The role of md5 value
MD5 (Message Digest Algorithm 5) is a commonly used digest algorithm that can convert data of any length into a fixed-length hash value. The MD5 algorithm is widely used in the computer field for data integrity verification and password security storage.
One of the main functions of the MD5 algorithm is data integrity verification. During data transmission and storage, in order to ensure data integrity, MD5 digest calculation can be performed on the data. After receiving the data, the receiver can also perform MD5 digest calculation on it, and then compare it with the MD5 value sent by the sender. If the two MD5 values are equal, it means that the data has not been tampered with and the integrity of the original data is maintained. If the MD5 values are not equal, the data may have been tampered with or corrupted.
In addition to data integrity verification, the MD5 algorithm is also widely used for secure storage of passwords. In the account system, in order to protect the security of the user's password, the password is usually calculated by MD5 digest and stored in the database. When the user logs in, the system will digest the password entered by the user through the MD5 algorithm, and then compare it with the MD5 value in the database. If the two MD5 values are equal, it means that the password entered by the user is correct and login is allowed; if they are not equal, it means that the password is wrong and login is prohibited. This prevents the original password from being exposed and improves account security.
In addition, the MD5 algorithm can also be used for file integrity verification. When downloading a file, the website usually provides the MD5 value of the file. Users can calculate the MD5 digest of the file after downloading it, and then compare it with the MD5 value provided by the website. If the two MD5 values are equal, it means that the file has been downloaded completely and no data corruption has occurred; if they are not equal, it means that the file may have been tampered with or damaged during the download process and needs to be downloaded again.
However, it is worth noting that with the enhancement of computing power, some people have discovered the weaknesses of some MD5 algorithms, which can generate the same MD5 value through collision attacks, thus destroying data integrity protection. and password security features. Therefore, in order to enhance security, the MD5 algorithm has been gradually replaced by more secure algorithms, such as SHA-256, etc.
To sum up, the MD5 algorithm plays an important role in data integrity verification, password security storage and file integrity verification. However, as security needs increase, we should continue to pay attention to the development of new and more secure encryption algorithms to protect users' data and password security.
The above is the detailed content of The role of md5 value. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 Enable 256-bit Bitlocker encryption on Windows 11 for increased security
Nov 26, 2023 am 11:21 AM
Enable 256-bit Bitlocker encryption on Windows 11 for increased security
Nov 26, 2023 am 11:21 AM
Bitlocker is the default encryption technology for Windows operating systems. It is widely used on Windows, but some users prefer third-party solutions such as VeraCrypt. What many users of Bitlocker don't know is that it defaults to 128-bit encryption, even though 256-bit is available. Without going into too much detail about the differences; the core difference between AES 128-bit and 256-bit encryption is the length of the security key. Longer keys make brute force attacks more difficult. While the default is 128-bit, even Microsoft recommends 256-bit for better security. The problem is, most users probably don't know about the weaker defaults or how to change them. First, you might want to know W
 Win11 encrypted dns detailed tutorial
Dec 25, 2023 am 10:13 AM
Win11 encrypted dns detailed tutorial
Dec 25, 2023 am 10:13 AM
Microsoft previously provided dns encryption services for win11, but many users do not know how to use win11 encrypted dns. In fact, we only need to open the dns settings under network settings. Detailed tutorial on win11 encrypted dns: 1. First enter the disk and find the folder you want to encrypt. 2. Then open "Ethernet" on the right 3. Then find the DNS server allocation below and click "Edit" 4. After changing "Auto (DHCP)" to "Manual", open "IPv4" below 5. After turning it on, enter "8.8.8.8" in the preferred DNS 6. Then change the preferred DNS encryption to "Encryption only (DNS over HTTPS)" 7. After the changes are completed, click "Save" and you will find
 Does Win10 Home Edition support folder encryption?
Jan 09, 2024 am 08:58 AM
Does Win10 Home Edition support folder encryption?
Jan 09, 2024 am 08:58 AM
File encryption aims to implement professional-level encryption of data to more effectively ensure data security! Only by mastering the correct encryption key can the decryption operation be performed, ensuring the security of information assets. However, the file encryption function of Win10 Home Edition does not yet have this feature. Can Win10 Home Edition encrypt folders? Answer: Win10 Home Edition cannot encrypt folders. Tutorial on encrypting files in Windows system 1. Right-click on the file or folder you want to encrypt (or press and hold for a while), and then select the "Properties" function. 2. In the new expanded interface, look for the "Advanced" option. After clicking to enter, remember to check the "Encrypt content to protect data" option located below. 3. After the setting is completed, click "OK" to
 How to set up encryption of photo album on Apple mobile phone
Mar 02, 2024 pm 05:31 PM
How to set up encryption of photo album on Apple mobile phone
Mar 02, 2024 pm 05:31 PM
In Apple mobile phones, users can encrypt photo albums according to their own needs. Some users don't know how to set it up. You can add the pictures that need to be encrypted to the memo, and then lock the memo. Next, the editor will introduce the method of setting up the encryption of mobile photo albums for users. Interested users, come and take a look! Apple mobile phone tutorial How to set up iPhone photo album encryption A: After adding the pictures that need to be encrypted to the memo, go to lock the memo for detailed introduction: 1. Enter the photo album, select the picture that needs to be encrypted, and then click [Add to] below. 2. Select [Add to Notes]. 3. Enter the memo, find the memo you just created, enter it, and click the [Send] icon in the upper right corner. 4. Click [Lock Device] below
 How to set a password for folder encryption without compression
Feb 20, 2024 pm 03:27 PM
How to set a password for folder encryption without compression
Feb 20, 2024 pm 03:27 PM
Folder encryption is a common data protection method that encrypts the contents of a folder so that only those who have the decryption password can access the files. When encrypting a folder, there are some common ways to set a password without compressing the file. First, we can use the encryption function that comes with the operating system to set a folder password. For Windows users, you can set it up by following the following steps: Select the folder to be encrypted, right-click the folder, and select "Properties"
 Common network communication and security problems and solutions in C#
Oct 09, 2023 pm 09:21 PM
Common network communication and security problems and solutions in C#
Oct 09, 2023 pm 09:21 PM
Common network communication and security problems and solutions in C# In today's Internet era, network communication has become an indispensable part of software development. In C#, we usually encounter some network communication problems, such as data transmission security, network connection stability, etc. This article will discuss in detail common network communication and security issues in C# and provide corresponding solutions and code examples. 1. Network communication problems Network connection interruption: During the network communication process, the network connection may be interrupted, which may cause
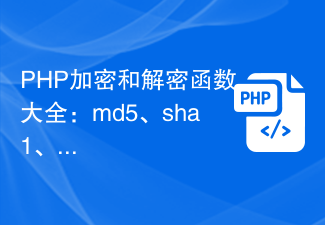 Complete list of PHP encryption and decryption functions: safe application methods of md5, sha1, base64_encode and other functions
Nov 18, 2023 pm 04:18 PM
Complete list of PHP encryption and decryption functions: safe application methods of md5, sha1, base64_encode and other functions
Nov 18, 2023 pm 04:18 PM
Complete list of PHP encryption and decryption functions: safe application methods of md5, sha1, base64_encode and other functions, requiring specific code examples. In the development of network applications, data encryption and decryption is very important. As a popular server-side scripting language, PHP provides a variety of encryption and decryption functions. This article will introduce commonly used functions and their secure application methods, and provide specific code examples. md5 function The md5 function is the most common encryption function that can convert a string of any length into 32 bits
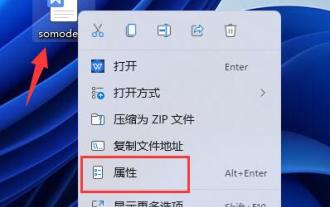 Complete guide to win11 file encryption
Jan 09, 2024 pm 02:50 PM
Complete guide to win11 file encryption
Jan 09, 2024 pm 02:50 PM
Some friends want to protect their files, but don’t know how to encrypt win11 documents. In fact, we can directly use folder encryption or use third-party software to encrypt files. Detailed tutorial on win11 document encryption: 1. First find the file you want to encrypt, right-click to select it, and open "Properties" 2. Then click "Advanced" in the properties column 3. Select "Encrypt content to protect data" in Advanced and click " OK" 4. Then click "OK" to save. 5. Finally, select the desired encryption mode and "OK" to save the document to encrypt the document.






