Firewalld Linux firewall
firewall firewall
The firewalld service has two working modes: CLI and GUI. Compared with iptables, firewall supports dynamic updates and introduces the concept of zone.
In short, a zone refers to a set of firewall policies predefined by the firewall, which allows these policies to be quickly switched between firewalls, thereby significantly improving the switching efficiency and application speed of the firewall.
| area | Default Policy Rules |
| trusted | Allow all packets |
| home | Deny incoming traffic, but allow ssh, mdns, ipp-client, dhcpv6-client services to pass |
| internal | Equivalent to home area |
| work | Deny incoming traffic, but allow ssh, ipp-client, and dhcpv6-client services to pass |
| public | Deny incoming traffic, but allow ssh, ipp-client, and dhcpv6-client services to pass |
| external | Deny incoming traffic, but allow it if it is related to the ssh service |
| dmz | Deny incoming traffic, but allow it if it is related to the ssh service |
| block | Reject incoming traffic unless related to outgoing traffic |
| drop | Reject incoming traffic unless related to outgoing traffic |
firewalld is a dynamic firewall management tool on Linux systems. It is the default firewall management tool for Centos7 systems, replacing the previous iptables firewall.
Firewalld mainly works at the network layer and is a packet filtering firewall. Compared with traditional iptables, firewalld is more flexible and easy to use, and can achieve more detailed network access control.
firewalld firewall mainly consists of two aspects: zone and service. Zones define different parts of the network and have a set of rules for each zone. For example, the public zone is suitable for hosts in a public Internet environment, while the internal zone is suitable for hosts in an internal network environment. A Service, on the other hand, is a set of predefined rules that control access to specific ports. By configuring zone and service rules, the firewall can be effectively managed to ensure network security.
firewalld is a dynamic firewall management tool that supports network connections and interfaces defined by network zones and security levels. It configures IPv4 and IPv6 firewall settings, as well as Ethernet bridges. Provides two modes: runtime configuration and permanent configuration.

Firewall status query command: Some commonly used firewall status query commands only need to specify complete parameters to obtain the current firewall status.
[root@localhost ~]# firewall-cmd --state #显示运行状态 [root@localhost ~]# firewall-cmd --get-zones #显示所有zone区域 [root@localhost ~]# firewall-cmd --get-active-zones#显示当前使用的区域 [root@localhost ~]# firewall-cmd --get-default-zone#显示默认使用的区域 [root@localhost ~]# firewall-cmd --get-zone-of-interface=ens32 #查看ens32网口的区域 [root@localhost ~]# firewall-cmd --zone=public --list-ports#显示public区域所有开放的端口
Firewall service release command: First, we deny all through the parameter --panic-on, and release the port number corresponding to the NFS service through --add-service.
[root@localhost ~]# firewall-cmd --get-services #显示服务列表 [root@localhost ~]# firewall-cmd --list-service #查询当前放行服务 [root@localhost ~]# firewall-cmd --panic-on #拒绝所有包 [root@localhost ~]# firewall-cmd --panic-off#取消拒绝状态 [root@localhost ~]# firewall-cmd --query-panic#查看是否拒绝 [root@localhost ~]# firewall-cmd --reload #重新加载防火墙 [root@localhost ~]# firewall-cmd --add-service=nfs#临时允许nfs服务通过 [root@localhost ~]# firewall-cmd --add-service=nfs --permanent#永久允许nfs服务通过 #放行https服务数据包通过 [root@localhost ~]# firewall-cmd --add-rich-rule 'rule family=ipv4 source address=192.168.1.0/24 service name=httpd accept' [root@localhost ~]# firewall-cmd --list-rich-rule rule family="ipv4" source address="192.168.1.0/24" service name="https" accept
Firewall port release command: We can use the --add-port command to add a port, or use the --remove-port to block a port. Use the port number and Any service name is acceptable.
[root@localhost ~]# firewall-cmd --list-all #显示所有端口列表 [root@localhost ~]# firewall-cmd --list-services#查看开放的服务 [root@localhost ~]# firewall-cmd --list-ports #查看开放的端口 [root@localhost ~]# firewall-cmd --add-port=443/tcp #临时开启443端口 [root@localhost ~]# firewall-cmd --remove-port=443/tcp#删除443端口 [root@localhost ~]# firewall-cmd --add-service=mysql#开放mysql端口 [root@localhost ~]# firewall-cmd --remove-service=http#阻止http端口 [root@localhost ~]# firewall-cmd --add-port=3306/tcp#开放通过tcp访问3306 [root@localhost ~]# firewall-cmd --remove-port=80/tcp #阻止通过tcp访问3306 [root@localhost ~]# firewall-cmd --add-port=233/udp #开放通过udp访问233 #临时放行8080端口,和8081端口 [root@localhost ~]# firewall-cmd --zone=public --add-port=8080-8081/tcp success [root@localhost ~]# firewall-cmd --zone=public --list-ports 8080-8081/tcp #放行本地的3260端口 [root@localhost ~]# firewall-cmd --add-rich-rule 'rule family=ipv4 source address=192.168.1.0/24 port port=3260 protocol=tcp accept'
Firewall configuration port forwarding: The port forwarding function is automatically forwarded to a port on the local machine or the target host when a user accesses port 80 of the machine.
#将80端口的流量转发至8080 [root@localhost ~]# firewall-cmd --add-forward-port=port=80:proto=tcp:toport=8080 #将80端口的流量转发至192.168.1.1 [root@localhost ~]# firewall-cmd --add-forward-port=proto=80:proto=tcp:toaddr=192.168.1.1.1 #将80端口的流量转发至192.168.1.1的8080端口上 [root@localhost ~]# firewall-cmd --add-forward-port=proto=80:proto=tcp:toaddr=192.168.1.1:toport=8080
Query and set the default area: Query the area currently used by the firewall service, and set the new default area of the service to the external area.
#查询firewall服务当前所使用的区域 [root@localhost ~]# firewall-cmd --get-default-zone public #查看ens32网卡的所在区域信息 [root@localhost ~]# firewall-cmd --get-zone-of-interface=ens32 public #设置默认区域为external [root@localhost ~]# firewall-cmd --set-default-zone=external success [root@localhost ~]# firewall-cmd --get-default-zone external
Modify the default zone to a new zone: Modify the public zone of the ens32 network port to the external zone, and it will take effect permanently.
[root@localhost ~]# firewall-cmd --get-zone-of-interface=ens32 public [root@localhost ~]# firewall-cmd --zone=external --change-interface=ens32 [root@localhost ~]# firewall-cmd --zone=external --change-interface=ens32 --permanent success [root@localhost ~]# firewall-cmd --get-zone-of-interface=ens32 external
Set the service status of a certain area: Set whether a certain area allows traffic requesting SSH and HTTPS protocols
#查询public区域内是否放行了ssh,https服务 [root@localhost ~]# firewall-cmd --zone=public --query-service=ssh yes [root@localhost ~]# firewall-cmd --zone=public --query-service=https no #把public区域的https请求,永久允许通过 [root@localhost ~]# firewall-cmd --zone=public --add-service=https success [root@localhost ~]# firewall-cmd --zone=public --add-service=https --permanent success #把public区域的https请求,设置为永久拒绝. [root@localhost ~]# firewall-cmd --zone=public --remove-service=https success [root@localhost ~]# firewall-cmd --zone=public --remove-service=https --permanent success
Set port forwarding policy: For systems in the 192.168.1.0/24 network, access to the local port 5423 will be forwarded to the local 80 port.
[root@localhost ~]# firewall-cmd --add-rich-rule 'rule family=ipv4 source address=192.168.1.0/24 forward-port port=5423 protocol=tcp to-port=80' --permanent
Allow/remove access ports: batch allow or remove the port policy of a host in a certain area.
# 允许/移除 192.168.1.10 所有访问所有端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.1.10" accept' --permanent firewall-cmd --zone=public --remove-rich-rule 'rule family="ipv4" source address="192.168.1.10" accept' --permanent firewall-cmd --zone=public --remove-rich-rule 'rule family="ipv4" source address="192.168.1.10" drop' --permanent # 允许192.168.2.0/24所有访问所有端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.2.0/24" accept' --permanent # 允许192.168.10访问22端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.1.10" port port=22 protocol=tcp reject' --permanent # 移除192.168.10访问22端口 firewall-cmd --zone=public --remove-rich-rule 'rule family="ipv4" source address="192.168.1.10" port port=22 protocol=tcp reject' --permanent # 允许192.168.1.0/24访问22端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.1.0/24" port port=22 protocol=tcp accept'
Firewall technology types:
(1) Packet filtering firewall (packet filtering)
(2) Application proxy firewall (application proxy)
(3) Stateful inspection firewall (stateful inspection)
(firewalld is a packet filtering firewall, so we only talk about packet filtering firewalls here)
Packet Filtering Firewall Overview:
(1) netfilter: The packet filtering function system located in the Linux kernel becomes the "kernel state" of the Linux firewall.
(2) firewalld: CentOS7's default tool for managing firewall rules, becoming the "user mode" of the Linux firewall.
————The above two names can be expressed as Linux firewall.
Working level of packet filtering:
(1) Mainly the network layer, checking the source IP for IP packets.
(2) is reflected in the processing of IP address, port and other information in the package.
Network area:
Firewalld’s nine predefined network areas:
①trusted②public③work④home⑤internal⑥external⑦dmz⑧block⑨drop
————There are some valid zones by default. The zones provided by firewalld are ordered from untrusted to trusted.
(1) Drop Zone: If the drop zone is used, any incoming packets will be dropped. This is similar to iptables -j drop on Centos6. Using drop rules means that there will be no response.
(2) Block Zone: The blocking zone will reject incoming network connections and return icmp-host-prohibited. Only connections that have been established by the server will be passed, that is, only network connections initialized by the system are allowed.
(3) Public Zone: Only accept those selected connections. By default, only ssh and dhcpv6-client are allowed. This zone is the default zone (default means default, so the public zone is also the default zone) , going to the public area without any configuration).
(4) External Zone: This zone is equivalent to the router's startup masquerading option. Only specified connections will be accepted, that is, ssh, while other connections will be dropped or not accepted.
(5) Isolation Zone (DMZ Zone): If you want to allow only some services to be accessed from the outside, you can define it in the DMZ zone. It also has the feature of only selected connections, that is, ssh. This zone also It's called a demilitarized zone.
(6)工作区域(Work Zone):在这个区域中,我们只能定义内部网络,比如私有网络通信才被允许, 只允许ssh、ipp-client和dhcpv6-client。
(7)家庭区域(Home Zone):这个区域专门用于家庭环境,它同样只允许被选中的连接, 即ssh、ipp-client、mdns、samba-client和dhcpv6-client。
(8)内部区域(Internal Zone):这个区域和 工作区域(Work Zone) 类似,只允许通过被选中的连接,与 家庭区域(Home Zone) 相同。
(9)信任区域(Trusted Zone):信任区域允许所有网络通信通过,因为 信任区域(Trusted Zone)是最被信任的,即使没有设置任何的服务,那么也是被允许的,因为 信任区域(Trusted Zone)是允许所有连接的。
————以上是系统定义的所有的区域(Zone),但是,不是所有的区域(Zone)都在使用,只有活跃的区域(Zone)才有实际操作意义。
注意:因为默认区域只允许ssh和dhcp,所以在没有任何配置的情况下默认是拒绝ping包的。
常用命令
# 查看所有放行端口 firewall-cmd --zone=public --list-ports # 禁止IP访问机器 firewall-cmd --permanent --add-rich-rule='rule family=ipv4 source address="192.168.0.1" drop' # 禁止一个IP段,比如禁止192.168.*.* firewall-cmd --permanent --add-rich-rule='rule family=ipv4 source address="192.168.0.1/16" drop' # 禁止一个IP段,比如禁止192.168.0.* firewall-cmd --permanent --add-rich-rule='rule family=ipv4 source address="192.168.0.1/24" drop' # 禁止机器IP从防火墙中删除 firewall-cmd --permanent --remove-rich-rule='rule family=ipv4 source address="192.168.0.1" drop' # 允许http服务(对应服务策略目录:/usr/lib/firewalld/services/) firewall-cmd --permanent --add-service=http # 关闭http服务(对应服务策略目录:/usr/lib/firewalld/services/) firewall-cmd --permanent --remove-service=http # 允许端口:3306 firewall-cmd --permanent --add-port=3306/tcp # 允许端口:1-3306 firewall-cmd --permanent --add-port=1-3306/tcp # 关闭放行中端口:3306 firewall-cmd --permanent --remove-port=3306/tcp # 查看firewall的状态 firewall-cmd --state # 查看防火墙规则(只显示/etc/firewalld/zones/public.xml中防火墙策略) firewall-cmd --list-all # 查看所有的防火墙策略(即显示/etc/firewalld/zones/下的所有策略) firewall-cmd --list-all-zones # 重新加载配置文件 firewall-cmd --reload # 更改配置后一定要重新加载配置文件 firewall-cmd --reload # Postgresql端口设置。允许192.168.142.166访问5432端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.142.166" port port="5432" protocol="tcp" accept" # redis端口设置。允许192.168.142.166访问6379端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.142.166" port port="6379" protocol="tcp" accept" # beanstalkd端口设置。允许192.168.142.166访问11300端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.142.166" port port="11300" protocol="tcp" accept" # 查看防火墙端口列表 firewall-cmd --list-ports # 添加指定端口tcp firewall-cmd --zone=public --add-port=8080/tcp --permanent# 开放8080/tcp端口 firewall-cmd --zone=public --add-port=10002-10010/tcp --permanent# 开放10002-10010/tcp端口范围 # 添加指定端口udp firewall-cmd --zone=public --add-port=9200/udp --permanent # 开放9200/udp端口 firewall-cmd --zone=public --add-port=20015-20020/udp --permanent# 开放20015-20020/udp端口范围 # 删除指定端口 firewall-cmd --zone= public --remove-port=19800/tcp --permanent # 删除已开放的19880/tcp端口 firewall-cmd --zone= public --remove-port=9200-9300/udp --permanent# 删除已开放的9200-9300/udp 端口范围 # 热加载防火墙,使之生效 firewall-cmd --reload # 指定某IP访问某端口 firewall-cmd --permanent --zone=public --add-rich-rule="rule family="ipv4" source address="192.168.0.107" port protocol="tcp" port="3306" accept" # 删除策略 firewall-cmd --permanent --zone=public --remove-rich-rule="rule family="ipv4" source address="192.168.0.107" port protocol="tcp" port="3306" accept" # 指定某个网段访问某个端口范围 firewall-cmd --permanent --zone=public --add-rich-rule="rule family="ipv4" source address="11.76.168.0/24" port protocol="udp" port="1-65535" accept" # 删除策略 firewall-cmd --permanent --zone=public --remove-rich-rule="rule family="ipv4" source address="11.76.168.0/24" port protocol="tcp" port="1-65535" accept" # 禁止指定ip 访问某个端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.100.200" port protocol="tcp" port="80" reject" # 禁止某个段的ip 访问某个端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="10.0.0.0/24" port protocol="tcp" port="80" reject" # 允许指定ip 访问所有端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.100.100" port protocol="tcp" accept" # 允许指定ip段 访问所有端口 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.1.0/24" port protocol="tcp" accept" # 允许192.168.1.10所有访问所有端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.1.10" accept' --permanent # 移除192.168.1.10所有访问所有端口 firewall-cmd --zone=public --remove-rich-rule 'rule family="ipv4" source address="192.168.1.10" accept' --permanent # 允许192.168.2.0/24(0-255)所有访问所有端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.2.0/24" accept' --permanent # 允许192.168.1.10所有访问TCP协议的22端口 firewall-cmd --zone=public --add-rich-rule 'rule family="ipv4" source address="192.168.1.10" port port=22 protocol=tcp reject' --permanent # 移除192.168.1.10所有访问TCP协议的22端口 firewall-cmd --zone=public --remove-rich-rule 'rule family="ipv4" source address="192.168.1.10" port port=22 protocol=tcp reject' --permanent # 防火墙重新载入(必须重新载入后才能生效) firewall-cmd --reload # 查看rich-rules(富规则) firewall-cmd --list-rich-rules # 查看防火墙服务规则 firewall-cmd --list-services # 查看防火墙所有规则 firewall-cmd --list-all # 查看防火墙所有区域的配置规则 firewall-cmd --list-all-zones # 查看默认区域 firewall-cmd --get-default-zone # 查看网络接口使用区域 firewall-cmd --get-active-zones # 查看默认的可用服务 firewall-cmd --get-services # 要启用或禁用HTTP服务 firewall-cmd --zone=public --add-service=http --permanent firewall-cmd --zone=public --remove-service=http --permanent # 移除现有规则(此步骤相当重要,很多文章和博客都没提及到) firewall-cmd --permanent --zone=public --remove-port=80/tcp firewall-cmd --reload # 在192.168.100.100102上测试访问 curl192.168.100.101 发现均无法再访问101的80端口 # 设置规则 firewall-cmd --permanent --add-rich-rule="rule family="ipv4" source address="192.168.100.102" port protocol="tcp" port="80" accept" firewall-cmd --reload # 测试访问 curl 192.168.100.101 # 100无法访问102可以访问 至此实现了通过防火墙firewalld设置规则,指定ip访问指定端口
The above is the detailed content of Firewalld Linux firewall. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1377
1377
 52
52
 Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
Win11 firewall advanced settings gray solution
Dec 24, 2023 pm 07:53 PM
When setting up the firewall, many friends found that their win11 firewall advanced settings were grayed out and unable to be clicked. This may be caused by not adding a control unit, or by not opening the advanced settings in the correct way. Let’s take a look at how to solve it. Win11 firewall advanced settings gray method one: 1. First, click the start menu below, search and open "Control Panel" at the top 2. Then open "Windows Defender Firewall" 3. After entering, you can open "Advanced Settings" in the left column . Method 2: 1. If the above method cannot be opened, you can right-click "Start Menu" and open "Run" 2. Then enter "mmc" and press Enter to confirm opening. 3. After opening, click on the upper left
 How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
How to enable or disable firewall on Alpine Linux?
Feb 21, 2024 pm 12:45 PM
On AlpineLinux, you can use the iptables tool to configure and manage firewall rules. Here are the basic steps to enable or disable the firewall on AlpineLinux: Check the firewall status: sudoiptables -L If the output shows rules (for example, there are some INPUT, OUTPUT, or FORWARD rules), the firewall is enabled. If the output is empty, the firewall is currently disabled. Enable firewall: sudoiptables-PINPUTACCEPTsudoiptables-POUTPUTACCEPTsudoiptables-PFORWARDAC
 Why can't I download Google Chrome in Windows 7?
Apr 13, 2024 pm 11:00 PM
Why can't I download Google Chrome in Windows 7?
Apr 13, 2024 pm 11:00 PM
Reasons why you can't download Google Chrome on Windows 7: The operating system version is too old; security protocols are out of date; necessary components are missing; blocked by firewall or security software; network connection issues. Solution: Upgrade operating system, enable TLS 1.2, install necessary components, check firewall, check network connection.
 How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
How to remove the firewall logo on the Win10 desktop icon?
Jan 01, 2024 pm 12:21 PM
Many friends who use win10 system find that there is a firewall logo on the icon on the computer desktop. What is going on? This makes many friends with obsessive-compulsive disorder particularly uncomfortable. In fact, we only need to open the control panel and click " It can be solved by changing "Change User Account Control Settings". Let's take a look at the specific tutorial. How to cancel the firewall logo on the desktop icon in Windows 10 1. First, right-click the Start menu button next to the computer startup screen, and then select the Control Panel function from the pop-up menu. 2. Then select the "User Account" option and select the "Change User Account Control Settings" item from the new interface that appears. 3. After adjusting the slider in the window to the bottom, click Confirm to exit.
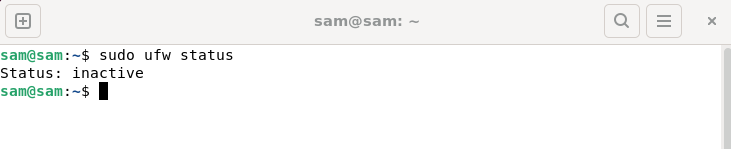 How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
How to fix UFW status showing as inactive in Linux
Mar 20, 2024 pm 01:50 PM
UFW, also known as Uncomplex Firewall, is adopted by many Linux distributions as their firewall system. UFW is designed to make it easy for novice users to manage firewall settings through both the command line interface and the graphical user interface. A UFW firewall is a system that monitors network traffic according to set rules to protect the network from network sniffing and other attacks. If you have UFW installed on your Linux system but its status shows as inactive, there could be several reasons. In this guide, I will share how to resolve the UFW firewall inactive issue on Linux systems. Why UFW Shows Inactive Status on Linux Why UFW Is Inactive by Default on Linux How to Inactive on Linux
 Why can't the win11 control panel open?
Apr 17, 2024 pm 02:15 PM
Why can't the win11 control panel open?
Apr 17, 2024 pm 02:15 PM
Reasons why Windows 11 Control Panel won't open may include: Process conflicts Corrupted files Virus or malware infection Registry errors Permission issues Windows updates Hardware issues Other reasons (corrupted system files, conflicting drivers, or firewall configurations)
 How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve if Edge browser is blocked by firewall?
Mar 13, 2024 pm 07:10 PM
How to solve the problem that the Edge browser is blocked by the firewall? Edge browser is Microsoft's own browser. Some users found that this browser was blocked by the firewall during use. So what's going on? Let this site give users a detailed introduction on how to recover the Edge browser if it is blocked by the firewall. How to restore the Edge browser if it is blocked by the firewall? 1. Check the firewall settings: - Click the "Start" button on the Windows taskbar, and then open "Settings". -In the Settings window, select Update & Security. -exist
 The best Linux version of 2024: perfect integration of technology and art, open and innovative attitude towards life
Apr 03, 2024 am 08:01 AM
The best Linux version of 2024: perfect integration of technology and art, open and innovative attitude towards life
Apr 03, 2024 am 08:01 AM
As a Linux enthusiast in 2024, my expectations for the best Linux distribution are exciting. Below, I will explain my personal views and analyze why the most attractive Linux distribution in 2024 has many unique advantages. 1. First introduction to the most beautiful Linux distribution. There is no doubt that the best Linux distribution in 2024 can be called the perfect fusion of technology and art. It has excellent performance in many aspects such as user interface, function planning and performance optimization, making it unique in the face of many competitors. This is not only an operating system, but also a symbol of a free, open and innovative attitude towards life. This optimal version incorporates a new design and interactive mode, which is bound to be refreshing. Whether it is layout structure, logo pattern or color matching,




