to find users? Can I find my mobile phone number?
Mar 22, 2024 am 08:40 AM
With the rapid development of social media, Xiaohongshu has become one of the most popular social platforms. Users can create a Xiaohongshu account to show their personal identity and communicate and interact with other users. If you need to find a user’s Xiaohongshu number, you can follow these simple steps. 1. How to use Xiaohongshu account to find users? 1. Open the Xiaohongshu APP, click the "Discover" button in the lower right corner, and then select the "Notes" option. 2. In the note list, find the note posted by the user you want to find. Click to enter the note details page. 3. On the note details page, click the "Follow" button below the user's avatar to enter the user's personal homepage. 4. In the upper right corner of the user's personal homepage, click the three-dot button and select "Personal Information"
 Log in to Ubuntu as superuser
Mar 20, 2024 am 10:55 AM
Log in to Ubuntu as superuser
Mar 20, 2024 am 10:55 AM
In Ubuntu systems, the root user is usually disabled. To activate the root user, you can use the passwd command to set a password and then use the su- command to log in as root. The root user is a user with unrestricted system administrative rights. He has permissions to access and modify files, user management, software installation and removal, and system configuration changes. There are obvious differences between the root user and ordinary users. The root user has the highest authority and broader control rights in the system. The root user can execute important system commands and edit system files, which ordinary users cannot do. In this guide, I'll explore the Ubuntu root user, how to log in as root, and how it differs from a normal user. Notice
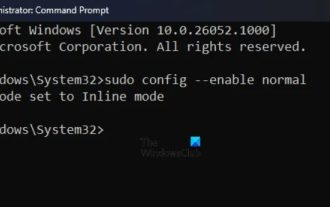 How to run SUDO commands in Windows 11/10
Mar 09, 2024 am 09:50 AM
How to run SUDO commands in Windows 11/10
Mar 09, 2024 am 09:50 AM
The sudo command allows users to run commands in elevated privilege mode without switching to superuser mode. This article will introduce how to simulate functions similar to sudo commands in Windows systems. What is the Shudao Command? Sudo (short for "superuser do") is a command-line tool that allows users of Unix-based operating systems such as Linux and MacOS to execute commands with elevated privileges typically held by administrators. Running SUDO commands in Windows 11/10 However, with the launch of the latest Windows 11 Insider preview version, Windows users can now experience this feature. This new feature enables users to
 What is sudo and why is it important?
Feb 21, 2024 pm 07:01 PM
What is sudo and why is it important?
Feb 21, 2024 pm 07:01 PM
sudo (superuser execution) is a key command in Linux and Unix systems that allows ordinary users to run specific commands with root privileges. The function of sudo is mainly reflected in the following aspects: Providing permission control: sudo achieves strict control over system resources and sensitive operations by authorizing users to temporarily obtain superuser permissions. Ordinary users can only obtain temporary privileges through sudo when needed, and do not need to log in as superuser all the time. Improved security: By using sudo, you can avoid using the root account during routine operations. Using the root account for all operations may lead to unexpected system damage, as any mistaken or careless operation will have full permissions. and
 How to check the MAC address of the network card in Win11? How to use the command to obtain the MAC address of the network card in Win11
Feb 29, 2024 pm 04:34 PM
How to check the MAC address of the network card in Win11? How to use the command to obtain the MAC address of the network card in Win11
Feb 29, 2024 pm 04:34 PM
This article will introduce readers to how to use the command prompt (CommandPrompt) to find the physical address (MAC address) of the network adapter in Win11 system. A MAC address is a unique identifier for a network interface card (NIC), which plays an important role in network communications. Through the command prompt, users can easily obtain the MAC address information of all network adapters on the current computer, which is very helpful for network troubleshooting, configuring network settings and other tasks. Method 1: Use "Command Prompt" 1. Press the [Win+X] key combination, or [right-click] click the [Windows logo] on the taskbar, and in the menu item that opens, select [Run]; 2. Run the window , enter the [cmd] command, and then
 Where is hyperv enhanced session mode? Tips for enabling or disabling Hyper-V enhanced session mode using commands in Win11
Feb 29, 2024 pm 05:52 PM
Where is hyperv enhanced session mode? Tips for enabling or disabling Hyper-V enhanced session mode using commands in Win11
Feb 29, 2024 pm 05:52 PM
In Win11 system, you can enable or disable Hyper-V enhanced session mode through commands. This article will introduce how to use commands to operate and help users better manage and control Hyper-V functions in the system. Hyper-V is a virtualization technology provided by Microsoft. It is built into Windows Server and Windows 10 and 11 (except Home Edition), allowing users to run virtual operating systems in Windows systems. Although virtual machines are isolated from the host operating system, they can still use the host's resources, such as sound cards and storage devices, through settings. One of the key settings is to enable Enhanced Session Mode. Enhanced session mode is Hyper
 Super practical! Sar commands that will make you a Linux master
Mar 01, 2024 am 08:01 AM
Super practical! Sar commands that will make you a Linux master
Mar 01, 2024 am 08:01 AM
1. Overview The sar command displays system usage reports through data collected from system activities. These reports are made up of different sections, each containing the type of data and when the data was collected. The default mode of the sar command displays the CPU usage at different time increments for various resources accessing the CPU (such as users, systems, I/O schedulers, etc.). Additionally, it displays the percentage of idle CPU for a given time period. The average value for each data point is listed at the bottom of the report. sar reports collected data every 10 minutes by default, but you can use various options to filter and adjust these reports. Similar to the uptime command, the sar command can also help you monitor the CPU load. Through sar, you can understand the occurrence of excessive load
 Analysis of user password storage mechanism in Linux system
Mar 20, 2024 pm 04:27 PM
Analysis of user password storage mechanism in Linux system
Mar 20, 2024 pm 04:27 PM
Analysis of user password storage mechanism in Linux system In Linux system, the storage of user password is one of the very important security mechanisms. This article will analyze the storage mechanism of user passwords in Linux systems, including the encrypted storage of passwords, the password verification process, and how to securely manage user passwords. At the same time, specific code examples will be used to demonstrate the actual operation process of password storage. 1. Encrypted storage of passwords In Linux systems, user passwords are not stored in the system in plain text, but are encrypted and stored. L






