How to password protect PDF on Mac
When sharing confidential PDF files, it is very important to ensure that they cannot be accessed without authorization. One effective method is to create password-protected PDF files. The process is very simple and only requires a few steps. In this blog, I will share how to password protect PDF files on Mac.
Why is it important to password protect PDFs on Mac?
Password protecting PDF on Apple Mac computers is essential to protect your data from prying eyes. The process is safe and simple for users of all levels of expertise. By password-protecting a PDF file, you can encrypt its contents to ensure they are inaccessible without a password. In this way, even if your PDF file is accidentally leaked, you can ensure that the sensitive information in it will not be easily obtained. Whether you are an individual user or a business user, you should keep the importance of password protection in mind when dealing with PDF files.
So you can share or distribute information with confidence without worrying about data loss or security breaches. This is especially important for businesses and organizations that handle sensitive data, such as customer information and financial records. In addition, they are able to ensure compliance with industry and government data protection and privacy regulations.
How to Create a Password-Protected PDF File on Mac
You can use different methods to create a password-protected PDF on Mac. Let’s try to understand the gist of the methods you can use to protect PDF on Mac in a few simple steps:
Method 1: Password-protect PDF in Preview
Open the PDF you want to lock. Click File on the menu bar → select Export.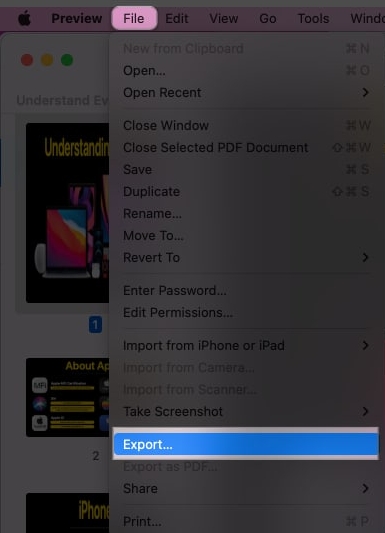 Click "Permissions".
Click "Permissions". 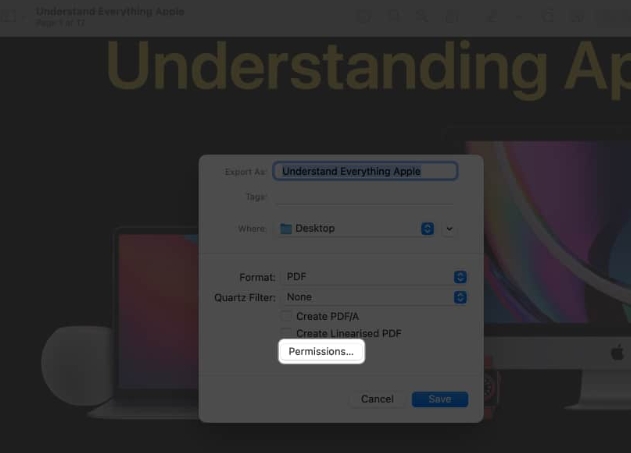 Select the Require password to open document option. Enter the password twice → Set owner password → Click Apply.
Select the Require password to open document option. Enter the password twice → Set owner password → Click Apply. 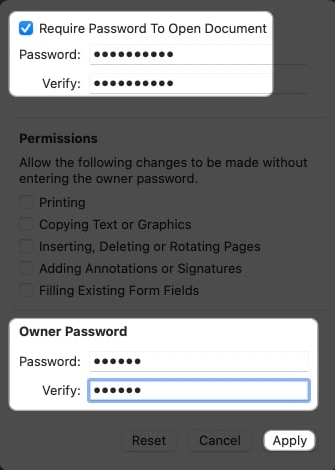 Select Save. Select Replace when prompted.
Select Save. Select Replace when prompted. With this step, the password-protected version of the file replaces the original version.
Overview of Security Options
In addition to locking the PDF, you can enable a number of security permissions to ensure complete control over the document.
Print: Allows users to print documents. Copy text or graphics: You can copy the entire contents of a PDF. Insert, delete or rotate pages: This will make it easier for users to perform corresponding operations on PDFs. Allow comments or signatures: Users can sign or add comments to the PDF. Fill existing form fields: It enables users to fill in specific sections or the entire form in a PDF.When you check the box for a specific permission, the user can perform that action. After making the necessary changes, press Apply → Save → Replace.
Method 2: Use the Print Dialog Box
Access any document you want from Finder. (Example: Word, PDF, Image, etc.) In this case, I chose to use an image. Select File from the menu bar → click Print or use the CMD P key combination. Click PDF at the bottom and select Save as PDF. Select security options. Check Require password to open document and enter password → click OK. Click Save.Navigate to the file's location from the Finder to find a locked version of the same document.
Overview of Security Options
In addition to locking files, you can add an extra layer of security by turning on a few other options, such as:
Require a password to copy text, images, and other Context: Check this box to prevent recipients from copying the contents of the PDF. Require password to print document: Enable this to prevent anyone from printing the PDF.You must create different passwords for these permissions. After setting the document's security settings, click OK → Save. Now, users can only read PDFs and require a password to copy or print PDF content.
The Best Third-Party Apps to Set PDF Password on Mac
The default system settings for locking PDFs are very simple. However, in addition to the default PDF viewing and editing tools, there are several third-party applications for Mac. These apps come with advanced features and security features.
Format PDF UPDF Shallow PDFHow to Open Password Protected PDF File on Mac
Now that you have a clear idea of the different ways to lock a PDF, you might be wondering how to unlock the same PDF. Don’t worry; see our guide to remove password protection from PDF in simple steps. Therefore, you can quickly access file contents and print them.
FAQ
What should I do if I forget the password for a password-protected PDF document?
If you forget the password to encrypt a PDF document, you will not be able to access the contents of the document. Passwords cannot be recovered, so it is crucial to record them in a safe place.
Can I password protect individual pages of a PDF document?
Unfortunately, the Preview application does not have built-in functionality to password-protect individual PDF document pages. You must use a third-party application or online tool to do this.
Log out!
Password protecting PDF on Mac is simple and straightforward, keeping sensitive documents safe and preventing malicious users from accessing them. With the above steps, you can create password-protected PDFs in just a few clicks.
The above is the detailed content of How to password protect PDF on Mac. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 How long does the motherboard battery last?
May 08, 2024 pm 09:04 PM
How long does the motherboard battery last?
May 08, 2024 pm 09:04 PM
How often should you replace a computer motherboard battery? Generally speaking, the service life of a motherboard battery is 3-5 years, but it may be shorter or longer. If the computer has problems such as inaccurate clock and incorrect system settings, it may be caused by damage to the motherboard battery. The motherboard battery should be replaced every 2 to 3 years. The motherboard battery is used to record the time of the computer system, that is, to maintain the accuracy of the system clock. When the battery is insufficient, the time will return to the factory date. When CMOS errors occur frequently when starting the computer, and the date and time are incorrect, it is time to replace the battery. The battery life of the motherboard is very long, usually about 5 years. The battery is in a charging state when the computer is turned on, and the BIOS is discharged after the computer is shut down to maintain the associated information in the BIOS (such as
 The easiest way to convert mobile phone videos to MP4 (quick tips for converting mobile phone videos to MP4 format)
May 08, 2024 pm 08:43 PM
The easiest way to convert mobile phone videos to MP4 (quick tips for converting mobile phone videos to MP4 format)
May 08, 2024 pm 08:43 PM
But sometimes it is necessary to convert it to MP4 format to play on other devices. People shoot more and more mobile phone videos with the popularity of smartphones. To help users quickly convert mobile phone videos to MP4 format, this article will introduce the simplest method. 1. Use professional video conversion tools to convert mobile phone videos to MP4 format, such as FFmpeg, etc., such as HandBrake. Can meet the needs of different users, these tools provide rich conversion options. 2. Mobile phone application conversion tools such as iConv also provide video conversion functions. Users only need to import mobile phone videos into the application and choose to output them in MP4 format. Some mobile phone applications such as VideoConverte
 How to solve the problem that the excel table cannot be opened
May 08, 2024 pm 08:36 PM
How to solve the problem that the excel table cannot be opened
May 08, 2024 pm 08:36 PM
Steps to solve an Excel table that cannot be opened: Check whether the file type is correct; repair the file or choose another application to open; disable add-ins; change file associations; reset Excel default settings; try other methods (such as reinstalling Excel).
 What is the value and use of icp coins?
May 09, 2024 am 10:47 AM
What is the value and use of icp coins?
May 09, 2024 am 10:47 AM
As the native token of the Internet Computer (IC) protocol, ICP Coin provides a unique set of values and uses, including storing value, network governance, data storage and computing, and incentivizing node operations. ICP Coin is considered a promising cryptocurrency, with its credibility and value growing with the adoption of the IC protocol. In addition, ICP coins play an important role in the governance of the IC protocol. Coin holders can participate in voting and proposal submission, affecting the development of the protocol.
 Apple MacBook Air and MacBook Pro M4, M4 Pro and M4 Max refreshes to rumoured launch with new AI features locked to monthly paid subscription but no design changes
Jul 02, 2024 am 07:29 AM
Apple MacBook Air and MacBook Pro M4, M4 Pro and M4 Max refreshes to rumoured launch with new AI features locked to monthly paid subscription but no design changes
Jul 02, 2024 am 07:29 AM
For now, the only way to get your hands on an Apple M4 chipset is to purchase the company's latest iPad Pro, the entry point for which remains the iPad Pro 11 with 256 GB of storage and Wi-Fi-only connectivity (curr. $944 on Amazon). However, rumours
 The difference between oracle database and mysql
May 10, 2024 am 01:54 AM
The difference between oracle database and mysql
May 10, 2024 am 01:54 AM
Oracle database and MySQL are both databases based on the relational model, but Oracle is superior in terms of compatibility, scalability, data types and security; while MySQL focuses on speed and flexibility and is more suitable for small to medium-sized data sets. . ① Oracle provides a wide range of data types, ② provides advanced security features, ③ is suitable for enterprise-level applications; ① MySQL supports NoSQL data types, ② has fewer security measures, and ③ is suitable for small to medium-sized applications.
 Usage of rename in sql
May 09, 2024 am 09:36 AM
Usage of rename in sql
May 09, 2024 am 09:36 AM
The RENAME command is used in SQL to rename a table, column, or constraint. The syntax is: RENAME [object_type] old_name TO new_name;, where object_type specifies the object type (table, column, or constraint), old_name is the old name, and new_name is the new name. You need to pay attention to the following when renaming: the new name cannot be repeated with objects of the same type; when renaming a column, the column type cannot be changed; when renaming a constraint, the new name must comply with the constraint type rules; the RENAME command does not support cross-database renaming; recommendations Back up the table structure before using the RENAME command to prevent data loss.
 The role of keep-alive in vue
May 09, 2024 pm 02:42 PM
The role of keep-alive in vue
May 09, 2024 pm 02:42 PM
The keep-alive directive in Vue is used to cache components to prevent them from being destroyed and recreated when switching routes. By caching components, keep-alive can improve performance, maintain component status, and optimize user experience. Applicable scenarios include components that need to cache data, components that need to maintain interactive state, and components that need to avoid performance degradation caused by frequent re-rendering. When used, reactive properties and methods need to be persisted, and asynchronous or functional components cannot be cached.






