 web3.0
web3.0
 Vitalik's new article: If a quantum attack comes tomorrow, how will Ethereum solve the problem?
Vitalik's new article: If a quantum attack comes tomorrow, how will Ethereum solve the problem?
Vitalik's new article: If a quantum attack comes tomorrow, how will Ethereum solve the problem?
Original author: Vitalik Buterin
Translator: Azuma, Odaily Planet Daily
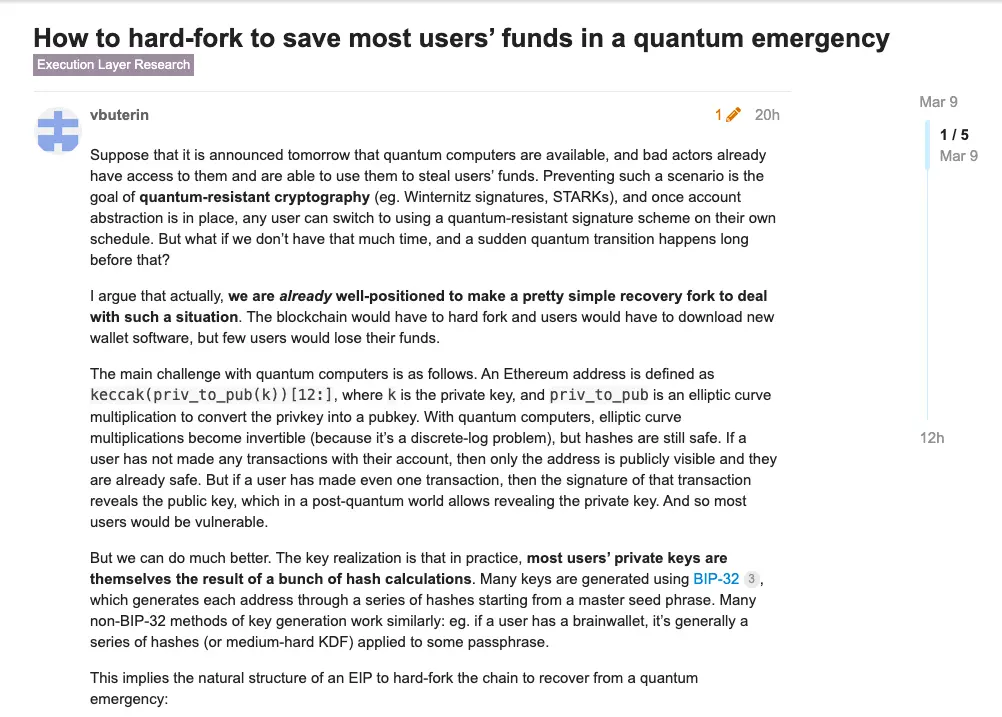
On March 9, Vitalik Buterin, the co-founder of Ethereum, spoke at Ethereum A short article was published on the research forum, titled "Coping with Sudden Quantum Attacks: Protecting User Funds through Hard Forks."
In the article, Vitalik reviews how Ethereum can minimize the loss of user funds in the event that it may face a quantum attack, and discusses the program changes in emergency situations to deal with quantum threats, thereby ensuring that the system can return to normal run.
The following is the full text of Vitalik, compiled by Odaily Planet Daily.
Suppose a quantum computer becomes available tomorrow, and a bad actor has somehow gained access to it and wants to use it to steal user funds, what should we do?
Quantum-resistant technologies such as Winternitz signatures and STARKs were developed to prevent this from happening. Once the account abstraction is ready, any user can randomly switch to a quantum-resistant one. Signature scheme. But if we don’t have that much time, what should we do if the quantum attack comes more suddenly than everyone thinks?
I think,In fact, we currently have sufficient conditions to solve this problem through a relatively simple recovery fork. With this solution, the Ethereum network will have to undergo a hard fork and users will have to download new wallet software, but only a small number of users may lose their funds.
The main threats of quantum attacks are as follows. The Ethereum address is obtained by operating the keccak(priv_to_pub(k))[12:] function, where k corresponds to the private key and priv_to_pub corresponds to an elliptic curve multiplication used to convert the private key into a public key.
When quantum computing is realized, the above elliptic curve multiplication will become reversible (because this is actually the solution to the discrete logarithm problem), but the hash operation is still safe. If the user has not made any transactions, then only the address information is disclosed, in which case they will still be safe; but as long as the user has made even one transaction, the transaction signature will expose the public key, which is impossible in quantum computers. There is the possibility of exposing the private key. So in this case, most users will be at risk.
But we actually have ways to mitigate this threat. The key point is that in practice, most users’ private keys are generated through a series of hash operations. For example, many private keys are generated using the BIP-32 specification, which is generated through a series of hash operations based on a set of mnemonic words; many non-BIP-32 private key generation methods are almost similar, for example, if the user uses It is a brain wallet, which is usually generated by a series of hash operations (or a moderately difficult key derivation function) of a password.
This means that the solution to deal with sudden quantum attacks through restorative forks will take the following steps:
- First, roll back all blocks after the large-scale attack;
- Second, disable the traditional transaction mode based on EOA addresses;
- Third, ( If it has not been implemented by then) add a new transaction type to allow transactions through smart contract wallets (such as part of RIP-7560);
- Fourth, add new transaction types or operations code, through which users can provide STARK proof. If the proof is passed, the code of the user's address will be switched to a new verified code, and then the user can use the new code address as a smart contract wallet.
- Fifth, for the purpose of saving gas and due to the large amount of data required for STARK proofs, we will support batch STARK proofs to conduct multiple STARK proofs of the above types at the same time.
In principle, tomorrow we could begin development on the infrastructure needed to implement this restorative fork, allowing the Ethereum ecosystem to be prepared in the event of a sudden quantum attack.
The above is the detailed content of Vitalik's new article: If a quantum attack comes tomorrow, how will Ethereum solve the problem?. For more information, please follow other related articles on the PHP Chinese website!

Hot AI Tools

Undresser.AI Undress
AI-powered app for creating realistic nude photos

AI Clothes Remover
Online AI tool for removing clothes from photos.

Undress AI Tool
Undress images for free

Clothoff.io
AI clothes remover

Video Face Swap
Swap faces in any video effortlessly with our completely free AI face swap tool!

Hot Article

Hot Tools

Notepad++7.3.1
Easy-to-use and free code editor

SublimeText3 Chinese version
Chinese version, very easy to use

Zend Studio 13.0.1
Powerful PHP integrated development environment

Dreamweaver CS6
Visual web development tools

SublimeText3 Mac version
God-level code editing software (SublimeText3)

Hot Topics
 1386
1386
 52
52
 What is Ouyi for? What is Ouyi
Apr 01, 2025 pm 03:18 PM
What is Ouyi for? What is Ouyi
Apr 01, 2025 pm 03:18 PM
OKX is a global digital asset trading platform. Its main functions include: 1. Buying and selling digital assets (spot trading), 2. Trading between digital assets, 3. Providing market conditions and data, 4. Providing diversified trading products (such as derivatives), 5. Providing asset value-added services, 6. Convenient asset management.
 Will Dogecoin etf be approved?
Mar 28, 2025 pm 03:51 PM
Will Dogecoin etf be approved?
Mar 28, 2025 pm 03:51 PM
As of March 2025, the Dogecoin ETF has not yet had a clear approval schedule. 1. There is no formal application yet and the SEC has not received any relevant application. 2. Market demand and controversy are high, and regulators are conservative. 3. The potential timeline is a 1-2-year review period, which may be observed from 2025 to 2026, but there is high uncertainty.
 What are the Ethereum trading platforms?
Mar 26, 2025 pm 04:48 PM
What are the Ethereum trading platforms?
Mar 26, 2025 pm 04:48 PM
Want to play Ethereum? Choose the right trading platform first! There are centralized exchanges (CEXs) such as Binance, Ouyi, Coinbase, Kraken, and Gate.io. The advantages are fast speed and good liquidity, while the disadvantages are centralized risks. There are also decentralized exchanges (DEXs) such as Uniswap, SushiSwap, Balancer, and Curve. The advantages are security and transparency, while the disadvantages are slow speed and poor experience.
 Detailed explanation of the issuance price and issuance time of LOOM coins
Mar 20, 2025 pm 06:21 PM
Detailed explanation of the issuance price and issuance time of LOOM coins
Mar 20, 2025 pm 06:21 PM
LOOM Coin, a once-highly-known blockchain game and social application development platform token, its ICO was held on April 25, 2018, with an issue price of approximately US$0.076 per coin. This article will conduct in-depth discussion on the issuance time, price and important precautions of LOOM coins, including market volatility risks and project development prospects. Investors should be cautious and do not follow the trend blindly. It is recommended to refer to the official website of Loom Network, blockchain browser and cryptocurrency information platform to obtain the latest information and conduct sufficient risk assessment. The information in this article is for reference only and does not constitute investment advice. Learn about LOOM coins, start here!
 The latest summary of Ethereum formal trading platform 2025
Mar 26, 2025 pm 04:45 PM
The latest summary of Ethereum formal trading platform 2025
Mar 26, 2025 pm 04:45 PM
In 2025, choosing a "formal" Ethereum trading platform means security, compliance and transparency. Licensed operations, financial security, transparent operations, AML/KYC, data protection and fair trading are key. Compliant exchanges such as Coinbase, Kraken, and Gemini are worth paying attention to. Binance and Ouyi have the opportunity to become formal platforms by strengthening compliance. DeFi is an option, but there are risks. Be sure to pay attention to security, compliance, expenses, spread risks, back up private keys, and conduct your own research.
 The difference between Ether and Bitcoin What is the difference between Ether and Bitcoin
Mar 19, 2025 pm 04:54 PM
The difference between Ether and Bitcoin What is the difference between Ether and Bitcoin
Mar 19, 2025 pm 04:54 PM
The difference between Ethereum and Bitcoin is significant. Technically, Bitcoin uses PoW, and Ether has shifted from PoW to PoS. Trading speed is slow for Bitcoin and Ethereum is fast. In application scenarios, Bitcoin focuses on payment storage, while Ether supports smart contracts and DApps. In terms of issuance, the total amount of Bitcoin is 21 million, and there is no fixed total amount of Ether coins. Each security challenge is available. In terms of market value, Bitcoin ranks first, and the price fluctuations of both are large, but due to different characteristics, the price trend of Ethereum is unique.
 How to check the contract address on gate.io exchange
Mar 25, 2025 pm 03:54 PM
How to check the contract address on gate.io exchange
Mar 25, 2025 pm 03:54 PM
There are two ways to view contract addresses on the Gate.io exchange: 1. Through the currency details page: log in to the account, search for the target currency, and enter the details page to find the contract address. 2. Through the recharge page: log in to the account, enter the recharge page, and select the currency to view the contract address in the recharge information.



