Mysql开源备份工具Xtrabackup备份部署_MySQL
bitsCN.com
Mysql开源备份工具Xtrabackup备份部署
Xtrabackup是一个对InnoDB做数据备份的工具,支持在线热备份(备份时不影响数据读写),是商业备份工具InnoDB Hotbackup的一个很好的替代品。
Xtrabackup有两个主要的工具:xtrabackup、innobackupex
1、xtrabackup只能备份InnoDB和XtraDB两种数据表,而不能备份MyISAM数据表
2、innobackupex是参考了InnoDB Hotbackup的innoback脚本修改而来的.innobackupex是一个perl脚本封装,封装了xtrabackup。主要是为了方便的 同时备份InnoDB和MyISAM引擎的表,但在处理myisam时需要加一个读锁。并且加入了一些使用的选项。如slave-info可以记录备份恢 复后,作为slave需要的一些信息,根据这些信息,可以很方便的利用备份来重做slave。
Xtrabackup下载地址:
http://www.percona.com/downloads/XtraBackup/LATEST/binary/
选择合适的版本,我这里选择binary。
解压到/usr/src/目录,解压后目录名percona-xtrabackup-2.1.3,进入到bin目录,即可直接使用innobackupex命令
# pwd
/usr/src/percona-xtrabackup-2.1.3/bin
# ls -l
total 112396
-rwxr-xr-x 1 root root 110738 Jun 7 11:43 innobackupex
-rwxr-xr-x 1 root root 110738 Jun 7 11:43 innobackupex-1.5.1
-rwxr-xr-x 1 root root 2211237 Jun 7 11:43 xbcrypt
-rwxr-xr-x 1 root root 2285672 Jun 7 11:43 xbstream
-rwxr-xr-x 1 root root 13033745 Jun 7 11:43 xtrabackup
-rwxr-xr-x 1 root root 16333506 Jun 7 11:43 xtrabackup_55
-rwxr-xr-x 1 root root 80988093 Jun 7 11:43 xtrabackup_56
在开始使用的时候可能会报如下错误:
sh: xtrabackup_55: command not found
innobackupex: fatal error: no 'mysqld' group in MySQL options
解决办法xtrabackup_55复制到/usr/bin下即可。
# cp /usr/src/percona-xtrabackup-2.1.3/bin/xtrabackup_55 /usr/bin/
建立mysql备份用户:
mysql> GRANT RELOAD, LOCK TABLES, REPLICATION CLIENT ON *.* TO 'backupuser'@'localhost' identified by 'skEBfef5E2';
mysql> FLUSH PRIVILEGES;
备份脚本内容(每周一次全备,六次增量备份,保留2周的备份,并压缩):
[plain]
#!/bin/bash
BEGINTIME=`date +"%Y-%m-%d %H:%M:%S"`
format_time=`date +"%Y-%m-%d_%H:%M:%S"`
week=`date +%w`
backupbin=/usr/src/percona-xtrabackup-2.1.3/bin
backdir=/data/databasebak/bak
file_cnf=/etc/my.cnf
user_name=backupuser
password="skEBfef5E2"
db="db1 db2 db3 db4"
out_log=$backdir/xtrabackup_log_$format_time
time_cost=$backdir/xtrabackup_time.txt
if [ -f "$backdir.lastlastlastweek.gz" ];then
rm -rf $backdir.lastlastweek.gz
mv $backdir.lastweek.gz $backdir.lastlastweek.gz
fi
if [ -d "$backdir/rec5" ];then
gzip -cr $backdir >$backdir.lastweek.gz
rm -rf $backdir
mkdir $backdir
fi
#full
if [ ! -d "$backdir/full" ];then
echo "#####start full backup at $BEGINTIME to directory full" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" $backdir/full 1> $out_log 2>&1
break;
elif [ ! -d "$backdir/rec0" ];then
echo "#####start 0 incremental backup at $BEGINTIME to directory rec0" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" --incremental --incremental-basedir=$backdir/full $backdir/rec0 1> $out_log 2>&1
break;
elif [ ! -d "$backdir/rec1" ];then
echo "#####start 1 incremental backup at $BEGINTIME to directory rec1" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" --incremental --incremental-basedir=$backdir/rec0 $backdir/rec1 1> $out_log 2>&1
break;
elif [ ! -d "$backdir/rec2" ];then
echo "#####start 2 incremental backup at $BEGINTIME to directory rec2" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" --incremental --incremental-basedir=$backdir/rec1 $backdir/rec2 1> $out_log 2>&1
break;
elif [ ! -d "$backdir/rec3" ];then
echo "#####start 3 incremental backup at $BEGINTIME to directory rec3" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" --incremental --incremental-basedir=$backdir/rec2 $backdir/rec3 1> $out_log 2>&1
break;
elif [ ! -d "$backdir/rec4" ];then
echo "#####start 4 incremental backup at $BEGINTIME to directory rec4" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" --incremental --incremental-basedir=$backdir/rec3 $backdir/rec4 1> $out_log 2>&1
break;
elif [ ! -d "$backdir/rec5" ];then
echo "#####start 5 incremental backup at $BEGINTIME to directory rec5" >>$time_cost
$backupbin/innobackupex --defaults-file=$file_cnf --no-timestamp --user=$user_name --password=$password --slave-info --databases="$db" --incremental --incremental-basedir=$backdir/rec4 $backdir/rec5 1> $out_log 2>&1
break;
fi
ENDTIME=`date +"%Y-%m-%d %H:%M:%S"`
begin_data=`date -d "$BEGINTIME" +%s`
end_data=`date -d "$ENDTIME" +%s`
spendtime=`expr $end_data - $begin_data`
echo "it takes $spendtime sec for packing the data directory" >>$time_cost
部署备份脚本;
# crontab -l
10 2 * * * /opt/cron/mysqldbbakup.sh
恢复:
#全备恢复:
innobackupex --apply-log --redo-only --defaults-file=$file_cnf --user=$user_name --password=$password $backdir/full
#增备恢复,修改增量备份目录,逐个apply-log,到第五天的增量rec4都是输出都显示innobackupex: completed OK!
innobackupex --apply-log --redo-only --defaults-file=$file_cnf --user=$user_name --password=$password $backdir/full --incremental-dir=$backdir/rec5
bitsCN.com

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

AI Hentai Generator
Generate AI Hentai for free.

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
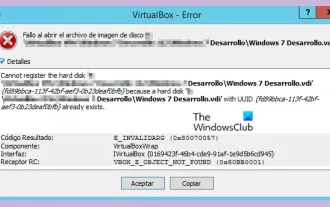 VBOX_E_OBJECT_NOT_FOUND(0x80bb0001)VirtualBox error
Mar 24, 2024 am 09:51 AM
VBOX_E_OBJECT_NOT_FOUND(0x80bb0001)VirtualBox error
Mar 24, 2024 am 09:51 AM
When trying to open a disk image in VirtualBox, you may encounter an error indicating that the hard drive cannot be registered. This usually happens when the VM disk image file you are trying to open has the same UUID as another virtual disk image file. In this case, VirtualBox displays error code VBOX_E_OBJECT_NOT_FOUND(0x80bb0001). If you encounter this error, don’t worry, there are some solutions you can try. First, you can try using VirtualBox's command line tools to change the UUID of the disk image file, which will avoid conflicts. You can run the command `VBoxManageinternal
 How effective is receiving phone calls using airplane mode?
Feb 20, 2024 am 10:07 AM
How effective is receiving phone calls using airplane mode?
Feb 20, 2024 am 10:07 AM
What happens when someone calls in airplane mode? Mobile phones have become one of the indispensable tools in people's lives. It is not only a communication tool, but also a collection of entertainment, learning, work and other functions. With the continuous upgrading and improvement of mobile phone functions, people are becoming more and more dependent on mobile phones. With the advent of airplane mode, people can use their phones more conveniently during flights. However, some people are worried about what impact other people's calls in airplane mode will have on the mobile phone or the user? This article will analyze and discuss from several aspects. first
 How to develop an online restaurant reservation system using Laravel
Nov 02, 2023 pm 01:48 PM
How to develop an online restaurant reservation system using Laravel
Nov 02, 2023 pm 01:48 PM
How to use Laravel to develop an online restaurant reservation system In recent years, with the rapid development of the Internet and mobile Internet, online reservations have become an indispensable part of modern people's lives. The catering industry is no exception. More and more restaurants are beginning to provide online reservation services to improve user experience and expand market share. This article will introduce how to use the Laravel framework to develop a simple but fully functional online restaurant reservation system, and provide specific code examples to facilitate readers to learn and practice. Environment setup First, we need
 How to turn off the comment function on TikTok? What happens after turning off the comment function on TikTok?
Mar 23, 2024 pm 06:20 PM
How to turn off the comment function on TikTok? What happens after turning off the comment function on TikTok?
Mar 23, 2024 pm 06:20 PM
On the Douyin platform, users can not only share their life moments, but also interact with other users. Sometimes the comment function may cause some unpleasant experiences, such as online violence, malicious comments, etc. So, how to turn off the comment function of TikTok? 1. How to turn off the comment function of Douyin? 1. Log in to Douyin APP and enter your personal homepage. 2. Click "I" in the lower right corner to enter the settings menu. 3. In the settings menu, find "Privacy Settings". 4. Click "Privacy Settings" to enter the privacy settings interface. 5. In the privacy settings interface, find "Comment Settings". 6. Click "Comment Settings" to enter the comment setting interface. 7. In the comment settings interface, find the "Close Comments" option. 8. Click the "Close Comments" option to confirm closing comments.
 File Inclusion Vulnerabilities in Java and Their Impact
Aug 08, 2023 am 10:30 AM
File Inclusion Vulnerabilities in Java and Their Impact
Aug 08, 2023 am 10:30 AM
Java is a commonly used programming language used to develop various applications. However, just like other programming languages, Java has security vulnerabilities and risks. One of the common vulnerabilities is the file inclusion vulnerability (FileInclusionVulnerability). This article will explore the principle, impact and how to prevent this vulnerability. File inclusion vulnerabilities refer to the dynamic introduction or inclusion of other files in the program, but the introduced files are not fully verified and protected, thus
 How to use Java Websocket to implement online audio and video calls?
Dec 02, 2023 am 09:44 AM
How to use Java Websocket to implement online audio and video calls?
Dec 02, 2023 am 09:44 AM
How to use JavaWebsocket to implement online audio and video calls? In today's digital age, real-time communication is becoming more and more common. Whether it is remote collaboration at work or remote communication with relatives and friends at home, real-time audio and video calls have become an indispensable part of people. This article will introduce how to use JavaWebsocket to implement online audio and video calls, and provide specific code examples. 1. Understand WebsocketWebsocket is a new technology in HTML5
 The impact of data scarcity on model training
Oct 08, 2023 pm 06:17 PM
The impact of data scarcity on model training
Oct 08, 2023 pm 06:17 PM
The impact of data scarcity on model training requires specific code examples. In the fields of machine learning and artificial intelligence, data is one of the core elements for training models. However, a problem we often face in reality is data scarcity. Data scarcity refers to the insufficient amount of training data or the lack of annotated data. In this case, it will have a certain impact on model training. The problem of data scarcity is mainly reflected in the following aspects: Overfitting: When the amount of training data is insufficient, the model is prone to overfitting. Overfitting refers to the model over-adapting to the training data.
 What problems will bad sectors on the hard drive cause?
Feb 18, 2024 am 10:07 AM
What problems will bad sectors on the hard drive cause?
Feb 18, 2024 am 10:07 AM
Bad sectors on a hard disk refer to a physical failure of the hard disk, that is, the storage unit on the hard disk cannot read or write data normally. The impact of bad sectors on the hard drive is very significant, and it may lead to data loss, system crash, and reduced hard drive performance. This article will introduce in detail the impact of hard drive bad sectors and related solutions. First, bad sectors on the hard drive may lead to data loss. When a sector in a hard disk has bad sectors, the data on that sector cannot be read, causing the file to become corrupted or inaccessible. This situation is especially serious if important files are stored in the sector where the bad sectors are located.






