 System Tutorial
System Tutorial
 LINUX
LINUX
 You can try to use the following solutions to intercept Linux kernel functions
You can try to use the following solutions to intercept Linux kernel functions
You can try to use the following solutions to intercept Linux kernel functions
You can try to use the following solutions to intercept Linux kernel functions:
Using Linux Security API
From the perspective of best practices, we feel that using the hook function of the Linux security API is the best choice, because this socket is designed for this purpose. Key points in the kernel code include security function calls, which may cause the installation of security modules to escalate. This module can study the context of a specific operation and decide whether to allow or prohibit it. Unfortunately, the LinuxSecurityAPI has two major limitations:

In fact, kernel developers have different ideas on whether the system can contain multiple security modules, and it is a certain fact that the modules cannot be loaded dynamically. To ensure that a system remains secure from the start, security modules must be part of the kernel. For this reason, in order to use the Linux security API, we need to create a custom Linux kernel.
Change system call table
Because it is mainly used for operations performed by user applications, we can implement it at the system call level. All Linux system call handlers are stored in the sys_call_table table. Modifying the values in this table results in modified system behavior. We can do this by hooking the system call by saving the old handler value and adding our own handler to the table. These methods also have some advantages and disadvantages.
The main advantages are as follows:
However, these methods also have several disadvantages:
Technical implementation is more complex. In fact, it is not difficult to replace the values in the table Call linux kernel functions, but there are some additional tasks that require individual conditions and some non-obvious solutions:

Only hook system calls. Because this approach allows you to replace system call handlers, it greatly limits entry points. All additional detection can be performed before or immediately after the system call, we only have the system call parameters and their return values. Therefore, sometimes we may need to carefully check the access permissions of the process and the validity of the system call parameters. It is reported that in some cases, the need to copy the user process memory twice will cause additional expenses. For example, when a parameter is passed through the watch needle, there are two copies: one created by ourselves and one created by the original handler.
Use Kprobes
Kprobes — An API designed for Linux kernel tracing and debugging. Kprobes allows the installation of pre- and post-processors for any kernel instruction as well as function entry and function return handlers. Handlers have access to registers and can modify them. This way, we have the opportunity to monitor the file execution flow and change it.

The main uses of using Kprobes to track Linux kernel functions are as follows:
Kprobes also have shortcomings:
Splicing
A classic way to configure kernel function hooking: replace the instructions at the beginning of the function with an unconditional jump to a custom handler. The original instruction is wired to a different location and executed before jumping back to the intercepted function. For this reason, with two jumps, the code can be spliced into a function. This works the same way as kprobes jump optimization. Using splicing, you can get the same results as using kprobes, but with less overhead and full control over the process.
The advantages of using splicing are very significant:
However, these methods have a major drawback - technical complexity. Replacing the machine code in a function is not easy. In order to use splicing to call the linux kernel function, you need to complete the following operations:
Relatively speaking, splicing may be a very useful way to hook Linux kernel functions. But the implementation of this method is too complicated. Because considering our own capabilities and some other incentives, we are not prepared to adopt these methods for the time being, so we use them as candidates.
The above is the detailed content of You can try to use the following solutions to intercept Linux kernel functions. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Mastering Text Manipulation With the Sed Command
Mar 16, 2025 am 09:48 AM
Mastering Text Manipulation With the Sed Command
Mar 16, 2025 am 09:48 AM
The Linux command line interface provides a wealth of text processing tools, one of the most powerful tools is the sed command. sed is the abbreviation of Stream EDitor, a multi-functional tool that allows complex processing of text files and streams. What is Sed? sed is a non-interactive text editor that operates on pipeline inputs or text files. By providing directives, you can let it modify and process text in a file or stream. The most common use cases of sed include selecting text, replacing text, modifying original files, adding lines to text, or removing lines from text. It can be used from the command line in Bash and other command line shells. Sed command syntax sed
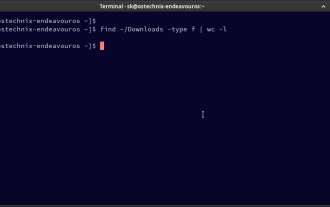 How To Count Files And Directories In Linux: A Beginner's Guide
Mar 19, 2025 am 10:48 AM
How To Count Files And Directories In Linux: A Beginner's Guide
Mar 19, 2025 am 10:48 AM
Efficiently Counting Files and Folders in Linux: A Comprehensive Guide Knowing how to quickly count files and directories in Linux is crucial for system administrators and anyone managing large datasets. This guide demonstrates using simple command-l
 Pilet: A Modular, Portable Mini-Computer Powered by Raspberry Pi
Mar 06, 2025 am 10:11 AM
Pilet: A Modular, Portable Mini-Computer Powered by Raspberry Pi
Mar 06, 2025 am 10:11 AM
Discover Pilet: A Retro-Futuristic, Open-Source Mini-Computer Looking for a mini-computer that blends classic style with cutting-edge technology? Meet Pilet, a modular, open-source marvel powered by the Raspberry Pi 5. Boasting a 7-hour battery life
 Linux Kernel Source Code Surpasses 40 Million Lines
Mar 05, 2025 am 09:35 AM
Linux Kernel Source Code Surpasses 40 Million Lines
Mar 05, 2025 am 09:35 AM
Linux: The cornerstone of modern computing, from smartphones to supercomputers, can do everything. Over the years, the size and complexity of the Linux kernel has increased significantly. As of January 2025, the Linux kernel source code contains approximately 40 million lines of code! This is one of the greatest achievements in the history of open source, community-driven projects. This article will discuss the exponential growth of the number of lines in the Linux kernel source code, the reasons and how to check the current number of lines by yourself. Directory -Linux kernel history Count the number of lines of the Linux kernel source code only count C and header files Exponential trend of kernel growth Verify historical Linux kernel lines Summary Linux kernel history Since 1991 Linus Tor
 System76 Introduces Meerkat Mini PC: Big Power in a Tiny Package
Mar 05, 2025 am 10:28 AM
System76 Introduces Meerkat Mini PC: Big Power in a Tiny Package
Mar 05, 2025 am 10:28 AM
The System76 Meerkat: A Mighty Mini PC Looking for a powerful yet space-saving computer? Meet the Meerkat mini PC from System76! This compact powerhouse is perfect for tidy desktops and demanding tasks. Table of Contents - Compact Design, Impressive
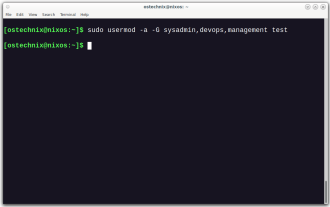 How To Add A User To Multiple Groups In Linux
Mar 18, 2025 am 11:44 AM
How To Add A User To Multiple Groups In Linux
Mar 18, 2025 am 11:44 AM
Efficiently managing user accounts and group memberships is crucial for Linux/Unix system administration. This ensures proper resource and data access control. This tutorial details how to add a user to multiple groups in Linux and Unix systems. We
 The Secret Weapon to Supercharge Your Linux System With Liquorix Kernel
Mar 08, 2025 pm 12:12 PM
The Secret Weapon to Supercharge Your Linux System With Liquorix Kernel
Mar 08, 2025 pm 12:12 PM
Liquorix kernel: a powerful tool to improve Linux system performance Linux is known for its flexibility, security and high performance, becoming the operating system of choice for developers, system administrators, and advanced users. However, the universal Linux kernel is not always meeting the needs of users seeking maximum performance and responsiveness. This is where the Liquorix kernel comes into play—a performance-optimized alternative that promises to enhance your Linux system. This article will explore what the Liquorix kernel is, why you might want to use it, and how to install and configure it to get the most out of your system. Liquorix kernel detailed explanation Liquorix kernel is a precompiled Linux kernel designed for
 Building Your Own Ubuntu Personal Cloud: A Step-by-Step Guide to Creating a Secure Data Haven
Mar 05, 2025 am 11:02 AM
Building Your Own Ubuntu Personal Cloud: A Step-by-Step Guide to Creating a Secure Data Haven
Mar 05, 2025 am 11:02 AM
In today's digital age, data is not just information, but also a part of our lives. From photos and documents to sensitive personal information, our data represents our memories, work and interests. Although cloud storage services are widely available, they are often accompanied by privacy concerns, subscription fees, and customization restrictions. That's what building a personal cloud on Ubuntu is about as a powerful alternative, which gives you complete control over your data and the flexibility to customize and scale as needed. This guide will guide you to set up a Ubuntu-based personal cloud, use Nextcloud as the primary application, and ensure your settings are secure and reliable. Why build a personal cloud on Ubuntu? Ubuntu is the most popular Linux





